CertNexus CFR-410 Exam Overview and Certification Value
Look, the CertNexus CFR-410 exam isn't just another cybersecurity cert to throw on your resume. It's designed for people who need to actually respond when things go sideways. When networks get compromised. When ransomware hits, when executives are freaking out and someone needs to figure out what's happening right now.
What you're actually getting certified for
The CyberSec First Responder (CFR) certification proves you can handle the chaos of an active security incident. Not gonna lie, this is vendor-neutral territory, which means you're learning methodologies and workflows that work regardless of whether your organization runs Splunk, QRadar, or some cobbled-together ELK stack. The exam validates that you can detect threats as they're happening, respond before damage spreads, and recover systems without making everything worse.
I mean, think about it. Most security training teaches you theory or how to use specific products. CFR focuses on what you do when alarms are blaring and management wants answers in 20 minutes. Wait, scratch that. More like 10 minutes while someone's already drafting the press release. The certification covers incident detection, analysis, containment, eradication, and recovery using approaches that translate across different environments. You're not memorizing vendor commands. You're learning how to think when systems are on fire.
Who actually benefits from taking this exam
IT professionals trying to pivot into cybersecurity? They make up a huge chunk of CFR candidates. If you're a network admin who's tired of configuring VLANs and wants to do something more critical, this cert gives you incident response chops without requiring five years of SOC experience first. SOC analysts use it to formalize skills they've picked up on the job. Incident handlers grab it for credibility when dealing with external stakeholders.
Security operations personnel benefit because CFR covers the full incident lifecycle. Not just detection or just forensics, but the entire workflow from "something looks weird" to "threat eliminated and lessons documented." Network administrators find value here too since incidents often involve network-based attacks that require understanding both security and infrastructure. The overlap between network ops and security response is bigger than most job descriptions admit.
The skills this certification actually validates
You're tested on assessing information security risk in practical scenarios. The thing is, the exam throws reconnaissance threats at you. Can you spot when someone's mapping your network or enumerating users? Can you detect network-based attacks as they unfold, not just review logs after the fact?
The incident response procedures section? That's where things get real. You need to know containment strategies, evidence preservation, communication protocols, and recovery priorities. One domain might ask how you'd handle a suspected data exfiltration. Another tests whether you understand the difference between isolating a system and taking it completely offline.
Investigation skills matter here. Heavily.
You're proving that you can analyze artifacts, correlate events across multiple sources, and reconstruct attack timelines. It's scenario-heavy rather than "memorize these 47 port numbers" nonsense. Which honestly makes it harder to cram for, but that's kind of the point.
How employers and the industry view CFR-410
The certification fits with NICE framework work roles, specifically Cyber Defense Analyst and Incident Responder positions. Government contractors love this because it maps cleanly to workforce requirements. Private sector employers recognize it as proof you've got beyond entry-level security knowledge but aren't necessarily a senior forensics investigator yet.
Job postings for SOC analyst incident handling roles? They're increasingly mentioning CFR as preferred or equivalent to other incident response certifications. The vendor-neutral aspect actually helps here because enterprises running mixed security stacks want people who understand concepts, not just button-pushers trained on one platform. Tool vendors change their interfaces every 18 months anyway.
Comparing CFR to other incident response credentials
GCIH costs significantly more and goes deeper into forensics and advanced response techniques. If you've got the budget and experience, GCIH carries more weight in specialized IR roles. But honestly? CFR gets you 80% of the knowledge for maybe 40% of the cost.
CompTIA CySA+ covers broader defensive security but doesn't dive as deep into hands-on incident response workflows. CEH focuses on offensive techniques and ethical hacking. Different skillset entirely. ECIH from EC-Council overlaps more but tends toward tool-specific training. The CFR-410 sits in a sweet spot between foundational security certs and expensive specialized credentials.
Practical application emphasis
The exam uses scenario-based questions that simulate real incident response decisions. You're not just identifying attack types. You're choosing appropriate containment actions, prioritizing investigation steps, and determining when to escalate versus handle internally. This approach tests whether you understand incident response workflow knowledge that translates to actual SOC floor situations where chaos is the default setting and coffee's the only constant. Sometimes not even good coffee.
Framework alignment and methodology coverage
CFR training maps directly to NIST Cybersecurity Framework functions, especially the Detect, Respond, and Recover categories. You'll work with MITRE ATT&CK tactics and techniques throughout preparation. The Cyber Kill Chain methodology gets covered as a mental model for understanding attack progression. Frameworks matter less than knowing when to apply them, but you need the vocabulary to communicate with other teams.
Career trajectory and certification validity
The certification stays valid for three years before renewal requirements kick in. During that window, it is an entry point for SOC analyst roles, helps build cyber threat hunting fundamentals, and gives you digital forensics and triage basics understanding without requiring you to become a full forensics specialist.
The vendor-neutral advantage? It means you're not locked into specific tool ecosystems. Whether you end up working with commercial SIEM platforms, open-source tools, or cloud-native security services, the core incident response principles remain applicable. That flexibility matters when you're job hunting across different industries or company sizes.
International markets recognize CFR alongside other vendor-neutral credentials, and it's relevant for both private sector incident response teams and government security positions that require demonstrated competency rather than product-specific training.
CFR-410 Exam Details: Format, Cost, and Passing Requirements
What this exam actually proves
The CertNexus CFR-410 exam tests whether you can handle actual incidents, not just recite security terms like some kind of trained parrot. You've gotta spot attacker patterns, sort through noisy alerts, keep evidence intact, and make solid calls when everything's on fire. Fast decisions. Real pressure.
Look, it's built around incident response certification skills you'd actually deploy in a SOC or IR team environment. Think SOC analyst incident handling, cyber threat hunting fundamentals, and digital forensics and triage basics, all crammed together in a way that honestly feels way more like actual work than your typical bubble-sheet nightmare.
Who should take it
Perfect fit? SOC analysts, junior incident responders, security engineers who constantly get dragged into "hey can you look at this weird alert" situations, and IT folks pivoting toward blue team work. The thing is, if you've literally never touched logs or endpoint telemetry, you're gonna struggle because the cybersecurity first responder course content just assumes you won't freak out when you see technical output.
Some people wonder about CFR certification prerequisites. Officially? There usually isn't some hard barrier stopping you from booking it, but the exam expects baseline networking knowledge, Windows/Linux comfort, and security fundamentals baked in. You can memorize terms if you want. The performance sections will destroy that approach.
The money part (and how it compares)
CFR-410 exam cost currently sits around $449 USD, though region pricing, taxes, and promotional deals shift that number constantly. Let's be real here. I've seen training partners bundle vouchers at a discount when you grab CertNexus CFR training at the same time, and sometimes employers swing volume pricing that changes everything.
Compared to competitors? Midrange territory. Security+ often runs cheaper depending on voucher hunting and discount timing, while GIAC incident response style certs can explode into thousands once you factor in practice tests, maybe travel expenses. CySA+ usually lands in CFR's general neighborhood when you account for typical voucher deals, but it bounces around like crazy.
Voucher sources: CertNexus website and authorized training partners are your standard routes. Shopping around? Double-check whether that "bundle" includes a retake voucher or just training platform access, because the fine print separates winners from regretful buyers. One line. Huge difference.
