GIAC GCED Certification: Complete Guide to the GIAC Certified Enterprise Defender Exam
What GCED actually validates in enterprise security
Real talk here.
The GIAC Certified Enterprise Defender certification is designed for folks who need proving they can actually defend networks against real threats, not just talk about them during meetings. There are tons of certs out there focusing on breaking things or theoretical security models, but GCED sits firmly in the defensive camp where you're the one building walls and watching for intruders trying to climb over them. You know, the people who actually have to deal with the aftermath when things go wrong.
This cert validates your ability handling advanced persistent threats, configuring defensive infrastructure properly, and detecting when something goes sideways in your enterprise environment. You get tested on Windows and Linux hardening fundamentals, security monitoring that actually catches things, and incident detection and response capabilities that matter when executives start asking uncomfortable questions at 3am.
What makes GCED different? Its focus on practical, hands-on defensive techniques across diverse enterprise environments rather than memorizing security frameworks or vendor-specific tools. You need to demonstrate you can apply defensive security controls in real-world scenarios. That's way more valuable than regurgitating textbook definitions.
Who actually benefits from getting GCED certified
SOC analysts are probably the biggest group pursuing this certification. If you're staring at dashboards all day trying to separate signal from noise, GCED teaches you what matters and what's just log spam. I mean, we've all been there drowning in alerts that mean absolutely nothing. Incident responders also find value here since the exam covers detection and initial response fundamentals that you use literally every day.
System administrators transitioning to security roles benefit hugely from GCED.
Look, I've seen plenty of sysadmins who know their infrastructure inside and out but struggle with the security mindset. This cert bridges that gap effectively. It gives them the defensive thinking patterns they're missing even when their technical skills are solid. Network defenders and IT professionals responsible for enterprise security also fit the target audience perfectly.
The certification demonstrates hands-on incident response skills and practical knowledge that hiring managers actually look for when building security teams. Opens opportunities in SOC analyst roles, security operations positions, incident response teams, and enterprise security architecture jobs where you're making real defensive decisions.
Where GCED sits in the certification space
Within the GIAC family, GCED occupies an interesting middle ground between the foundational GSEC certification and more specialized options like GCIH. If GSEC is your security fundamentals and GCIH is your deep incident handling expertise, GCED is your practical enterprise defense validation that proves you can actually secure and monitor production environments without everything catching fire.
Unlike purely offensive security certifications such as GPEN, GCED puts weight on defensive posture, detection capabilities, and protective controls. Not gonna lie, breaking things is fun, but someone needs to actually keep the lights on and detect attacks before they become breaches. That's where GCED professionals live.
The certification gets recognized globally as validation of enterprise security defense certification competency and defensive security operations expertise. it's a US thing, which matters if you're working for multinational organizations or considering relocating. Though honestly, I've noticed more European companies starting to care about GIAC certs in general over the past few years, which is a shift from when they mostly cared about local certifications.
How the exam actually works and what it costs
The GCED exam cost typically runs several hundred dollars, though exact pricing varies and you should check GIAC's official site for current rates. They change things periodically, so don't quote me on specific numbers. The exam is proctored, timed, and open-book, which confuses some people until they realize that having books doesn't mean the exam is easy.
You get tested on practical knowledge application across enterprise defense domains including network security architecture, host security, security operations, threat intelligence, detection technologies, and incident response fundamentals. The thing is, the exam format tests your ability interpreting security tool outputs and making defensive decisions under time pressure. Completely different from leisurely reading through reference materials.
GCED passing score requirements are set by GIAC and represent competency across all tested domains. The exam puts weight on your ability applying security concepts in practical scenarios rather than just recognizing terminology.
Training alignment and study requirements
GCED aligns closely with SANS SEC501: Advanced Security Essentials - Enterprise Defender course content and hands-on labs. The SANS GCED training provides structured learning that maps directly to exam objectives, though it's not technically required to sit for the exam.
Typical preparation ranges from 60-120 hours depending on existing experience and familiarity with enterprise security concepts. Some people breeze through, others need more time, no judgment either way. If you're already working in a SOC or doing system hardening daily, you'll need less study time than someone transitioning from a different IT role.
While no formal prerequisites exist for taking the exam, recommended background knowledge and experience levels really impact success rates. Having hands-on experience with Windows and Linux systems, understanding basic networking concepts, and exposure to security monitoring tools makes preparation substantially easier.
Success typically requires access to practice environments where you can actually configure defensive controls and see how attacks manifest in logs, because reading about detection without seeing it happen is like learning to swim by reading books. GCED study materials should include official GIAC resources, the SEC501 course books if you took the training, and practice tests that help you build an effective index for the open-book exam format.
Keeping your certification current
GCED follows a four-year certification cycle with continuing professional education requirements to maintain current knowledge.
You'll need to earn CPEs through various activities like attending conferences, taking additional training, or participating in security community events. Honestly, the CPE requirements aren't terrible compared to some other certs that demand ridiculous amounts.
GCED renewal requirements make sure certified professionals stay current with changing threats and defensive techniques. The renewal fees are separate from initial certification costs, so factor that into your long-term planning.
Is GCED worth pursuing for your career?
The certification's value depends heavily on your career goals and current role. For SOC analysts and incident responders, GCED is absolutely worth it since it directly validates the skills you use daily and helps you stand out when competing for positions or promotions. I've seen it make the difference in hiring decisions personally.
Investment considerations beyond just exam cost include study materials, potential SANS training expenses, and the time commitment required for adequate preparation. Building practice labs and dedicating 2-3 months to serious study represents a real investment that should align with your career trajectory.
If you're choosing between certifications, compare GCED carefully against alternatives like GCIA for intrusion analysis or GCIH for deeper incident handling. GCED exam difficulty is considered intermediate within the GIAC portfolio, requiring both breadth across multiple domains and sufficient depth to handle scenario-based questions effectively.
GCED Exam Format, Structure, and Delivery Options
What the GCED certification is
GIAC GCED certification is the GIAC Certified Enterprise Defender credential. It targets people who defend actual production environments, not folks who just like reading about security. Think enterprise security defense certification with a heavy tilt toward practical defensive controls, detection, and response.
It's not a pure incident response badge, but it expects hands-on incident response skills and the ability to reason through what you'd do next when telemetry, logs, and hardening choices collide in the real world.
Who should take the GCED?
Security analysts. Sysadmins who got dragged into security. Blue team engineers who touch Windows and Linux hardening fundamentals and want a credential that maps to daily work.
If you're comparing it to other GIAC options, the GIAC Enterprise Defender exam sits in that "defender who configures stuff" lane. Not purely managerial. Not purely red team.
How the exam is structured
The GCED exam format is linear, not adaptive. Everyone gets the same count and the same clock. That means no weird "the test is changing because I missed one" anxiety, but it also means pacing matters because you can't rely on the exam getting easier or harder based on performance.
