ECCouncil 312-50v13 (Certified Ethical Hacker Exam (CEHv13))
ECCouncil 312-50v13 (CEHv13) Exam Overview and What It Certifies
What is the ECCouncil 312-50v13 CEHv13 exam and why it matters in 2026
The ECCouncil 312-50v13 CEHv13 exam? It's the gold standard for offensive security credentials. Sure, it's not the most brutally technical cert you'll find, but HR departments actually recognize it. That counts for more than people admit. The Certified Ethical Hacker version 13 validates that you understand attack vectors, penetration testing methodologies, and defensive countermeasures in a way that makes sense to both technical teams and business stakeholders who need to justify security budgets without getting lost in jargon.
CEH v13 in 2026 still holds weight. Government agencies want it. Defense contractors literally put it in job requirements because it satisfies DoD 8570/8140 baseline requirements. Fortune 500 companies ask for it because their compliance frameworks mention it by name. The certification proves you know how attackers think and operate, which is half the battle in security. Maybe more.
What separates ethical hacking from the malicious kind in a professional context? Documentation and authorization. That's it. The techniques are identical, which is kind of wild when you think about it. CEH v13 hammers this constantly. You're learning real attack methods, but the entire framework is built around getting proper permissions, defining scope, and reporting findings to help organizations fix vulnerabilities before the bad guys exploit them. I once watched a junior pentester almost lose a contract because he started scanning before the paperwork cleared. Not a mistake you make twice.
Roles and career paths CEH v13 certification prepares you for
Penetration tester. Obvious one. Security analyst positions love seeing CEH on resumes. Vulnerability assessor roles expect it at this point. Security consultant gigs, especially at the mid-level, treat CEH as table stakes.
Salary ranges vary wildly depending on market and experience, but CEH-certified professionals typically pull $75k-$95k starting out in most US markets. That jumps to $110k-$150k with 3-5 years of experience. Senior folks with CEH plus other credentials can hit $160k-$200k+ in high-cost-of-living areas or specialized industries. CEH alone won't get you FAANG money, but combined with practical experience and maybe a portfolio, it opens doors that'd otherwise stay closed.
Career progression usually goes junior analyst doing vulnerability scans and basic assessments, moving into mid-level penetration testing where you're actually exploiting systems and writing detailed reports. Then senior roles where you're designing security programs or leading red team operations that simulate advanced persistent threats across entire corporate networks. Some people branch into security architecture. The 312-50v12 was solid for this path, but v13 updated content makes the progression smoother.
Industries with highest demand? Finance needs CEH people constantly because of regulatory requirements that aren't going away. Healthcare is desperate for security folks who understand compliance frameworks like HIPAA. Government work practically requires it. Try getting a federal security job without it. Technology companies want it even if they claim they don't care about certs, because their clients ask about team credentials during vendor assessments.
Understanding the exam code structure: 312-50v13 explained
The 312-50 series represents EC-Council's flagship ethical hacking certification line. The "312" prefix groups all the ethical hacking related exams together in their portfolio, while "50" specifically identifies the CEH track, different from something like the 312-49v10 which covers forensics.
Version 13 brings updates over CEH v12 and earlier versions, particularly around cloud security, container technologies, and modern attack frameworks that actually reflect what penetration testers encounter in 2026 engagements. The 312-50v11 was getting dated with its treatment of IoT and operational technology security. V13 fixed that gap. The exam lifecycle typically runs 2-3 years before EC-Council releases the next version, so expect CEH v14 sometime around late 2027 or early 2028 based on historical patterns.
Backward compatibility? Interesting question. If you passed an earlier version like CEH-v11, you're still certified. You don't suddenly lose your credential or anything. However, the industry knows which version you hold, and some job postings specifically request "CEH v12 or later" to ensure current knowledge. Grandfathering policies let you maintain your certification through continuing education credits rather than retesting every cycle, which is nice.
EC-Council as the certifying body and vendor credibility
EC-Council's been in the cybersecurity training industry since 2001. They're not newcomers trying to cash in. Their position is unique because they focus specifically on security certifications rather than being a generalist training company that does networking, cloud, and security as afterthoughts. The 712-50 CISO certification and other offerings create a full career pathway if you want it.
ANSI/ISO 17024 accreditation matters more than people realize. This means an independent body verified that EC-Council's certification processes meet international standards for personnel certification programs. it's EC-Council saying their cert is valuable. There's external validation of the entire program structure, exam development process, and ongoing maintenance procedures by organizations that have no stake in EC-Council's success.
Global recognition is legitimate. I've seen CEH accepted in Europe, Asia-Pacific, Middle East markets without question or weird conversion requirements. Some regions actually value it more than North American employers do, which is interesting. EC-Council maintains exam relevance through industry advisory boards that include practitioners from major corporations, government agencies, and consulting firms who provide input on what skills actually matter in the field right now, not what mattered five years ago.
CEH v13 exam objectives alignment with real-world ethical hacking
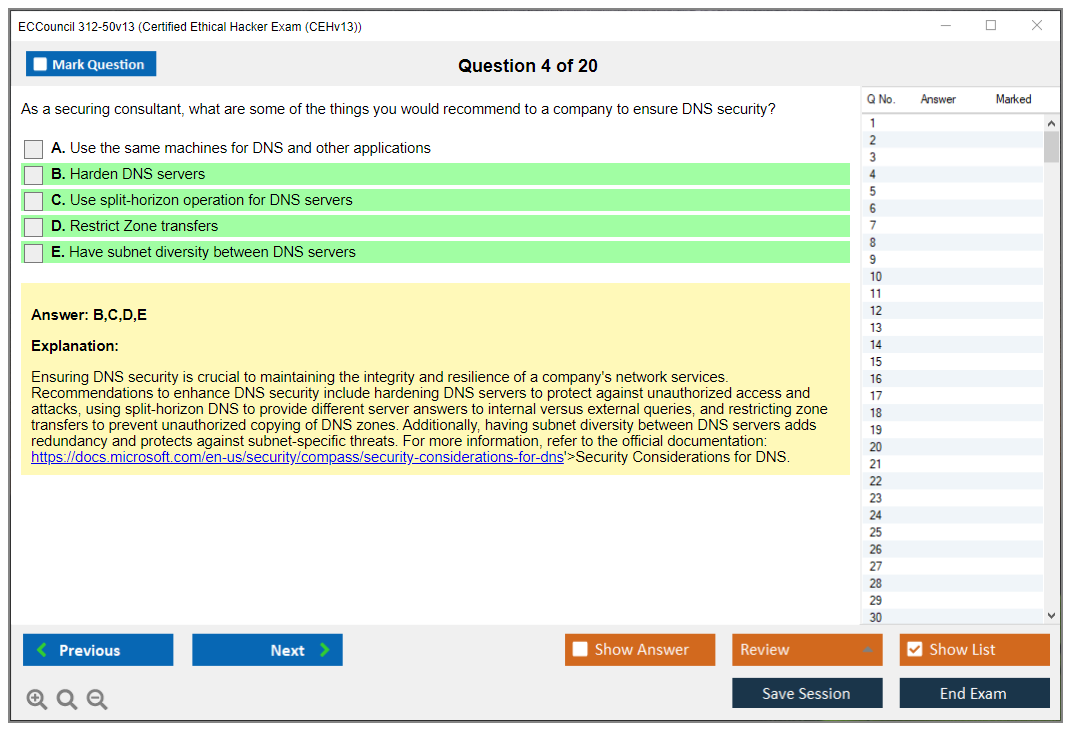
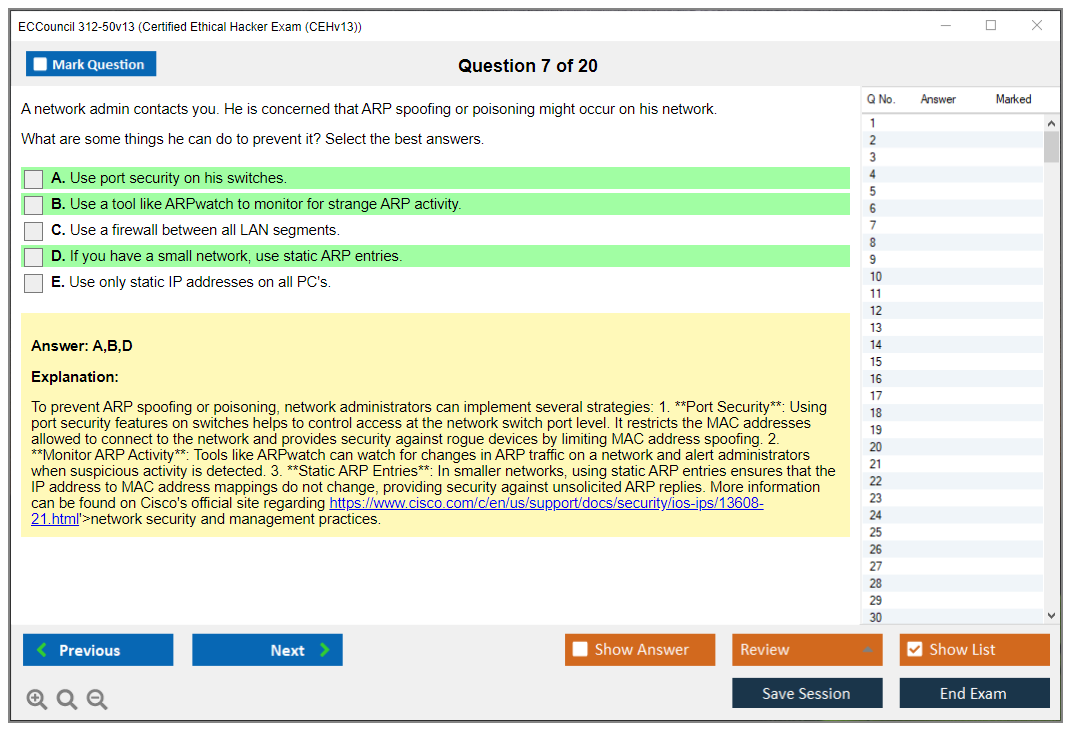
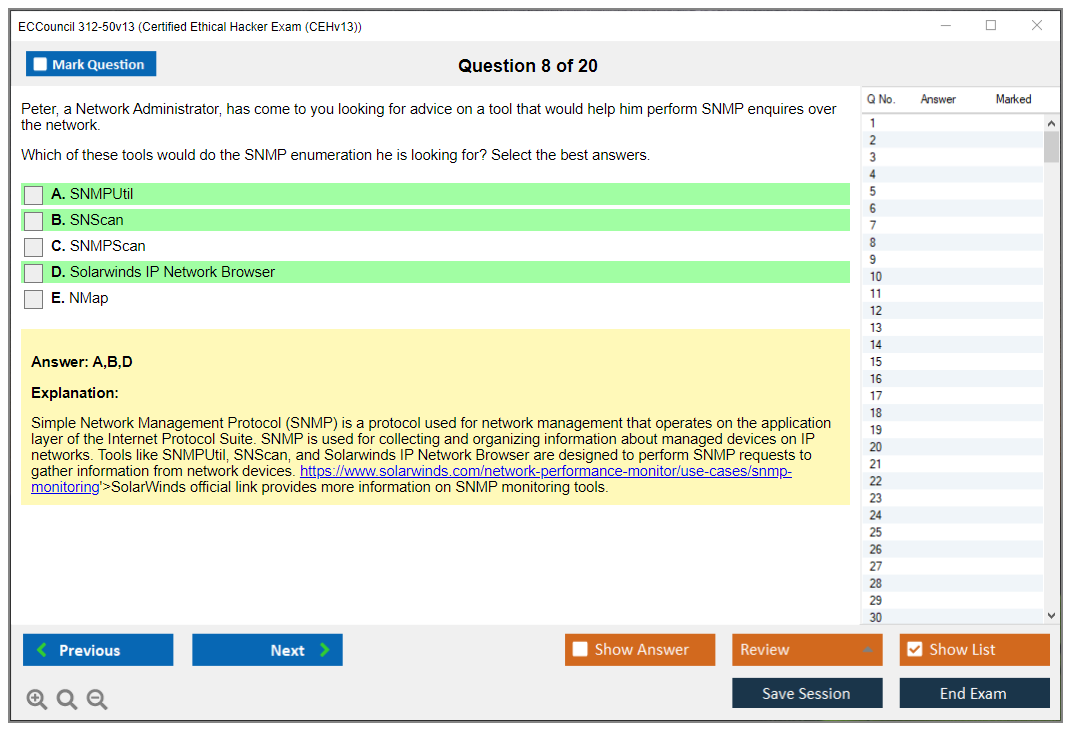
The exam covers modern attack techniques including cloud security testing, IoT device exploitation, and operational technology vulnerabilities. These aren't theoretical anymore. They're what you actually encounter in penetration tests for clients across industries. The balance between theoretical knowledge and practical tool proficiency is decent. You need to know why attacks work, not just memorize Metasploit commands like some script kiddie.
Exam content reflects the current threat space reasonably well, incorporating elements of the MITRE ATT&CK framework that most security teams use for threat modeling and incident response. The pairing of defensive thinking alongside offensive techniques is what makes CEH different from purely offensive certifications. You're expected to understand not just how to exploit a SQL injection vulnerability, but also how to recommend proper parameterized queries and input validation as countermeasures that developers can actually implement.