Passing score and what "700" really means
The CertNexus CFR passing score sits at a scaled 700 out of 1000. People translate that to "roughly 70%," which works as a mental shortcut, but scaled scoring isn't raw percentage scoring. That's the entire point of the system.
Scaled scoring maps your actual performance onto a consistent scale so different test versions maintain "equal difficulty" even when one form throws nastier curveballs. Honestly, this explains why two candidates swear they missed identical question counts yet land on completely different scaled results. Question weighting varies. Exam forms aren't carbon copies.
Score reporting? Pretty straightforward. You get immediate pass/fail notification when you finish, then domain-level breakdowns appear within roughly 24 to 48 hours, which is what you'll actually use for planning your next move. Or, I mean, celebrating if you crushed it.
Format, timing, and question types
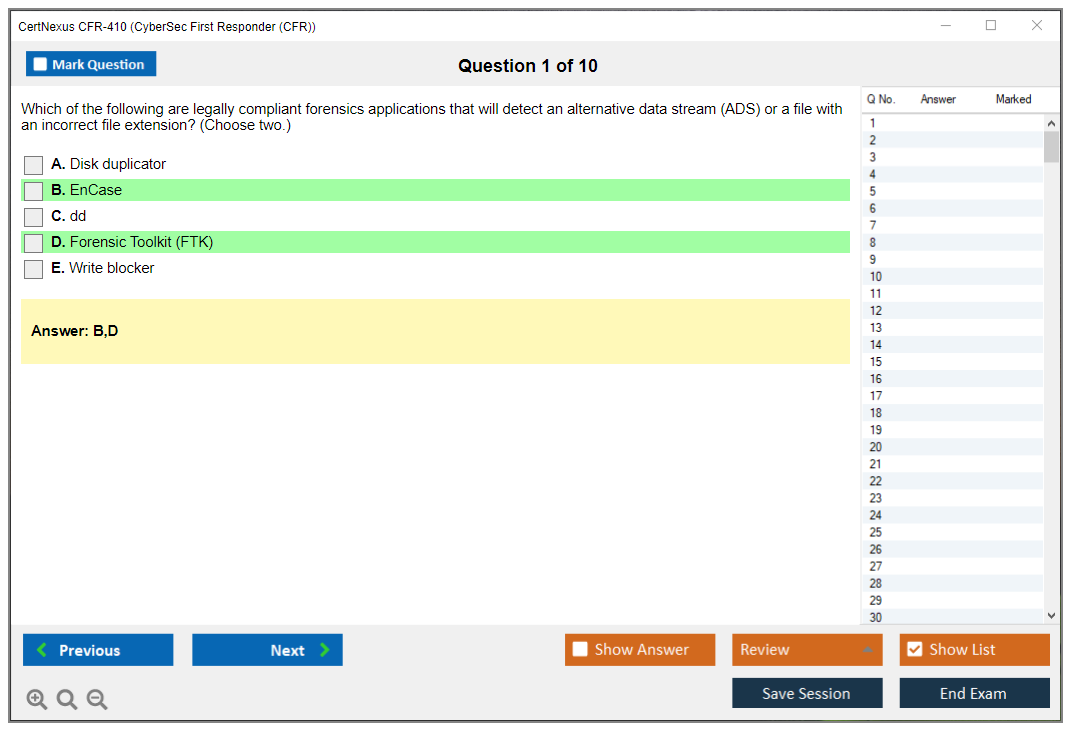
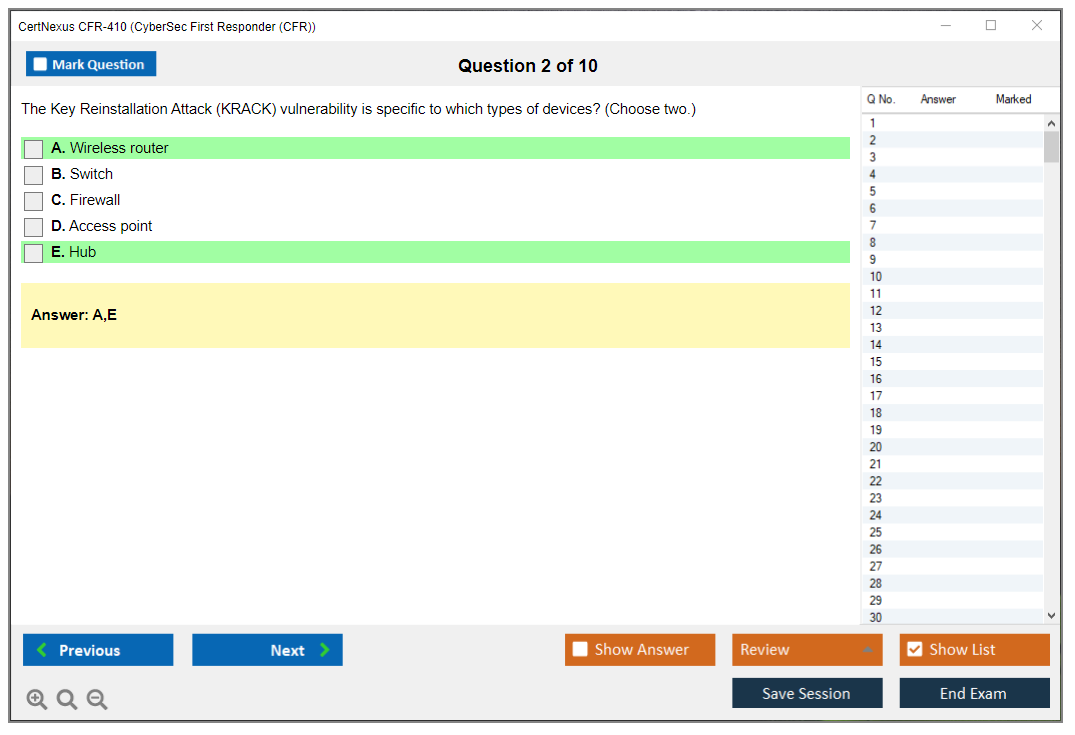
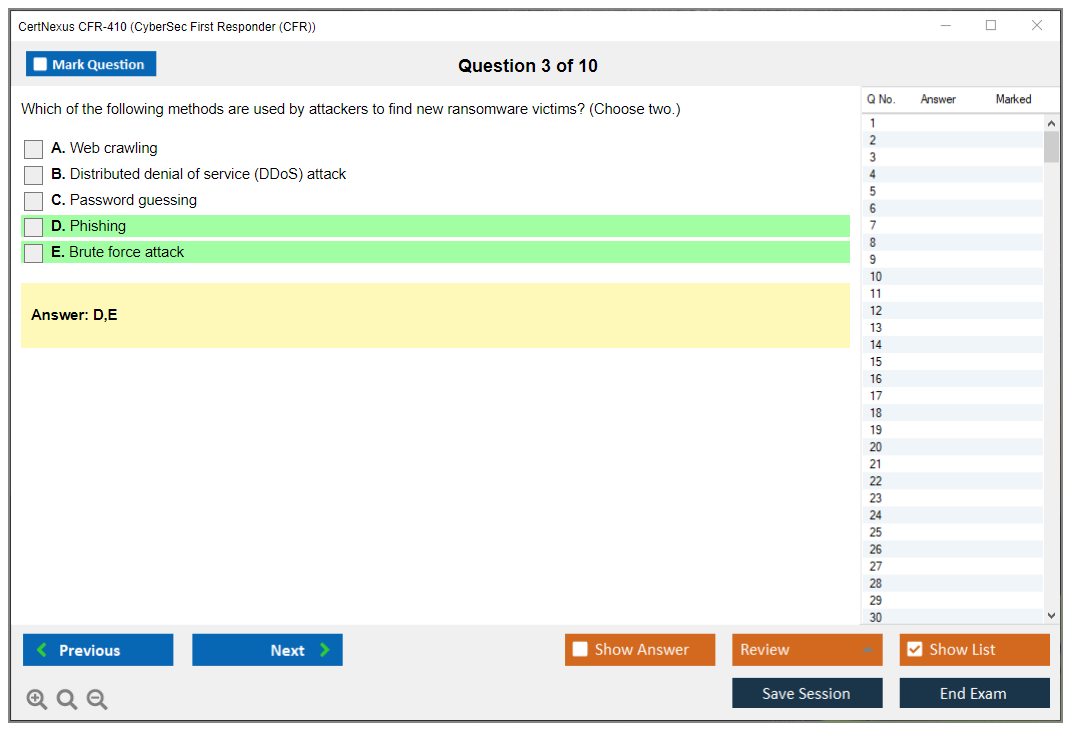
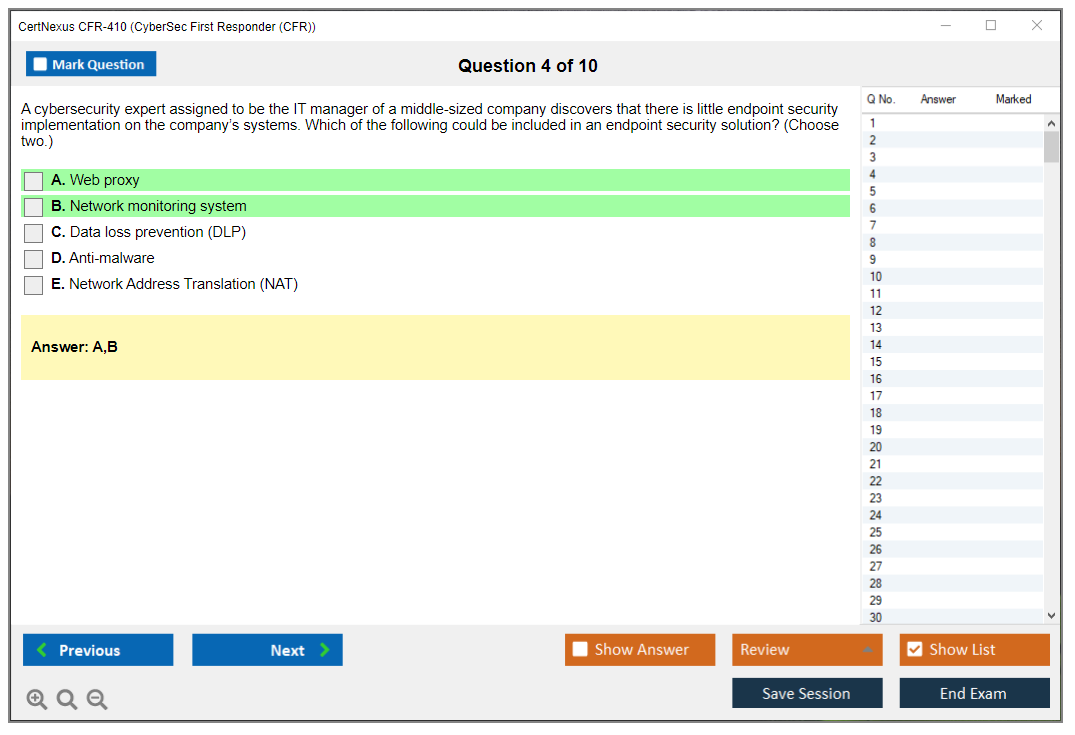
The exam format delivers 100 questions mixing multiple-choice with performance-based scenarios via computer-based testing. Total time clocks in at 165 minutes (2 hours 45 minutes). Quick math? You can't camp on individual items forever, and my personal rule stays simple: target 1.5 to 2 minutes per question on your first sweep, flag the brutal ones, circle back later if time permits.
Question types you'll face include traditional multiple-choice (the easy stuff), multiple-select items where people hemorrhage points by selecting "almost correct" extras, drag-and-drop matching for scenarios (mapping artifacts to attack phases or response actions), and simulated tool-style questions where you interpret output and choose next steps. This part? You cannot cram it the night before.
I once watched someone spend forty minutes on a single drag-and-drop scenario because they kept second-guessing the MITRE ATT&CK framework mappings. Don't be that person. Trust your prep and move forward.
Where you can take it (and what each option feels like)
Delivery options typically include Pearson VUE testing centers and online proctored formats. Both work fine. Both bring their own annoyances.
Testing center experience: show up early, complete check-in procedures, present valid ID (usually one or two forms depending on regional requirements), smile for your photo, lock everything away. No phone access. No notes. Sometimes not even fitness trackers. Then you sit at a computer that looks like it survived multiple apocalypses. Quiet environment. Awkward silence. Reliable setup.