115 questions. 3 hours. No scheduled breaks. That's the headline, and honestly it's the part that surprises people who assume "open-book" means "relaxed."
Timing, pacing, and the reality of 3 hours
Three hours for 115 multiple-choice questions is tight if you're flipping pages like you've never seen your books before. Do the math and you're around 1.5 minutes per question. Some are quick recall while others are scenario-based questions that make you stop, re-read, and decide which defensive move is least bad given the constraints.
A practical rhythm: answer what you know immediately, mark what's fuzzy, keep moving. Short bursts. No hero mode. If you stall for five minutes hunting a single line in a book, you're donating time you'll desperately want later.
By the way, I've watched people spend half their exam time perfecting an index system during the test itself. That's like organizing your toolbox while the house is on fire. Build your system before you sit down.
Question types you'll see
All multiple choice, but varying complexity. Some are foundational recall, like "what does this control do" or "what's the best place to detect this," and then you get the longer scenario prompts where you're reading a mini incident report and choosing the most defensible action based on evidence.
GCED exam difficulty often comes from the mix. You'll be cruising on straightforward items, then you hit a scenario that wants analysis and synthesis, and suddenly your index quality matters more than your raw memory.
Open-book rules and what you can bring
GCED is open-book. That's real. You can bring printed books, printed course materials, and handwritten or printed notes and indexes. Physical paper only. No electronic reference materials, no smartphone "just for my notes," no tablet, no PDF on a laptop. If it's digital, assume it's banned.
That open-book policy changes how you study. You're not memorizing everything. You're building retrieval speed. Organization is the whole game.
Why your index makes or breaks you
A well-organized index is your time machine. You can know the material and still lose because you can't find the one table, the one command, the one "which log source is best" detail quickly enough under the clock.
Build an index that points to exact page numbers, tabs, and sections you actually used while studying, not an aspirational "I indexed the whole book" monster you never tested. Then pressure-test it with GCED practice tests, because your index should get faster every time you use it.
Delivery options: remote or testing center
Proctored delivery is available either via remote proctoring (online) or at Pearson VUE testing centers worldwide. Pick based on your life and your tolerance for tech risk.
Testing centers are boring in the best way. Controlled environment. No neighbor mowing the lawn. No surprise Wi-Fi drop. If you're the kind of person who gets rattled by small disruptions, the testing center advantage is that you can focus on the exam, not your router.
Remote proctoring is convenient, but you're trading commute time for setup discipline and the possibility that your computer decides to update at the worst moment.
Remote proctoring requirements and system checks
For remote testing you need stable internet, a webcam, a microphone, a quiet room, and a system that passes the proctoring software compatibility checks. Do the system check early, not the night before, because troubleshooting drivers and permissions when you're already stressed is a terrible vibe.
Also expect a check-in process that includes ID verification and an environment scan. Clear your desk. Remove extra monitors if required. Have your allowed reference materials ready to show.
What exam day logistics feel like
Identification requirements are strict. Government-issued photo ID is required whether you're at Pearson VUE or remote. At a testing center, arrive early because check-in takes time and you don't want to start flustered.
Break policy is simple: no scheduled breaks during the 3-hour exam. You can take a bathroom break, but the exam clock keeps running, so plan your caffeine like an adult.
Scratch paper is limited. In-person you typically get scratch paper. Remote usually means a digital whiteboard. Either way, use it for quick notes, not essays.
Review, results, and what happens after you click submit
You can mark questions for review and return to them before final submission. Use that feature aggressively. It's one of the few advantages you have in a timed, linear exam.
Preliminary results are typically immediate, meaning you see pass/fail when you finish. The official score report usually follows within 1-2 business days and includes performance by domain.
Cost, scoring, retakes, and accommodations (quick hits)
People always ask about GCED exam cost and GCED passing score. Those details can change, so verify in the GIAC portal when you register, along with the GCED exam objectives and any updates to exam policies.
Scheduling flexibility is decent: you can usually schedule within the registration validity window, commonly about 4 months from purchase. Retakes cost extra, and failed attempts come with a waiting period per GIAC's terms, so don't treat your first attempt like a "practice run."
If you need accommodations, request them through GIAC before exam registration. Don't assume it's automatic.
Language and objectives notes
The exam is primarily offered in English, so if that's not your first language, confirm options up front. Keep your prep anchored to the published GCED exam objectives: enterprise defense and security operations, detection and monitoring, response fundamentals, system and network hardening, defensive tooling, and common threats with mitigation techniques, the stuff you'd expect if you've done SANS GCED training or equivalent.
One last opinion. If you treat open-book like open-internet, you'll have a bad day. If you treat it like "I built a paper search engine and practiced using it under time pressure," you're playing the exam the way it's designed.
GCED Exam Objectives and Knowledge Domains
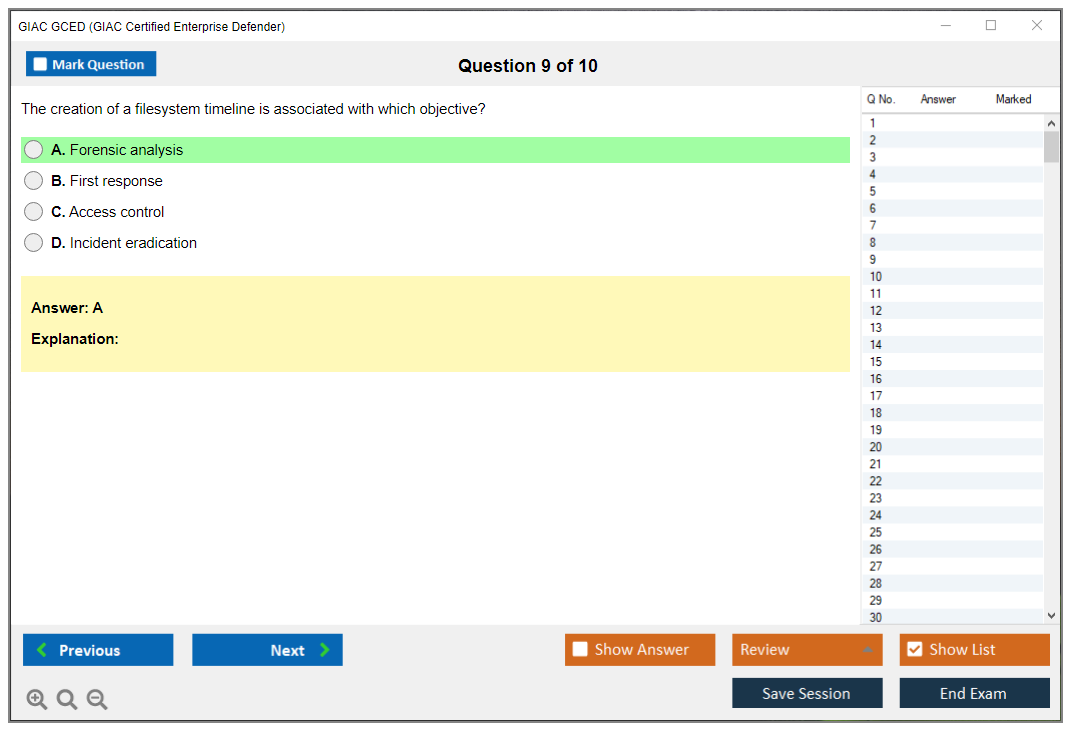
What the GCED exam actually tests you on
The GCED certification exam isn't just another multiple-choice test you can cram for the night before. You could try that. But you'd regret it. This exam covers six major knowledge domains, and honestly, they're all weighted differently, so knowing where to focus your study time matters way more than people realize. I mean, you can't just memorize definitions and expect to pass this thing.