Wait, I should clarify something. The defensive component isn't just theory they tacked on. When you're in a client debrief explaining findings, you better have solutions ready. I've watched presentations where pentesters just dumped vulnerabilities without remediation guidance and clients looked lost. That's where CEH's balanced approach actually helps.
Certified Ethical Hacker v13 syllabus scope and breadth
Twenty full modules. Everything from initial reconnaissance through post-exploitation and covering tracks. It's really broad. Maybe too broad for some people's taste. The focus on methodology rather than tool-specific memorization means the knowledge stays relevant even as specific tools evolve or disappear. Tools change constantly in this field, but the methodology of information gathering, scanning, enumeration, exploitation, maintaining access stays consistent across engagements.
Cross-domain knowledge requirements span networks, systems, applications, and wireless technologies. You can't just be a web app specialist or a network guru. You need foundational understanding across all domains or you'll struggle with certain modules. Updated content addressing AI/ML security, container security, and emerging technologies like blockchain attack surfaces keeps the certification from feeling outdated six months after you pass, which happened with some earlier versions.
Credential portability and international recognition
DoD 8570/8140 baseline certification acceptance? Huge for government contractors. CEH satisfies requirements for multiple job categories under these directives, which translates directly into job opportunities with federal agencies and contractors who can't hire you without approved certifications. International markets in Europe, Asia-Pacific, and the Middle East recognize CEH without needing regional equivalents or additional validation in most cases.
Compliance frameworks mention CEH by name sometimes, which is pretty wild. ISO 27001 implementations, PCI-DSS security testing requirements, HIPAA security assessments. Organizations pursuing these standards often look for CEH-certified staff because auditors understand what the certification represents without lengthy explanations. Reciprocity with other certifications exists informally. Many people hold CEH alongside 212-82 or 312-39 credentials, and continuing education programs often accept training that counts toward multiple certifications at once.
Value proposition: CEH v13 versus other ethical hacking certifications
Compared to OSCP? CEH is broader but less technical. No question. OSCP demands you actually pop shells during a practical exam that's really challenging. CEH tests knowledge through multiple choice and scenario-based questions, which some people dismiss as easier. GPEN from SANS covers similar material but costs way more and ties you into the SANS ecosystem. PenTest+ from CompTIA is closer in difficulty but lacks the brand recognition CEH has built over two decades of market presence.
