Microsoft SC-200 (Microsoft Security Operations Analyst)
Microsoft SC-200 (Security Operations Analyst) Certification Overview
What is the Microsoft SC-200 certification and why it matters in 2026
Real-world security handling.
The Microsoft SC-200 certification proves you can actually handle security operations in real Microsoft environments. Not just theory stuff, but hands-on detection, investigation, and response using Microsoft Sentinel and the entire Defender XDR suite. It's a role-based certification that validates you know how to run a modern security operations center using Microsoft's cloud-native platforms.
Here's the thing: enterprises are dumping legacy SIEM solutions for Microsoft 365 E5 and Azure security tools at a pretty aggressive pace, which creates opportunity for certified professionals. Organizations desperately need people who can configure detection rules, write KQL queries, and build automated response playbooks without constantly calling Microsoft support. SC-200 demonstrates you're that person. It sits alongside other Microsoft security certs like SC-100 (Cybersecurity Architect), SC-300 (Identity and Access Administrator), and AZ-500 (Azure Security Engineer) in their security certification pathway, but SC-200 focuses on the operational side. Incident handling, threat hunting, and keeping the SOC running smoothly.
The demand keeps climbing.
Every company migrating to Microsoft 365 realizes they need analysts who understand how Sentinel analytics work. How to correlate alerts across endpoints and cloud apps. How to tune detection rules so they're not drowning in false positives. That's exactly what SC-200 validates. It's incredibly practical, really, though I've seen some folks struggle with the KQL portions if they come from purely GUI-based tools.
What SC-200 validates: core role-based skills for Security Operations Analysts
This certification covers the full incident lifecycle from detection through containment. You need to demonstrate proficiency in managing Microsoft Sentinel as your primary SIEM platform. Configuring data connectors, building analytics rules, creating workbooks for visibility, and implementing SOAR capabilities with Logic Apps and automation playbooks. The exam also tests your knowledge of Microsoft Defender XDR, which pulls together Defender for Endpoint, Defender for Identity, Defender for Office 365, and Defender for Cloud Apps into a unified detection and response platform.
KQL's critical here. You can't fake your way through threat hunting and custom detection queries if you don't understand Kusto Query Language at a functional level. The exam expects you to read KQL queries, understand what they're detecting, and know how to modify them for specific use cases. You'll work with incident management workflows, configure automated response actions, and understand how to investigate alerts across multiple Microsoft security products at once.
Practical application dominates.
The skills measured include managing security operations environments, configuring protections and detections across the Microsoft security stack, managing security incidents and alerts through their entire lifecycle, and performing proactive threat hunting using threat intelligence and behavioral analytics. You're also expected to understand how data connectors feed information into Sentinel. How to build custom workbooks for security monitoring. How to collaborate with security architects and administrators who manage the underlying infrastructure.
Look, this isn't entry-level stuff. Microsoft expects hands-on experience with security operations workflows, incident response procedures, and ideally some exposure to previous SIEM or security monitoring platforms. The exam tests practical application through scenarios where you need to investigate a suspicious login, track lateral movement across a network, or build detection rules for specific attack techniques.
Who should pursue the SC-200 certification in 2026
SOC analysts are the obvious target audience. Whether you're Tier 1 handling alert triage, Tier 2 performing deeper investigations, or Tier 3 conducting advanced threat hunting, SC-200 validates skills you're probably already using daily. Incident response specialists and security incident handlers benefit because the cert covers the entire IR lifecycle within Microsoft's ecosystem.
Threat hunters benefit considerably.
Threat hunters and threat intelligence analysts find value in SC-200's emphasis on proactive detection and KQL-based hunting queries, which is where the real detective work happens. Security engineers implementing Microsoft security solutions need this certification to demonstrate they understand operational requirements, not just deployment mechanics. IT professionals transitioning into cybersecurity roles often choose SC-200 as their entry point into security operations, especially if they already have Microsoft infrastructure experience from certifications like AZ-104 (Azure Administrator) or MS-102 (Microsoft 365 Administrator).
MSSP personnel supporting Microsoft environments need this certification. Managed security providers running multi-tenant Sentinel deployments require analysts who can work across different customer environments efficiently. Security consultants designing SOC implementations use SC-200 to validate their operational knowledge when recommending Microsoft security solutions to clients.
Career switchers with some security fundamentals often start with SC-900 (Security Fundamentals) before tackling SC-200, but if you have solid IT experience and some security exposure, you can probably jump straight to SC-200 with sufficient hands-on practice. Why wait?
How SC-200 fits into the Microsoft security certification pathway
SC-200 occupies the intermediate level in Microsoft's security track. It assumes you understand basic security concepts but doesn't require formal prerequisites. That said, you'll struggle without hands-on experience in Azure, Microsoft 365, and general security operations workflows. The certification complements other Microsoft security credentials rather than replacing them.
Identity matters enormously.
SC-300 (Identity and Access Administrator) pairs naturally with SC-200 because identity is central to modern security operations. Understanding how to investigate identity-based attacks makes you more effective at incident response. AZ-500 (Azure Security Engineer) covers the infrastructure security side, like network security groups, Azure Firewall, security baselines. SC-200 focuses on detection and response. Combined, they give you full Azure security coverage.
For those aiming higher, SC-100 (Cybersecurity Architect) represents the expert-level certification. SC-200 provides the operational foundation that architects need to understand when designing security solutions. You can't architect effective security operations without understanding what analysts actually do daily, and SC-200 gives you that perspective. I've noticed architects without operations experience tend to design systems that look great on paper but frustrate the people who actually have to use them.
it's résumé filler.
Microsoft recognizes SC-200 as necessary for security operations roles in enterprise environments. Organizations hiring for SOC positions specifically request this certification because it demonstrates current, relevant skills with the tools they're actually using.
Career impact and salary expectations for SC-200 certified professionals
Security Operations Analysts with SC-200 certification typically earn between $75,000 and $120,000 USD annually, though this varies by region, experience level, and organization size. Major metropolitan areas and organizations with mature security programs pay toward the higher end. Entry-level analysts might start lower, while senior analysts with additional certifications and several years of experience can exceed these ranges.
Doors open faster.
The certification demonstrates commitment to Microsoft's security ecosystem, which matters when Fortune 500 companies, government agencies, and large MSSPs are hiring. These organizations often standardize on Microsoft security tools, making SC-200 certification directly relevant to their operational needs. It's not uncommon to see job postings specifically requesting SC-200 or equivalent Microsoft security credentials.
Career progression with SC-200 typically moves from SOC analyst roles toward senior analyst positions, threat hunting specialists, or security architect roles. Some certified professionals transition into security engineering positions where they implement and maintain the security infrastructure that analysts use. Others move into consulting, helping organizations design and optimize their security operations capabilities.
The certification increases visibility for roles requiring Microsoft Sentinel and Defender expertise specifically. As more organizations migrate to Microsoft's security stack, demand for analysts who can hit the ground running continues growing. You're not spending six months learning proprietary SIEM platforms because you already know the tools.
Certification alone won't make you a senior threat hunter overnight. But combined with practical experience and continuous learning about emerging threats and attack techniques, SC-200 validates you have the foundational skills organizations need. It opens doors to interviews and demonstrates you've invested time in developing relevant, current security operations expertise in one of the most widely deployed security ecosystems globally.
SC-200 Exam Details and Registration Information
Microsoft SC-200 (Security Operations Analyst) certification overview
The SC-200 certification is Microsoft's role-based badge for people doing day-to-day security operations work. Think triage, incident response, tuning detections, and threat hunting across Microsoft Sentinel and the Defender stack. Not theory. Work.
Look, if your job title has SOC, IR, or "security analyst" anywhere near it, this one fits. You're expected to recognize what "normal" looks like in logs, ask better questions with KQL queries for security monitoring, and make calls fast when alerts pile up at 9:07am on a Monday.
What SC-200 validates (role-based skills)
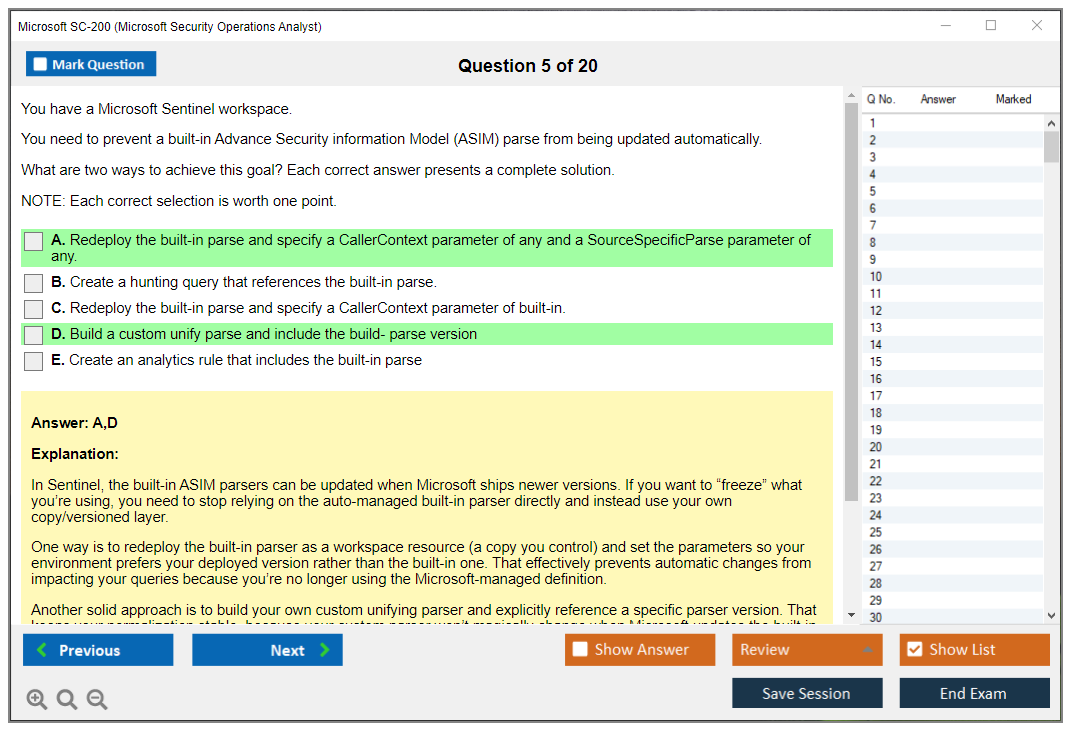
SC-200 is basically a Microsoft Sentinel analyst exam mixed with Microsoft Defender incident response. You need to know how incidents get created, how alerts correlate, what automation can and cannot do, and where data connectors, analytic rules, and hunting queries actually live. Short version: you're being tested on operations.