Online proctoring requirements run stricter than most people anticipate. You need functioning webcam and microphone, stable internet connection, and a completely clean desk in a secure room, plus you'll run system compatibility checks before launch. No second monitor allowed. No "my roommate's walking through the background" situations. And yeah, they will terminate your exam if environmental conditions get sketchy. Fragments of sound. The rules aren't negotiable.
Retakes, accommodations, language, and the NDA
Retake policy stays simple and kinda brutal: immediate retakes are permitted, requiring full exam fee payment each attempt, with no mandatory waiting period enforced. That's great if you want rapid rescheduling. It sucks if you expected discounted second attempts.
Accommodations: CertNexus and Pearson VUE process ADA-style accommodations, but you must request them ahead of time with proper documentation, and waiting until exam week is strategic suicide. Paperwork processing takes time. People constantly forget that.
Language availability centers primarily on English, with additional languages occasionally offered in select markets depending on local availability and demand.
Also? You'll sign a non-disclosure agreement before starting. Standard certification stuff. You can discuss your prep strategies and broad topics all day, but not specific questions or detailed scenarios.
Where to get the blueprint (and why you should)
The CFR-410 exam objectives exist as a free downloadable document from the CertNexus website. Grab it. Print it. Treat it like your personal roadmap. It breaks down which domains appear and helps you allocate study time toward what's actually tested, especially around incident response lifecycle steps and tool-and-technique expectations that show up repeatedly.
Quick FAQs people keep asking
How much does the CertNexus CFR-410 exam cost? Around $449 USD, with regional and promotional variation. What is the passing score for the CFR-410 exam? Scaled 700/1000, landing roughly around 70% depending on form difficulty and question weighting. How hard is the CyberSec First Responder (CFR) certification? Medium-hard if you're lacking hands-on IR context, because scenario and workflow questions punish pure memorization strategies. What are the CFR-410 exam objectives and domains? Download the official objectives document and use it as your primary study map. How do I renew the CertNexus CFR certification? Renewal requirements depend on CertNexus policy updates, but expect a validity period with continuing education or recertification options. Check the current CFR certification renewal page before making long-term plans.