When is CEH the right choice? If you're building foundational knowledge, transitioning into security from another IT role, or working in environments where the certification name matters more than deep technical skills that you'll develop on the job anyway. For pure technical depth, something like OSCP or ECSAv10 makes more sense. CEH is foundation for advanced EC-Council credentials like Licensed Penetration Tester (LPT) or ECSA, creating a clear progression path if you stay within their ecosystem.
The ECCouncil 312-50v13 CEHv13 exam isn't perfect. But it's established and recognized. That matters when you're trying to get past HR filters and into interviews where you can prove your actual skills matter more than any certification.
CEH v13 Exam Format, Structure, and Key Administrative Details
ECCouncil 312-50v13 (CEHv13) exam overview
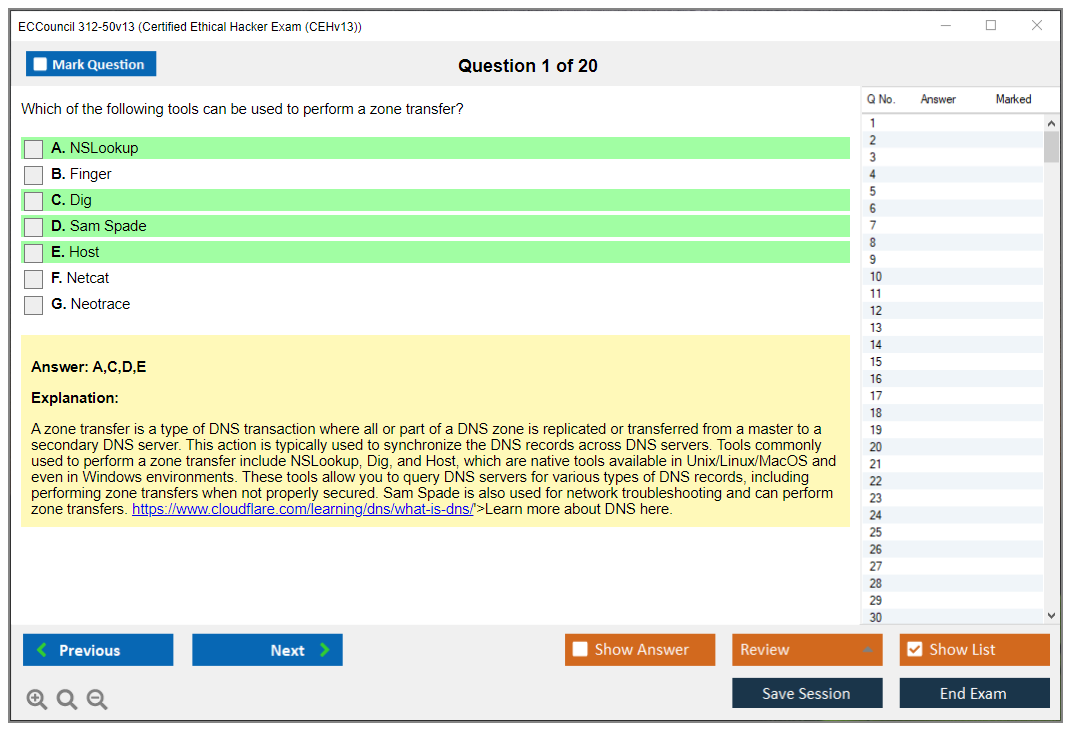
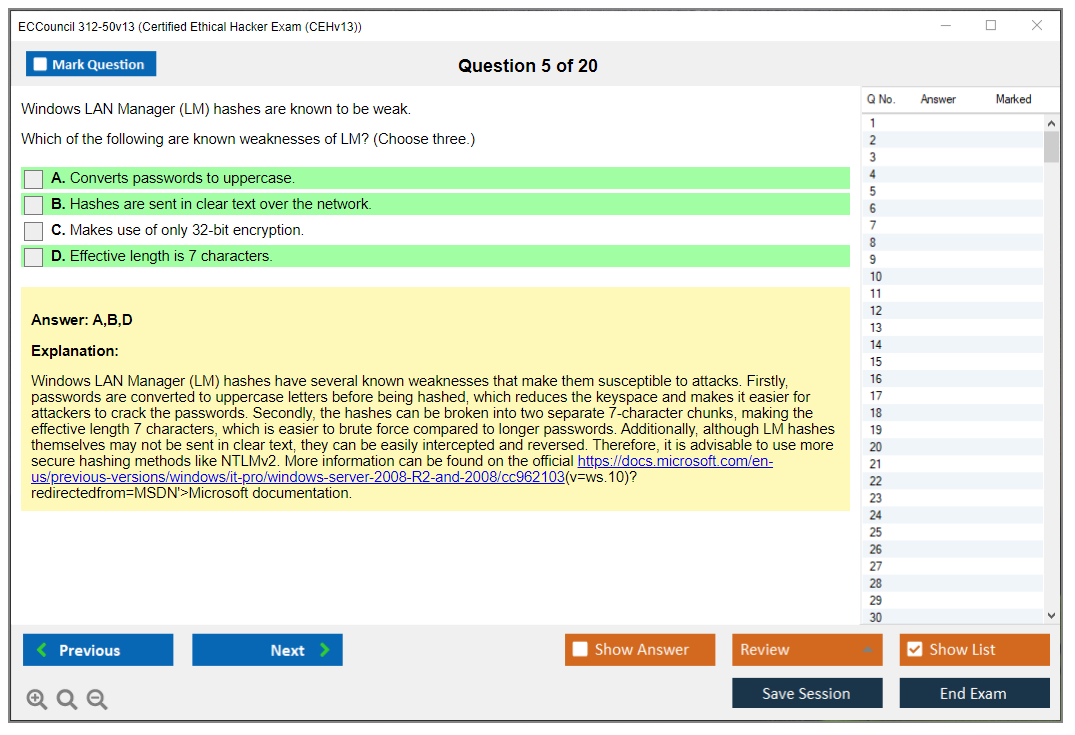
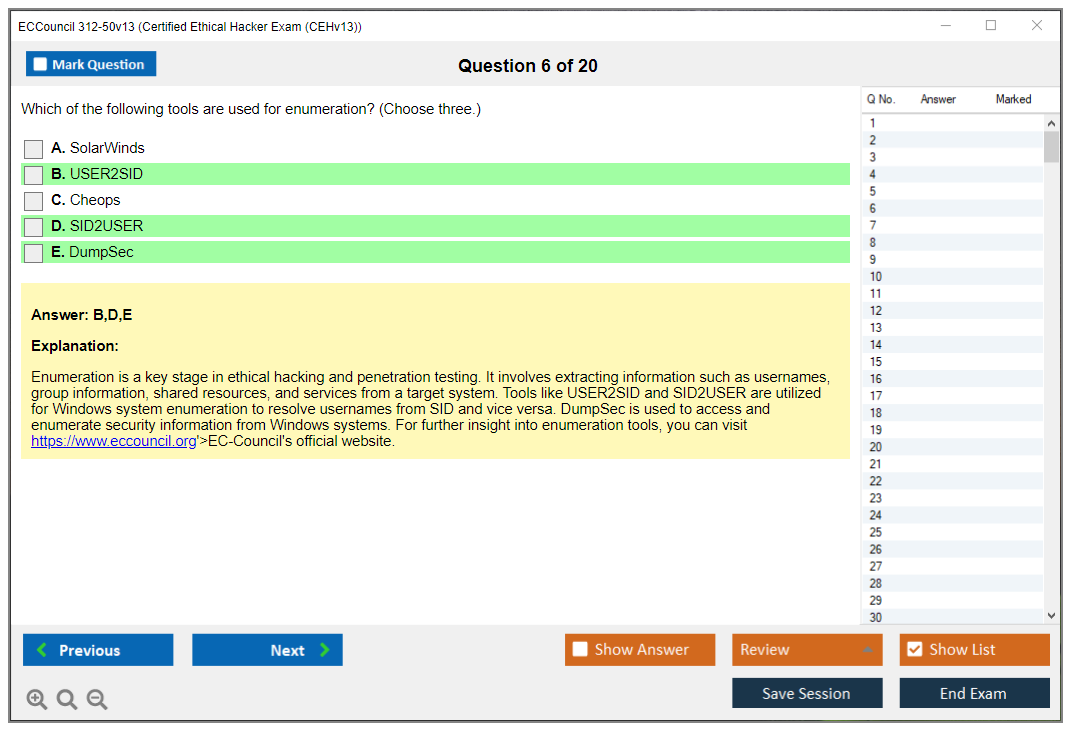
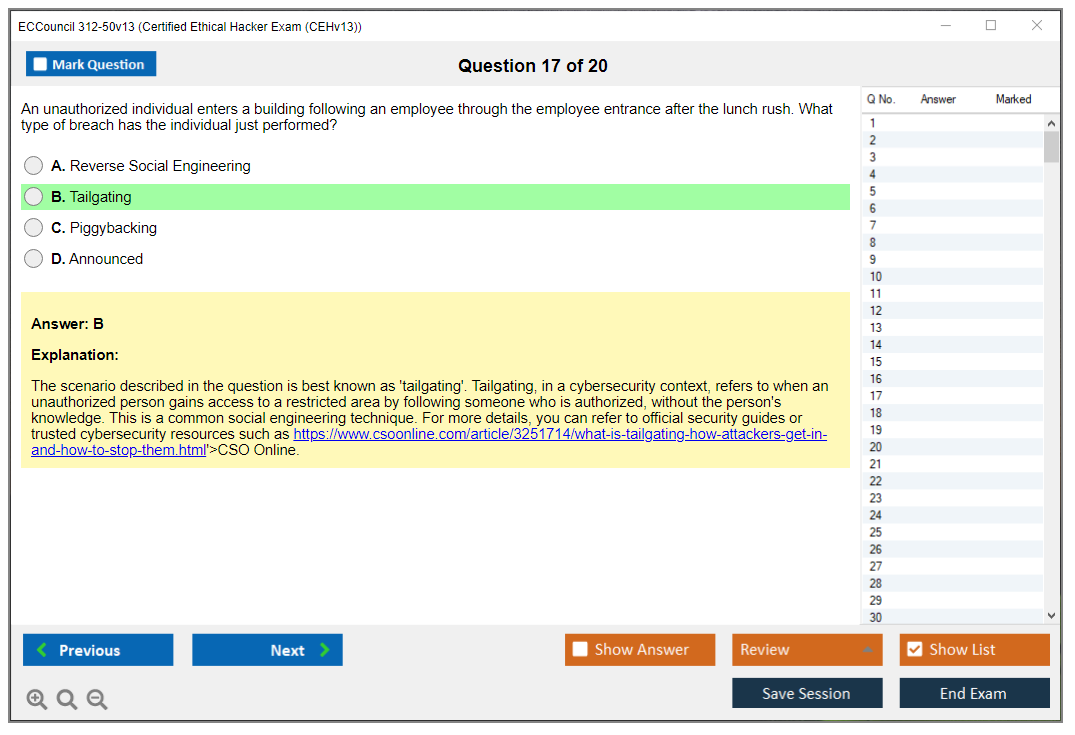
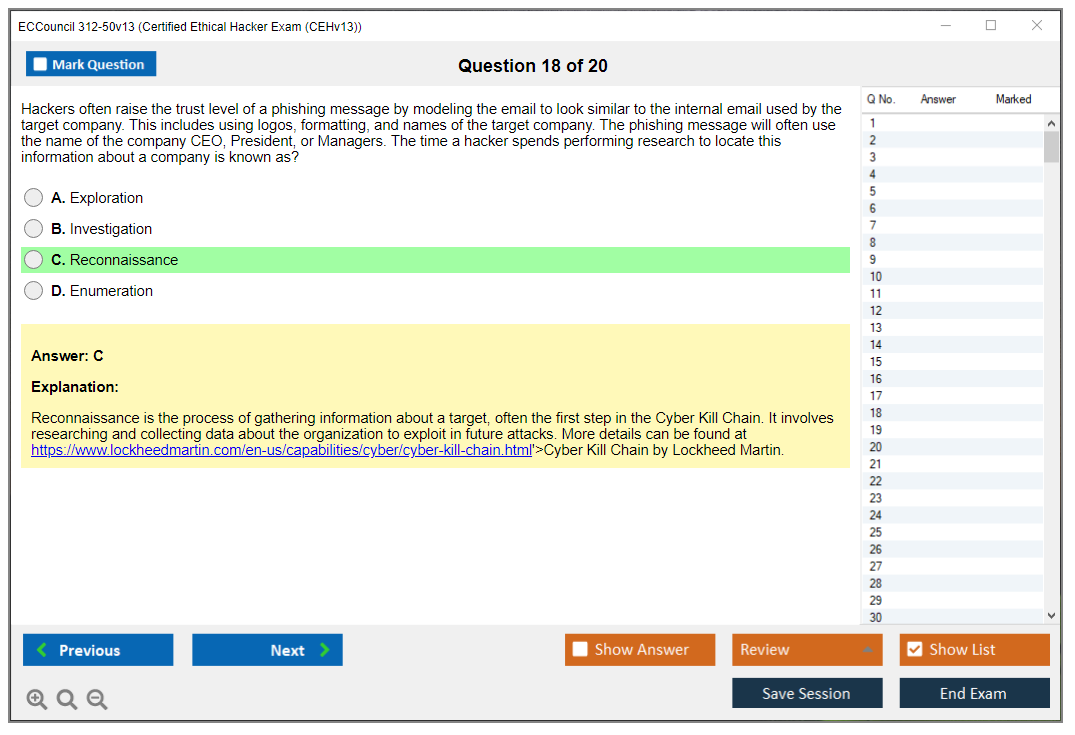
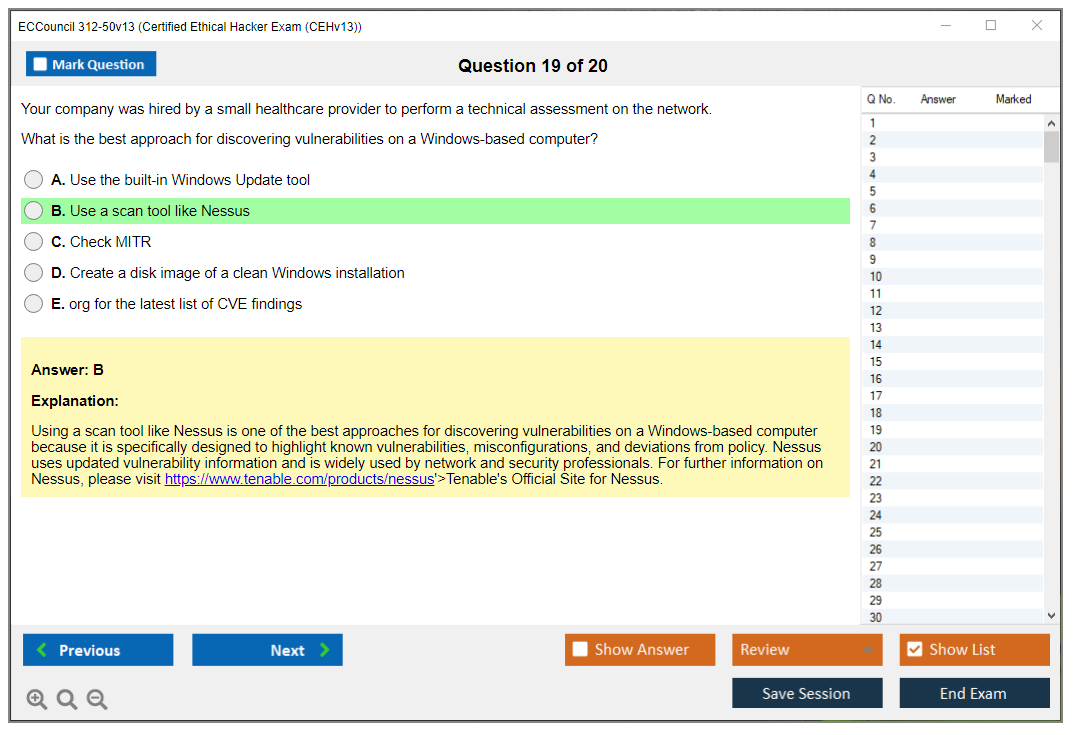
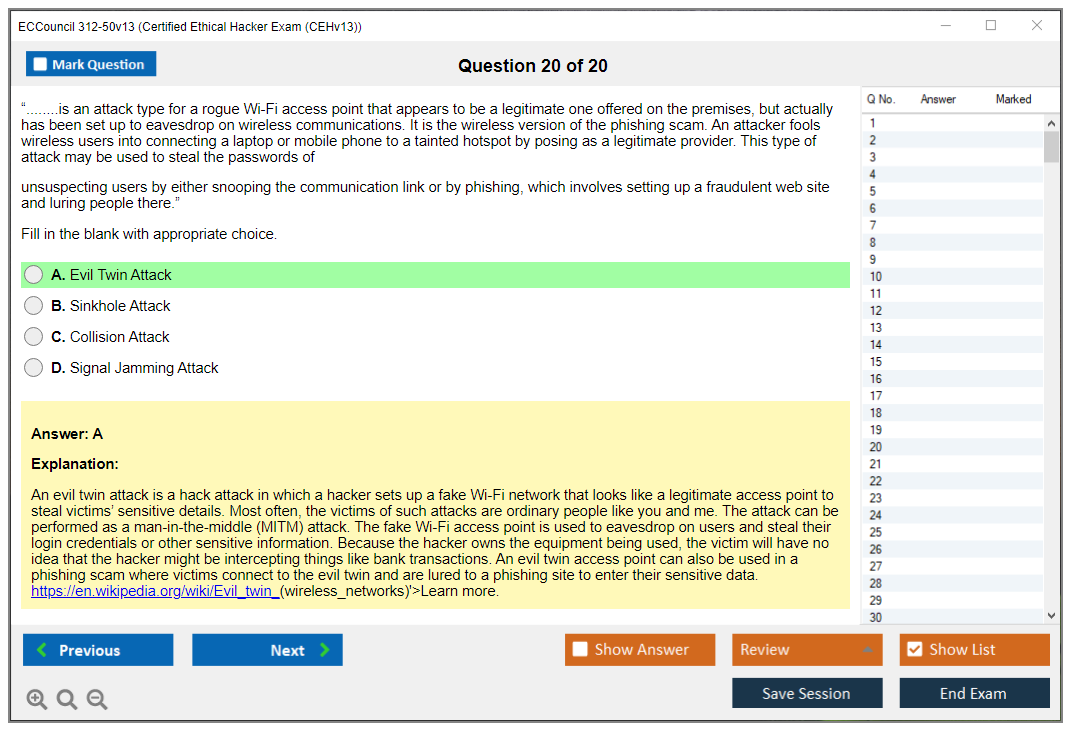
Look, the ECCouncil 312-50v13 CEHv13 exam is the multiple-choice Certified Ethical Hacker test most people mean when they say "I'm taking CEH." It's vendor-run, very blueprint-driven, and honestly, it rewards people who can recognize tools, terms, and attack flows quickly. Not people who can pop shells live on a keyboard. Short version? Lots of breadth. Plenty of trivia. I mean, there's just a ton of it.
CEH v13 certifies that you understand common offensive security concepts across recon, scanning, exploitation basics, web, cloud, and defensive hygiene, with enough vocabulary to talk to security teams without sounding lost. Hiring managers love it for checkbox reasons, and I've got mixed feelings about that. Some candidates love it because it gives structure. Others hate it because the "real hacking" part is mostly adjacent. Both takes are fair.
I knew someone who passed CEH v13 after failing twice, and what finally clicked for him wasn't "studying harder" but changing how he read the questions. He stopped trying to answer what he thought they were asking and started answering what they actually wrote. Sounds obvious, but the wording on this exam can mess with your head if you're used to doing the work instead of talking about the work.
CEH v13 exam format and key details
Number of questions, question types, and time limit
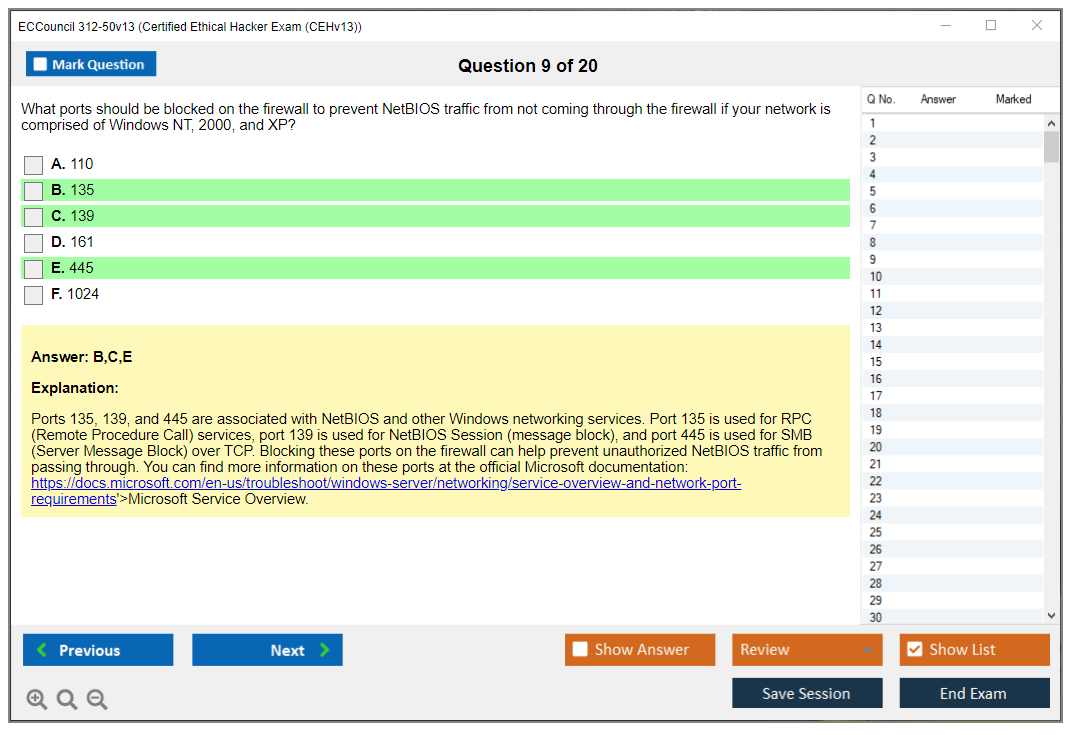
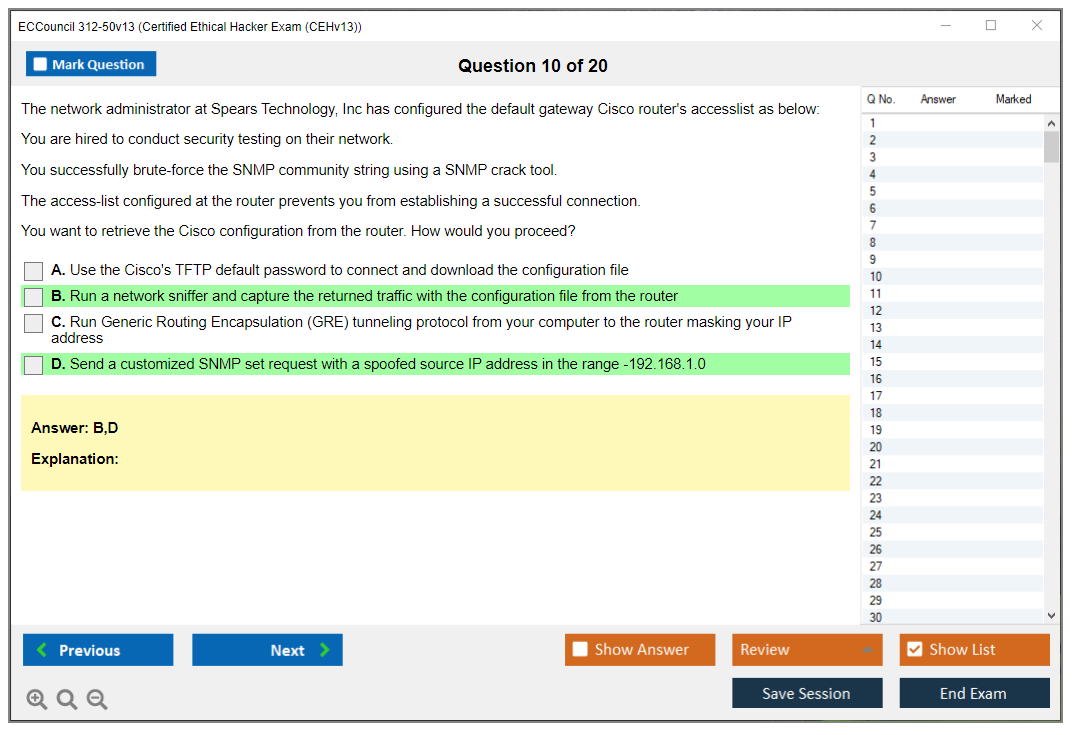
The standard CEH 312-50v13 exam is 125 questions, mostly classic multiple-choice. That's the number you should plan for, anyway. Still, EC-Council (like other vendors) can include pilot or beta-style questions that don't count toward your score, and you won't get a label that says "this one is unscored," so treat every question like it matters.
