Overview of CertNexus ITS-110 CIoTSP Certification
What you're actually getting with the CIoTSP credential
The CertNexus ITS-110 CIoTSP certification is a vendor-neutral credential that validates your ability to secure IoT deployments from device to cloud. it's another checkbox cert. This thing focuses on practical IoT security implementation rather than abstract theory. You're proving you can identify IoT-specific threats, design secure architectures across the entire IoT stack, and implement risk mitigation strategies that actually work in production environments.
What makes CIoTSP different? The practitioner focus. While some certifications obsess over policy frameworks or generic cybersecurity concepts, CIoTSP gets into the weeds of IoT device constraints, edge computing security, and the weird authentication challenges you face when dealing with thousands of connected sensors that might run for years on a battery. The credential covers secure device provisioning, OTA firmware updates, encryption key management for resource-constrained devices, and monitoring strategies that make sense when you're dealing with massive IoT deployments.
The timing matters. By 2026 we're staring down 75+ billion connected devices according to most projections, and the security talent pool hasn't kept pace. Not even close. IoT breaches keep making headlines. Compromised smart cameras, botnet-infected home routers, industrial control systems getting ransomware. Regulatory pressure's mounting too with GDPR enforcement, the IoT Cybersecurity Improvement Act, and industry-specific compliance requirements. Companies need people who actually understand IoT security fundamentals, not just traditional IT security folks trying to wing it.
Who should actually pursue this certification
IoT security engineers? Architects? They're the obvious candidates. If you're designing connected systems, you need to understand threat modeling for IoT, secure architecture patterns, and how to balance security with device constraints. But that's not everything.
Cybersecurity professionals expanding into IoT make perfect candidates. You've got the security foundation, now you need the IoT-specific knowledge. How authentication works differently when devices can't handle complex protocols, why firmware integrity verification matters more in IoT than traditional systems, how to secure communication channels when devices connect through untrusted networks. The ITS-110 certification bridges that gap.
Network administrators managing IoT deployments need this too. You're dealing with device onboarding at scale, network segmentation strategies for IoT traffic, and monitoring systems that generate completely different telemetry than your traditional infrastructure. IT managers overseeing IoT infrastructure benefit because they need to understand the security implications of procurement decisions. Policy development for IoT governance. Risk assessment frameworks specific to connected devices.
Product security engineers working with connected devices should consider CIoTSP. Compliance officers responsible for IoT governance frameworks. Systems integrators implementing enterprise IoT solutions. Even career changers entering the IoT security field can use this as an entry credential if they've got some baseline IT knowledge.
The actual skills you're validating
The certification proves you can identify IoT-specific security threats and vulnerabilities. Not just generic cybersecurity risks but the unique attack vectors that emerge from device constraints, physical access concerns, and the massive attack surface of distributed IoT deployments. You're demonstrating knowledge of secure IoT architecture across device, edge, and cloud layers. Understanding how security responsibilities shift across these tiers and where the critical control points actually exist.
Authentication gets complicated here. Authorization too. How do you implement access control when devices might not have user interfaces? How do you handle authorization decisions when latency matters and cloud connectivity isn't guaranteed? CIoTSP validates you understand these implementation challenges. Data protection mechanisms including encryption and key management are critical. You need to know how to select appropriate encryption algorithms for resource-constrained devices, implement secure key storage when you don't have hardware security modules available, and design key rotation strategies that work at IoT scale.
Secure device provisioning? Huge. Firmware management? Equally huge. You're proving competency in secure boot processes, signed firmware updates, OTA update mechanisms that maintain device integrity even when updates fail halfway through. Being able to design and implement IoT monitoring and incident response procedures matters because traditional SIEM approaches don't translate directly to IoT environments where you're dealing with different log formats, massive data volumes, and devices that might be offline for extended periods.
IoT vulnerability assessment and security testing require specialized knowledge. How do you perform penetration testing on devices with non-standard interfaces? What firmware analysis techniques reveal security flaws? CIoTSP covers these practical skills. Governance, compliance, and regulatory considerations round out the credential because IoT deployments often span multiple jurisdictions with different data protection requirements. I remember a project where we had sensors in twelve countries and the legal headaches around data residency requirements made the technical challenges look simple by comparison.