CFR-410 Exam Objectives and Domain Breakdown
Look, if you're serious about breaking into incident response or leveling up your SOC analyst game, you need to understand what the CertNexus CFR-410 exam actually tests. This isn't one of those certs where you memorize port numbers and call it a day. We're way past that kind of surface-level stuff.
The five-domain framework that mirrors real IR work
The CFR-410 structures its content around five primary domains that basically walk you through the entire incident response lifecycle, from threat assessment all the way through post-incident activities. It's honestly pretty well thought out compared to some vendor certs that just throw random security topics at you.
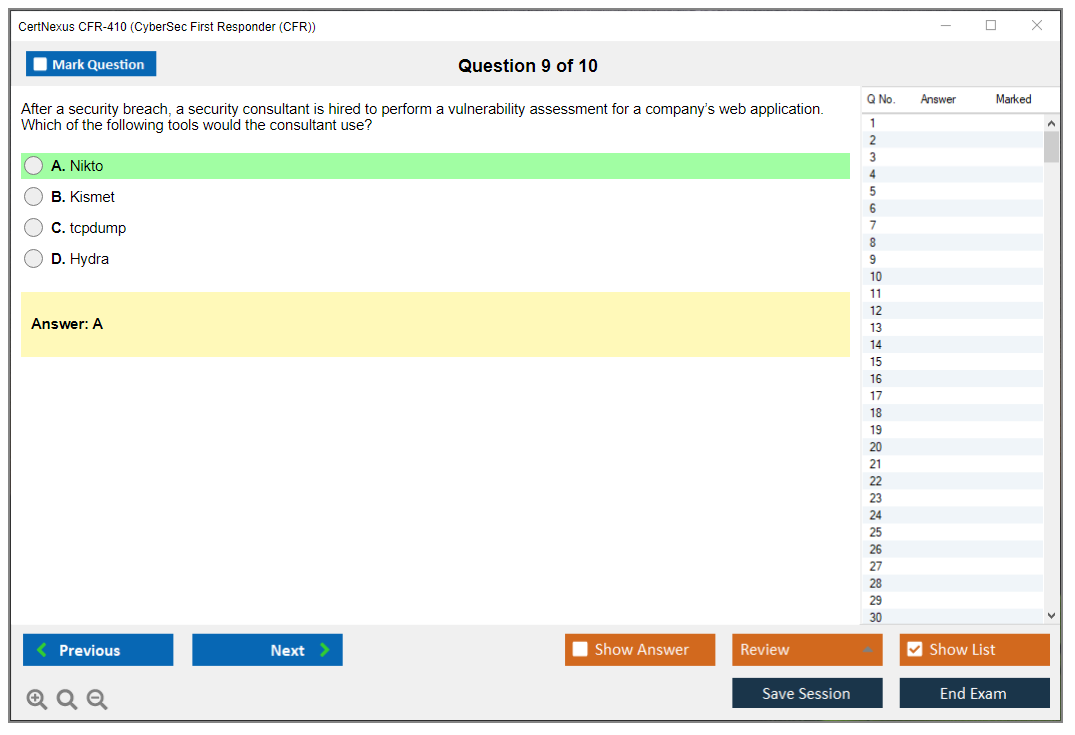
Domain 1 covers assessing information security risk. That's 15% of the exam. You're identifying threat actors and attack vectors that actually matter to your organization's assets, not just generic boogeyman stuff. Though, the thing is, sometimes those "generic" threats turn out to be your biggest problem. The vulnerability assessment piece gets into penetration testing concepts without requiring you to be a full-blown pentester. You'll evaluate security controls across administrative, technical, and physical categories, which sounds boring but is really useful when you're trying to figure out where your defenses are weakest. Risk analysis methodologies come up too. Qualitative versus quantitative approaches. And yeah, you need to know your risk treatment strategies: acceptance, avoidance, transference, and mitigation.
Where reconnaissance detection gets serious
Domain 2 jumps to 21% of the exam and focuses on analyzing reconnaissance threats. This is where packet analysis becomes your friend (or enemy, depending on how comfortable you are with Wireshark). Detecting network reconnaissance activities means you're looking at actual traffic patterns, not just reading about them in some sterile textbook scenario that bears zero resemblance to the chaos you'll encounter in production environments. Social engineering tactics get covered: phishing, pretexting, baiting, tailgating. The whole playbook adversaries use before they even touch your network.
Application-level reconnaissance targeting web apps and APIs is in here too. Footprinting and enumeration activities show up in system logs and network traffic, and you better know what normal looks like versus suspicious. OSINT methods are huge here because that's exactly how attackers scope you out during the reconnaissance phase. Side note, but I once watched a pentester find our CEO's home address, phone number, and kids' school in about fifteen minutes using nothing but LinkedIn and property records. Made that "OSINT isn't a real threat" conversation with management a lot shorter. Anyway, the exam maps all this to MITRE ATT&CK Tactic TA0043 and associated techniques, which is super practical if you work in a modern SOC.
The biggest chunk tests actual attack analysis
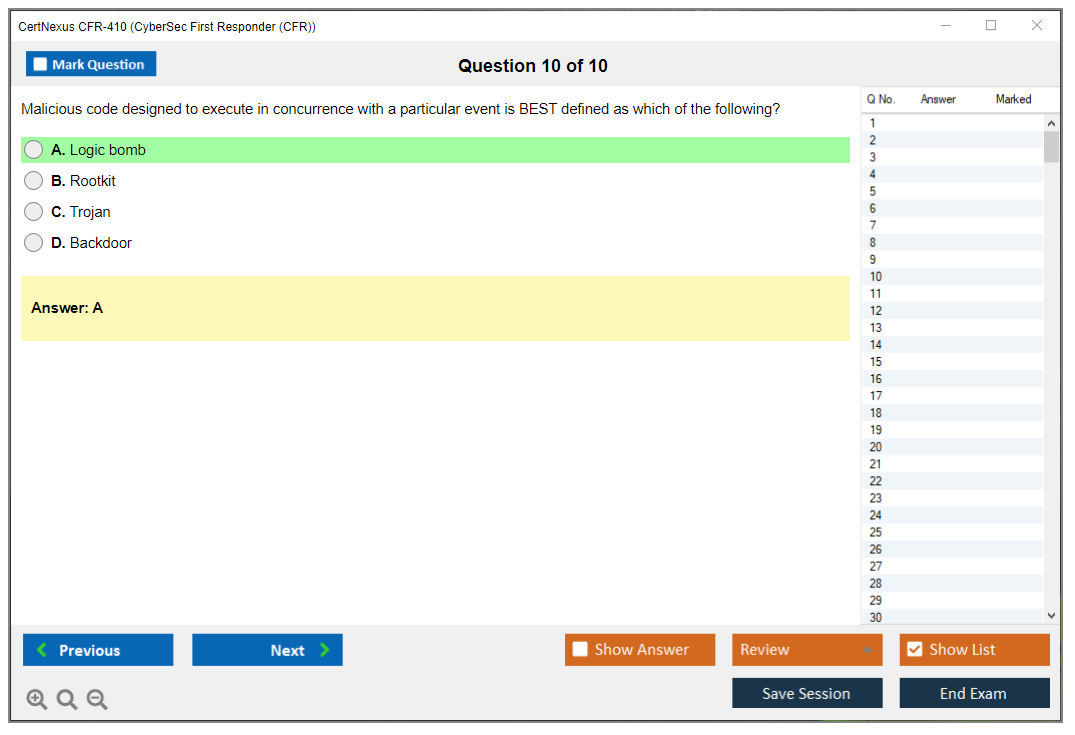
Domain 3 is 27% of the exam. Heaviest weighted section. Common attack types include malware infections, DDoS, man-in-the-middle, injection attacks, and privilege escalation. You're analyzing indicators of compromise in endpoints, network traffic, and application logs, not just listing what an IOC is like some dictionary definition nobody actually uses.