Question distribution maps to the 20 knowledge domains in the EC-Council CEH exam blueprint and the Certified Ethical Hacker v13 syllabus. You won't see "Domain 7 starts now," but you'll feel it in clusters. Like a run of web questions, then a run of network stuff, then some cloud and incident-ish content. The allocation generally reflects domain weighting in the blueprint, meaning high-weight areas show up more often, while niche topics appear as single questions that can still sting if you ignored them. You don't need to memorize the percentage table, but you do need to respect it when you plan your CEH v13 study materials.
Now the CEH v13 question format itself. You'll mainly see:
- Single-answer multiple-choice. Pick the "best" answer. Sometimes two look right. Annoying.
- Multiple-select questions where more than one option is correct and the prompt says so. Read that line twice. People miss it and bleed points.
Other types show up, too, but less consistently. Scenario-based questions are a thing, and they can include an exhibit like a snippet of command output, a log line, a nmap result, or an HTTP request, and then ask what you'd do next or what it indicates. Tool identification prompts happen, like "what tool uses this syntax" or "what does this flag do," sometimes with a screenshot or a command line. Not gonna lie, these are where people who only watched videos and never typed commands get punished, because the options will include realistic distractors that differ by one letter.
What you won't get on 312-50v13: performance-based, hands-on lab tasks. No live exploitation. No "configure this." No "capture the flag." That's the big difference between CEH (312-50v13) and CEH Practical, which is the hands-on exam where you actually do tasks in a lab environment. If you want the keyboard-and-terminal experience, CEH Practical is the one that scratches that itch, while 312-50v13 is the knowledge and recognition exam.
Time limit? 4 hours (240 minutes). With 125 questions, that's about 1.9 minutes per question on average. That's generous, and it changes your pacing strategy: you don't need to speed-run, but you also can't spend 6 minutes arguing with yourself about two answers that both look "kinda right." My take? First pass, keep momentum, mark the time-sinks, then come back.
Tutorial time's usually separate from the scored time in many testing setups, but don't bank on that as free relaxing time. No scheduled breaks, and if you take a bathroom break, the clock usually keeps running. Plan like a grown-up. Hydrate earlier.
Delivery method (online proctoring vs test center)
You can take CEH v13 through ECC EXAM online proctoring or at a Pearson VUE test center, depending on availability in your region and how EC-Council's routing this version at the time you book. Check both.
For online proctoring, expect the usual: webcam, mic, stable internet, and a system check. You'll need adequate bandwidth and a machine that passes their compatibility tool, and you'll need a workspace that fits the "clean desk" policy. That means no notes, no extra screens, typically no dual monitors, and no random electronics sitting around. Proctors can and will ask for a room scan, and if your camera angle's wrong or your lighting's bad, you can lose time fixing it.
Test centers are more predictable. You show up, they check your ID, you sit down, you take the exam, you leave. The upside's fewer "my webcam driver updated five minutes ago" problems. The downside? You have to travel, you're on their schedule, and some centers feel like taking a test inside a fluorescent box.
Common remote-proctor issues I see people hit: corporate VPNs blocking the proctor app, aggressive antivirus, flaky Wi-Fi, Bluetooth audio devices acting up, and roommates walking in. Troubleshooting's boring but real. Use wired internet if you can, kill background apps, reboot before launch, and don't take it on a locked-down work laptop unless you enjoy chaos.
Exam languages and retake policy
English's the primary and most current language for CEH v13. Translations exist in some regions, but there can be lag behind English updates, and sometimes translated phrasing makes technical terminology feel off. If you're comfortable reading technical English, I usually recommend sticking with it, because the tools and command outputs are English anyway, and the "closest meaning" answers can get muddy in translation.
If you're a non-native English speaker, ask about extra time accommodations. They're not automatic. You typically need to request them through EC-Council and provide whatever documentation they require.
Retakes: EC-Council's got an official retake policy, and it can change, so verify the current terms when you buy. In many cases, candidates can reschedule relatively quickly after a failed attempt, but pricing and waiting periods depend on the voucher type and the policy in effect. Score-improvement retakes are allowed, but you're still paying for the seat, and multiple failures can trigger additional requirements depending on the program rules at the time. The practical advice's boring: budget for the possibility of a second attempt when you estimate CEH v13 exam cost, because plenty of capable people miss on attempt one due to breadth and wording.
CEH v13 exam cost (312-50v13)
CEH v13 exam cost varies a lot by region, discounts, and whether you buy exam-only or a bundle. Exam vouchers often land in a "not cheap" range. Honestly, it can sting. And bundles that include CEH training official courseware iClass and labs can jump significantly. Taxes, proctoring-related fees, and rescheduling fees can add to the final number.
If you're comparing options, don't just compare sticker price. Consider what you actually need. Some people only need a voucher and CEH v13 practice tests. Others need a structured course because they're missing fundamentals.
CEH 312-50v13 passing score
People always ask for the exact number, and EC-Council doesn't make it a simple fixed target. The CEH 312-50v13 passing score is typically a scaled or variable cut score, and it can vary by form. Translation: two candidates can take "the same exam" and have different pass thresholds depending on difficulty calibration.
What you do get after the exam's a score report with domain-level feedback. It's not super granular, but it's enough to see where you were weak, which matters if you're planning a retake.
Scheduling, rescheduling, and cancellation policies
You can usually schedule in advance as long as seats exist, and remote proctoring often has more time slots than test centers. Rescheduling windows commonly sit around 24 to 48 hours before the appointment, and late changes can mean fees or a lost voucher, depending on the terms you agreed to when you booked. No-shows? Worst case. That's often a straight forfeiture.
Best practice: pick a date when your life's calm. No on-call. No travel week. No "I'll just squeeze it in between meetings." Give yourself a buffer day for review and sleep.
Exam environment rules and what to expect on test day
Expect strict rules. Prohibited items usually include phones, watches, notes, books, and any reference material. You'll need a government-issued ID, and you'll agree to an NDA and confidentiality terms. At test centers, you often get a laminated noteboard or scratch paper setup. Online, you may be limited to an on-screen whiteboard. Calculator access's typically via an on-screen tool, not your own device.
Proctors monitor eye movement, audio, and off-screen attention. Red flags include reading questions out loud, looking away repeatedly, someone entering the room, or having extra monitors connected. Even innocent stuff can trigger a pause. Wait, I mean, keep your space boring. Just boring.
Accessibility accommodations for candidates with special needs
Accommodations are possible, but they take time. You request them through EC-Council, you provide documentation, and you wait for approval. Extra time's common. Modified environments can happen, too, depending on need and delivery method. Don't leave this to the last minute, because processing isn't instant, and your preferred exam date can disappear while you're waiting.
CEH v13 difficulty, objectives, prereqs, and renewal quick hits
CEH v13 difficulty's mostly about breadth and wording. Compared to Security+ it often feels more tool-and-attack focused, but less conceptually clean. Compared to PenTest+, it can feel less hands-on, more memorization. Your mileage varies.
CEHv13 exam objectives follow the EC-Council blueprint and the syllabus, split across 20 domains. Respect the high-weight areas, but don't ignore the weird small ones, because one question's still one question.
CEH prerequisites 312-50v13 depend on your path. If you're not taking official training, EC-Council's got eligibility rules you may need to meet, usually tied to work experience and an application process. Read that before you buy anything.
Renewal requirements matter after you pass. CEH renewal requirements (ECE credits) fall under EC-Council's continuing education system, so plan for ethical hacking certification maintenance with ECE credits and any fees on the renewal cycle, not when you're already about to expire.
CEH v13 FAQs
How much does the CEH v13 (312-50v13) exam cost? It depends on voucher type, region, and bundles, so check current pricing and factor retakes.
What's the passing score for the CEH 312-50v13 exam? It's variable or scaled, not a single fixed published number.
Is CEH v13 hard compared to Security+ or PenTest+? Different hard. CEH's broader and more tool-term heavy, PenTest+ trends more "do the thing," and Security+'s more general security foundations.
What are the CEH v13 exam objectives and domains? They're in the EC-Council CEH exam blueprint and the Certified Ethical Hacker v13 syllabus, organized into 20 domains.
How do you renew CEH certification and how many ECE credits are required? You renew via EC-Council's ECE program with credits over the renewal cycle plus any fees, so check the current ECE credit number and deadlines before you're up against the clock.
CEH v13 Exam Cost: Complete Pricing Breakdown for 312-50v13
CEH v13 Exam Cost: Complete Pricing Breakdown for 312-50v13
Okay, real talk here. CEH v13 isn't exactly pocket change. When you're planning your budget for the 312-50v13, you need to understand the full financial picture because EC-Council's pricing feels like working through a maze blindfolded sometimes.
Standard CEH v13 exam voucher pricing in 2026
Exam-only vouchers? $950 to $1,199 USD typically. That's a massive spread, I know. Your final cost hinges on geography and which EC-Council authorized training center processes your purchase. I've watched North American candidates consistently shell out $1,199 when they go straight through EC-Council. Certain authorized centers drop closer to $950 when they're running promotions or trying to hit quarterly targets.
EC-Council tweaks pricing based on market dynamics and what different regions can realistically afford. No press releases about it. You just log in one random Tuesday and boom, everything's $50 more expensive. The pricing model honestly feels like they're throwing darts at a board, but that's pretty standard for certification vendors who've got a monopoly on their own ecosystem.
Where you live matters way more than most people realize. Indian candidates might pay substantially less than Americans, though EC-Council doesn't exactly publish transparent regional pricing charts like some competitors do. Europeans need to remember VAT. That's an extra 20% or more tacked on depending on which country you're in.
How CEH stacks up against Security+ and PenTest+ pricing
CompTIA's Security+ runs $404. Your baseline. The CompTIA PenTest+ sits at $428, positioning it as mid-tier. CEH v13 costs roughly 2.5 to 3 times more than Security+.
What're you getting for that premium? More full curriculum depth, especially around practical hacking techniques that actually matter in real scenarios where you're testing defenses under pressure and documenting vulnerabilities that need immediate remediation. CEH spans 20 domains. Web app hacking, SQL injection, wireless attacks, malware analysis, all with serious granular detail. Security+ gives foundational knowledge. PenTest+ goes deeper than Security+ but doesn't quite match CEH's scope.
ROI perspective? CEH unlocks opportunities Security+ sometimes can't. Government contracting gigs specifically demand CEH since it's on the DoD 8570 approved list. Fortune 500 companies frequently list CEH as preferred or mandatory for penetration tester and security analyst positions. That said, Security+ gets your foot in the door for help desk and junior roles at a fraction of the cost.
Speaking of government work, I once talked to a contractor who spent five months trying to land a federal pen testing role without CEH on his resume. Had OSCP, had real experience, didn't matter. The HR filter wanted CEH because that's what the requirement doc said. He passed the exam and got three interview requests within two weeks. Bureaucracy's weird like that.
Training bundle versus buying just the exam voucher
This is where things get interesting, actually. EC-Council packages official iClass training with the exam voucher for $3,500 to $4,500. That bundle delivers instructor-led or self-paced training, official courseware, lab access, and the exam voucher. Some authorized training centers charge even more. I've personally seen packages hit $5,000 without blinking.
But here's the thing. You don't always need the bundle. Got two years of documented information security work experience? You can purchase the exam-only voucher. EC-Council calls this the "eligibility waiver." Submit proof of your work history, they review it (usually takes a few business days), then you're cleared to buy just the exam voucher.
Cost-benefit analysis is pretty straightforward here. If you're already working in security, have hands-on experience with the tools CEH covers, and you're comfortable with self-directed study, dropping $4,000 on training you don't really need is just wasteful spending. Buy the voucher for $1,199, grab quality study materials for $200-300, and you're still under $1,500 total. That's less than half the training bundle cost.