There's also this really specific vibe to the exam questions. You'll get scenarios, screenshots, and "what would you do next" prompts, and the right answer often matches Microsoft's intended workflow, not the random hack you did once at 2am that technically worked.
Who should take SC-200 (SOC, IR, threat hunting)
SOC analysts. Incident responders.
Threat hunters working security operations at Microsoft shops who live in Sentinel and Defender daily.
If you're a pure identity admin, SC-300 will feel more "home." Building policies and guardrails in Azure? AZ-500 feels more direct. SC-200 is the "I'm staring at alerts, logs, and timelines" exam, with a heavy dose of threat hunting in Microsoft 365 Defender.
SC-200 exam details
SC-200 exam cost and registration process
The standard SC-200 exam cost is $165 USD, but pricing may vary by country and testing center. Honestly, it's one of those things where you should click through the checkout once just to see the final amount, because taxes and regional pricing can surprise you.
Register through the Pearson VUE testing platform. You can schedule online proctored or in-person at a test center, and you'll pick your time slot based on availability. Scheduling is flexible: sometimes you can book 24 hours out, other times you're looking at several weeks, especially during end-of-quarter training rushes.
Discounts exist, but they're not magically applied. I mean, Microsoft Certified Trainers can get reduced pricing, Microsoft Partner Network members sometimes have benefits depending on the agreement, and students may qualify through academic programs. Corporate voucher programs are also a thing for enterprise training initiatives, so if you work at a bigger company, ask your manager or training coordinator before you pay out of pocket. Random note: vouchers can have expiration dates.
Cancellation and rescheduling are pretty reasonable. Free changes up to 24 hours before your appointment. Miss that window and you're usually eating the fee, so set a calendar reminder the day before and check your life situation.
Retakes are straightforward. After your first attempt, you wait 24 hours. After that, it's 14 days between attempts. Not gonna lie, that second wait can feel long if you failed by a hair, so plan your study schedule like you might need attempt two.
SC-200 passing score and scoring methodology
The SC-200 passing score is 700 out of 1000 on a scaled scoring system. Scaled scoring exists because not every exam form is identical, and Microsoft adjusts for difficulty differences across question sets, so your "raw correct answers" number isn't what you see at the end.
Scores are typically available immediately after completing online proctored exams, and test centers usually hand you results right away too. You also get a performance report that shows strength areas and domains requiring improvement, which is useful because it tells you where you were shaky, even if it doesn't tell you exactly which questions you missed.
One thing people trip on: there's generally no partial credit on most question types. Multiple response questions are the classic trap, where you must select all correct answers or you get nothing. Microsoft doesn't publish exact question weighting or the raw-score-to-scaled-score conversion, so don't waste time trying to reverse engineer it. Study the SC-200 exam objectives and get good at the skills.
Exam format, question types, and duration (what to expect)
Active testing time is 120 minutes. There's also about 30 minutes extra for tutorial, review screens, and the post-exam survey, and that time doesn't count against your testing clock. Still, budget more time on your calendar.
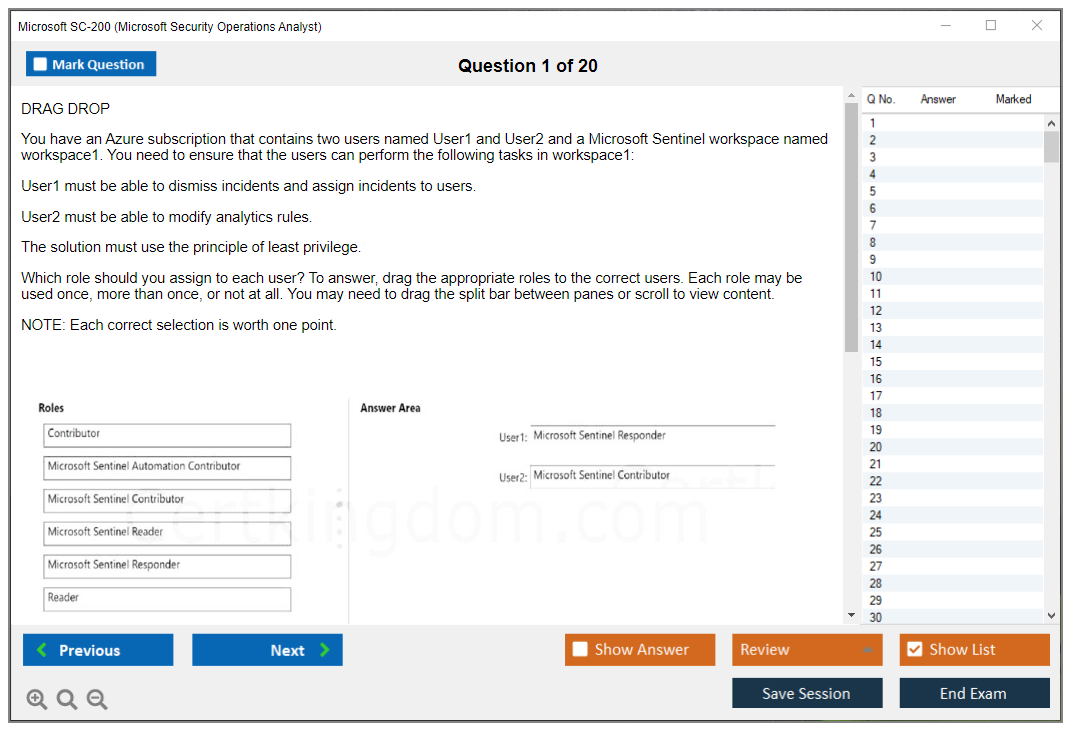
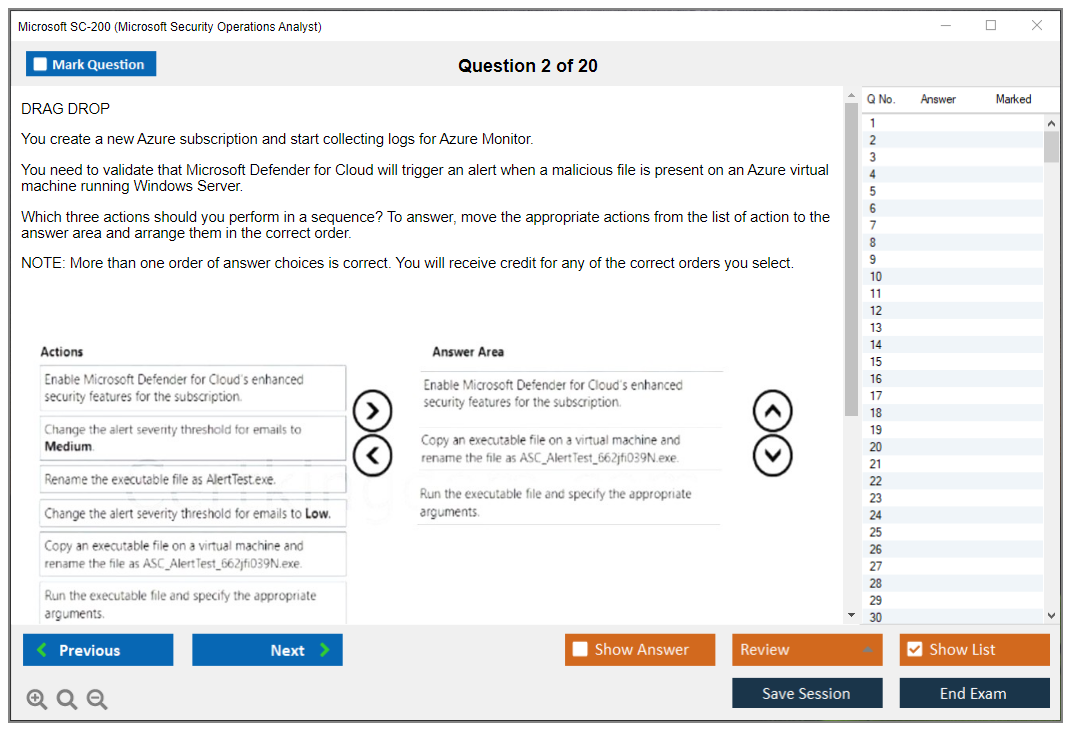
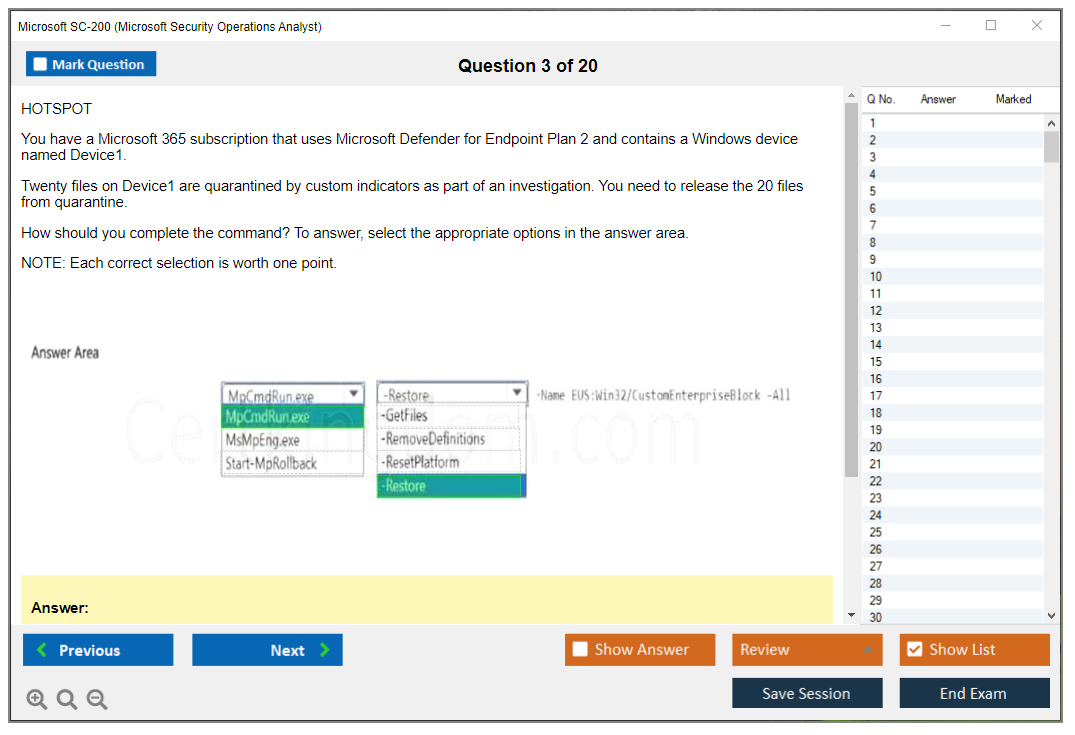
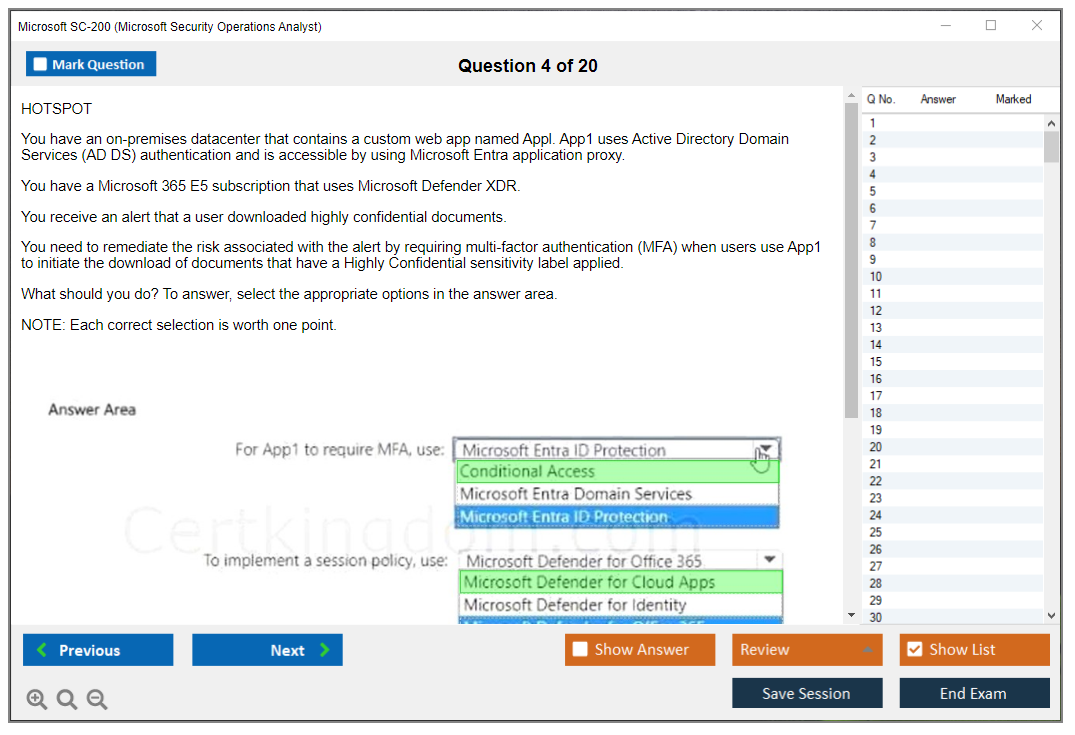
Question count is usually 40 to 60, depending on the form. Expect multiple choice, multiple response, drag-and-drop, case studies, and scenario-based questions. Case studies are where the exam starts to feel like real work: you get a business situation, current tooling, constraints, and then a set of questions that build on that scenario.