Lateral movement detection is critical here. Pass-the-hash, RDP abuse, PowerShell exploitation. These are the techniques that turn a single compromised workstation into a full domain takeover, and I mean, we've all seen that nightmare scenario play out. Persistence stuff gets examined because adversaries want long-term access, not just a quick smash and grab. Data exfiltration methods need to be on your radar so you can detect unauthorized data transfers before everything ends up on a paste site.
The exam correlates attack patterns with both Cyber Kill Chain phases and the MITRE ATT&CK framework, which honestly just reflects how the industry works now. Static and dynamic malware analysis fundamentals round this out. You won't become a malware reverse engineer, but you'll understand the basics enough to communicate with the folks who are.
Incident management separates amateurs from pros
Domain 4 sits at 25%. It covers managing incident response. This follows NIST SP 800-61 guidelines because that's basically the incident response bible, though some folks swear by SANS, and honestly both approaches have merit depending on your environment. Evidence collection and chain of custody procedures matter for digital forensics and triage basics. Screw this up and your evidence is worthless in any legal proceeding.
Containment techniques? Isolation, segmentation, system quarantine. Communication coordination during incidents involves stakeholders, management, and external parties, which is where many responders struggle in real scenarios. Documentation of incident details, timelines, and response actions feeds into reporting and lessons learned. Unglamorous work, but it saves your neck later.
You need to understand escalation procedures and when to loop in law enforcement or external IR teams. Incident severity classification and prioritization frameworks help you triage when everything's on fire simultaneously, which, the thing is, happens more often than leadership wants to admit. SIEM tools and incident response platforms for case management get tested because that's the tooling you'll actually use.
Post-incident activities close the loop
Domain 5 is 12% and covers post-incident response techniques. Root cause identification through post-incident analysis prevents the same incident from happening again next week. You'd be surprised how many organizations skip this step and wonder why they keep getting popped. Remediation strategies address the vulnerabilities that got exploited in the first place.
Lessons learned sessions? Critical. Playbook updates turn incidents into organizational knowledge instead of just painful memories people don't talk about. Security control improvements based on incident findings actually make your environment stronger. You can't ignore regulatory and compliance reporting obligations. Some incidents require external notification whether you like it or not. System restoration and recovery validation ensure you're actually back to normal. Tracking metrics for IR effectiveness and team performance gives you data to improve instead of just vibes-based assessments.
Cross-cutting skills and tool expectations
Network protocol analysis (TCP/IP, HTTP, DNS), operating system security for Windows and Linux, log analysis, SIEM query construction, and scripting fundamentals for automation appear throughout all domains, so yeah, you can't just focus on one area and hope for the best. The exam is vendor-neutral but scenarios reference Wireshark, Sysinternals Suite, Volatility Framework, YARA rules, and open-source SIEM platforms.
Questions are scenario-based, presenting realistic incident situations requiring multi-step analysis and decision-making. This tests whether you can actually apply knowledge in SOC analyst incident handling workflows and cyber threat hunting fundamentals, not just regurgitate definitions you memorized the night before. Honestly, that's what makes the CFR-410 more valuable than some other incident response certifications. It focuses on what you'd actually do during an incident, not what looks good on a PowerPoint slide.
CFR Certification Prerequisites and Recommended Experience
Quick snapshot of what CFR-410 is about
The CertNexus CFR-410 exam is built around real incident handling. Triage stuff. Containment. Evidence. Communication, obviously.
If you've done SOC work, on-call ops, or even messy "security-ish" tickets in IT, the CyberSec First Responder (CFR) certification will feel familiar because it tests how you think under pressure, not just whether you memorized terms. Honestly that's why people find it both useful and irritating, depending on their background and how much practical experience they've actually accumulated in the trenches.
What the CFR certification proves
This incident response certification is basically saying: you can show up mid-incident, interpret what you're seeing, and not make the situation worse. That means log review, packet sniffing, endpoint triage, and knowing when something is "weird but fine" versus "this is active compromise."
Look, the exam isn't trying to turn you into a full digital forensics person. It's more digital forensics and triage basics. Enough to preserve evidence, capture the right artifacts, and hand off to the deeper forensics folks without nuking timestamps. Which, I mean, sounds simple until you're actually staring at a live incident and your boss is breathing down your neck.
Who should take it (and who shouldn't)
The ideal candidate profile is someone with 3 to 5 years in IT roles where security slowly became your problem. Or 1 to 2 years in a dedicated security operations position doing SOC analyst incident handling. That's the sweet spot, really.
New to cybersecurity? Pause. Not forever, obviously. Just long enough to stop drowning in acronyms and basic concepts that everyone assumes you already know.
CFR-410 exam details you'll care about
Cost matters. So does the passing bar, even if people pretend it doesn't affect their study strategy.
CFR-410 exam cost
People always ask, how much does the CertNexus CFR-410 exam cost? It varies by training provider, voucher deals, and region, so I'm not going to throw a single number out and pretend it's universal. You should expect "professional cert pricing," not entry-level pricing, especially if you bundle it with CertNexus CFR training. The thing is, sometimes the bundle saves you money compared to piecing everything together separately, so do the math before you commit.
Passing score and format
Next: what is the passing score for the CFR-410 exam? CertNexus publishes exam policies, but the exact CertNexus CFR passing score details can change over time, and some vendors avoid making it the headline anyway, which is annoying. Plan like you need to be strong across domains, because weak areas show up fast in scenario questions.
Delivery is typically proctored, often online. Time limit and question count depend on the current exam blueprint. Check the official listing before scheduling. One sentence, yes. Still important, though.
What the exam objectives feel like in practice
People also ask: what are the CFR-410 exam objectives and domains? High-level, you're living in the incident response lifecycle. Preparation, detection, analysis, containment, eradication, recovery, plus reporting and lessons learned. Basically the whole messy cycle that never actually ends as cleanly as the frameworks suggest it should.
The tools and techniques mapped to objectives are the usual suspects: packet capture, endpoint indicators, basic malware behaviors in a controlled view, and correlation thinking. Not fancy threat hunting platform stuff. More cyber threat hunting fundamentals like "what log source would prove this?" and "what would you grab next?" before everything gets overwritten or the attacker notices you're onto them.