On the flip side? If you're career-changing into security with minimal hands-on experience behind you, that official training provides structure and access to lab environments that would cost hundreds to replicate independently without institutional support or existing infrastructure. The 312-50v13 Practice Exam Questions Pack at $36.99 helps fill gaps in your prep regardless of which path you choose.
What official EC-Council training actually includes
Instructor-led live online training typically runs 5 days (40 hours) and costs around $4,000-$4,500 including the exam voucher. You get interaction with a certified instructor who's been through the trenches, scheduled lab time with dedicated resources, and official courseware PDF access that you can reference indefinitely.
Self-paced iClass online training gives you 12 months of access to video modules, labs, and courseware for roughly $3,500-$4,000 including the exam voucher. Work through content on your schedule, which honestly works better if you're employed full-time and can't block out entire weeks for training.
Both options include access to EC-Council's iLabs environment. A cloud-based lab platform with pre-configured vulnerable machines and hacking tools already installed and ready. This is actually valuable since setting up your own lab with properly vulnerable targets takes significant time and technical knowledge that beginners don't have yet. The courseware itself is thorough, though some candidates find it dry and too focused on tool memorization rather than methodology and critical thinking.
Authorized training centers sometimes offer group discounts that make the math work differently. I've seen corporate clients negotiate 15-20% off when sending 5+ employees through training simultaneously. Direct EC-Council purchases rarely get discounted, but authorized centers have more pricing flexibility.
Additional fees that sneak up on you
Online proctoring fees? Typically included in the exam voucher price. If you test at a Pearson VUE center there might be a small administrative fee ($15-25), though most candidates don't encounter this since EC-Council's online proctoring is baked into the voucher cost.
Rescheduling costs $25-50 if you need to change your exam date with less than 24 hours notice. Wait, actually, I need to interrupt myself here because late cancellations forfeit the entire exam fee, which is way harsher than the rescheduling penalty. Your voucher expires 12 months from purchase. Miss that window and you're buying a new voucher at full price with zero credit.
International candidates might hit currency conversion fees from their bank or credit card issuer. These aren't EC-Council's fault but they definitely add up over time. I've seen candidates pay an extra $30-50 in transaction fees when converting from euros or pounds sterling.
Retake costs and voucher policies
Failed your first attempt? You're paying full price again. Period. EC-Council doesn't offer discounted retake vouchers like some vendors do. No multi-attempt packages either. Each attempt costs the full $950-$1,199.
This makes thorough preparation absolutely critical from a financial standpoint, not just a career one. Failing twice means you've spent $2,400-$3,600 on exams alone before even passing once. Using resources like the 312-50v13 Practice Exam Questions Pack helps you gauge readiness before dropping another $1,199 on a retake that might not go any better.
Your voucher is valid for 12 months from purchase. That's reasonable but not generous. Some vendors give 18-24 months of validity. If life gets in the way and you can't schedule within a year, that voucher becomes completely worthless.
Regional pricing and purchasing power differences
North American pricing is EC-Council's baseline reference point. Candidates in the US, Canada, and Mexico typically pay the full $1,199 for exam-only vouchers without much variation.
European candidates pay similar base amounts but VAT gets added on top of everything. In the UK that's 20% VAT, pushing the effective cost to around £1,100-1,200 (roughly $1,400-1,500 USD depending on exchange rates). Germany, France, and other EU countries have similar VAT rates that substantially increase the total.
Asia-Pacific pricing varies wildly by country and sometimes even by city within countries. India and other developing markets sometimes get discounted pricing through local authorized training centers, though EC-Council doesn't advertise this openly or consistently. I've heard of vouchers in India selling for $700-800, but verification is difficult without direct contact with those centers.
Currency exchange rates create extra uncertainty that's hard to plan around. If the dollar strengthens against your local currency between when you start studying and when you purchase the voucher, you might pay significantly more than you originally budgeted.
Getting your employer to pay for it
Most employers with professional development budgets will reimburse CEH costs if you make a solid business case that connects certification to organizational needs. Focus on how the certification benefits the organization. Improved security posture, compliance requirements, client-facing credentials that win contracts.
Corporate training accounts with EC-Council allow bulk voucher purchases at negotiated rates that individual purchasers can't access. If your organization employs multiple security professionals, having your manager contact EC-Council about corporate pricing could save everyone money in the long run.
Government and military personnel sometimes qualify for discounted pricing through GSA schedules or defense contractor programs that aren't publicly advertised. Check with your contracting officer or training coordinator. These discounts exist but they're not exactly broadcasting them on the website.
Certification costs are tax-deductible as professional development expenses in most jurisdictions globally. Keep receipts for the exam voucher, study materials, and any training courses you complete. Consult a tax professional for specifics in your country because I'm not giving tax advice here.
Hidden costs beyond the exam voucher
Study materials add up quickly if you're not careful. Quality books run $50-80 each, and you'll want 2-3 covering different aspects and perspectives. Practice test platforms cost $100-200 for question banks that actually simulate the real exam experience. Lab subscriptions for hands-on practice run $50-200 depending on provider and subscription duration. Budget $200-500 total for study materials.
You'll need a lab environment for practical skills. Cloud-based options like EC-Council's iLabs (if not included in your training package) cost $100-150 monthly. Building your own home lab requires a decent computer with enough RAM and storage, virtualization software, and vulnerable machine downloads. Figure $200-500 in hardware if you don't already have suitable equipment.
Time investment represents an opportunity cost that's easy to overlook. Most candidates study 8-12 weeks at 10-15 hours weekly. That's 80-180 hours you could spend earning money through freelancing, learning other skills, or honestly just sleeping because burnout is real. Not a direct financial cost but worth considering when evaluating total investment.
CEH requires renewal every three years through EC-Council's continuing education program that tracks your professional activities. You need 120 ECE credits and pay a $80-100 renewal fee every cycle. Annual maintenance runs roughly $25-35 per year when averaged out over time. Compare this to certifications like EC-Council Certified CISO which have similar renewal requirements and fee structures.
Strategies to save money without cutting corners
Negotiate employer sponsorship before you start studying and spending your own money. Frame it as investing in the company's security capabilities and risk mitigation. Offer to present what you learned to the team or update security procedures based on CEH knowledge you acquire.
Watch for EC-Council promotions around major security conferences like Black Hat or RSA when they're trying to drive enrollment. Authorized training centers sometimes discount bundles 10-15% during these periods to compete with each other. Sign up for EC-Council's newsletter. They occasionally email promo codes that actually work.
Previous edition study materials work fine for foundational concepts that don't change much between versions. The 312-50v12 and 312-50v11 versions covered 90% of the same material as v13 with minor variations. Buy used books from those versions for $20-30 instead of $60-80 new v13 books. Just make sure you supplement with current exam objectives documentation from EC-Council's website.
Free resources supplement paid materials if you're strategic. YouTube channels, security blogs, and community forums provide excellent explanations of complex topics that paid courses sometimes rush through. GitHub repositories offer free vulnerable machines for lab practice that work perfectly well. The 312-50v13 Practice Exam Questions Pack at $36.99 gives you exam-style questions without breaking the bank or requiring expensive subscriptions.
Look, the CEH v13 exam costs serious money no matter how you slice it or try to optimize. Budget $1,500-2,000 minimum for exam-only path with decent study materials, or $4,000-5,000 for official training bundles. But compared to other advanced security certifications in the market, CEH's pricing sits in the middle range and the career ROI justifies the investment if you're serious about offensive security roles long-term.
CEH 312-50v13 Passing Score: Understanding Exam Scoring and Results
ECCouncil 312-50v13 (CEHv13) exam overview
CEH v13 is EC Council's broad "ethical hacking" knowledge check. Maps to job titles like SOC analyst, junior pentester, security analyst, and sometimes even IT auditor who needs to understand attack paths.
Here's the thing: it's not a pure hands-on pentest cert. It's also not a trivia-only exam. It sits in that middle zone where you need to recognize tools, techniques, and defensive takeaways, and you also need enough real-world context to not get tricked by wording.
CEH v13 is the Certified Ethical Hacker exam, version v13, exam code ECCouncil 312-50v13 CEHv13 exam. That code matters when you buy vouchers, schedule, or explain to HR what you actually took, because "CEH" alone gets messy with versions and add-ons.
CEH v13 exam format and key details
Most candidates see 125 multiple-choice questions with a 4 hour time limit, and the CEH v13 question format includes single-answer and multiple-select items. Some questions are straight definitions. Others are scenario-ish. A few feel like "which tool would you pick first" style.
Testing can be online proctored or at a test center, and your experience varies a lot depending on your internet stability and whether your proctor's chill or strict. Honestly, if your home setup's chaotic, a test center is less stress. I took mine at a Pearson VUE center on a Tuesday morning, which was weirdly quiet except for someone's clicking pen three chairs down, and that was still better than worrying about my router dropping mid-exam.
Languages vary by region, and retakes are allowed. EC Council's current stance is that there's no waiting period between retake attempts for CEH v13, so you can reschedule quickly if you miss it, but your wallet might not love that plan.
CEH v13 exam cost (312-50v13)
CEH v13 exam cost depends on whether you're buying exam-only or a bundle. Exam vouchers commonly land in the several-hundred-dollar range, and bundles can climb much higher when you add official training, labs, and extras.
Training bundle versus exam-only cost is where people get surprised. If your employer's paying, great. If you're paying personally, you need to decide whether official courseware iClass is worth it for your learning style, or if you'll do better mixing independent CEH v13 study materials with labs and targeted practice.
Other fees exist. Taxes. Rescheduling charges. Sometimes proctoring rules that force you into specific setups. Read the fine print before you click purchase.
CEH 312-50v13 passing score
Official CEH v13 passing score requirements
The CEH 312-50v13 passing score isn't a single fixed number that applies to every candidate on every day. EC Council has published guidance that the passing score falls in a 60 to 85 percent range depending on the exam form, which is their way of saying different versions of the test can have slightly different cut scores.
That "range" freaks people out. I mean, it sounds like they're making it up as they go, but the real reason is exam forms aren't identical, and some sets of questions are statistically harder than others.
How CEH scoring works: scaled versus raw scores
Raw score? Just how many questions you got right. Scaled score is the adjusted result after the exam's statistical model accounts for form difficulty and question performance. EC Council doesn't typically publish raw-to-scaled conversions because it invites people to reverse engineer the item bank, and because the conversion can change when they refresh forms.
Psychometric scaling is the fairness piece. If Form A's harder than Form B, a scaled system can avoid punishing the people who happened to get the tougher set that day, and that's where Item Response Theory (IRT) concepts show up. IRT models question difficulty and discrimination and how likely a candidate at a given ability level is to answer correctly.
Also, two candidates can have the same raw score and still land differently after scaling if they took different forms with different difficulty profiles, and if certain items are weighted in the model differently based on how they perform across the testing population. That sounds annoying. It is. But it's also why "my buddy passed with X correct" is usually useless advice.
Minimum passing threshold and why it can vary
There's still a minimum passing threshold, it's just not expressed as one universal percent. It's determined using standard setting methods, where a panel and psychometric data estimate what a minimally qualified candidate should know, and then that cut score's mapped to each exam form.
Passing scores may vary slightly between administrations because EC Council rotates items, retires bad questions, introduces new ones, and rebalances domains to match the EC Council CEH exam blueprint and the Certified Ethical Hacker v13 syllabus. New questions also need validation. Which brings us to, wait, pilot items.
What score you need to pass: interpreting EC Council's guidance
In practical terms, most people should treat "about 70 to 75 percent correct" as the typical passing neighborhood for many forms, even though the official statement's the 60 to 85 percent range. If you want a safety margin, aim for 80 percent or higher on CEH v13 practice tests, not because the exam's guaranteed to demand 80, but because test-day stress and tricky wording can knock you down fast.
Unscored pilot questions can exist, and you won't know which ones they are. So your strategy's simple. Take every question seriously. Don't burn time trying to guess whether an item "feels experimental."
Multiple-select questions are also a trap for people who expect partial credit. CEH scoring's typically all-or-nothing on those, so if it says "choose two," you need both correct choices, and one wrong selection can zero it out.
Score report format and what you'll receive after the exam
You usually get an immediate pass/fail at the test center screen or right after an online proctor ends the session. Then a detailed score report's delivered either immediately or within about 24 hours depending on the delivery pipeline.
The report includes a domain-by-domain performance breakdown aligned to the CEHv13 exam objectives, and you'll see proficiency levels for each knowledge domain. These proficiency levels aren't a fine-grained map of every topic you missed. They're broad performance bands.
No exact numerical score's typically provided in a way that helps you compute "I got 91/125," so don't expect that kind of transparency. It's pass/fail plus those domain indicators, and that's what you plan from.
Understanding domain-level feedback on your score report
Most candidates see ratings like Above Target, Near Target, and Below Target. Above Target means you're comfortably over the expected level for that domain. Near Target means you're flirting with the line. Below Target's the "yeah, you need to fix this" signal.
Use it like a heat map. If you fail, you pick the two or three weakest domains and rebuild them with labs, notes, and question review, then you retake. If you pass, you can still use the feedback to guide what you practice on the job, because passing CEH doesn't mean you're magically good at web testing or cloud attacks the next day.