Active screen labs can show up too, which are hands-on tasks in simulated Microsoft environments. When they appear, they can be a time sink if you don't know where features live in the UI, so don't just memorize terms from a SC-200 study guide, actually click around Sentinel and Defender at least a little.
Important gotcha: in case study sections, you typically cannot mark questions for review and return later. You answer and move on. Calculator and notepad tools exist inside the testing interface, but you're not doing math-heavy work here, you're doing "read carefully and don't panic" work.
SC-200 difficulty (how hard is it and why)
SC-200 is considered intermediate.
It expects practical experience, and the hardest part is that the questions test application, not memorization. Knowing definitions won't save you when the prompt asks what to change in an analytics rule, which connector to configure, or where to investigate an entity, and it does it under time pressure with distractors that look almost right.
Kusto Query Language is a big deal here. Heavy emphasis. You need to read KQL quickly, know common operators, and understand how query changes affect results and performance. The thing is, query optimization matters more than people expect, because the exam loves to ask "which query returns X" or "how do you reduce noise," and a tiny change like 'has' versus 'contains' can flip the outcome.
You also need familiarity with multiple Microsoft security products and their integration points. Sentinel, Defender for Endpoint, Microsoft 365 Defender, identity signals, incidents, alerts, workbooks, automation rules, playbooks, and where each feature lives. Questions often include product UI screenshots, so interface familiarity helps, and the tricky distractors usually come from similar features across Sentinel and Defender platforms that sound interchangeable until you've actually used them in production. Or at least lab'd them thoroughly. Honestly, I've seen people with five years of traditional SIEM experience struggle here because the Microsoft ecosystem has its own internal logic, and memorizing feature names isn't the same as understanding the workflow.
Comparison: is SC-200 harder than SC-100, SC-300, or AZ-500?
SC-200 versus SC-100: SC-100 is expert-level and architecture-focused. SC-200 is operational and hands-on, more "what do you do during an incident" than "design the strategy."
SC-200 versus SC-300: different focus areas. SC-300 emphasizes identity. SC-200 covers broader security operations, including detection engineering and threat hunting.
SC-200 versus AZ-500: AZ-500 is about Azure security implementation, controls, and configuration. SC-200 is about detection and response workflows across Microsoft's security tools.
Microsoft doesn't publish pass rates, but community estimates often put first-attempt pass rates around 60 to 70 percent. Take that with a grain of salt. Difficulty depends on your background, and the main SC-200 difficulty factors are KQL proficiency, multi-product knowledge, and incident response experience.
Online proctored vs test center: choosing your exam delivery method
Online proctored exams mean you take it from home or the office with a live proctor watching via webcam. Test center exams are the classic Pearson VUE setup. Controlled room.
Fewer surprises overall.
For online testing, you need a quiet private room, stable internet, a webcam, and a government-issued ID. You'll also do a system check on Windows or Mac before exam day, and you should do it early, because nothing is worse than fighting permissions, camera drivers, or corporate endpoint controls 10 minutes before your slot.
Test centers are boring in a good way. No technical setup concerns, and if something breaks, there's immediate issue resolution. Online is pure convenience, flexible scheduling, no travel, and honestly great if you can control your environment.
Proctor communication for online exams is usually chat-based support. If you need to move out of frame, read the rules first. They can and will end the session if you do something that looks suspicious, even if you're just reaching for a charger.
SC-200 exam objectives, practice tests, and renewal requirements (quick notes)
The SC-200 exam objectives map to running a SOC in Microsoft land: manage a security operations environment, configure protections and detections, manage incidents and alerts, and perform threat hunting. If you're shopping for an SC-200 practice test, pick one that forces you to read long scenarios and interpret KQL, not just memorize trivia.
Renewal matters too.
SC-200 renewal requirements typically mean completing Microsoft's online renewal assessment during your renewal window, and it's focused on product updates and skills refresh, so if you stop touching Sentinel for a year, you'll feel it.
SC-200 FAQs
How much does the SC-200 exam cost?
$165 USD as the standard fee, with regional variations. Discounts may apply for MCTs, partner orgs, and students.
What is the passing score for SC-200?
700 out of 1000 on a scaled scoring model.
Is SC-200 harder than SC-100 or SC-300?
Harder than SC-300 for many people if they lack SOC experience and KQL. Easier than SC-100 because SC-100 is architect-level and more strategic.
What are the SC-200 exam objectives and skills measured?
Security operations environment management, detection configuration, incident and alert handling, and threat hunting across Sentinel and Defender tools.
How do you renew the Microsoft SC-200 certification?
Through Microsoft's online renewal assessment during the renewal period, focused on current features and updated workflows.
SC-200 Exam Objectives and Skills Measured
What the SC-200 exam actually tests
The SC-200 Microsoft Security Operations Analyst certification validates your ability to investigate, respond to, and hunt for threats using Microsoft's security stack. This is not one of those exams where you memorize definitions and call it a day. You need hands-on experience. You have to know Sentinel, Defender XDR, and KQL to pass.
Microsoft updates exam objectives regularly, so always check the official exam page before you start studying. The 2025 version breaks down into three domains with different weightings, and Mitigate threats using Microsoft Sentinel dominates at 50-55%, which tells you where to focus your prep time. Microsoft Defender XDR comes in at 25-30%. Defender for Cloud rounds it out at 15-20%.
All domains are tested. No exceptions.
There are no optional sections or specialization tracks you can lean on. You cannot skip Defender for Cloud just because it represents the smallest chunk. The weighted percentages indicate relative importance and roughly how many questions you will see from each area, but Microsoft does not publish exact question counts, which is frustrating.
Speaking of frustration, I once tried to reverse-engineer the scoring algorithm by tracking which sections felt harder during my first attempt. Completely useless exercise. Turns out perception and reality diverge pretty dramatically when you're stressed.
Mitigate threats using Microsoft Defender XDR
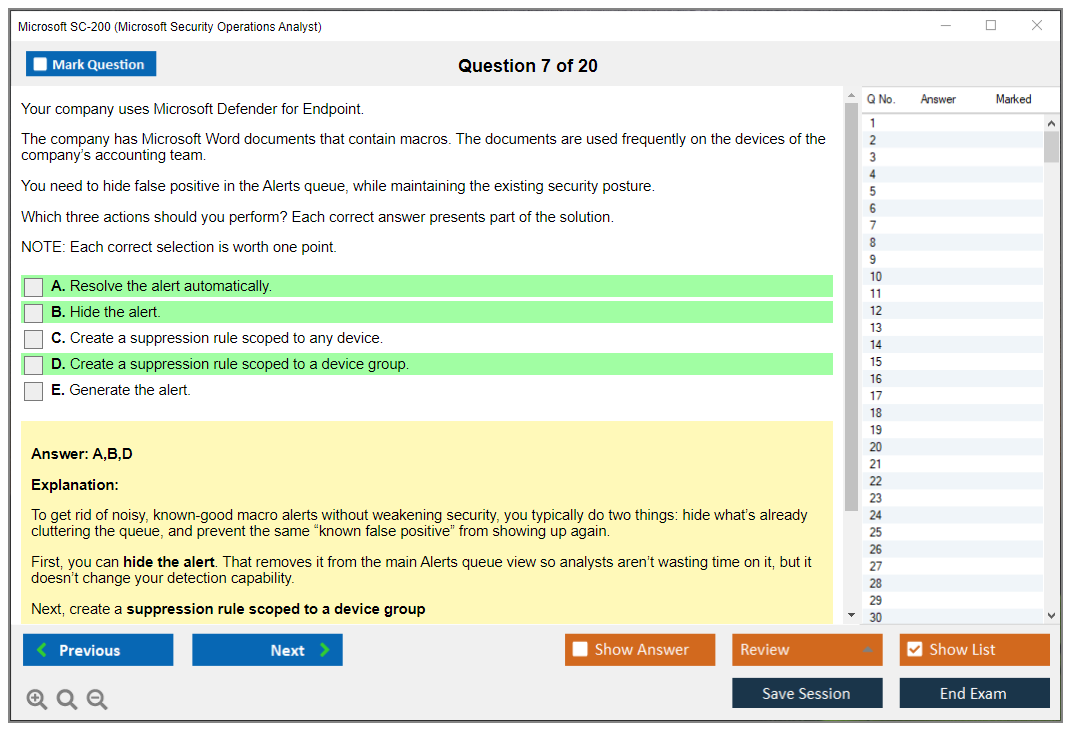
This domain covers incident management across Microsoft 365 Defender portal, which unifies alerts from endpoints, identities, email, and cloud apps. You need to manage incidents by assigning them, setting status, managing the incident queue. The exam tests whether you understand incident graphs and attack storylines, which visualize how an attack progressed across your environment.