The actual CFR certification prerequisites (and what you really need)
Here's the clean answer on CFR certification prerequisites: CertNexus has no mandatory certifications or formal prerequisites required to attempt the CFR-410 exam. You can book it whenever, honestly. No gatekeeping there.
Now the messy truth. No prerequisites doesn't mean "no background needed," because the exam assumes you can read a network conversation, understand what an admin tool looks like, and tell the difference between normal authentication noise and something that smells like credential stuffing. Wait, let me rephrase that. It expects you to already have pattern recognition built from actual experience.
Recommended baseline knowledge areas
You want a solid understanding of networking concepts. OSI model stuff. TCP/IP protocol suite. Routing and switching basics that don't make your eyes glaze over. If you've never looked at a TCP handshake or you don't know why DNS can ruin your day, you'll spend half the exam translating the question instead of answering it, which burns precious time you don't have.
You also need Windows and Linux familiarity. File systems, user management, and basic command-line operations that don't require constant Googling. Nothing exotic, thankfully. But you should know where logs live. What a service account is. How to do quick checks without clicking around for ten minutes like you're hunting for Waldo.
Information security principles matter too. CIA triad. Authentication vs authorization. What "integrity" actually means when you're staring at altered logs and trying to figure out your timeline. Add basic security tech on top: firewalls, IDS/IPS, antivirus, endpoint protection. Mentioned casually, but you need the mental model behind them.
Tools, scripting, and incident context
Hands-on exposure to packet capture analysis, log review, and security information correlation is the difference between "I studied" and "I can answer this." Wireshark sessions. Sysmon logs. Simple SIEM queries that don't require a PhD. Even just reading Windows Event IDs without panicking helps.
Scripting and automation familiarity isn't heavily tested, but basic PowerShell, Python, or Bash helps you understand automation-related questions and not misread them as something completely different. Fragments of knowledge. Worth it, though. Side note: I once watched someone spend twenty minutes trying to parse a log file manually because they refused to learn regex. Don't be that person. Even terrible regex beats manual grep when you've got thousands of lines to sort through.
Incident response exposure helps a lot, no question. If you've participated in investigations, even as the person pulling logs or isolating hosts, the scenarios click faster. You've seen the human chaos part. The ticketing mess. The "wait, which system is authoritative?" arguments that happen in every single real-world incident.
Best path depending on where you're starting
Entry-level candidates should strongly consider foundational certs first. CompTIA Network+ if networking is shaky and unpredictable. CompTIA Security+ for security basics that everyone assumes you already have. Then step into CFR territory. Not gonna lie, that order saves you weeks of frustration, confusion, and wondering why nothing makes sense.
CertNexus CFR training is the fast lane for people without direct IR time, honestly. It's a 5-day instructor-led course with hands-on labs covering the CFR-410 exam objectives. If you've never done containment steps or evidence handling, that structure matters because self-study can turn into random YouTube wandering and Reddit rabbit holes that waste your time.
Self-study is totally doable for experienced responders who've already been through the fire. If you've already lived the workflow, you can prepare with official materials, home labs, and a good CFR-410 practice test strategy that exposes your weak spots. If you want a question pack to drill weak spots systematically, CFR-410 Practice Exam Questions Pack is a straightforward option at $36.99. I mean use it as a diagnostic tool, not as your whole plan or some magic shortcut.
Prep timeline that won't wreck your life
Experienced IR professionals (2+ years): 4 to 6 weeks of focused review and labs, assuming you're consistent. IT pros transitioning to security: 8 to 12 weeks, realistically. Expect to build reps on logs and packets until they become second nature. Entry-level candidates: 12 to 16 weeks minimum, because you're building foundations plus exam prep at the same time, which is honestly exhausting but necessary.
Also, build a lab. A couple of VMs running different operating systems. A Windows box for practice. A Linux box for contrast. Packet capture tools installed and configured. Sample malware only in an isolated environment where you can't accidentally wreck your production network. Because that's happened to people, trust me.
Extra signals that make CFR prep easier
Complementary certs help more than people admit. Security+ for basics everyone expects. CySA+ for defensive concepts and thinking. CEH if you need more attacker-method context, even if the branding annoys you or feels overhyped.
Industry knowledge sources matter more than people admit, honestly. Read threat intel reports regularly. Follow incident writeups from reputable sources. Case studies from real breaches. You start recognizing patterns without thinking about it, and the exam is full of pattern recognition exercises disguised as scenario questions.
Community helps too, surprisingly. Forums where people actually help. Local ISSA/ISC2 chapters if they're active. Incident response working groups. You hear how teams actually operate in the wild, not how a study guide claims they do in some idealized fantasy world.
Renewal and keeping it active
People ask, how do I renew the CertNexus CFR certification? CFR certification renewal rules can change over certification cycles, so check the current CertNexus policy for cycle length. Whether they want continuing education units, coursework, or a retest option that nobody wants. If you wait until expiration, you usually pay more in time and hassle and bureaucratic nonsense. That's the real penalty nobody warns you about.
If you're building your final review plan, do a couple rounds of timed questions first. Then patch gaps with targeted labs. Finish with another practice pass to confirm you've actually improved. And if you want extra reps right before scheduling your exam date, CFR-410 Practice Exam Questions Pack is an easy add, especially when you're trying to get comfortable with scenario wording and question formats on the CertNexus CFR-410 exam.
Assessing CFR-410 Exam Difficulty and Success Factors
Understanding where CFR-410 sits in the certification space
Real talk here. The CertNexus CFR-410 exam occupies this interesting middle ground that makes it both accessible and challenging at the same time. It's definitely harder than Security+ if you're coming from that world, but nowhere near the technical brutality of OSCP or GCIH. Think of it as the certification that bridges theory and actual hands-on incident response work.
Here's the annoying part. CertNexus doesn't publish official pass rates. But based on what I've seen in forums and talking to people who've taken it, first-attempt pass rates seem to hover around 60-75% for candidates who actually prepared properly. That's not terrible, honestly. It's also not a gimme.
What actually makes this exam tough
Scenario-based questions? Total trip-up zone. You're not just answering "what tool does X." You're reading through multi-paragraph incident descriptions and figuring out what to do next. These questions demand multi-step reasoning. Real incident response isn't multiple choice, and the exam reflects that reality in ways that'll surprise you if you're expecting straightforward knowledge checks.
The performance-based items really separate people who've touched the tools from those who just read about them. Simulated interfaces, drag-and-drop activities, log analysis tasks that go beyond simple recall. You can't cram your way through a Wireshark packet capture analysis or Windows Event Log interpretation if you've never actually done it before.
Time pressure? Brutal. 100 questions in 165 minutes sounds reasonable until you hit question 70 and realize you've got 30 questions left with 40 minutes remaining, and suddenly your palms are sweating. Efficient question processing becomes critical.
The breadth of coverage across five domains means you can't just be amazing at network forensics and coast through everything else. You need balanced preparation. Threat detection. Vulnerability management. Incident response procedures. Digital forensics basics. Threat intelligence. Specialization doesn't help you here, which is frustrating if you're really strong in one particular area.