Limitations matter though. The categories are broad, and they won't tell you "you missed SSRF payload handling" or "you forgot how ARP spoofing detection works." You still need to map domains to your own notes and lab work.
If you want targeted drilling for a retake, this is where a focused question pack can help, as long as you treat it as practice and not a substitute for learning. I've seen people pair their weak domains with timed sets from a pack like 312-50v13 Practice Exam Questions Pack and then go back to labs to prove they actually understand the topic.
What happens if you fail: score validity and retake considerations
No waiting period between retake attempts sounds great, but don't instantly rebook if you were far off. If your report shows multiple Below Target areas, you need more than a weekend.
Statistically, lots of candidates do pass on the second attempt with focused study, mostly because the first attempt shows them the real CEH v13 difficulty and the wording style, and then they stop studying "interesting hacking stuff" and start studying what the blueprint actually tests.
Schedule a retake when your practice results stabilize. If you can't hold 80 percent across mixed-domain practice sets, you're probably gambling. A tighter plan's to do two weeks of domain repair, then one week of mixed timed exams, then book it.
CEH exam difficulty calibration and pass rates
EC Council doesn't publish official pass rates. So anything you hear's an estimate, and you should treat it like one.
Industry estimates often put first-attempt pass rates somewhere around 50 to 70 percent, and the spread's wide because the population's wide, from people with years in IT to folks who just finished a bootcamp. Preparation time, prior networking knowledge, comfort with Linux, and whether you've actually used common tools all swing outcomes a lot.
Compared to Security+ and PenTest+, CEH v13's usually broader than PenTest+ in topic coverage but often less deep in exploitation details, and it can feel more memorization-heavy than some people expect. If you already live in blue team land, the attack chain questions can feel weird. If you only know red team tricks, the governance and process bits can feel like homework.
Score confidentiality and sharing results with employers
Your score report's confidential. Employers don't get your domain breakdown unless you hand it over.
Most employers verify via the EC Council certification verification portal, and what they care about is "certified or not." Your digital badge and certificate prove you passed, and they don't show a score. Personally, I wouldn't volunteer a domain breakdown to an employer unless you're using it to explain a training plan you're already executing.
Challenging exam results or requesting score review
EC Council has a score challenge policy, and it's there for cases like administrative or scoring irregularities, not "I feel like I should've passed." The timeline and costs vary, and you'll follow their formal procedure through support.
Not gonna lie, the historical success rate for score challenges across most certification vendors is very low. If you had a real technical disruption, file a case. If you simply didn't like the outcome, your best move's usually to study, use your domain feedback, and retake.
If you're building that retake plan, I'd rather see you do targeted review plus timed practice than endless rereading. Mix CEH training official courseware iClass or other CEH v13 study materials with hands-on labs, and then pressure-test with questions, whether that's your own bank or something like the 312-50v13 Practice Exam Questions Pack when you need structured repetition.
CEH v13 FAQs
How much does the CEH v13 (312-50v13) exam cost? It varies by voucher and bundle, and training packages raise the total fast, so check current pricing where you're buying and budget for retakes.
What's the passing score for the CEH 312-50v13 exam? EC Council publishes a 60 to 85 percent passing range depending on exam form, with many candidates treating 70 to 75 percent correct as a realistic target and 80 percent practice performance as a confidence buffer.
Is CEH v13 hard compared to Security+ or PenTest+? It's broad and sometimes wordy, usually harder than Security+ for attack tooling, often less technically deep than PenTest+ but more "wide."
What're the CEH v13 exam objectives and domains? They're listed in the EC Council CEH exam blueprint and map to the Certified Ethical Hacker v13 syllabus, and your score report'll reflect those domains.
How do you renew CEH certification and how many ECE credits are required? You renew via CEH renewal requirements (ECE credits) under EC Council's continuing education program, so plan for ethical hacking certification maintenance activities and fees during the renewal cycle.
If you're shopping for extra drilling before test day, the 312-50v13 Practice Exam Questions Pack is the kind of add-on I'd use late in prep, after you've already covered the CEHv13 exam objectives and you're trying to close gaps fast.
CEH v13 Difficulty: How Hard Is the 312-50v13 Exam Really?
Overall difficulty assessment: where CEH v13 ranks among security certifications
Honestly? Not gonna lie.
The 312-50v13 sits in this weird middle zone that really frustrates people, and I mean, it makes sense when you think about it because it's tougher than entry-level stuff like CompTIA Security+ but definitely not playing in the same brutal league as OSCP. Most test-takers I've talked to rate it somewhere around 6 or 7 out of 10, which feels about right from what I've personally seen, though obviously everyone's mileage varies depending on their background and how much hands-on experience they're bringing to the table.
Here's the thing.
CEH v13 is intermediate. You need more than book knowledge, but you're not expected to be some penetration testing wizard either. Compared to Security+, CEH digs way deeper into offensive tools and attack methodologies. Security+ honestly feels more like security awareness with some technical flavor thrown in. CEH actually expects you to understand how attacks work and which specific tools accomplish what objectives.
But put CEH next to OSCP? Not even close. OSCP's brutal. 24 hours of actual hacking, exploitation, privilege escalation on live systems. CEH's multiple choice. It tests knowledge, not hands-on exploitation skills under serious pressure. And CISSP? Different animal entirely. CISSP's management-focused, governance-heavy, experience-required. CEH's technical but broader, if that makes sense.
The evolution from earlier versions matters too. CEHv12 and CEHv13 added more cloud content, IoT attack vectors, and container security stuff that wasn't front-and-center before. The exam's getting more modern, which honestly makes it slightly harder if you're coming from a traditional network security background without much cloud exposure. I actually know someone who aced CEHv11 three years ago but struggled with v13 because all the cloud and container stuff was new territory.
Breadth versus depth: CEH's "mile wide, inch deep" challenge
This is where CEH gets people.
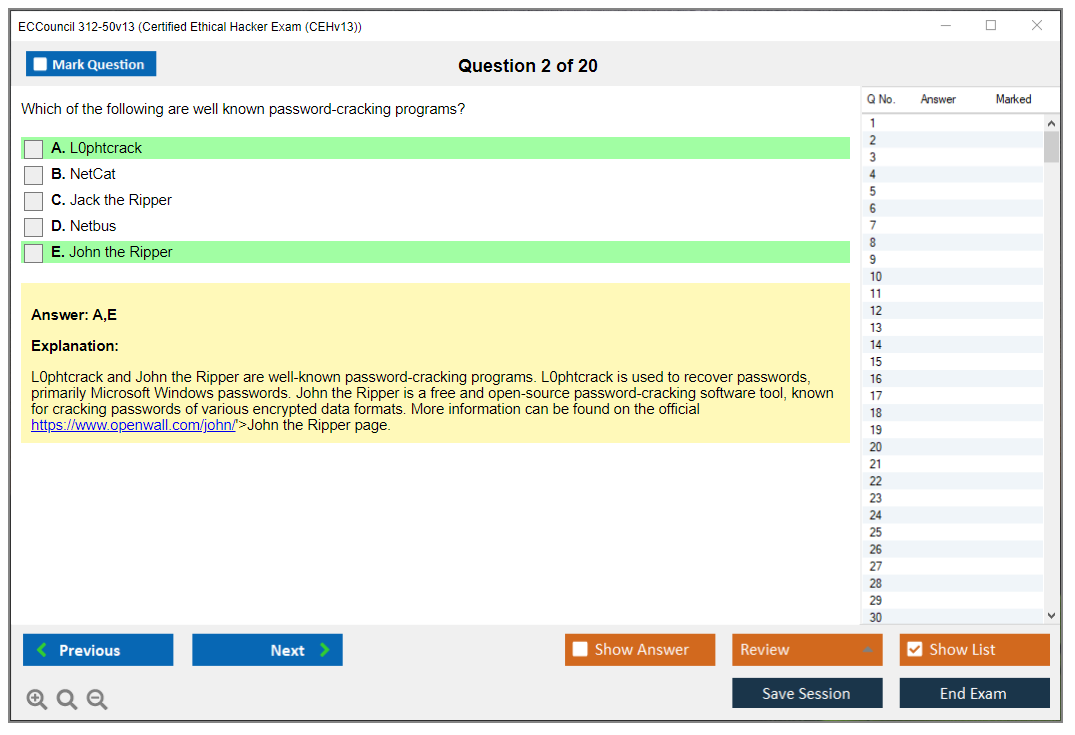
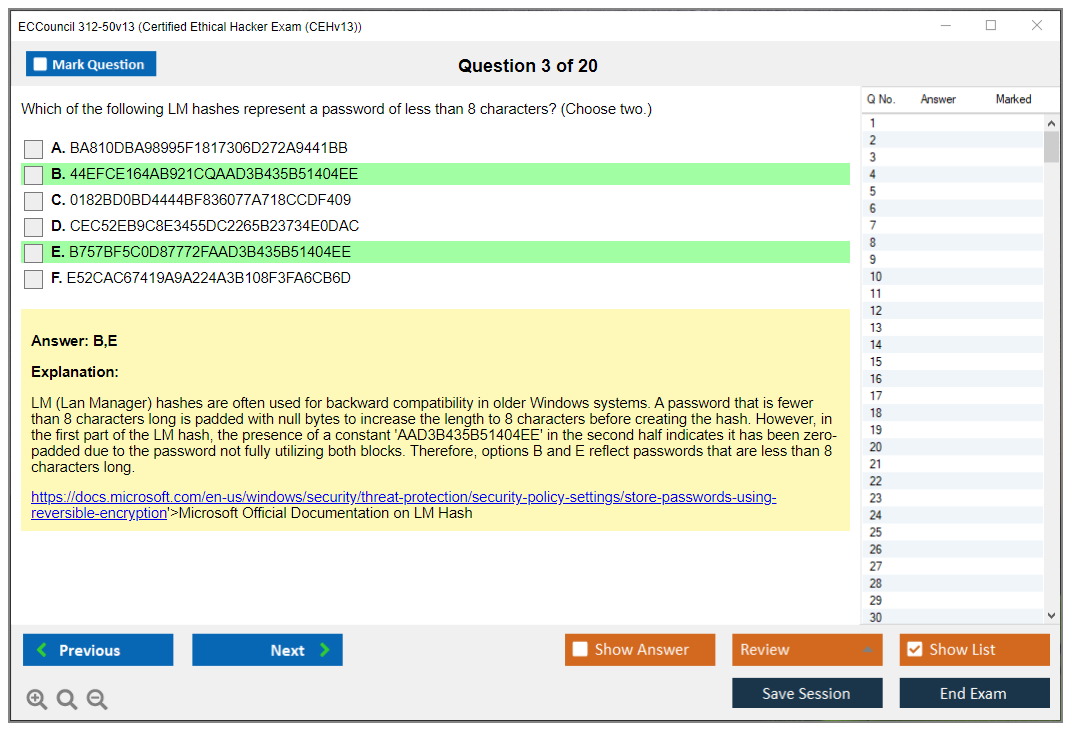
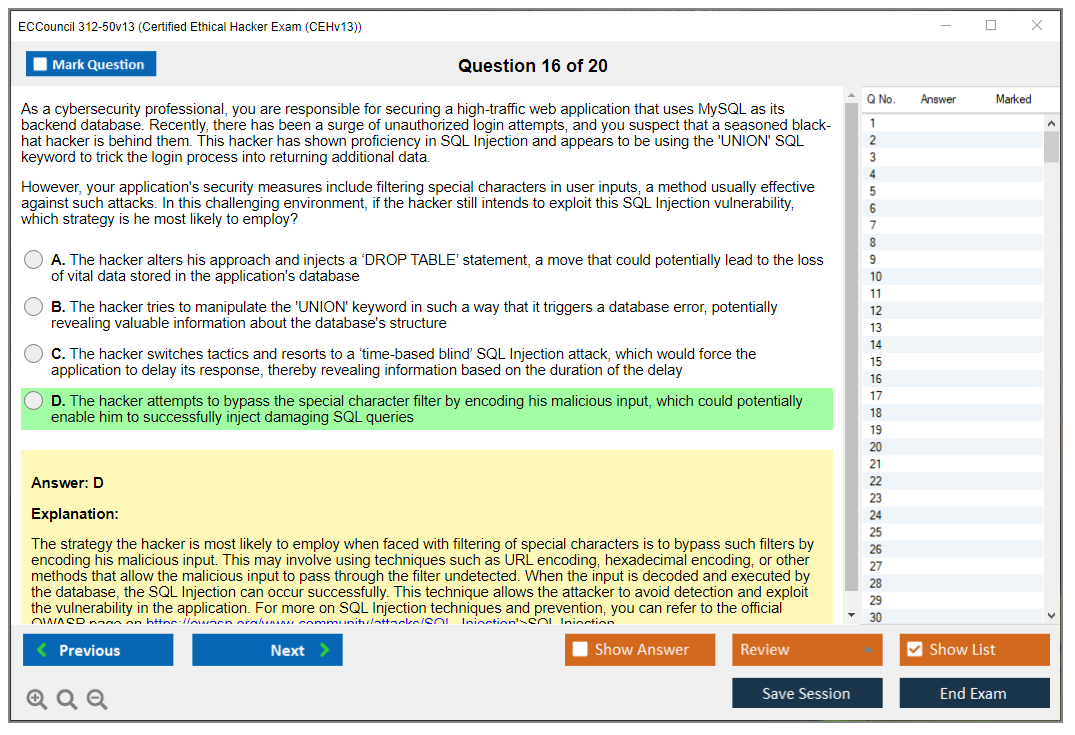
Twenty domains. You're covering reconnaissance, scanning, enumeration, system hacking, malware, sniffing, social engineering, denial of service, session hijacking, web app attacks, SQL injection, wireless attacks, mobile attacks, IoT, cloud, cryptography. I'm getting tired just listing them.