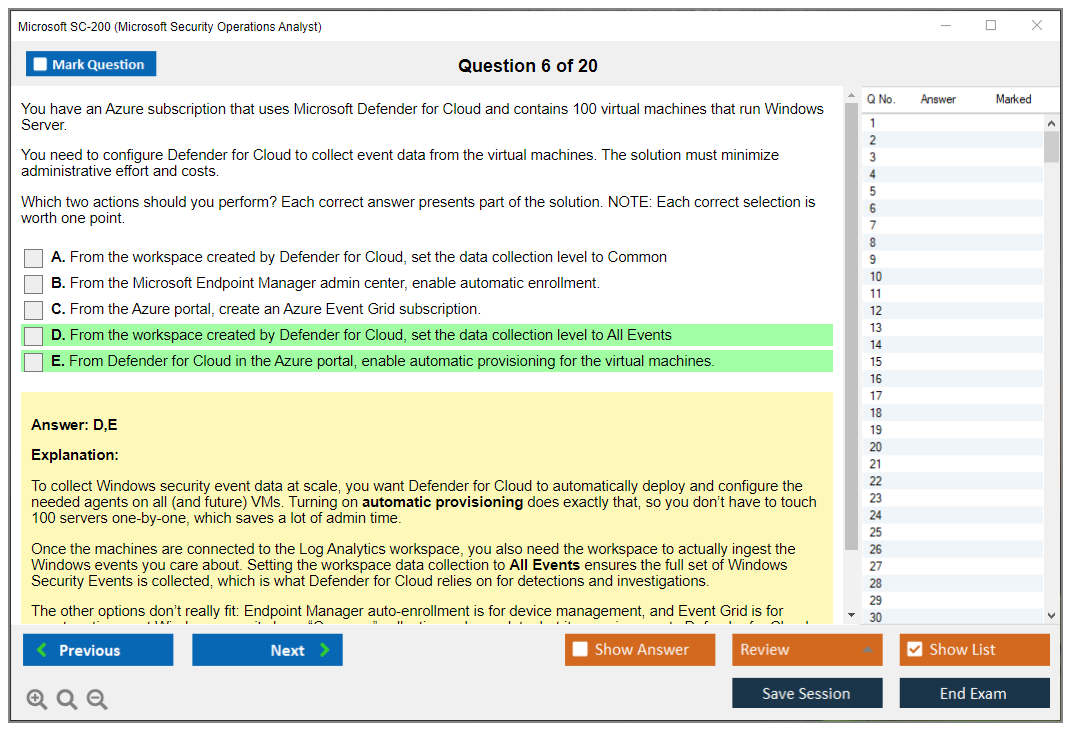
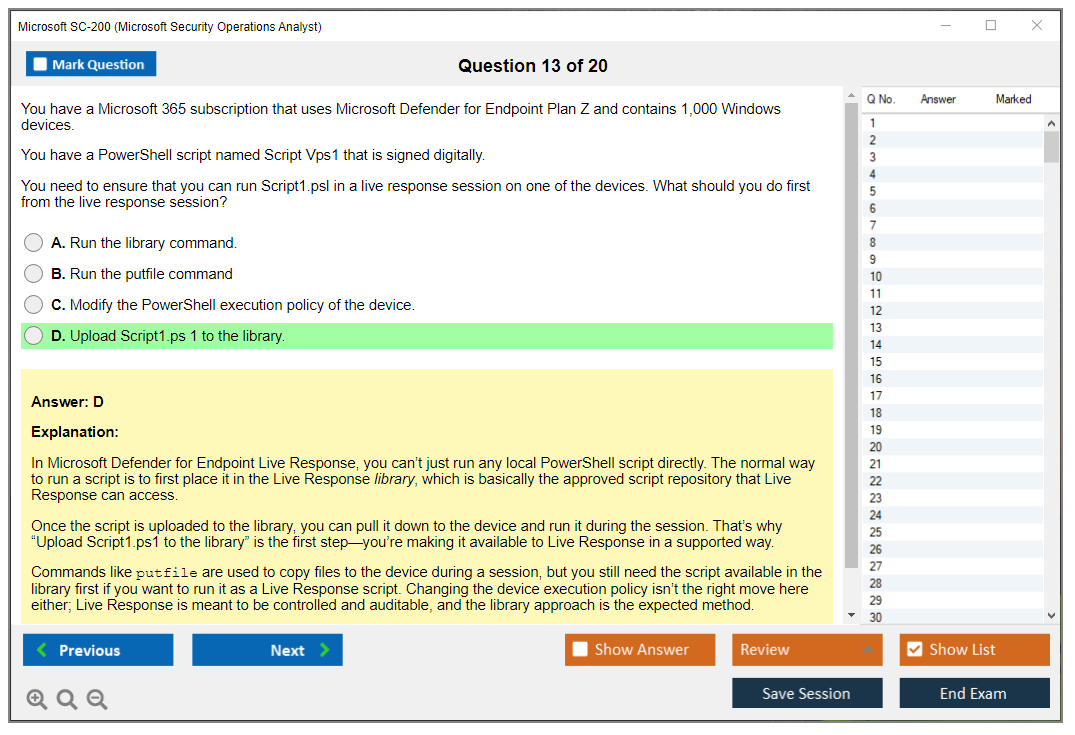
Microsoft Defender for Endpoint is a significant piece here. You need to know device isolation, file collection, and live response actions. Not just what they do, but when to use each one. Threat and vulnerability management recommendations come up frequently. How do you prioritize them? What do they actually mean for your environment? Attack surface reduction rules get tested too, along with reviewing automated investigations and approving remediation actions.
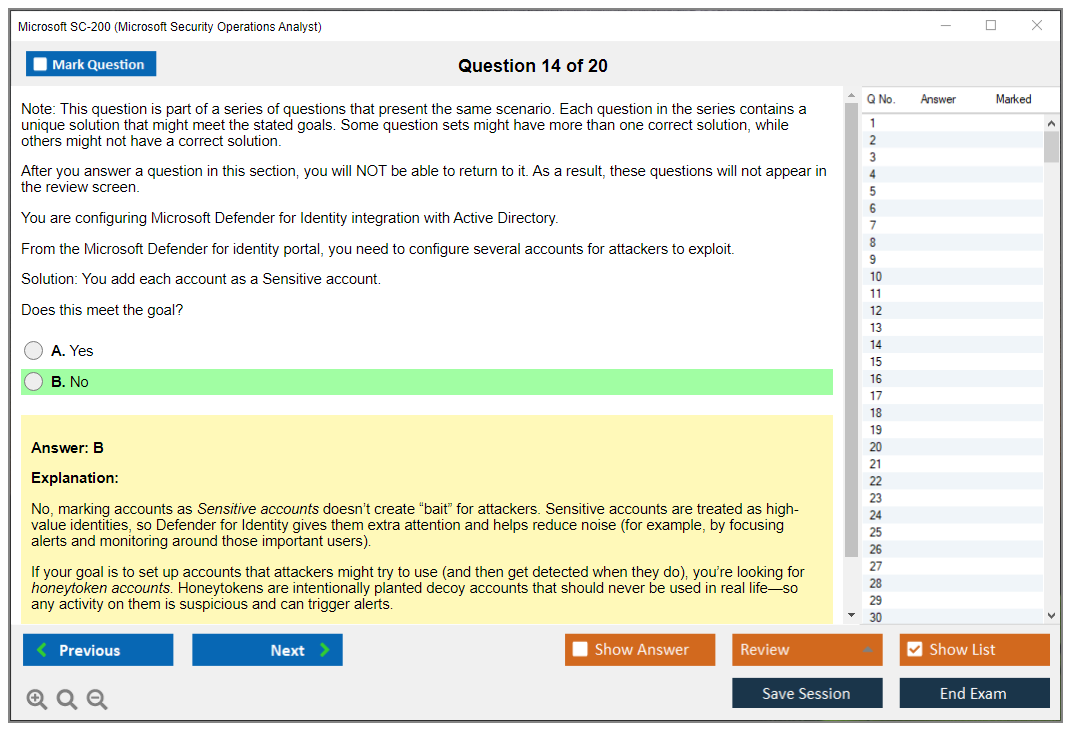
For Defender for Identity, you're looking at lateral movement detection and compromised credential alerts. The exam wants you to configure detection exclusions and understand identity security posture assessments. This is where a lot of SOC analysts struggle because identity attacks are subtle. They do not generate the obvious noise that malware does.
Defender for Office 365 covers phishing campaigns and malicious email threats. You use Threat Explorer and real-time detections to investigate, review email entity pages, analyze headers. Automated investigation and remediation for emails is testable content. Know how it works and when it triggers.