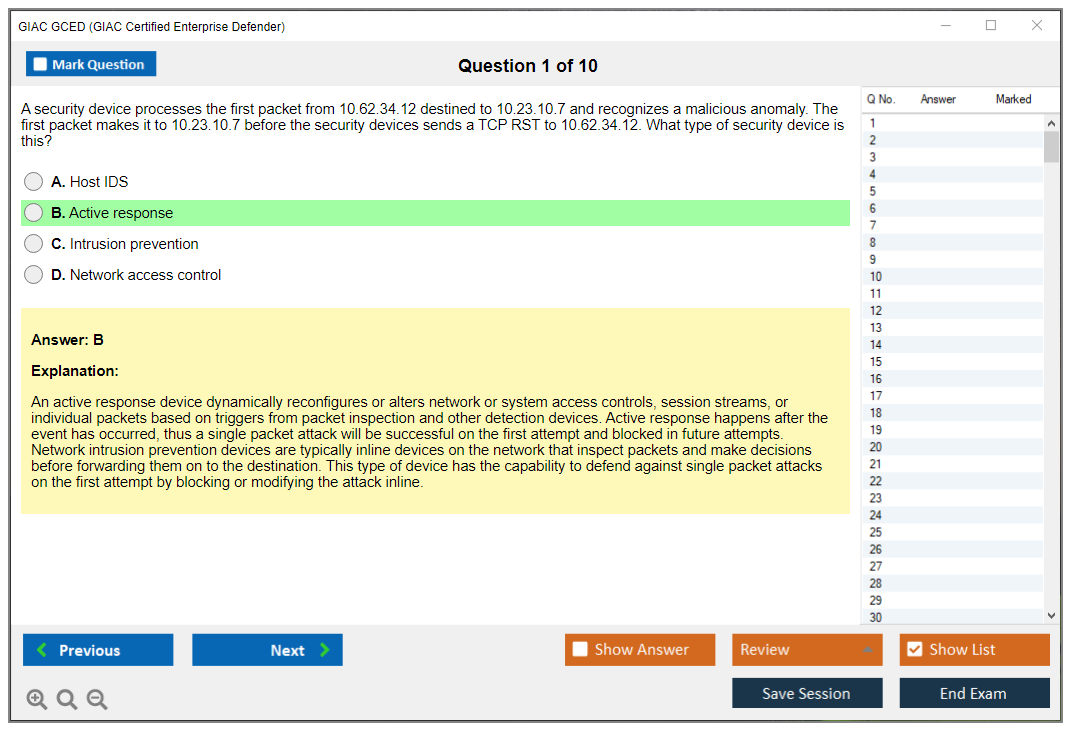
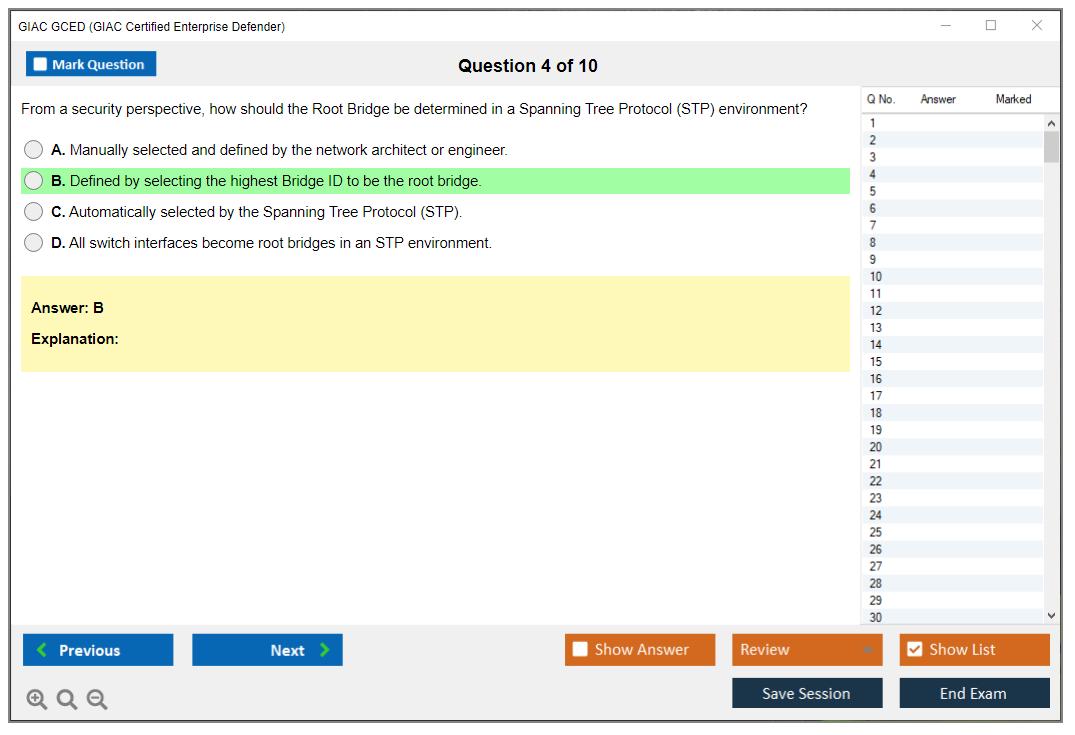
Domain 1 eats up about 20% of the exam and focuses entirely on defensive network infrastructure. We're talking network security architecture, perimeter defense strategies, and how to actually implement segmentation that doesn't just look good on paper but works in production environments. You'll need to understand firewall technologies beyond just "block bad stuff, allow good stuff." Next-gen firewalls, stateful inspection, ACL optimization, the whole deal. Network segmentation is huge here too. VLANs, micro-segmentation, zero-trust principles that everyone talks about but fewer people actually implement correctly. IDS and IPS deployment comes up repeatedly, and you better know the difference between signature-based and anomaly-based detection because the exam will definitely ask about tuning methodologies and when to use which approach.