The breadth's the real challenge here. You don't need expert-level depth in any single domain, but you need working knowledge across all of them, and that's actually harder for a lot of people than going deep on one topic. I've seen network engineers who know TCP/IP inside-out struggle because they've never touched web application attacks or mobile security.
Memorization requirements are real. You need to know tools. Nmap, Metasploit, Wireshark, Burp Suite, John the Ripper, Hashcat, Aircrack-ng, and literally a hundred more. Port numbers too. FTP's 21, SSH's 22, Telnet's 23, SMTP's 25, DNS's 53, HTTP's 80, HTTPS's 443, SMB's 445. The list goes on. Attack types, their characteristics, countermeasures..all fair game.
But it's rote memorization, which would almost be easier. You need conceptual understanding too. Why does a particular attack work? What conditions make it possible? How do you detect it? That balance between "know the facts" and "understand the concepts" trips people up constantly. Some tests let you slide with pure memorization, others with pure understanding. CEH wants both, which is annoying but probably more valuable long-term.
Why's breadth harder than focused tests? Simple. Focused certs let you build deep expertise in one area. Your brain can create detailed mental models, connect everything together. With CEH, you're context-switching constantly. One minute you're thinking about cryptographic algorithms, the next about wireless attack tools, then about cloud misconfigurations. It's mentally exhausting, honestly.
Technical complexity factors that increase difficulty
The technical prereqs aren't officially brutal, but let's be real. You need solid foundations.
Multiple operating systems for starters. Windows administration, Linux command line, some mobile OS familiarity. If you freeze up when someone says "grep" or "PowerShell," you're gonna have a bad time with this exam.
Networking fundamentals are non-negotiable. TCP/IP stack, OSI model, subnetting, routing basics, how firewalls work, what IDS/IPS actually do. I've seen people try CEH without understanding three-way handshakes, and it doesn't go well because the exam assumes you already know this stuff and builds attack concepts on top of those foundations without explaining the basics.
Web application architecture's huge in v13. You need to understand HTTP/HTTPS, cookies, sessions, same-origin policy, how web servers and databases interact, common vulnerabilities like XSS and CSRF. Not developer-level understanding, but more than just "I browse websites."
Cryptography concepts come up without requiring you to be a mathematician, thankfully. You should know symmetric versus asymmetric encryption, what hashing does, how digital signatures work, common algorithms (AES, RSA, SHA), and basic PKI concepts. The exam won't ask you to calculate anything by hand, but you need to understand when to use what and why certain approaches are vulnerable.
Cloud and virtualization technologies are everywhere now. If your experience is purely on-premises traditional infrastructure, catching up on cloud attack vectors takes real effort. AWS security groups, Azure network security, container vulnerabilities, serverless attack surfaces. Modern stuff.
Scripting and programming concepts at reading level..you don't need to write production code, but you should be able to look at Python, PowerShell, or bash scripts and understand what they're doing. Questions might show you script output or ask what a particular code snippet accomplishes.
Memorization requirements and knowledge retention challenges
Tool taxonomy's probably the most complained-about aspect.
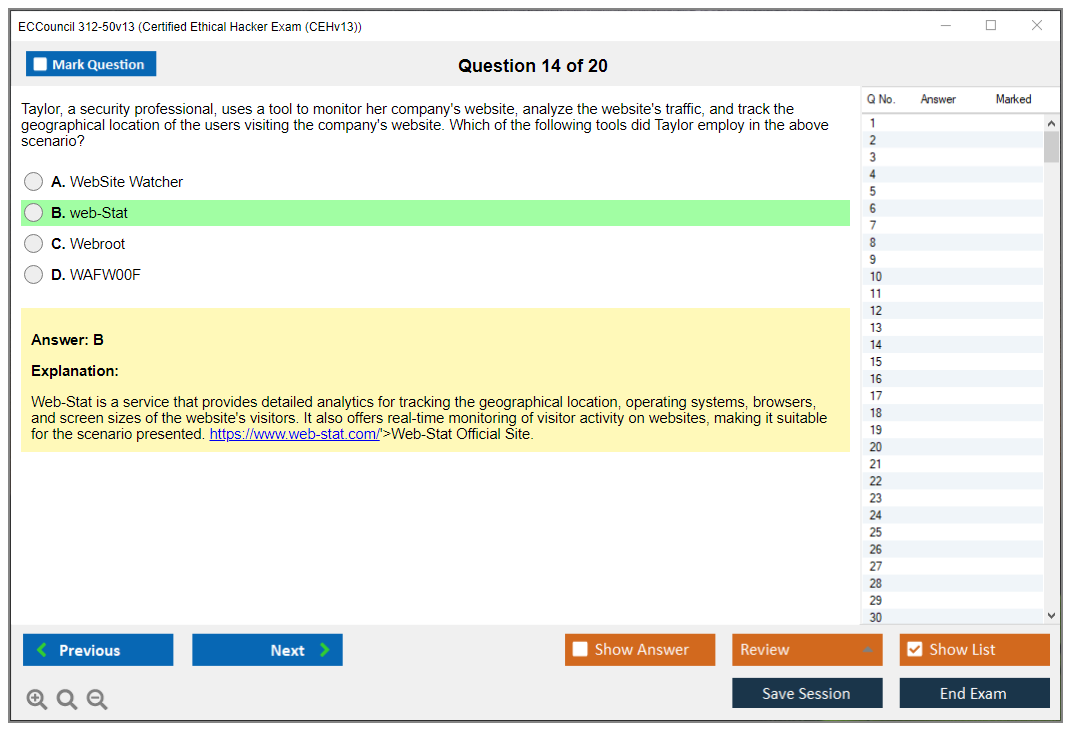
Over 100 tools across all domains. Reconnaissance tools like Maltego, theHarvester, Shodan. Scanning tools like Nmap, Nessus, OpenVAS. Exploitation frameworks like Metasploit, Canvas, Core Impact. Sniffers like Wireshark, tcpdump. Password crackers like John, Hashcat, Hydra.
You need to know what each tool does, when you'd use it, and often what kind of output it produces. Seems excessive until you realize the exam loves showing you tool output and asking you to identify it or interpret results. Then it makes sense why they emphasize this so much.
Port numbers and protocol associations are tested directly and indirectly. Directly: "What port does HTTPS use?" Indirectly: scenario questions where recognizing ports helps you understand what's happening. Common services and their ports need to be memorized cold.
Attack methodology phases are framework-based. Reconnaissance, scanning, gaining access, maintaining access, clearing tracks. Within each phase, specific techniques. The exam asks sequence questions. "What comes next in this attack" or "which phase is this activity part of."
Malware types and characteristics. Viruses, worms, Trojans, ransomware, rootkits, logic bombs, spyware, adware. How they spread, how they work, how to detect them, how to remove them. Countermeasures for each category, which gets tedious but you gotta know it.
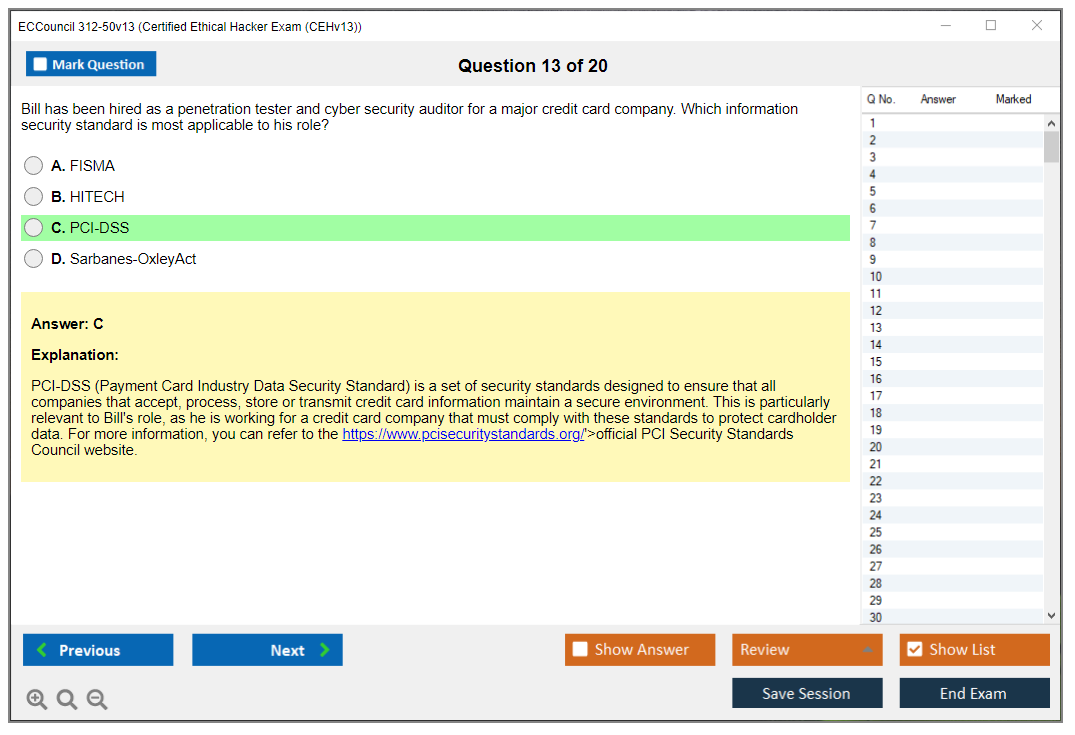
Regulatory and legal frameworks across jurisdictions. PCI-DSS, HIPAA, GDPR, various computer crime laws. You need basic awareness of legal constraints on ethical hacking and which regulations apply to what scenarios.
Best practices for memorization that actually work: spaced repetition with tools like Anki, physical flashcards for port numbers and tool names, hands-on practice in labs to build muscle memory that reinforces conceptual memory, teaching concepts to others to solidify your own understanding.
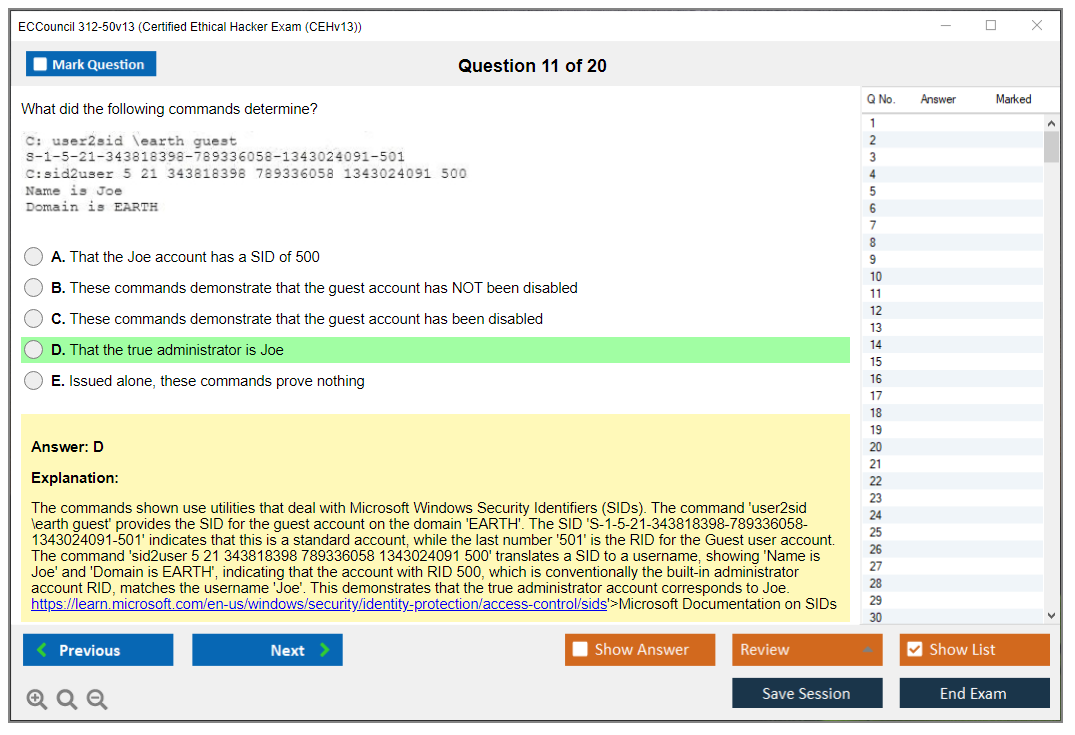
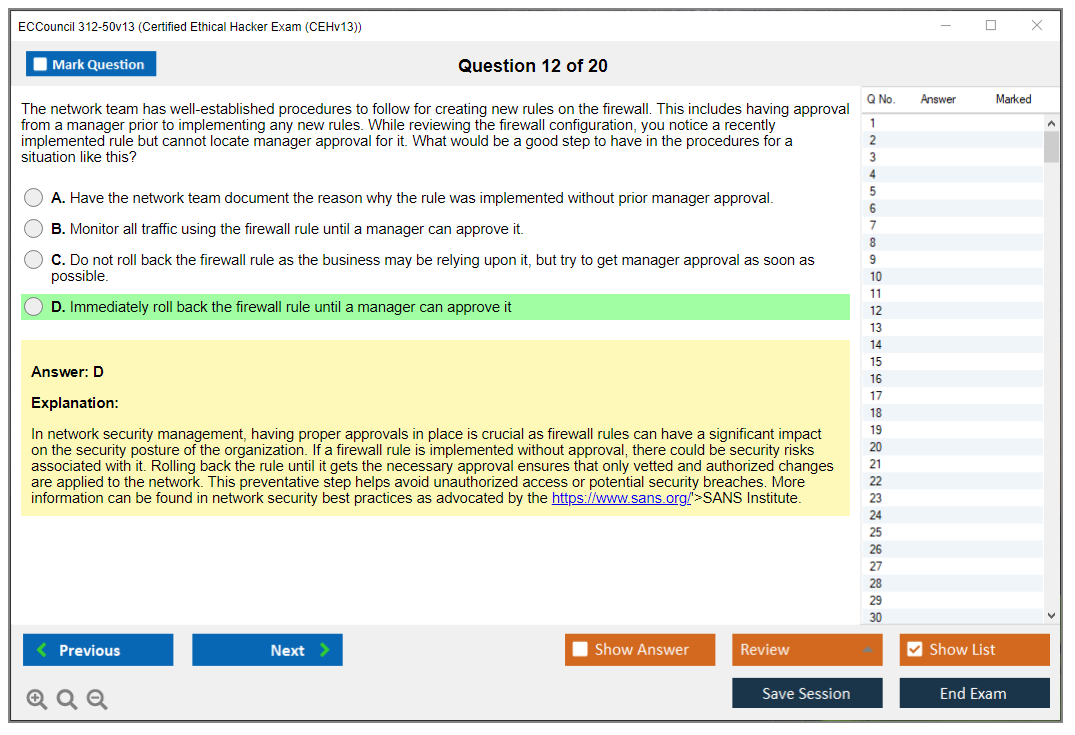
Scenario-based question complexity
Multi-step attack scenarios are where the exam gets interesting, honestly.