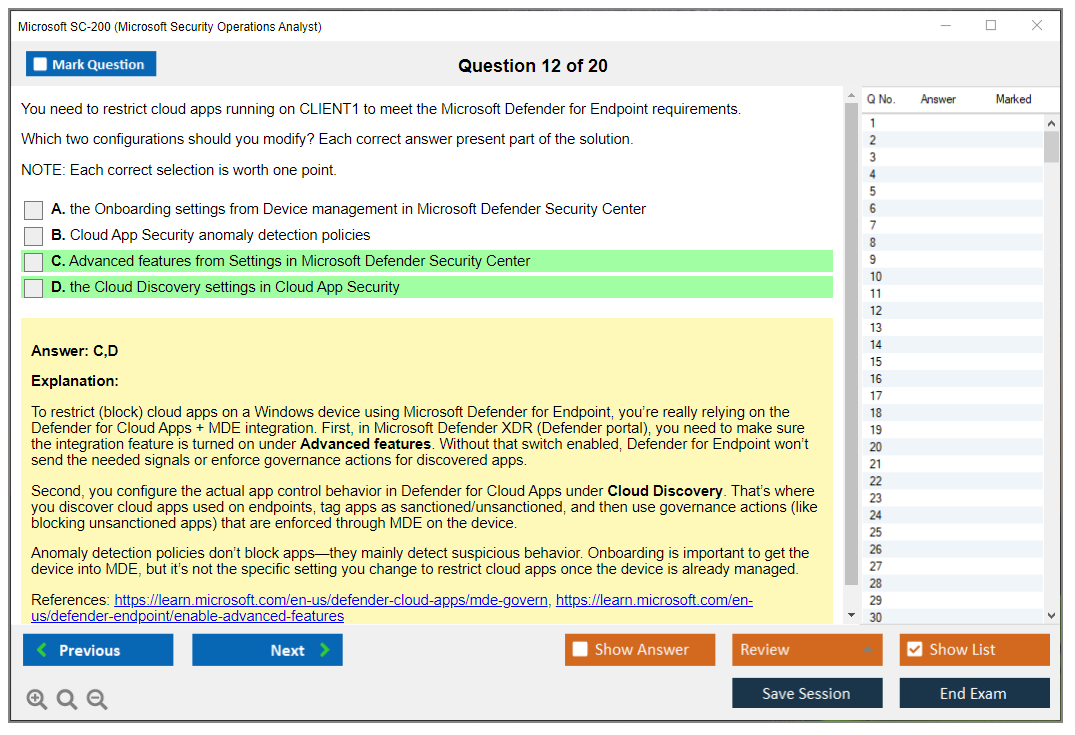
Defender for Cloud Apps rounds out the XDR domain. App governance and OAuth app risks are newer additions that trip people up. You need to investigate cloud discovery findings, understand shadow IT, create activity policies and anomaly detection policies.
Advanced hunting in Microsoft 365 Defender? Critical.
Write KQL queries across multiple data sources. The exam tests your understanding of the schema and table relationships. You cannot just memorize queries. You need to understand how IdentityLogonEvents relates to DeviceProcessEvents and when to join them. Creating custom detection rules from hunting queries is a practical skill you will definitely see tested.
Mitigate threats using Microsoft Defender for Cloud
This is the smallest domain but do not sleep on it. Design and configure Defender for Cloud settings means enabling Defender plans for Azure resources, hybrid servers, and multi-cloud environments. Auto-provisioning of agents and extensions comes up, along with workspace connections and data collection rules.
Secure score drives a lot of Defender for Cloud work. You prioritize recommendations using it, implement regulatory compliance standards, configure exemptions and grace periods. The exam wants you to understand the difference between Defender for Cloud and Azure Policy, which overlap but serve different purposes.
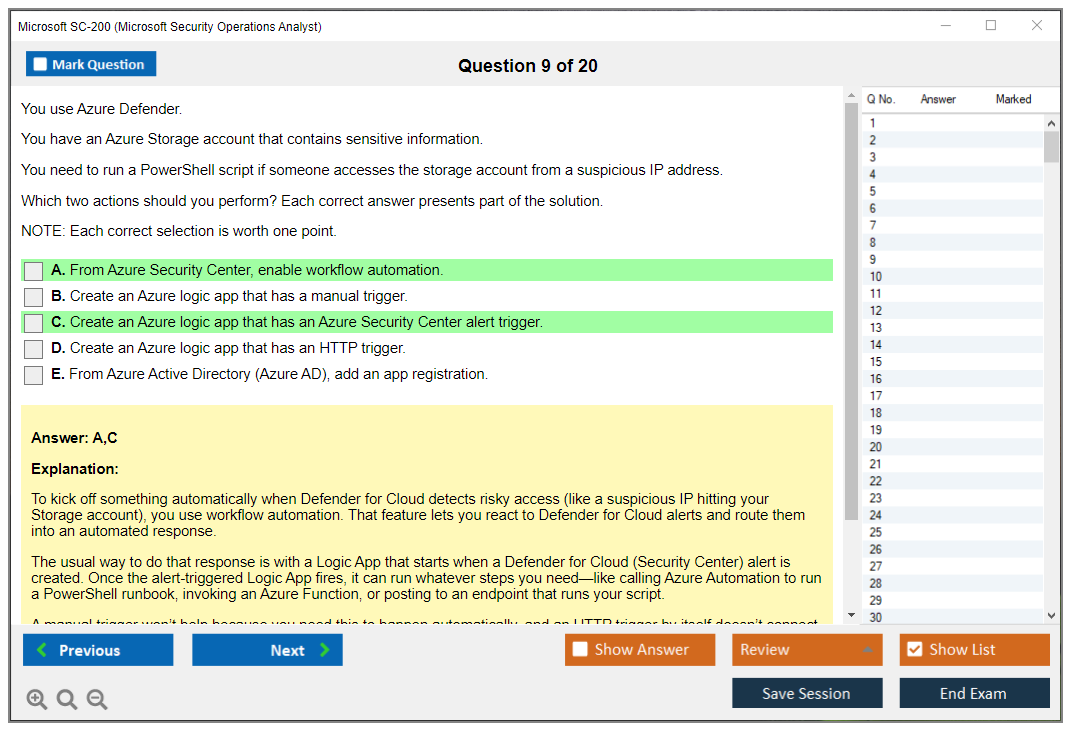
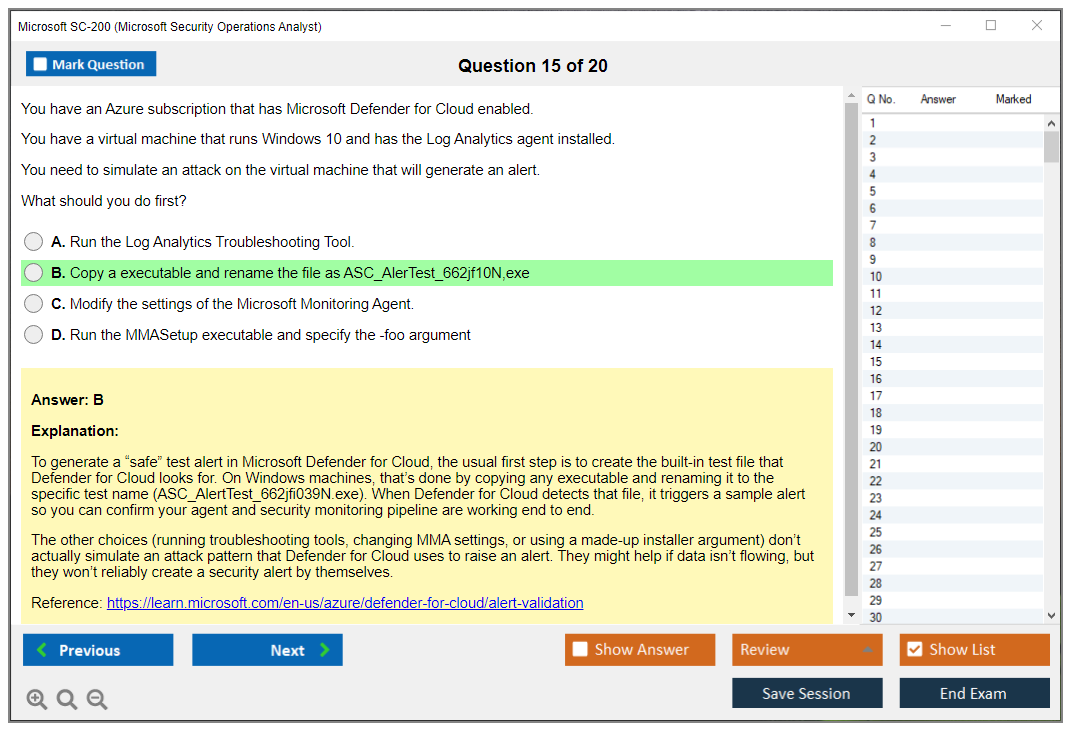
Security alerts require investigation using the Defender for Cloud alerts page. You suppress alerts, create suppression rules, configure email notifications. Workflow automation is where you create logic app playbooks triggered by Defender for Cloud alerts, implement automated responses to compliance findings.
Integrating Defender for Cloud alerts with Microsoft Sentinel is tested content because that is how most organizations actually use both products together. If you are studying for SC-200, you probably want to look at the SC-200 Practice Exam Questions Pack to see how Microsoft frames these integration scenarios.
Mitigate threats using Microsoft Sentinel
This is where you will spend most of your study time. 50-55% of the exam focuses on Sentinel, and it represents the most hands-on domain. Workspace architecture is foundational. Single versus multiple workspaces, when you need each approach. Configure workspace settings, retention, daily cap. RBAC for Sentinel gets complicated fast because you are layering permissions on top of Log Analytics workspace permissions.
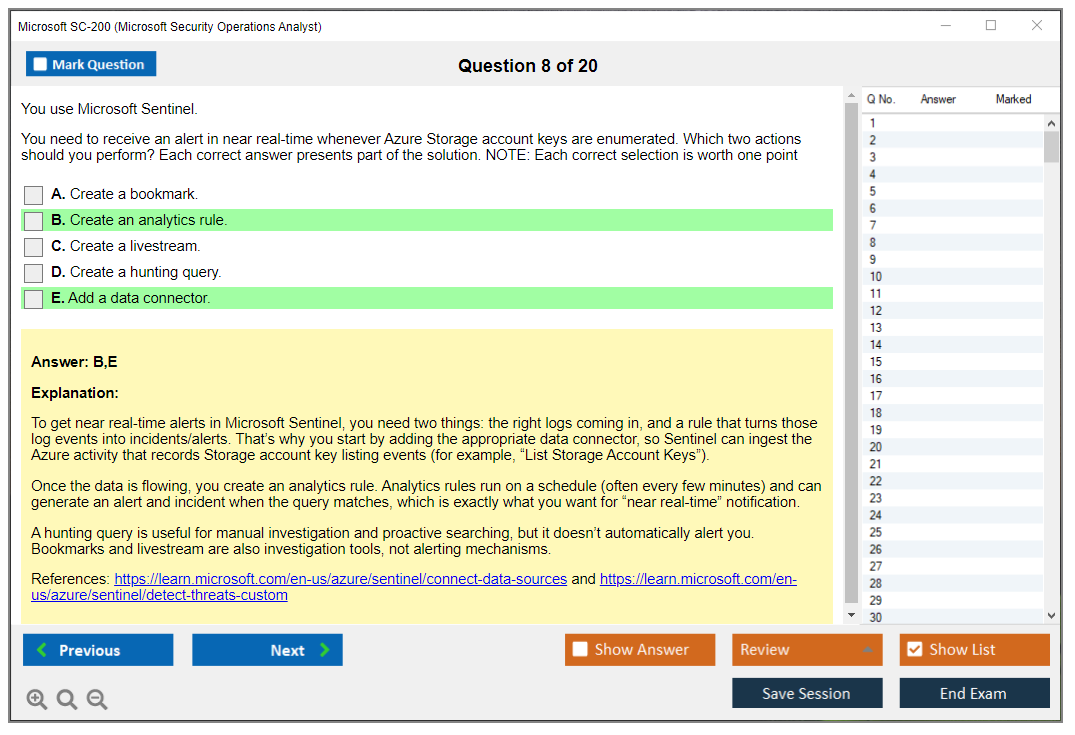
Data connector configuration is huge. Microsoft services, third-party solutions, custom sources. You need to know prerequisites and firewall requirements for each connector type. Common Event Format and Syslog collection trip up a lot of people. Custom log ingestion using Azure Monitor Agent and data collection rules is newer content that definitely appears on the exam.