VPN technologies show up here too, which makes sense because remote access security isn't going anywhere. Encryption protocols, site-to-site connectivity, security considerations that people often overlook when they're rushing to get VPNs deployed. Network monitoring and visibility rounds out this domain. Traffic analysis, flow data, packet captures, establishing behavioral baselines that actually mean something.
Wireless security gets its moment too. WPA2 versus WPA3, authentication mechanisms, detecting rogue access points before they become major problems.
System hardening across Windows and Linux environments
Domain 2 is the heaviest hitter at roughly 25% of the exam, and it's all about Windows and Linux hardening fundamentals. Look, if you're weak on either operating system, this domain will expose that weakness fast. Windows security architecture goes deep. UAC, security policies, Active Directory security configurations, Group Policy Objects that actually enforce security rather than just annoy users. Windows authentication mechanisms come up constantly. NTLM, Kerberos, how these protocols actually work under the hood, credential protection strategies, and mitigating pass-the-hash attacks that still plague organizations.
Windows logging and auditing is critical. Event log configuration, security event monitoring, implementing Sysmon properly, following logging best practices that balance storage concerns with security visibility needs.
Then you flip to Linux and the exam expects equal competency. File permissions that go beyond basic chmod commands. SELinux and AppArmor configurations. User and group management, sudo configuration that doesn't accidentally give someone root access when they shouldn't have it. Linux hardening techniques include service minimization, kernel hardening, iptables or nftables configurations, SSH hardening beyond just changing the default port. Honestly, the thing is, most people think SSH hardening means switching port 22 to something else and calling it a day. That's a start but nowhere near enough. I once watched a system admin spend two hours patting themselves on the back for that single change while leaving password authentication enabled.
Patch management strategies apply to both operating systems and honestly, this is where real-world experience shows through. Vulnerability assessment, testing patches before deployment, scheduling that doesn't break production, having rollback plans when patches cause problems. Because they will. Configuration management using CIS benchmarks comes up too, along with detecting configuration drift and maintaining compliance.
Security operations, monitoring, and detection capabilities
Domain 3 represents about 20% of the exam and covers security operations and monitoring. SIEM platforms are central here. Architecture, log aggregation, correlation rules, alert generation that doesn't create so much noise that analysts ignore everything. Log management and analysis goes beyond just collecting logs. You need centralized logging, retention policies that meet compliance requirements, log normalization so you can actually correlate events across different systems, identifying which log sources actually matter for security.
Security monitoring use cases require developing detection logic that works. Not gonna lie, this is where I've seen experienced security folks struggle because writing effective detection rules is harder than it looks. Tuning rules, reducing false positives without missing real threats, prioritizing alerts so the high-severity stuff gets attention first.
Threat hunting fundamentals appear here. Proactive detection, hypothesis-driven hunting, identifying indicators of compromise before they become full-blown incidents. Security metrics and reporting matter because executives need to understand what's happening without drowning in technical details.