And honestly? The ambiguous answer choices mess with people's heads more than anything. Multiple options might seem partially correct because incident response often involves judgment calls, and the thing is, you're selecting the "best" response based on standard procedures and best practices. This requires understanding the incident response workflow at a deeper level than just memorizing facts from a study guide.
Where candidates typically struggle
Insufficient hands-on experience with packet analysis tools absolutely kills people on network-based attack scenarios. I mean, if you've never actually analyzed suspicious traffic in Wireshark or interpreted flow data, those questions become educated guesses at best. Same goes for weak understanding of Windows and Linux log formats. Questions present log snippets expecting you to identify the security event or anomaly, and if you don't recognize the format, you're just stuck there.
Inadequate familiarity with incident response workflow causes poor decision-making on containment and eradication scenarios, which is where theory meets reality. Someone might technically understand malware persistence mechanisms but choose the wrong response order when the question asks what to do first in a live incident. It's one thing to know about registry autoruns and scheduled tasks. It's another thing entirely to know when you tackle them during an active breach while systems are still compromised and attackers might be watching.
I've seen people confuse similar attack techniques constantly. Is this lateral movement or privilege escalation? What's the appropriate countermeasure difference between a credential harvesting attack versus a pass-the-hash attack? The exam tests these distinctions relentlessly.
Time management issues lead to rushed responses on the final 20-30 questions, which is brutal because those questions count just as much as the earlier ones you spent five minutes analyzing while stress-eating mental energy.
Who actually passes on the first shot
SOC analysts with 1-2 years of active incident handling experience tend to crush this exam. They've lived the scenarios, dealt with the stress, made the judgment calls. IT professionals who completed official CertNexus CFR training with dedicated lab practice also do well because that training aligns directly with exam objectives in ways self-study sometimes misses.
Candidates who supplemented study with hands-on tool practice and simulated incident scenarios understand the practical application, not just theory. And those who used quality CFR-410 practice test resources to identify knowledge gaps before exam day walk in knowing exactly where they're weak and where they're strong, which gives you this confidence boost that really matters.
Who ends up retaking it
Entry-level candidates without prior security operations exposure attempting certification too early is a pattern I see repeatedly. I mean, you can technically take it, but should you? Probably not if you've never worked in a SOC or handled real incidents. You're setting yourself up for disappointment.
Experienced professionals who underestimated exam difficulty and prepared inadequately get surprised by the practical depth. Just because you're a senior sysadmin doesn't mean you understand incident response procedures the way this exam expects.
Candidates focused solely on theory without developing practical tool skills struggle with performance-based questions every single time. Those with strong technical skills but weak incident response procedure knowledge make poor decisions on scenario questions because they don't understand the response lifecycle or why certain steps come before others.
What actually determines success
Hands-on practice matters. Wireshark, Sysinternals tools, log analysis platforms. You need tactile experience, not just reading about them. Understanding incident response workflows and decision points matters more than isolated technical facts because the exam tests your judgment, not your memory.
You need to know why you're doing something, not just what to do. That distinction trips up book-smart candidates constantly.
Reviewing actual incident response case studies helps you see concepts applied in real scenarios rather than sanitized textbook examples. Taking multiple full-length simulations under timed conditions through a CFR-410 practice exam prepares you for both the content and the pressure, which honestly can't be replicated any other way.
Identifying personal weak domains through practice exams lets you focus remediation efforts where they'll actually help instead of spreading yourself thin. Don't spend equal time on everything. Shore up your weaknesses while maintaining your strengths. That's just smart preparation strategy.
Mental game and exam strategy
The 165-minute session tests focus and endurance as much as knowledge. Managing exam anxiety matters because second-guessing yourself on challenging questions wastes time and mental energy you'll desperately need later. When uncertain, apply incident response best practices and NIST guidelines to eliminate obviously incorrect options. Strategic guessing beats random selection every time if you're using frameworks to guide your thinking.
Compared to related certifications? CFR-410 is generally more practical than CEH, more focused than CySA+, and less technically demanding than GCIH. That positioning makes it valuable for people building incident response careers without requiring expert-level depth in any single area, which is actually pretty smart positioning by CertNexus.
Full CFR-410 Study Resources and Training Options
What the CFR credential proves
The CertNexus CFR-410 exam targets the "first responder" layer of security work. The folks who catch alerts, validate them, contain threats, and prevent total business meltdown. We're talking incident triage, basic forensics, log analysis, network investigation, and documenting everything so someone else can follow your trail later. Real work. Messy, chaotic work.
The thing is, the CyberSec First Responder (CFR) certification isn't some entry-level vocab quiz, but it's also not a pure malware reverse engineering flex either. It's designed for SOC analysts, junior IR folks, sysadmins who keep getting yanked into security incidents whether they like it or not, and basically anyone needing a structured incident response certification that actually maps to common playbooks and frameworks you'll encounter in the wild.
Who this exam fits (and who it doesn't)
If you're already doing SOC analyst incident handling, you'll recognize the flow. Most of it, anyway.
Brand new? You can still pass, honestly, but you'll need reps. Lots and lots of reps. Labs matter way more than reading ever will.
I mean, if your entire background is "I watched a few hacking videos on YouTube," you're gonna absolutely hate the scenario questions because you won't have developed instincts yet for triage, evidence handling, and deciding what to tackle first when five different things are simultaneously on fire and everyone's yelling at you. My first SOC gig, I once spent twenty minutes chasing what turned out to be a scheduled backup job because the alert description was garbage and nobody had bothered updating the runbook in six months. That kind of experience teaches you to ask better questions faster, which is exactly what this test wants to see.
Price, logistics, and the stuff nobody reads
People always ask about money first, so here you go, let's get it out of the way. CFR-410 exam cost varies by region and partner, and it's often bundled with training vouchers, so you'll see wildly different numbers depending on how you actually buy it. Training's where the big spend is, not the voucher itself.
The CertNexus CFR passing score and exact exam parameters can shift over time, so don't trust random forum posts from 2019 like they're gospel. Check the current candidate guide and the CFR-410 exam objectives PDF directly on CertNexus. That PDF is free, and it's the closest thing you'll get to "this will definitely be on the test." Time limit, delivery method, retake policy? All spelled out there. Boring documentation. Also, the difference between calm test day and full panic mode.
What's actually covered (domains, tools, workflows)
At a high level, the CFR-410 exam objectives track the incident response lifecycle. Preparation, detection, analysis, containment, eradication, recovery, and post-incident activity. You'll encounter digital forensics and triage basics, log review, packet inspection, endpoint artifacts, and reporting requirements.
A lot of candidates seriously underestimate how much "process" actually shows up on this thing. Chain of custody procedures. Documentation standards. Escalation paths. Basic threat intel context. You don't need to memorize every single vendor tool, but you absolutely do need cyber threat hunting fundamentals like "what artifact proves this actually happened" and "what data source confirms it beyond reasonable doubt."
Prereqs and the real-world baseline
CFR certification prerequisites are usually pretty light on paper, but don't confuse that with "easy." You want solid comfort with TCP/IP, Windows and Linux basics, and security fundamentals like common attack types and knowing what logs to pull when something looks off.