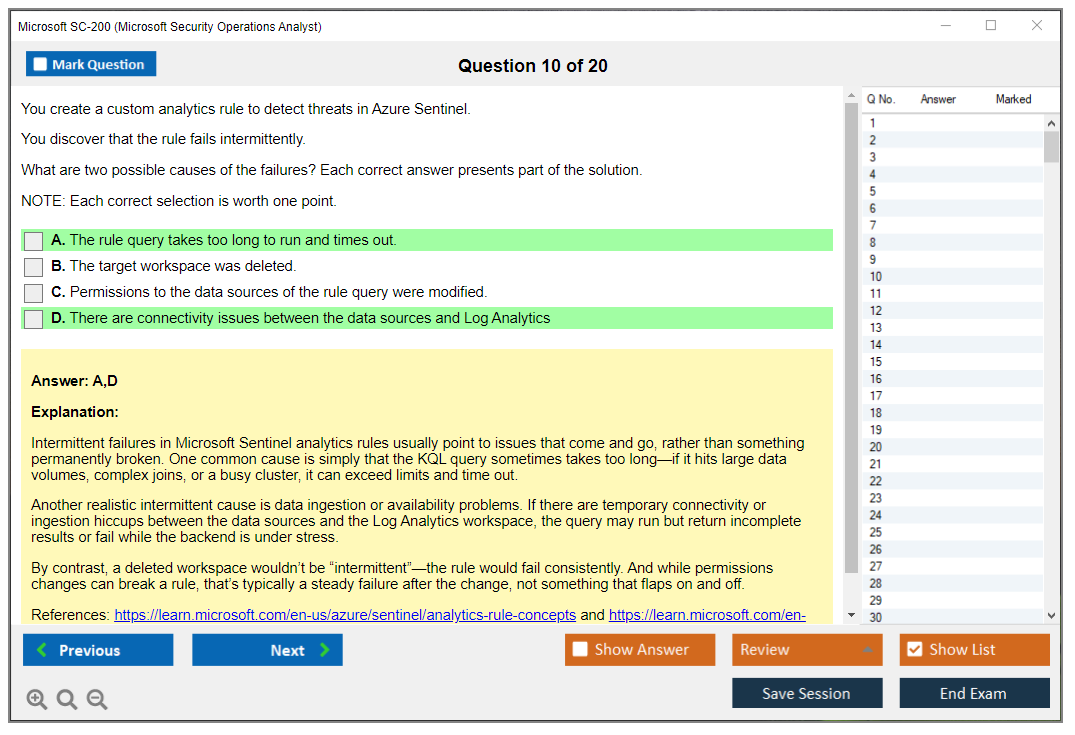
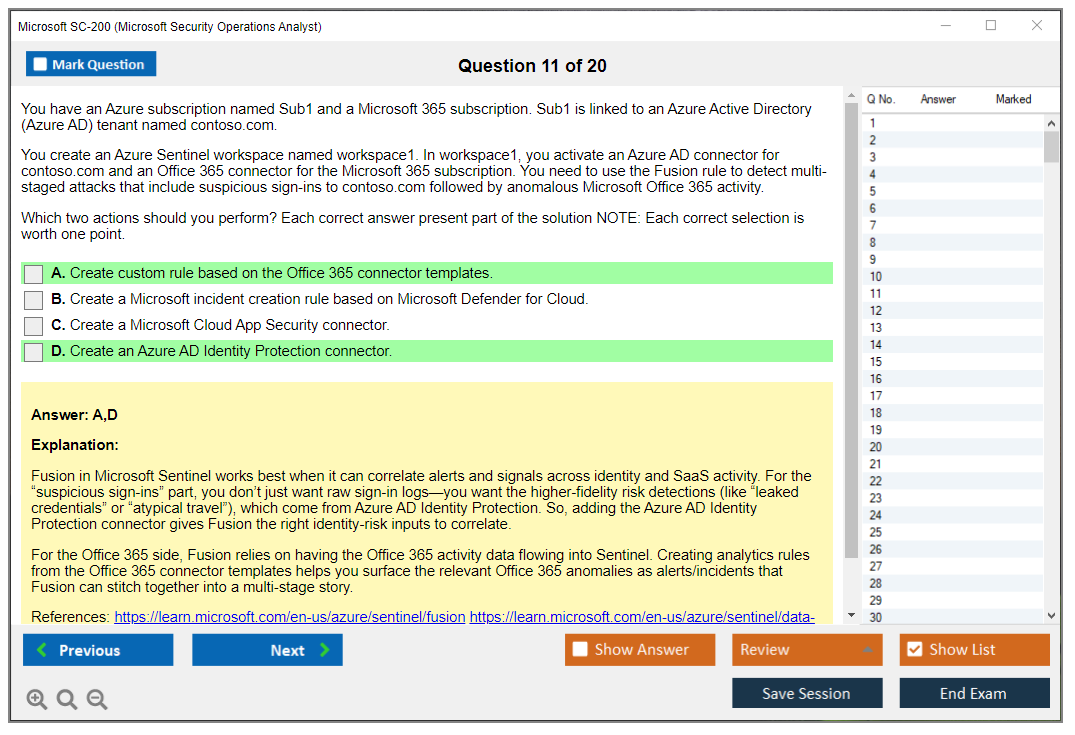
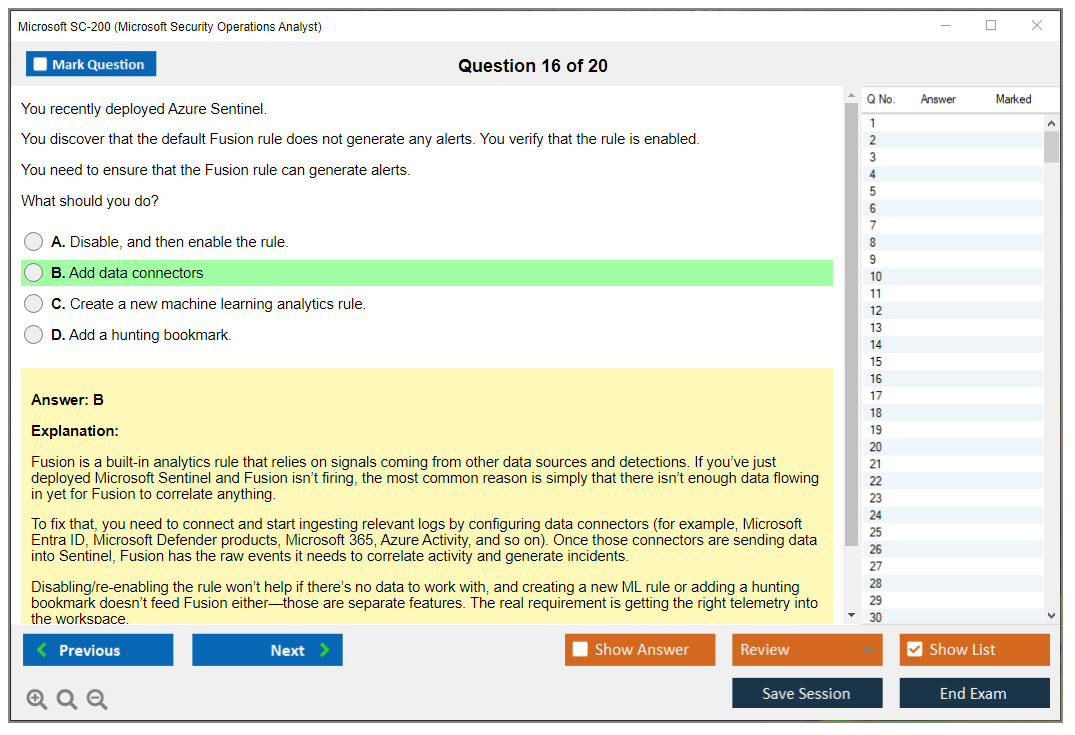
Analytics rules are core Sentinel functionality. Create scheduled query rules using KQL, configure entity mapping and alert enrichment. Near-real-time analytics rules have different limitations than scheduled rules, something people do not always realize. Microsoft security analytics rules and templates give you a starting point, but you need to tune them to reduce false positives. Fusion detection and machine learning behavior analytics work differently than rule-based detection.
Incident management in Sentinel overlaps conceptually with Defender XDR incident management, but the interface and capabilities differ. Triage, assign, update status. Investigation graphs and entity behavior are critical for understanding attack scope. Bookmarks let you save interesting findings during investigations. Automation rules handle incident assignment and enrichment automatically.
KQL is absolutely essential for SC-200. You cannot pass without solid KQL skills. Common operators like where, project, extend, summarize, join need to become second nature. You need to write queries using all of these. Time-based filtering and aggregations come up constantly in security queries. Parse operators extract fields from unstructured log data. The render operator creates visualizations, though that proves more useful for dashboards than incident response. Query optimization matters when you are dealing with terabytes of log data.
Security Orchestration, Automation, and Response means automation rules and playbooks. Automation rules handle simpler logic. If this alert fires, assign it to this team, add this tag. Playbooks use Azure Logic Apps for complex workflows. Configure triggers based on incidents, alerts, or entities. Microsoft Sentinel connectors in Logic Apps let you update incidents, add comments, block users. Approval workflows and notification actions are common playbook patterns.
Threat hunting is where you proactively search for threats instead of waiting for alerts. This is where you actually feel like a security analyst. Sentinel's hunting gallery provides pre-built queries, but you will create custom hunting queries for organization-specific threats. Bookmarks save interesting findings. You can promote hunting queries to analytics rules when you find a reliable detection pattern. Livestream lets you hunt in real-time as logs arrive.
Threat intelligence integration connects threat intelligence platforms to Sentinel, imports indicators manually or via TAXII feeds. Use threat indicators in analytics rules and hunting queries. Configure threat indicator matching and alerting so Sentinel automatically flags known-bad IPs, domains, file hashes.
Workbooks provide visualization and monitoring. Azure Monitor workbooks underpin Sentinel workbooks. Templates give you starting points for security monitoring. Interactive workbooks use parameters and drill-downs to explore data. The exam does not go super deep on workbook creation, but you need to understand when to use them versus hunting queries versus analytics rules.