Incident response processes and containment strategies
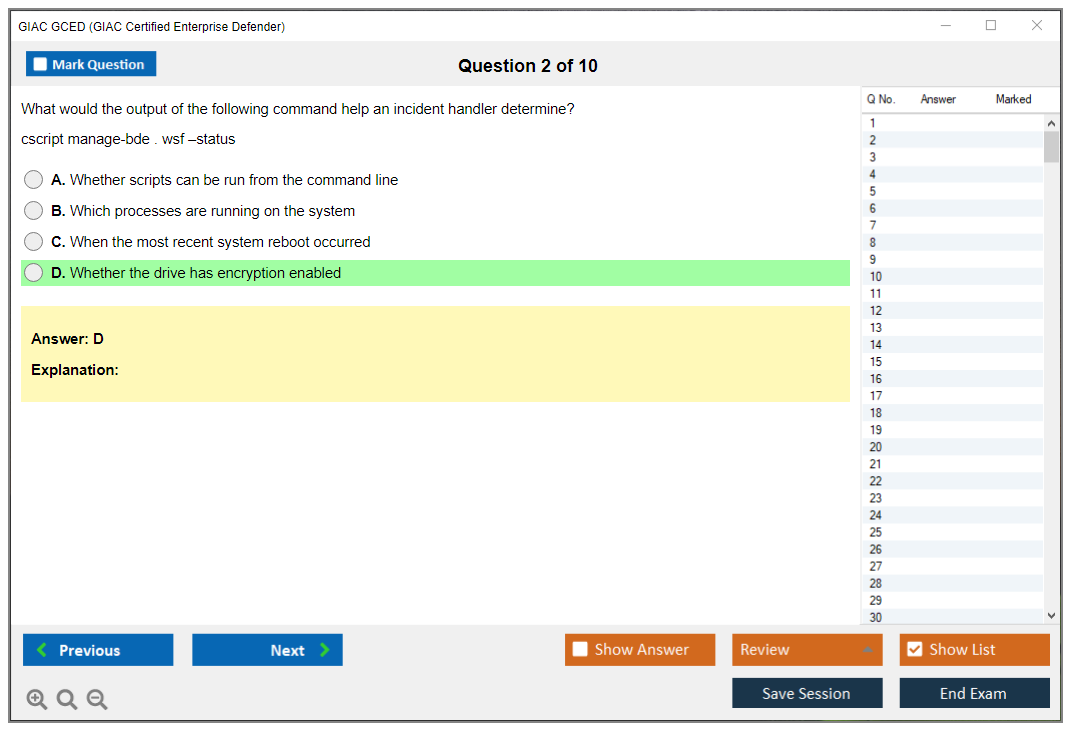
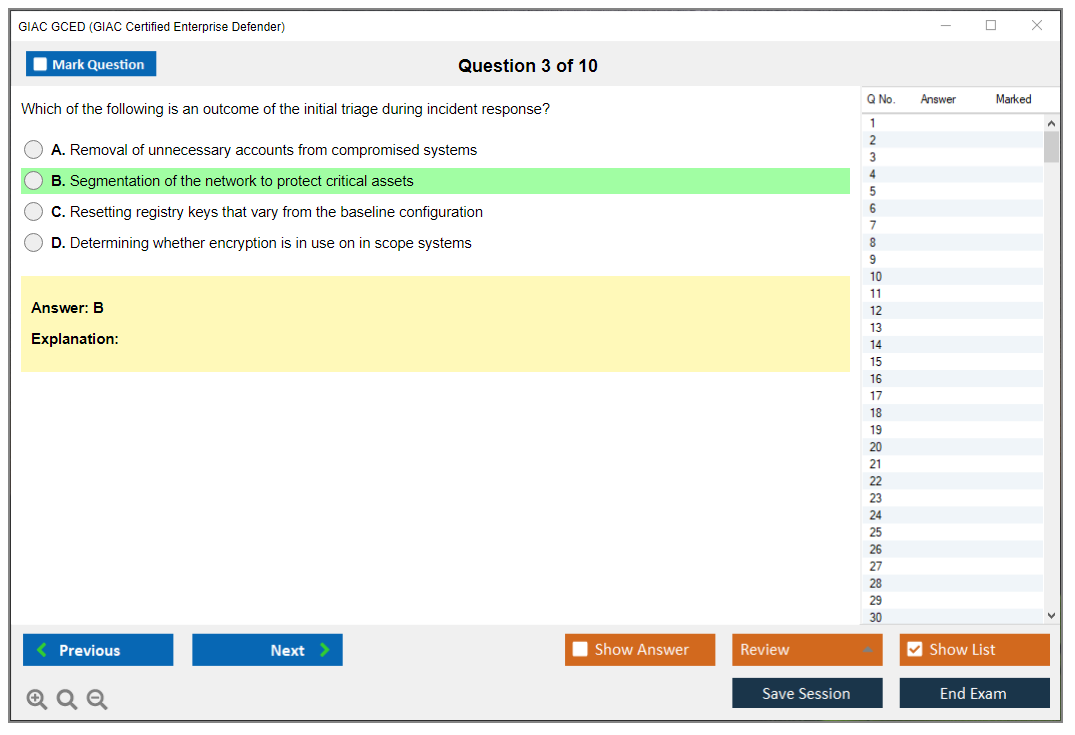
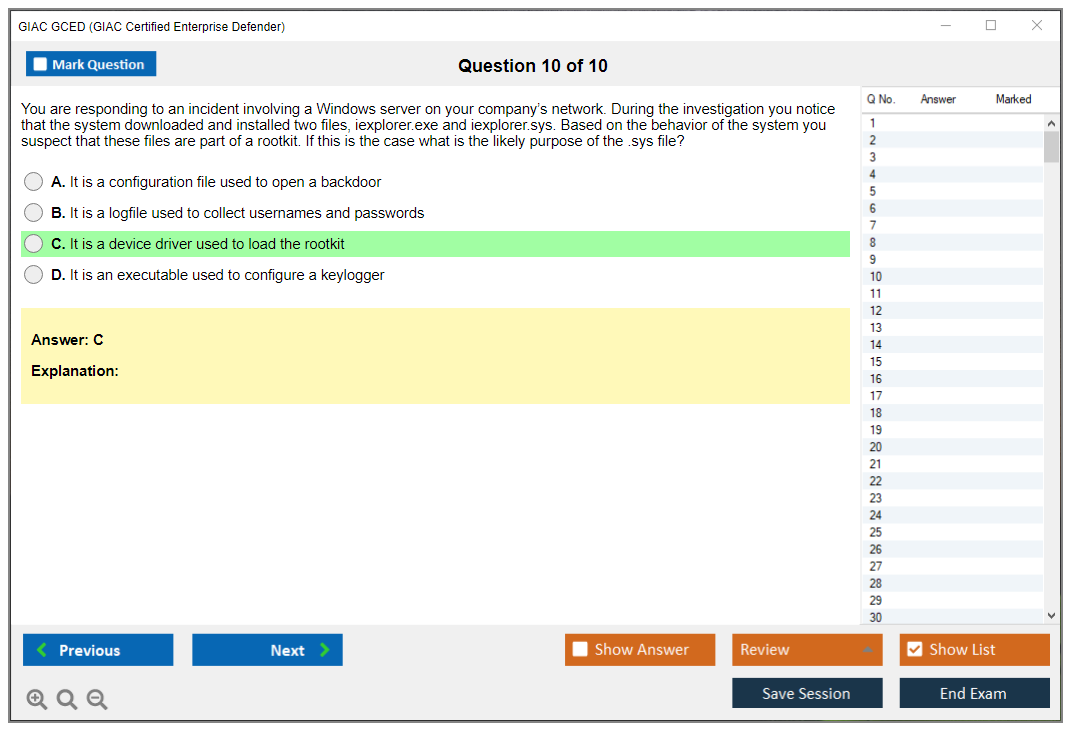
Domain 4 takes up approximately 15% and focuses on incident response and handling. The incident response lifecycle gets tested. Preparation, identification, containment, eradication, recovery, lessons learned that actually improve your program instead of just sitting in some SharePoint folder nobody reads. Evidence preservation is critical, especially chain of custody, forensic imaging, memory acquisition for investigations that might end up in court.
Containment strategies require balancing security with business continuity. Isolation techniques, network segmentation during active incidents, quarantining systems without taking down everything. Malware analysis fundamentals cover both static and dynamic analysis, sandboxing technologies, identifying malware behavior patterns. Digital forensics basics round this out. File system forensics, timeline analysis, artifact collection using proper tools.
Threat intelligence and adversary behavior modeling
Domain 5 is smaller at roughly 10% but covers threat intelligence and attack frameworks. Understanding different threat intelligence sources matters. OSINT, commercial feeds, information sharing communities, actually integrating intelligence into defensive operations rather than just having feeds you never look at. The MITRE ATT&CK framework shows up extensively here, and you need to understand TTPs mapping, adversary behavior modeling, developing ATT&CK-based detection that makes sense for your environment.
The cyber kill chain provides another framework. Understanding attacks from reconnaissance through actions on objectives. Indicator management includes IOCs, lifecycle management, threat actor attribution when possible.
Data protection, encryption, and privacy controls
Domain 6 rounds out the exam at approximately 10%, covering data protection and encryption. Encryption fundamentals go beyond "encryption is good." Symmetric versus asymmetric encryption, hashing algorithms, digital signatures, selecting appropriate protocols for what you're actually trying to protect. DLP technologies, data classification schemes, identifying sensitive data, preventing exfiltration before it happens. Backup and recovery strategies including encryption, disaster recovery planning, understanding RTOs and RPOs.
If you're comparing this to GSEC or GCIH, GCED sits somewhere between them in terms of enterprise defense focus versus pure incident handling capabilities.
GCED Exam Cost and Registration Details
The GIAC GCED certification is a defensive credential for people protecting actual enterprise environments. You're expected to recognize attacks, interpret logs, harden systems, and make good calls under time pressure. It's all about demonstrating you've worked with security tooling in production, not just read about it.
This isn't theory-only. It rewards people who've touched security tooling in real work, and it maps well to the "enterprise security defense certification" label because you're tested across controls, monitoring, and response, not one narrow slice.
Who should take the GCED
If you're in a SOC, blue team, IR, or "accidental security" role inside IT, GCED makes sense. If you're a sysadmin who got pulled into detection rules and endpoint hardening, also yes. But if you've never opened a SIEM and your only Linux experience is copying commands from a blog, you'll feel the GCED exam difficulty fast.
Some folks use the GIAC GCED certification as a credibility bump for internal promotions. Others use it to pivot from general IT into security operations with actual "hands-on incident response skills" on the resume that hiring managers care about.