Career paths and what this opens up
IoT Security Analyst positions typically range from $75k to $110k depending on location and experience. You're monitoring IoT deployments, investigating security incidents, performing vulnerability assessments, and recommending remediation strategies. IoT Security Architect roles in enterprise and industrial settings can pull $120k to $160k. You're designing secure architectures, selecting security technologies, and establishing security standards for IoT implementations.
Connected Device Security Engineer opportunities? They exist across industries from healthcare to manufacturing. IoT Governance and Compliance Specialist positions are emerging as regulatory requirements intensify. The career advancement opportunities within cybersecurity and IoT domains are solid because the skills gap is real.
CIoTSP complements other certifications well. If you've got CFR-410 or CISSP, adding IoT security expertise makes you more versatile. It pairs naturally with ITP-110 if you want both IoT fundamentals and security depth. Actually that's a really smart combination if you're starting fresh in this space. CompTIA Security+ provides general security foundation, CIoTSP adds the IoT specialization.
Why CertNexus makes sense as a certification provider
CertNexus has built a reputation for vendor-neutral, job-role focused certifications that map to what employers need. Their certification portfolio spans emerging technologies. You've got AIP-110 for AI practitioners, DSP-110 for data science, CET-110 for ethical technology considerations, and CSC-110 for secure coding.
The vendor-neutral approach? It matters in IoT because the ecosystem's fragmented. You're not learning one vendor's proprietary platform. You're learning principles and practices that apply whether you're working with AWS IoT, Azure IoT Hub, industrial protocols, or custom implementations. Industry partnerships and recognition give CertNexus credentials legitimacy. Global acceptance means the certification travels if you're looking at international opportunities.
IoT security isn't going away. The device explosion continues. The attack surface expands. The skills gap persists. Getting certified now positions you ahead of the curve rather than scrambling to catch up when IoT security becomes a mandatory requirement in your industry. CIoTSP gives you a structured path to demonstrate competency in a field where practical expertise is scarce and increasingly valuable.
Exam Details: ITS-110 Format, Cost, and Logistics
What CIoTSP validates (IoT security skills and job roles)
The CertNexus ITS-110 CIoTSP certification is a vendor-neutral IoT security cert that tests whether you actually get how IoT systems fail, how you'd reduce that risk, and whether you can discuss it like someone who does security for a living instead of just collecting smart gadgets. It's not magic. No lab component. Pure knowledge.
Expect heavy security lifecycle thinking. IoT threat modeling, device risk management, secure architecture decisions (device layer, gateway, edge, cloud), plus the practical stuff like secure provisioning and update strategy. The thing is, this maps pretty cleanly to roles like junior security analysts supporting IoT deployments, IoT product security folks, network and security engineers who're suddenly told to "also cover the cameras and sensors," and GRC people needing to ask smarter questions about IoT vulnerability assessment.
Who should earn CIoTSP (target audience)
Look, if your job touches connected devices, you're already in scope. IT folks rolling out smart buildings. OT adjacent teams. AppSec people pulled into "why does this device phone home." Also consultants needing a credible baseline.
Not gonna lie, it's also a decent signal for career switchers because it's specific. Saying "I know security" is vague. "I passed ITS-110 and can explain OTA signing and constrained device controls" is clearer. You sound like someone who actually builds or breaks these systems.
Exam format, duration, and delivery (online vs test center)
The ITS-110 exam format's pretty straightforward. Expect typically 75 to 80 questions, and the question styles are the usual mix: multiple choice, multiple response, and scenario-based questions where you read a short situation and pick the best action or control. Some items feel like policy. Some feel like architecture. A few feel like "spot the risk."
No performance-based items. No hands-on lab. That matters because you're not configuring tools or debugging packets under time pressure. You're proving you know concepts like segmentation, device identity, secure communications, and how to reason about constraints and tradeoffs across an IoT deployment.
Time's usually 90 to 120 minutes depending on the current delivery setup and version. I mean, that's enough time, but only if you don't treat every question like a philosophy debate. Flag hard ones, move on, come back. Three short rules. Read the stem. Watch for "best." Don't overthink.
Closed book. No notes allowed. No reference materials whatsoever. If you're used to open-book vendor exams, adjust your prep because you need recall on basics like crypto use cases, lifecycle stages, and where controls belong in an architecture.