Beginners should plan extra time for the tools. Experienced responders can move faster, but only if they've actually done real investigations, not just watched dashboards update while sipping coffee. Knowing what Sysmon is and knowing how to actually use Sysmon effectively are not remotely the same skill.
How hard is it, really
"How hard is the CyberSec First Responder (CFR) certification?" Hard enough to punish passive study habits. Period.
The questions tend to be scenario-based, and they reward people who can follow an IR workflow under pressure, pick the next best action from imperfect options, and avoid destroying evidence while trying to be a hero and save the day single-handedly.
Common mistakes? Predictable. Overthinking basic containment steps. Ignoring documentation requirements. Getting lost in malware details when the question's really about triage priority. Another one people hit constantly: they study definitions endlessly and skip hands-on practice, then they see a Wireshark screenshot and completely freeze up.
Official CertNexus training options
If you want the straight path, the official stuff's solid. Just pricey.
The instructor-led CyberSec First Responder course is a 5-day bootcamp style class with hands-on labs covering all the domains, and it typically runs $2,995 to $3,500 depending on which provider you go through. Fast. Intense. It's also the closest thing to "do exactly what the exam expects," because the labs force you to practice the precise motions you'll need when you're staring at suspicious logs at 2 a.m. and your boss is breathing down your neck.
You also get the Official CertNexus CFR Student Manual with instructor-led training. You can sometimes buy it separately through authorized partners if you look around. That manual's the core textbook. Not glamorous. Very test-aligned, though.
Prefer self-paced? CertNexus has an eLearning platform version with videos, interactive labs, and knowledge checks, usually running around $1,200 to $1,500. The win here is pacing control. The risk? Procrastination. Real talk.
Also, grab the official exam objectives document straight from the CertNexus website. Free PDF. Print it out. Highlight everything you can't explain clearly to someone else.
Books, labs, and practice that actually moves the needle
For books, the "CyberSec First Responder CFR-410 Cert Guide" is the obvious exam-prep pick because it stays mapped to domains and usually includes practice questions that mirror the real thing. Pair it with NIST SP 800-61 Rev. 2 because that incident handling guide is basically the grown-up version of what every IR process tries to be, and the exam absolutely loves that mindset and framework.
Then go hands-on. Actually touch things.
RangeForce incident response modules are great if you want guided, realistic incidents in a browser without complicated setup. CyberDefenders Blue Team Labs is where you grind hard, and it's free for a lot of content, so you can hammer log analysis, network forensics, and investigation flow without begging your employer for a budget line item. SANS cyber ranges exist too. Premium option, definitely not for everyone's wallet.
Build a home lab if you're serious about this. VirtualBox or VMware, a couple Windows boxes, a Linux box, Security Onion for a SIEM feel, and packet capture tools for network visibility. Add a malware analysis sandbox with isolated VMs plus REMnux and FLARE VM for safe practice without nuking your actual system. Keep it isolated, though. No shortcuts here.
Tool-wise, you'll keep running into Wireshark, Sysinternals, Volatility, YARA, and SIEM querying like Splunk or ELK stacks. Read docs first, then touch the tools. Clicking around actually matters more than you think.
Practice tests and smart exam prep
A CFR-410 practice test is useful only if you treat it like a diagnostic tool, not a magic solution. Take one early, identify your weak domains, then go back to labs and notes for targeted improvement. Don't just spam question banks mindlessly until you memorize phrasing patterns. That's not learning.
If you want extra reps, I sell a targeted pack that's meant for drilling and review: CFR-410 Practice Exam Questions Pack at $36.99. Use it after you've studied a domain properly, not before, and you'll get way more value out of it. Save a second pass of the CFR-410 Practice Exam Questions Pack for the final week when you're tightening timing and building confidence under pressure.
Final week checklist? Sleep properly. Re-read the objectives one more time. Do two or three timed practice sets under real conditions. Write down your personal "IR order of operations" so you stop second-guessing yourself mid-question when anxiety kicks in. If you want one more focused push before exam day, the CFR-410 Practice Exam Questions Pack is a decent way to keep your brain in exam mode without spending another grand on a full course you don't need at that point.
CFR certification renewal is typically handled through continuing education credits or a recert path, depending on CertNexus rules at the time you're actually reading this. Don't assume it's lifetime. It's not. Check the current policy, track your credits religiously, and keep receipts of training and events you attend.
Let it expire? You're usually looking at extra steps to get it back, and yeah, that's exactly as annoying as it sounds.
How much does the exam cost? Variable, and often bundled with training. Check the current voucher pricing through CertNexus partners for accurate numbers.
What's the passing score? CertNexus publishes it in the candidate info, and it can change between versions.
How long to prep? Two weeks if you're already doing IR daily and living this stuff. Four to eight weeks if you're building skills from scratch, especially on tools and digital forensics and triage basics that require muscle memory.
Conclusion
Why the CertNexus CFR-410 exam matters for your career
Straight up?
The CyberSec First Responder (CFR) certification isn't just another cert to plaster across your LinkedIn profile like some kind of digital trophy case. It's honestly one of those credentials that actually demonstrates to hiring managers you can handle the absolute chaos when incidents go sideways, not just pontificate about theoretical frameworks in some sterile meeting room while everyone pretends to care. The job market for SOC analysts and incident handlers? Competitive as hell right now. Having CFR-410 on your resume puts you in an entirely different conversation during interviews.
The exam itself?
Not gonna lie, it's challenging. You're looking at roughly 90 minutes for what CertNexus throws at you, and these aren't softball questions about memorizing port numbers or regurgitating textbook definitions. They want to see you understand the entire incident response lifecycle, from initial detection through containment and recovery. The CertNexus CFR passing score typically hovers in that 70-75% range, which sounds reasonable until you're actually sitting there working through scenario-based questions that test whether you actually know SOC analyst incident handling or just.. memorized some flashcards the night before.
Cost-wise, the CFR-410 exam cost runs about $350-$400 depending on your location and testing center. Middle-of-the-road for cybersecurity first responder course certifications. Not cheap but not CompTIA PenTest+ expensive either. CFR certification prerequisites are pretty minimal officially, but honestly you should have at least 6-12 months working with security tools before you attempt this thing. The cyber threat hunting fundamentals and digital forensics and triage basics covered in the CFR-410 exam objectives assume you've seen real alerts before, not just lab simulations.
I actually remember this one guy in my study group who tried jumping straight into CFR with zero SOC experience. Lasted about two weeks before he realized he didn't even know what a SIEM dashboard was supposed to tell him. You can technically sit for the exam without prerequisites, sure. Doesn't mean you should.
Here's what I recommend.
Get your hands dirty with practice before you schedule. Real talk, the best way to prepare is working through quality CFR-410 practice test materials that mirror the actual exam scenarios. The thing is, you need experience with incident response workflows, not just rote memorization. The CertNexus CFR-410 Practice Exam Questions Pack gives you that scenario-based experience. Not just memorization dumps but actual incident response workflows you'll face on test day. Combine that with some hands-on lab time and official CertNexus CFR training materials, and you're setting yourself up properly.
CFR certification renewal happens every three years, so plan for that. But honestly? Once you pass CFR-410 and get that incident response certification under your belt, you'll find doors opening for IR analyst and forensics positions that weren't even responding to your applications before.