How the exam is delivered
GIAC exams are proctored and delivered online through an approved testing method, so you're not stuck traveling unless you want to. The exam is open-book. Sounds easy, right? Until you realize open-book exams punish messy notes and reward indexing like your job depends on it.
Time pressure is real. You can't "control-F" your way through this unless your materials are organized, and even that won't save you if you don't understand the concepts. Your GCED study materials plan needs an index you trust.
Quick aside: I once watched someone bring a three-ring binder stuffed with 400 pages of untagged printouts to an open-book exam. They passed the time flipping pages while their score tanked. Don't be that person.
What you're tested on
The GCED exam objectives are broad in a very enterprise way.
Topics include enterprise defense and security operations, including how controls fit into day-to-day monitoring. Detection, monitoring, and response fundamentals, with the kind of log and alert thinking you do in a SOC at 2 a.m. System and network hardening concepts, including Windows and Linux hardening fundamentals. Security tooling and defensive controls, like what helps versus what just looks good in a slide deck. Threats, attacks, and mitigation techniques, where the point is picking the best next step, not reciting definitions.
One part that trips people up? The tooling angle. You need to understand what the tool output implies, not just what the tool is "for". That's why lab time matters more than another reread of notes.
What the exam costs
Baseline GCED exam cost is straightforward. Standard GIAC exam pricing is $949 USD (as of 2026), subject to change and regional variations. That's the number most candidates should anchor on for a standalone purchase.
If you buy the exam with the SANS SEC501 course, you're in a different pricing universe. The SANS course bundle that includes the GCED exam typically runs $8,900 to $9,500 depending on delivery format and location. It hurts, but companies pay it all the time.
There's also SANS OnDemand. Pricing for OnDemand training with the GCED exam typically ranges $2,500 to $3,000 for self-paced access plus certification, but confirm what's included in your quote because SANS packaging changes and some orgs negotiate better rates.
What you get for the money
With an exam purchase, you typically get one exam attempt, one official practice test, and a four-month scheduling window from the purchase date.
That included practice test matters. The official GCED practice tests set includes 75 questions that feel like the real exam in format and difficulty. It gives you the best early signal on whether your index is usable or just a pile of PDFs.
Retakes are cheaper. If you fail, retake exam cost typically falls around $429 to $499, which is less than the initial purchase price. Some bundles include a second attempt at reduced cost as insurance.
Need more time? You can often extend the four-month window for an extra fee, though GIAC exams are generally non-refundable once purchased. Don't buy the voucher and then "figure it out later". I've watched people lose money that way.
Passing score and scoring expectations
The GCED passing score? GIAC sets passing thresholds per exam version, and they can change, so the safest move is to check your GIAC portal for the current requirement before you schedule.
Scoring works like you'd expect: you answer a fixed set of questions under time, you get a scaled result, and you find out quickly whether you cleared the bar. What surprises candidates is how many questions are "best answer" based on defensive judgment, not trivia. Multiple answers could work, but which one's better in a real incident?
How hard GCED is
The GCED exam difficulty is "intermediate-to-advanced blue team", especially if your background is mostly compliance or policy. If you've done real ops work, it's very doable.
Common fail reasons? Weak index. Overconfidence about open-book (it's not a safety net if you can't find stuff). And not enough practice interpreting defensive data, because the exam doesn't care that you memorized a port list if you can't reason through what an alert means and what action reduces risk fastest.
Prereqs and recommended experience
Official GCED prerequisites are basically "none" in the formal sense. GIAC doesn't gatekeep with mandatory cert chains, which is nice.
Recommended background? Another story. A couple years in Windows and Linux administration helps a lot, along with basic networking and familiarity with enterprise monitoring. If you've done patching, endpoint controls, and log review in production, you're in the sweet spot.
Study materials that help
Officially, SANS GCED training is the SEC501 track, and it's the most direct route if your employer is paying (and they should be). If you're going exam-only, you need to bring your own structure: books, labs, notes, and repetition.
For extra question exposure, I like targeted practice packs as a supplement, not a replacement. The GCED Practice Exam Questions Pack is cheap enough at $36.99 to be a low-risk add-on for drilling weak spots, and it can help you pressure-test what you think you know. Same idea if you want a quick checkpoint later: GCED Practice Exam Questions Pack can be a lightweight way to keep momentum between deeper study sessions.
Indexing tip? Make an index while you study, not after. Use keywords you'd search under stress, add page numbers (not vibes), and test it ruthlessly.
Practice tests and prep strategy
Use the official practice test early. Then again later. First run diagnoses your index and timing, second run confirms you fixed the gaps.
Study plan options: 2-week only if you're already doing enterprise defense work daily and your notes are organized. 4-week is realistic for most working pros with evenings and weekends. 8-week is best if you're building fundamentals plus indexing from scratch.
If you want a third set of questions to keep you honest, sprinkle in something like the GCED Practice Exam Questions Pack between official practice attempts, and focus on why you missed questions, not just the score (ego won't help you pass).
Registration, payment, and org logistics
Standalone exam purchase is available through the GIAC website at the standard exam price. Organizations can also buy vouchers in bulk, sometimes with volume discounts, which is common for security teams that certify a whole cohort.
Payment methods usually include credit cards, purchase orders, wire transfers, and organizational billing options through GIAC. Prices are listed in USD. International candidates pay the equivalent amount and may eat currency conversion fees (check your bank). Taxes can apply too, like sales tax or VAT, depending on location.
Big money saver options exist. SANS Work Study can trade event assistance for free training and certification. There's also special pricing for government employees, military, and contractors via SANS government programs. Students or academic institutions may qualify for educational discounts. Scholarships and diversity programs pop up as well, but they're limited, so apply early.
Renewal and maintenance costs
Plan ahead. For GCED renewal requirements, GIAC certs renew on a cycle, typically every four years, and you'll need CPEs plus a renewal fee, often around $429. Budget it now. Track your CPEs as you earn them, because reconstructing proof later is a pain (trust me).
Cost vs value
ROI is personal. If your employer reimburses, grab that policy and follow it to the letter. If you're paying out of pocket, compare exam-only ($949) versus training bundles, add likely hidden costs like extra labs, retakes, time off work, and the opportunity cost of study hours.
The GIAC GCED certification can pay back through better roles, higher comp, and more credibility in enterprise defense interviews, but only if you pair it with real skills and can talk through what you did, what you saw, and what you'd do differently next time (because interviewers will ask, and they'll know if you're faking).
GCED Passing Score and Scoring Methodology
Understanding the 73% benchmark
So, 73%. That's your magic number.
The GCED passing score sits at 73%, which translates to roughly 84 correct answers out of the 115 total questions on the exam. That's the bare minimum to walk away with your certification. GIAC set this threshold as what they consider minimum competency for someone defending enterprise networks. The thing is, it makes sense when you think about the responsibility that comes with this role.