You'll see a paragraph describing a situation. An attacker performed X, observed Y, and now needs to accomplish Z. What's the next logical step? These require reasoning through attack chains, not just recalling facts you memorized the night before.
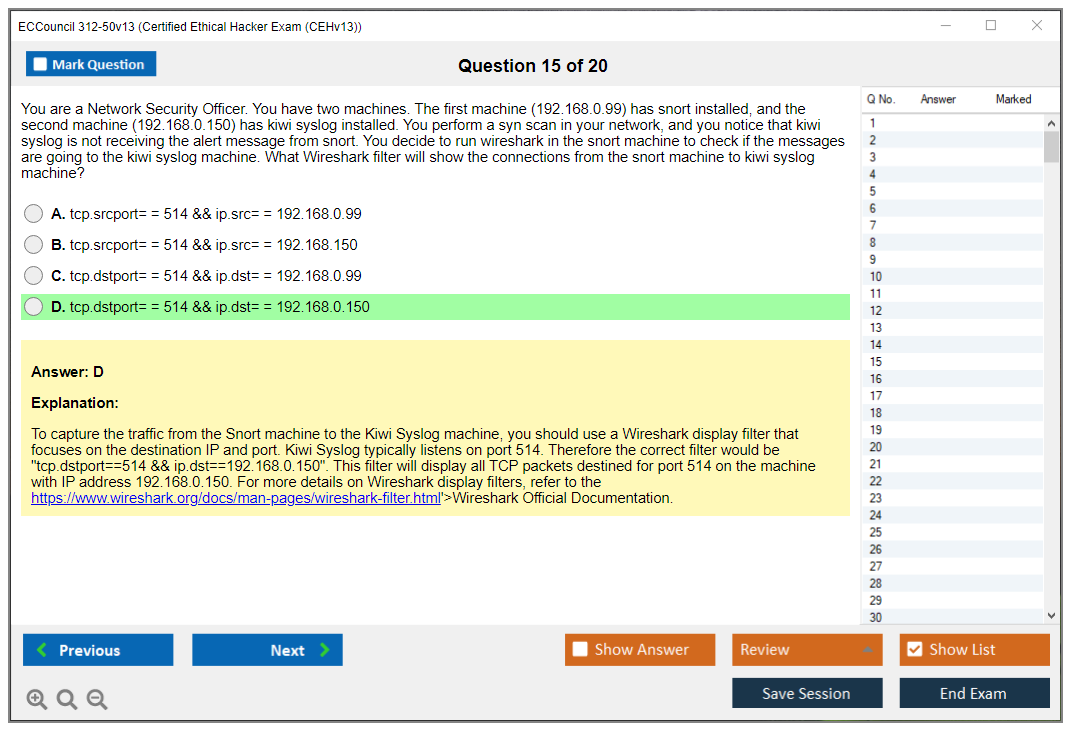
Log file analysis questions show you Apache logs, Windows Event Logs, firewall logs, IDS alerts. You need to interpret what happened, identify attack indicators, or determine what the attacker was trying to accomplish. If you've never actually looked at real logs, these questions feel impossible. Like trying to read a foreign language.
Tool selection questions test judgment. "Which tool would be most appropriate for this specific objective?" Multiple tools might technically work, but one's clearly better suited. This tests whether you actually understand tool capabilities or just memorized names without context.
Prioritization questions about remediation or testing approaches assess your thinking. "Given these vulnerabilities, which should be addressed first?" or "In this penetration test phase, what's the most important next action?" Experience helps enormously here, more than studying does.
"What would an ethical hacker do next?" sequence questions appear throughout. They're testing whether you understand attack methodology flow and decision trees. These aren't memorization questions. They're logic and reasoning based on scenarios, which I actually appreciate because they test real understanding.
Who finds CEH v13 easiest: ideal candidate profile
IT professionals with 2-5 years hands-on security or networking experience cruise through.
They've already seen most concepts in production environments. Reading about attacks in study materials just formalizes what they've observed or defended against in real networks, which makes retention so much easier because there's already a mental framework to attach new information to.
System administrators who've performed security hardening have huge advantages. They know Windows and Linux security configurations, understand user permissions and privilege escalation from the defensive side, and have worked with security tools in real environments rather than just reading about them in books.
Network engineers with firewall and IDS/IPS experience understand traffic flows, know protocols intimately, can read packet captures, and grasp network-based attacks immediately. The networking-heavy portions of CEH feel like review rather than new material.
Security analysts who've used security tools in production just need to fill knowledge gaps. They're already familiar with SIEM platforms, vulnerability scanners, and incident response procedures. CEH connects dots they've already seen, which..I mean, that's the ideal situation for any test.
Candidates who completed official EC-Council training with labs, especially the iClass platform with hands-on exercises, have notable advantages. The official training maps directly to exam objectives, and labs build practical familiarity with tools and techniques that you just can't get from reading alone.
Those with prior certs like Security+, Network+, or CCNA Security already have foundational knowledge locked in. They're building on solid ground rather than starting from scratch. I always recommend getting Security+ first if you're new to security tests..it's just a more logical progression.
Who finds CEH v13 hardest: challenging candidate profiles
Career changers without IT foundation entering the field face steep climbs.
If you don't already understand networking, operating systems, and basic IT operations, you're learning two things at once. Fundamental IT concepts and security concepts built on top of them. Which doubles your study time and cognitive load in ways that aren't immediately obvious until you're deep into preparation.
Candidates with purely theoretical knowledge and no hands-on experience struggle with scenario questions and tool-related content. You can read about Nmap all day, but if you've never actually run it and interpreted results, exam questions feel abstract and disconnected from reality.
Those attempting CEH as their first IT test are usually biting off more than they can chew. Not impossible, but unnecessarily difficult. Build foundations first with CompTIA stuff or equivalent experience, then tackle CEH when you've got context.
Professionals from compliance or governance backgrounds without technical depth know security policies and frameworks but lack technical implementation understanding. They can answer "what should you do" but struggle with "how does this attack work" or "which tool would you use here."
Self-study candidates without access to lab environments miss key hands-on practice, which honestly is one of the biggest disadvantages. Reading about SQL injection's completely different from actually exploiting it in a lab. Virtual labs are necessary, whether through official EC-Council resources or alternatives like Hack The Box or TryHackMe.
Non-native English speakers dealing with technical jargon face additional hurdles. Security terminology's already dense, and exam questions use specific phrasing. This isn't insurmountable but requires extra preparation time to get comfortable with the language patterns used in questions.
CEH v13 versus other certifications: difficulty comparisons
Comparing CEH v13 to Security+ is like comparing intermediate to beginner, which sounds harsh but it's accurate.
Security+ covers broader IT security at shallower depth. Risk management, cryptography basics, network security fundamentals, identity management. CEH requires more offensive security tool knowledge and goes deeper into attack methodologies. Security+ emphasizes governance and compliance more than CEH does, which makes sense given their different target audiences.
CEH technical questions are more complex and scenario-heavy than Security+. Security+ might ask "What's a rainbow table?" while CEH asks "Given this password hash and these constraints, which tool and attack method would be most effective?" Typical progression makes sense: Security+ first to build foundations, then CEH for specialization into offensive security.
PenTest+ is interesting because it's more hands-on focused with performance-based questions where you actually perform tasks in simulated environments. Changes the difficulty dynamic completely. CEH's broader in scope covering more domains, while PenTest+ goes deeper specifically in penetration testing methodology. CEH includes more defensive and countermeasure content that PenTest+ glosses over. PenTest+ assumes more baseline technical knowledge going in. Both are similar difficulty but different assessment approaches. CEH tests knowledge breadth, PenTest+ tests practical application.
OSCP comparison isn't even fair, honestly.
OSCP requires 24-hour practical exam with actual system exploitation, privilege escalation, report writing under time pressure. It's a completely different beast. CEH's multiple-choice knowledge assessment. OSCP demands advanced exploitation skills, buffer overflows, post-exploitation techniques at professional penetration tester level. CEH's suitable for broader security roles..analysts, administrators, consultants. OSCP's specifically for penetration testers. Many professionals pursue CEH first because it's more accessible, then OSCP later for deeper expertise if they want to specialize in pen testing, which seems like a smart progression to me.
CySA+ focuses more on defensive security operations, threat detection, incident response, and security analytics. CEH's offensive-focused. CySA+ professionals analyze security events and respond to incidents. CEH professionals understand how attacks work from the attacker's perspective. Different skill sets, different difficulty profiles depending on your background and what you're already comfortable with.
The difficulty you'll experience depends entirely on your background and how you prepare. If you've got networking and system administration experience, put in solid study time with hands-on labs, and use quality practice materials, CEH v13's absolutely achievable. It's not easy, but it's not impossibly hard either. Just respect the exam and prepare properly.
Conclusion
Look, the ECCouncil 312-50v13 CEHv13 exam isn't something you just wake up and pass without putting in the work. Period. The CEH v13 exam cost alone should tell you this isn't a casual weekend cert. You're investing real money and time into something that needs to stick. When you're looking at that CEH 312-50v13 passing score requirement and the sheer breadth of the CEHv13 exam objectives, it becomes pretty clear this is designed to validate actual ethical hacking knowledge, not just memorization skills.
Here's what I've seen work. You need a mix. Official EC-Council CEH exam blueprint materials, hands-on lab time (seriously, don't skip this), and targeted CEH v13 practice tests that mirror the actual CEH v13 question format. The Certified Ethical Hacker v13 syllabus covers everything from reconnaissance to cloud security, and you can't fake your way through tools you've never touched. A lot of people learn that the hard way when they sit down for the actual exam. Set up a home lab. Break things. Fix them. That's where the learning happens.
The CEH prerequisites 312-50v13 might seem flexible, but honestly? If you're coming in without networking fundamentals or basic Linux command-line experience, you're gonna struggle regardless of what the official requirements say. The CEH v13 difficulty isn't just about hard questions. It's about applying knowledge under time pressure across domains you might not use daily in your current role. Even experienced security professionals find themselves second-guessing answers when the clock's ticking. CEH training official courseware iClass helps, but it's not magic.
Once you pass, don't forget about ethical hacking certification maintenance. The CEH renewal requirements demand 120 ECE credits over three years. Those deadlines sneak up faster than you'd think. Some people forget about this entirely until they get that renewal email, then panic because they've got like two weeks left and zero credits banked. Plan for it now.
Before you schedule that exam, though, make sure you're actually ready. Not just "I finished the book" ready, but "I've tested myself under real conditions" ready. That's where CEH v13 study materials meet reality. The 312-50v13 Practice Exam Questions Pack at /eccouncil-dumps/312-50v13/ gives you that final confidence check with questions that actually reflect what you'll face. Use it as your benchmark, not your starting point. If you're consistently scoring well there, you're probably ready to book that exam slot.