How the exam actually works
Microsoft regularly updates exam objectives to reflect product changes. Sentinel gets new features every month. Defender XDR evolves constantly. Always verify the current version on the official exam page before you schedule. Cannot stress that enough. The exam costs $165 in the US. Passing score is 700 out of 1000, which is not a percentage. It represents a scaled score.
Question types include multiple choice, multiple select, drag-and-drop, case studies. Case studies give you a scenario and ask multiple questions about it. You cannot go back to case study questions once you move to the next section, which is annoying.
SC-200 difficulty sits somewhere between associate and expert level. It proves harder than AZ-900 or SC-900, but not as brutal as SC-100. If you are coming from a SOC background, the concepts make sense. If you are new to security operations? Expect a steep learning curve.
The exam assumes you have hands-on experience with the products. You cannot pass by just reading documentation. Microsoft Learn provides free training paths, but you need lab time. Set up a trial tenant, generate some security alerts, write KQL queries against real data.
Renewal happens annually through a free online assessment. Microsoft sends you an email when your renewal window opens. The renewal assessment covers product updates and new features added since you passed the original exam. It is not as hard as the full exam, but you still need to study.
Skills that actually matter for this exam
KQL proficiency makes or breaks your SC-200 attempt. Every domain tests it. Write queries that filter, aggregate, join, and parse data. Start with simple queries and build complexity. The DP-300 exam also covers query optimization if you want deeper database knowledge, though T-SQL and KQL are different languages.
Incident investigation is the core job function SC-200 validates. You need to understand attack patterns, know which logs contain relevant evidence, follow the attack timeline across multiple data sources. Practice with realistic scenarios, not just individual tool features.
Automation separates good SOC analysts from great ones. You cannot manually respond to every alert. Know when to use automation rules versus playbooks, how to design workflows that reduce analyst workload without introducing risk.
Threat hunting requires curiosity and creativity. The exam tests whether you can write effective hunting queries and recognize suspicious patterns. This skill develops over time. You cannot cram it the night before.
Most people study 4-6 weeks if they have SOC experience, 8-10 weeks if they are newer to security operations. Hands-on practice matters more than reading time. An hour in a Sentinel workspace teaches you more than three hours reading documentation.
The SC-200 Practice Exam Questions Pack helps you understand question formats and identify knowledge gaps. Practice tests are not a substitute for hands-on experience, but they show you how Microsoft asks questions about the products.
SC-200 Prerequisites and Recommended Experience
Official prerequisites (if any)
Here's the deal: Microsoft doesn't list official prerequisites for the SC-200 certification. None. Zero gatekeeping. You could book the Microsoft SC-200 exam today if you wanted.
But hold on. The thing is, the exam isn't written for total beginners, and Microsoft kinda hints at that without actually saying it out loud, you know? They recommend familiarity with Microsoft 365 and Azure services, plus a baseline understanding of security concepts and the threat space. But you won't see "must have X years" anywhere. The content assumes you've at least touched a SOC workflow before, because you're gonna get questions where you're expected to know what "triage" means, what matters first during an incident, and why a random alert is just noise versus an actual problem that'll ruin someone's weekend.
No enforced experience requirements exist on paper. Practical knowledge? Strongly advised. The exam's designed for professionals already working in security operations roles, or people training into that role who can replicate it in labs.
Recommended background (Azure, Microsoft 365, SOC workflows, KQL)
If you want the "what Microsoft expects but won't require" version, assume 6 to 12 months of hands-on time with Microsoft security solutions. Not "watched videos" time, but real clicking around, setting stuff up, breaking it, fixing it, and figuring out why the incident queue's full at 3 AM.
Start with basic networking. TCP/IP, DNS, firewalls, proxies. You don't need to become a network engineer, but you do need to understand what normal traffic looks like. Why is DNS always involved in something shady? And why a proxy log can save your life when someone asks which endpoint actually talked to that domain.
Then OS fundamentals. Windows admin basics plus a little Linux. You can pass with mostly Windows knowledge, but attackers don't care about your preferences, and logs don't either.
Cloud fundamentals matter way more than people expect. Azure and Microsoft 365 architectures show up constantly in the SC-200 exam objectives, because the tools you're working with are cloud-first and their data sources are cloud-first. If you don't know the difference between a tenant and a subscription, or how Log Analytics workspaces fit into Sentinel, you'll spend half the exam translating the question instead of answering it. Which is frustrating when the clock's ticking and you're on question 38 wondering why nothing looks familiar.
Identity and access management is another "silent prerequisite." You should know Azure AD (which is Entra ID now) at least at the basics level: users, groups, roles, conditional access, sign-in logs, audit logs, and what "privileged" means in practice. A ton of detections and investigations come back to identity. Because identity's the control plane attackers love.
You'll also want SIEM concepts. Not vendor-specific at first, just the idea of ingesting logs, normalizing, correlating, alerting, building detections, and doing case management. Add basic scripting if you can. PowerShell helps, Python helps. It's not required, but when you're staring at repetitive investigation steps and you know automation exists, you'll wish you had at least enough comfort to read a script and not panic.
Hands-on log reading? That's the difference between "studied SC-200" and "can do the job." You should be comfortable staring at sign-in logs, endpoint alerts, email events, cloud app activity, and then building a story from it.
Product knowledge for SC-200 success
This is where the Microsoft Security Operations Analyst certification gets very specific. You're expected to understand what each tool does, how it connects to the others, and what an analyst actually does inside them.
Microsoft Sentinel's a big one. Workspace management, data connectors, analytics rules, incidents, automation rules, watchlists, hunting. You should know how logs get into Sentinel, and what you can do when they arrive. If your only exposure's screenshots, you're gonna struggle when a question asks you to pick the right connector, the right table, or the right place to tune an alert.
Defender XDR's also core. The unified portal, incident investigation, and cross-product correlation. This is the "single pane" Microsoft wants you to live in, where endpoint, identity, email, and cloud signals get stitched together. You need to understand what an incident is, how alerts roll up, and what evidence and entities mean when you pivot.
Then the product-specific Defender stack shows up a lot. Defender for Endpoint covers device onboarding, threat protections, response actions like isolate device, collect investigation package, run AV scan, live response basics. This one is the bread-and-butter for many SOC teams. Defender for Identity monitors on-prem Active Directory with sensors, suspicious LDAP, lateral movement vibes. If you've never worked with AD, at least learn what "domain controller" means and why it's always a big deal. Defender for Office 365 handles Safe Links, Safe Attachments, phishing investigations, email message trace style thinking. Email's still how a lot of incidents start, so this isn't optional knowledge. Defender for Cloud Apps brings CASB capabilities, app discovery, session controls, cloud app governance. It's mentioned a lot, and it ties into "what are users doing in SaaS?" Defender for Cloud focuses on Azure workload protection plus security posture management, recommendations, secure score type concepts, and alerts tied to workloads.
Don't ignore Azure Monitor and Log Analytics either. Workspace concepts, data collection, basic querying. Sentinel's basically welded to Log Analytics, so if you don't get the workspace model, you'll miss easy points.
Kusto Query Language (KQL) proficiency requirements
KQL's heavily tested. Full stop.
You don't need to memorize every operator ever created, but you must understand basic query structure and common operators like "where", "project", "extend", "summarize", "join", "count", "bin()", and time filters. Expect questions where you read a query and explain what it returns, spot why it's broken, or choose the missing line. You should be able to interpret and modify existing KQL queries, and you should be able to write from scratch for simple detection scenarios, like "show sign-ins from risky countries for this user in the last 24 hours" or "find devices connecting to this domain."
Table schemas matter more than people realize. Sentinel tables, Defender tables, which table holds what. If you don't know where the data lives, you can't query it. And if you can't query it, threat hunting turns into guesswork.
Microsoft Learn KQL modules are worth doing before the exam. Not because they're fun, but because they map to how Microsoft asks questions. Practice in a demo Sentinel workspace or Log Analytics environment if you can. Even basic muscle memory helps.
If you're using a SC-200 study guide or a SC-200 Practice Exam Questions Pack, treat KQL sections like the main course, not the side dish. Same thing if you're doing a SC-200 practice test. When you miss a KQL question, don't just note the answer. Rebuild the query and understand why.
Security operations center (SOC) workflow experience
The exam assumes you understand the incident response lifecycle: detection, analysis, containment, eradication, recovery. That sounds academic until you realize the exam questions are often practical, like "what do you do next" and "what action reduces risk fastest without destroying evidence."
Alert triage and prioritization matters. You need a mental model for severity, confidence, scope, business impact, and whether something's active or historical. Experience with security monitoring and log analysis is basically the background music of the whole test.
MITRE ATT&CK shows up as well. It's not there for decoration. You should recognize common attack techniques and how detections map to them, especially when you're doing threat hunting in Microsoft tooling. Threat hunting concepts matter too: hypothesis-driven searching, pivoting between entities, and validating whether activity's benign or suspicious.
Automation and orchestration's another area people underestimate. Sentinel playbooks, automation rules, and basic "when this happens, do that" workflows. You don't need to be a Logic Apps wizard, but you should know what automation's good for and where it fits.
Metrics and reporting show up lightly, but they're part of real SOC life. Mean time to acknowledge, mean time to remediate, incident volume, false positive rate. Stuff your manager asks about.
Helpful related certifications (optional internal links)
If you're new to Microsoft security, SC-900's a great warm-up. It covers fundamentals that get assumed in SC-200, and it's good for career changers or anyone who's strong in IT but weaker in security vocabulary.
AZ-900 also helps. Not required, but it gives you the context for Azure concepts referenced in the SC-200 exam objectives, which makes Sentinel and Defender for Cloud questions less annoying.
MS-500 overlaps with Defender technologies and Microsoft 365 security administration. It's more admin-focused, while SC-200's operational, so don't treat it like a hard prerequisite. If you already have practical SOC experience with Microsoft tools, don't delay SC-200 just to collect more certs.
If you want extra reps before scheduling, a SC-200 Practice Exam Questions Pack can help you find weak spots fast, especially around KQL and incident flow. And it's cheaper than failing and paying the SC-200 exam cost again.
Self-assessment: are you ready for SC-200?
Quick gut check time.
Can you work through Microsoft Sentinel and Defender XDR portals without hunting through menus for ten minutes? Have you created or modified analytics rules and hunting queries? Can you write basic KQL queries to search security logs? Have you investigated and responded to security incidents using Microsoft tools? Do you understand the integration points between Sentinel and the Defender products, like how incidents correlate and how data flows?
If you answered "no" to most of that, don't panic. Just don't book the exam yet. Spend more time in hands-on labs, follow a solid SC-200 study guide, and use a SC-200 Practice Exam Questions Pack or another SC-200 practice test to pressure-test your skills.