Look, here's what you need to know about that 73% number: it's not arbitrary. GIAC certifications like GCED maintain consistent standards across their intermediate-level certs. You'll see similar passing thresholds for GCIH and GCIA, which tells you they've calibrated this to represent real-world capability, not just memorization. You need to demonstrate you can actually apply enterprise defense concepts under pressure.
How GIAC converts your raw score
Scaled scoring methodology sounds complicated. It's not really, though.
GIAC uses this approach to protect you from getting an unfair exam version. Raw scores get converted to a standardized scale that accounts for question difficulty variations between different exam forms, so some test-takers get slightly harder questions, others get slightly easier ones, and the scaling evens everything out. Everyone faces the same passing standard regardless of which version lands on their screen. Not gonna lie, this is actually helpful because it means your 73% represents the same competency level as someone who tested six months ago or someone testing next week.
The scaled approach ensures consistency across all GCED candidates regardless of when or where they sit for the exam.
Every question counts the same
All 115 questions carry equal weight. Period.
Doesn't matter if it's a straightforward question about Windows hardening fundamentals or a complex scenario about incident response. Each one is worth the same points, and there's no partial credit either since the multiple-choice format is binary. You're either right or wrong.
This equal weighting changes how you approach studying. I mean, you can't just master the "big topics" and ignore others because a question about Linux security is worth exactly as much as one covering detection methodologies. That domain breakdown on your score report becomes super important for identifying where you're actually weak versus where you just got unlucky with a couple questions.
What happens the moment you submit
You get preliminary pass/fail status displayed on screen immediately. That instant feedback is both a blessing and a curse depending on how you did, but at least you're not sitting around wondering for days while anxiety eats you alive. The detailed official score report with your percentage and domain-level breakdown arrives via email within 1-2 business days.
Honestly? That domain performance feedback is really useful. You'll see your percentage correct in each major knowledge area, which either validates your study approach or shows you exactly where things went sideways. If you're retaking after a fail, this breakdown becomes your roadmap.
The finality of your score
Once you submit that exam, your score is final. Done.
GIAC doesn't have an appeals process for challenging questions or disputing scoring decisions. I've seen people frustrated by this, especially when they feel a question was ambiguous, but that's the reality and your preparation needs to account for potential ambiguity because you won't get a second chance to argue about wording after the fact.
For candidates who land in that 70-72% range, it's frustrating as hell. You're so close to passing but still failed. The good news? Most people in this near-miss category pass on their retake with focused study on their weak domains. The GCED Practice Exam Questions Pack at $36.99 can help identify those exact weak spots before you burn another attempt.
Strategic scoring considerations
Here's what nobody tells you: aim for 80%+ on your practice tests. That margin of safety accounts for exam-day stress, harder-than-expected questions, and just plain bad luck. If you're barely scraping 73% on practice exams, you're probably not ready for the real thing and you're gambling with your attempt.
There's no negative scoring on GCED. Answer every single question.
Wrong answers don't subtract points, which means even if you're completely guessing, you should fill in something. Leaving questions blank because you ran out of time is how people fail when they actually knew enough to pass. Time pressure directly impacts your score, and pacing throughout the exam is absolutely critical. I once watched a colleague walk out knowing he'd failed because he left eight questions untouched at the end. Eight questions where he could have at least guessed. That still bothers me.
Performance data and benchmarks
GIAC doesn't publicly release official pass rates, but industry estimates put the first-attempt GCED pass rate somewhere around 60-70%. That's actually pretty reasonable compared to some vendor certs. Candidates who fail and retake typically see 10-15% score improvement with focused study. That tracks with what I've observed. You learn what the exam actually tests versus what you thought it would test.
Your score remains confidential between you and GIAC unless you choose to share it, and some employers ask to see transcripts. While 73% passes, a higher score does demonstrate stronger mastery if you're competing for positions. But a pass is a pass. Everyone who holds GCED met that same 73% standard regardless of their final percentage.
The scoring methodology connects to other GIAC certs too. If you're also eyeing GSEC or GSLC, you'll find similar passing thresholds and scaled scoring approaches. It's consistent across their certification portfolio, which makes planning a multi-cert path a bit more predictable.
GCED Exam Difficulty and Common Challenges
The GIAC GCED certification is one of those "defender brain" exams. Real talk. It's built around enterprise security defense certification work, meaning you've gotta think like someone who hardens systems, monitors activity, and responds when stuff breaks at 2 a.m. Not theory-only. Not vendor-specific trivia. Practical defensive decision-making. The thing is, that's harder than it sounds when you're staring at 115 questions.
Look, the GIAC Enterprise Defender exam is usually considered intermediate inside the GIAC lineup. More challenging than GSEC 'cause it expects you to apply controls in messy environments, but less specialized than GCIH since you're not living in exploit chains and deep incident handling all day. That middle spot sounds comfy. It isn't always. Sometimes that "jack of all trades" approach bites back harder than pure specialization would.
Security analysts. Blue team folks. Sysadmins who got pulled into security, and SOC engineers who touch real configs. People who already have Windows and Linux hardening fundamentals and have at least seen a SIEM rule, a firewall policy, and a "why is DNS doing that" moment in the wild.
If your background's purely academic, you can still pass, but you'll feel the friction. Hard.
How the test is delivered
GCED's proctored and multiple choice. You get 3 hours for 115 questions. That's about 1.5 minutes per question, which sounds fine until you hit scenario-based items that read like a mini ticket, a log snippet, and a policy argument all stapled together. Some questions feel like they're testing reading speed as much as security knowledge, which honestly bugs me sometimes. Time pressure's real.
Open-book, yes. But open-book's not open-infinite-time. That part trips people.
The GCED exam objectives cover a wide spread of enterprise defense topics. Breadth's the game here.
You'll see enterprise defense and security operations, detection work, response fundamentals, system and network hardening concepts, and defensive controls. Threats and mitigations too, obviously. Some questions are "what control fits," others are "what would you check next," and some are "which change reduces risk without breaking the business," which is honestly the most real-world part of the exam. Though it's also where opinions and experience matter more than pure memorization.
Cost and what you get
The GCED exam cost changes depending on whether you bundle it with SANS GCED training, any discounts, and whether you're buying through work. GIAC exams aren't cheap. Not gonna lie, that price tag alone makes the stress feel higher, 'cause nobody wants to explain a failed attempt to their manager after spending that much. Mixed feelings there. Value's high if you pass first try, but the financial pressure adds another layer of anxiety you don't need during prep.
What's included depends on the purchase path, but typically you're dealing with an exam attempt. Many candidates also buy official GCED practice tests as part of their prep stack. Retakes are their own expense, so plan like you only wanna sit once.
Passing score and scoring
The GCED passing score is published by GIAC, and you should verify the current number on the official page before you schedule. GIAC scoring's straightforward on exam day: you answer, you submit, you get a score report. No partial credit magic. No "but I was close."