People also ask about logistics, so here's the quick reality: the SC-200 exam cost varies by region, the SC-200 passing score is set by Microsoft and can change with exam versions, and the SC-200 renewal requirements are tied to Microsoft's renewal process (typically an online assessment). The bigger question's readiness. Because the exam's easiest when your day job already looks like the questions.
Best SC-200 Study Materials and Resources
Getting started with Microsoft Learn's free SC-200 path
Look, if you're serious about the Microsoft Security Operations Analyst certification, Microsoft Learn is honestly where you should start. It's free. The official learning path covers every single exam objective: mitigating threats using Microsoft Sentinel, managing incidents across Microsoft 365 Defender, and all the KQL queries you'll need to know. Each module comes with interactive exercises that actually help. You're not just reading theory and hoping it sticks.
The knowledge checks at the end of modules aren't super hard, but they give you a decent feel for how Microsoft phrases questions. The real SC-200 exam is trickier, but you need this foundation first. The self-paced format works if you've got a day job. You can knock out a module during lunch or spend a whole Saturday going deep on threat hunting techniques.
What the SC-200 exam actually tests
The SC-200 passing score is 700 out of 1000. Not gonna lie, that's a scaled score so you can't just count questions. Microsoft doesn't publish exact numbers but you're looking at probably 75-80% correct to pass comfortably. Exam costs $165 in the US, though pricing varies by region.
You'll face 40-60 questions in about 120 minutes. Mix of multiple choice, case studies, drag-and-drop scenarios. Some questions show you a Sentinel workspace screenshot and ask what KQL query would solve a specific detection problem. Others dump you into an incident response scenario across Microsoft Defender for Endpoint and expect you to know the next remediation step. These feel way more practical than your typical cert questions, which is refreshing.
The SC-200 exam objectives break down into four main areas. Managing a security operations environment means configuring data connectors in Sentinel, setting up analytics rules, understanding workspace architecture. Configuring protections and detections covers threat policies in Defender for Office 365, attack surface reduction rules, automated investigation responses. Managing incidents means triage, investigation workflows, remediation actions across the entire Microsoft security stack. Then there's performing threat hunting: writing KQL queries, using advanced hunting in Microsoft 365 Defender, proactive threat detection.
How SC-200 compares to other Microsoft security exams
People always ask: is SC-200 harder than SC-100 or SC-300? Different beasts entirely. SC-300 focuses on identity and access stuff like Entra ID, conditional access policies, privilege management. SC-100 is the architect exam, way more strategic thinking about security design across hybrid environments. SC-200 is hands-on operational work. You need to know how to actually investigate a compromised mailbox or hunt for lateral movement using KQL.
I'd say SC-200 sits somewhere in the middle difficulty-wise. Easier than SC-100 because you're not designing entire security architectures. Harder than SC-900 (the fundamentals exam) because you need actual technical skills. The KQL requirement trips people up. If you've never written queries before, that's a learning curve you can't skip.
Building your SC-200 study plan
Most people need 4-8 weeks depending on background. If you're already working as a SOC analyst with Sentinel experience, maybe you can compress it to 2-3 weeks of focused study. Complete beginners probably need the full 8 weeks, honestly maybe more if you're juggling work and life stuff.
Start with Microsoft Learn. Work through the entire official path. Don't skip modules even if you think you know the material. Then move to Microsoft documentation for deeper dives. The Sentinel documentation is massive but focus on data connectors, analytics rules, workbooks, and automation. For Defender, concentrate on Microsoft 365 Defender portal navigation, incident response workflows, and how the different Defender products (Endpoint, Office 365, Identity, Cloud Apps) integrate.
KQL practice is non-negotiable. Spend time in the demo Sentinel workspace Microsoft provides, or spin up a trial environment. Write queries for common scenarios like failed sign-ins, malware detections, suspicious PowerShell execution, lateral movement indicators. The SC-200 Practice Exam Questions Pack gives you realistic question formats for $36.99, which helps you understand how Microsoft tests KQL knowledge specifically.
I actually spent way too much time initially trying to memorize KQL syntax from documentation alone. Total waste. Turns out you need to just write the queries yourself, break them, fix them, see what errors pop up. That's how it sticks.
Hands-on labs and real-world practice
You can't pass SC-200 just reading documentation. The exam assumes you've actually used these tools. Microsoft offers some free lab environments, but they're time-limited. If your organization uses Microsoft security products, get access to the production environment (read-only if necessary) just to click around.
Practice creating analytics rules from templates in Sentinel. Investigate sample incidents in the Microsoft 365 Defender portal. Configure attack surface reduction rules and see what they actually block. Work through hunting queries in the advanced hunting interface. Start with Microsoft's example queries then modify them for different scenarios.
The exam loves case studies where you're given a security event and need to determine the correct investigation steps or remediation actions. These feel more like real SOC work than typical certification questions. You might see a phishing incident that compromised a user account, then spread to other mailboxes. Microsoft wants to know if you'd actually handle this correctly in production, not just whether you memorized some definitions. What's your triage priority? Which Defender tools do you use first? How do you contain it while investigating?
Understanding Microsoft Sentinel for the exam
Sentinel questions probably make up 40-50% of the exam. You need to know data connector types: which use APIs versus agents versus syslog. Analytics rules come up constantly. Scheduled queries versus Microsoft security alerts versus fusion rules. The exam tests whether you understand when to use each type.
Workbooks are visualization and monitoring tools. Playbooks are automated response workflows using Logic Apps. Don't confuse the two because exam questions specifically try to trick you on this. Know how automation rules differ from playbooks. Automation rules are simpler, trigger-based actions while playbooks are full Logic Apps workflows.
KQL query structure appears in multiple question formats. You might need to identify the correct query to find failed sign-ins from a specific IP range in the last 24 hours, or write a query that correlates security alerts with Azure activity logs. Practice common KQL operators: where, summarize, join, project, extend. Understand time functions because threat hunting always involves time-based analysis.
Microsoft Defender products across the exam
Microsoft 365 Defender (formerly Microsoft Threat Protection) is the integrated XDR solution. The exam expects you to understand how Defender for Endpoint, Defender for Office 365, Defender for Identity, and Defender for Cloud Apps work together in the unified portal. Incidents in Microsoft 365 Defender can contain alerts from multiple Defender products. You need to know how to investigate these correlated incidents.
Defender for Endpoint covers workstation and server protection. Know automated investigation levels, attack surface reduction rules, device isolation procedures. Defender for Office 365 handles email threats like anti-phishing policies, safe attachments, safe links. Questions about investigating compromised emails or configuring threat policies show up frequently.
Threat hunting in Microsoft 365 Defender uses the advanced hunting interface with KQL queries. Similar to Sentinel but focused on Microsoft 365 data. Practice common hunting scenarios: finding suspicious PowerShell executions, tracking file downloads from unusual locations, identifying credential dumping attempts. I've seen people who know Sentinel cold still struggle with the Defender hunting interface because it's slightly different enough to mess you up if you're not careful.
Practice tests and final preparation
The SC-200 Practice Exam Questions Pack helps you understand Microsoft's question style and identify weak areas. Don't just memorize answers though. Understand why each option is correct or incorrect. Microsoft changes exam questions regularly so memorization strategies fail.
About two weeks before your exam, take a full practice test under timed conditions. 120 minutes, no interruptions, no reference materials. Score it honestly. If you're hitting 75-80% or better, you're probably ready. Below 70%? Spend more time on your weak areas: usually KQL, incident response procedures, or specific Defender configuration scenarios.
Common mistakes people make include not understanding the difference between Sentinel and Microsoft 365 Defender (they're complementary but different), confusing automation rules with playbooks, not knowing KQL syntax well enough, missing questions about data retention and workspace management. The exam definitely tests operational details like how long Sentinel retains data in hot storage versus cold storage, or what happens when you delete a Sentinel workspace. Boring stuff, sure, but it's on there.
Renewal requirements after you pass
Microsoft certifications now renew annually through free online assessments. Six months before your SC-200 expires, you'll get access to the renewal assessment. It's untimed, open-book, and you can retake it if you fail. The renewal assessment focuses on updated features and product changes since you originally certified.
This is actually pretty nice compared to the old system where you had to retake entire exams every few years. Stay somewhat current with Sentinel and Defender updates. Read the "What's new" documentation every few months. When renewal time comes, review the renewal learning path Microsoft provides, take the assessment, and you're good for another year.
The SC-200 opens doors to SOC analyst roles, security operations positions, and threat hunting jobs. Organizations using Microsoft security stacks specifically look for this certification. Combined with related certs like AZ-500 or SC-300, you're building a solid security career foundation. Worth the effort if you're serious about security operations work in Microsoft environments.
Conclusion
Wrapping things up
Okay, real talk here.
The Microsoft SC-200 certification's absolutely worth chasing if you're really serious about security operations. The demand for folks who can actually work through Microsoft Sentinel, write decent KQL queries for security monitoring, and handle incident response in Microsoft Defender keeps climbing. Not gonna lie though, this isn't one of those exams you'd cram for over a weekend and expect to pass.
The SC-200 exam objectives cover a ton of ground. More than you'd initially think. You'll need hands-on experience with threat hunting in Microsoft 365 Defender, configuring detections, managing alerts across the entire Microsoft security stack. The SC-200 exam cost sits around $165 USD, and you've gotta hit that SC-200 passing score of 700 out of 1000. That number catches people off guard because the questions get pretty scenario-heavy. You're not just memorizing features. You're solving actual SOC analyst problems under time pressure.
Here's what I'd recommend: spend real time in the Microsoft Learn SC-200 learning path, but don't stop there. Get your hands dirty with Sentinel workspaces if you can access them through work or set up trial environments. Practice writing KQL queries until they feel natural because that skill alone will carry you through multiple exam sections. Might even save you when other areas get fuzzy. The SC-200 study guide materials are solid, but nothing replaces actually investigating incidents and building workbooks yourself.
I knew someone who spent three weeks just reading docs and felt ready. Scheduled the exam, walked in confident. Failed by like 80 points and had to wait two weeks to retake it. That waiting period sucked for them.
Before you schedule your Microsoft SC-200 exam, make absolutely sure you're testing yourself with realistic practice questions. A good SC-200 practice test will expose your weak spots, whether that's Defender configuration, Sentinel analytics rules, or the specific Microsoft 365 Defender incident response workflows. Too many people feel confident after reading documentation only to get blindsided by the exam format and question complexity.
And don't forget the SC-200 renewal requirements kick in after a year. Kind of annoying but also necessary. Microsoft expects you to stay current with their security tools through annual assessments, which actually makes sense given how fast these platforms evolve.
If you want to boost your chances of passing on the first attempt, I'd seriously check out the SC-200 Practice Exam Questions Pack. It'll give you the confidence you need and help identify exactly where you should focus your final prep hours before exam day.