Questions vary in difficulty. It can feel like you're getting wrecked and still end up fine, 'cause plausible distractors make you doubt yourself even when you're right.
How hard it is, really
On the GCED exam difficulty scale, I put it at intermediate, with spikes. The spikes come from integration and realism, not from obscure facts. The exam's broad, so you're constantly switching mental gears. Hardening one minute, detection logic the next, then response workflow, then controls and policy implications. That breadth vs. depth thing is the signature challenge, 'cause you don't get to camp out in one comfort zone like you might with more specialized certs.
Scenario-based question complexity is where most people feel it. A lot of items aren't "define X." They're "here's what's happening, here are constraints, pick the best next step," and you've gotta analyze, synthesize, and apply while the clock's ticking and the wrong answers look pretty reasonable.
Distractors are good. Like, annoyingly good. You'll see answer options that are technically true statements, but not the best fit for that scenario, that environment, or that point in the workflow. The thing is, this mimics real decision-making better than simple recall questions, but also makes you second-guess yourself constantly. You can't just pattern-match terms from the book and click.
Multi-domain integration shows up more than people expect. You might need to connect endpoint hardening with logging strategy, or interpret an operational constraint while choosing a defensive control. That's the "enterprise" part. It's not one box. Actually, it reminds me of the time I watched a junior analyst nail a threat hunt but completely miss the compliance implication of their remediation choice. Both matter.
Common failure reasons (and how to avoid them)
Insufficient hands-on experience's the big one. If you only read GCED study materials and never build labs, your brain won't have the "muscle memory" for troubleshooting logic, tool behavior, or what a sane configuration looks like under pressure. Fix: do labs. Even small ones. Set up a Windows baseline, a Linux baseline, turn on logging, break it, and then fix it. Yeah, break things intentionally, 'cause that's when learning actually sticks.
Poor time management's the other classic. People get stuck early, burn 6 minutes on a single monster scenario, and then later they're speed-clicking through easier questions they actually could've nailed. Fix: mark-and-move. Keep a strict pace, and come back with whatever time you can claw back.
Inadequate index preparation hurts more than it should, 'cause open-book navigation's part of the exam. If your index is messy, you'll waste precious minutes flipping through binders like you're searching for lost car keys. Fix: build an index that maps concepts to page numbers. Add tabs that make sense to your brain. Practice using it under timed conditions. I mean, seriously, practice the physical act of finding stuff quickly, not just reading content.
Prerequisites and recommended experience
GCED prerequisites officially are light. There usually isn't a hard gate like "must have X cert." But recommended background's very real: enterprise security operations exposure, basic networking, Windows and Linux admin comfort, and some hands-on incident response skills. If you've ever tuned logging, handled an endpoint alert, or fought with hardening settings, you're already ahead.
Study materials and indexing
Official training's the obvious path. SANS GCED training is high quality, but expensive. Like, really expensive, which makes it a tough sell if you're self-funding. If you go that route, treat the course books like your primary reference system and build your index as you go, not at the end when you're panicking.
Supplementals help, but don't overbuy. A couple targeted books, some hardening guides, and your own lab notes can beat a giant pile of PDFs you never open. The index is the real weapon for open-book GIAC exams. I mean, the index's basically your time machine.
Official GCED practice tests matter 'cause they teach you pacing and reveal weak areas fast. Take one earlier than you feel ready, review misses, then lab the topics you guessed on. Don't just reread. Actually do the thing.
Quick timelines. Two weeks's only realistic if you already do this job daily. Four weeks works for many working pros if you're consistent. Eight weeks's safer if you're newer, 'cause you need time to build that practical intuition, not just memorize terms.
Renewal requirements
GCED renewal requirements follow the GIAC renewal cycle with continuing education. You'll track CPEs, submit 'em, and pay the renewal fee. What counts's usually training, conferences, relevant work activities, and other security education, but check GIAC's current rules so you don't waste effort logging the wrong stuff.
GCED vs GSEC and GCIH
Compared to GSEC, GCED expects more real defensive operations thinking and configuration awareness. Compared to GCIH, GCED's less about specialized incident handler depth and more about broad enterprise defense decisions. If you're defending environments and making controls work, GCED fits. If you're still building fundamentals, GSEC first's usually smarter.
GCED FAQ
Is it worth it? If your role's blue team in an enterprise, yes, 'cause the exam maps to daily work and hiring managers recognize GIAC.
How long should you study? Long enough to do labs and indexing, not just reading. For most people, 4 to 8 weeks.
Can you pass without SANS training? Yes, but the bar's higher. You'll need strong labs, solid references, and an index good enough that open-book doesn't turn into open-panic.
Conclusion
Wrapping up your GCED path
Okay, real talk. The GIAC GCED certification? It's not some checkbox thing. This proves you can actually defend enterprise networks when everything's falling apart, not just sound smart in conference rooms. The exam difficulty forces you to really get detection, hardening, and incident response at depths most certs completely ignore.
The GCED exam cost stings upfront. We're looking at roughly $2,499 just for the exam, no training included. But think about what you're walking away with here. You're building hands-on incident response skills employers are desperate for right now, not some theoretical garbage collecting dust in a PDF file somewhere. The GCED exam objectives span everything from Windows and Linux hardening fundamentals through defensive controls you'll deploy daily. Real value. My friend took a different cert last year, spent half the money, and now complains he can't get past phone screens because nobody recognizes it.
Here's the thing about the GCED passing score: 73%, for the record. Totally achievable. You just gotta put in actual work. Most failures? They leaned way too hard on that open-book format without building a decent index or understanding what's behind the material. Don't make that mistake. The SANS GCED training delivers solid foundation material, sure, but you've gotta add practice to it.
Like, tons of practice.
Speaking of which, GCED practice tests are flat-out required for your prep. You need to identify your weak spots before exam day. Not during. I've watched too many candidates stroll in all confident, then realize they can't work through their materials fast enough or completely misread key enterprise security defense certification concepts.
The GCED renewal requirements? 36 CPEs every four years. Which keeps you sharp, honestly. This isn't some "pass it and ignore it forever" cert, and in this field, that's actually what you want.
Before scheduling your exam, work through real GCED study materials and test yourself without mercy. If you want quality prep resources mirroring actual exam format and difficulty, check out the GCED Practice Exam Questions Pack. It'll expose knowledge gaps and build the speed you desperately need for exam day.
Not gonna lie, this cert demands effort. Serious effort. But if enterprise defense work matters to you? Worth every single hour.


Overall, the GCED Exam test is a grueling yet satisfying instrument for IT professionals, especially those interested in ethical hacking. With careful study and practice, Campaigners can increase their chances of passing the test and carrying the instrument.
The total time distributed for the test is 2 hours 30 twinkles, and Campaigners must score at least 70 percent in order to pass.