Language's typically English, and CertNexus sometimes offers translations depending on region and partner support, but availability can change. Check the scheduling portal before you commit, because "potential translations" isn't the same thing as "available next week."
Passing score for CIoTSP
The CIoTSP passing score is commonly described as around 70 to 75%, or a scaled score equivalent. CertNexus uses scoring that can be scaled, meaning your final number may not map directly to "you got 56 out of 75." The exam can weigh questions differently, and versions can be equated so different forms stay fair.
You usually get an immediate pass or fail when you finish. Then you get a score report breaking down performance by domain, which's honestly the most useful part if you fail because it tells you where your CIoTSP exam objectives understanding is thin. Also, multiple-response questions typically have no partial credit, so if you pick three correct and one wrong, that can still be a miss. Painful. Real.
Scaled scoring versus raw percentage trips people up. Don't obsess over the math. Focus on mastering the domains, then practice timing with a CIoTSP practice test so you're not rushing the last 15 questions.
Exam cost and voucher options
The CertNexus ITS-110 exam cost is typically in the $295 to $350 USD range as of 2026. That range exists because pricing shifts, training partners bundle differently, and regions vary.
Regional pricing's a thing. Currency conversion can make the total feel random. Taxes too. If you're outside the US, the "same" voucher can land differently once local fees hit, so budget a little extra.
Bundles are common: exam voucher plus Certified Internet of Things Security Practitioner training (official courseware, instructor-led, or on-demand depending on partner). Some bundles are a good deal if you need structure, but if you already have a solid CIoTSP study guide plan and real IoT exposure, you might just buy the voucher.
Retakes usually mean paying again. Full price for each attempt's the standard pattern, and any discounted retake deal tends to be voucher-specific, not automatic. Some organizations can get corporate or volume discounts. Students sometimes get academic pricing, sometimes not. Promotions happen, usually via training partners or seasonal voucher discounts, so if you're flexible, watch for those. I once saw a guy wait three months for a Black Friday deal that saved him eighty bucks, which seemed excessive until his manager refused to reimburse him anyway.
Online proctoring vs test centers (scheduling and logistics)
Delivery's typically either online proctored through Pearson VUE or another authorized partner, or at a physical test center. Both work. Both have tradeoffs.
Online proctoring's convenient. You can often schedule close to 24/7, which's great if you're working full-time and your brain only functions at 9 pm. But your environment has to be clean, quiet, and compliant, and your system has to behave. Test centers are boring but stable. The internet's their problem, not yours.
System requirements for online exams are the usual: a supported OS, a working webcam and mic, stable internet bandwidth, and the ability to install the proctoring app. Corporate laptops can be a mess here. Locked-down devices, blocked permissions, weird VPN behavior. Honestly, do the technical check early. Not the morning of.
Scheduling's generally flexible online, and more limited at centers depending on your city. Rescheduling and cancellation policies vary by provider and how close you are to exam time, so read the fine print when you book, because "I forgot" is rarely refundable.
Check-in usually means government ID, matching name exactly, and a room scan for online proctoring. Rules are strict. No extra monitors. No phones. Break policies vary, and some exams don't allow breaks without ending the session. If you need accommodations, start that process early because approvals can take time.
Certification issuance and score validity timeline
After you pass, the official certification typically shows up in your CertNexus portal within a short window. Often days, sometimes a bit longer depending on processing. You'll usually get a digital certificate and a badge through a badge platform. Then you can verify your status via the portal or a verification link.
Add it to LinkedIn and your resume the same day. Quick win. Put "CertNexus ITS-110 (CIoTSP)" plus the full name once. Don't spam keywords.
Validity and CIoTSP renewal requirements depend on CertNexus policy for that credential at the time you earn it. Many modern certs use a renewal cycle with continuing education credits and a fee, or periodic recertification. Check the current candidate handbook, because renewal rules are the kind of thing that change quietly.
Registration process (step by step)
Create a CertNexus account. Simple. Then purchase an exam voucher either directly or through a training partner.
Pick delivery method. Online proctoring or test center. Choose location if needed. Schedule your date and time. You'll get confirmation emails, and they matter because they include candidate rules and links to pre-exam system tests.
Do the technical check if you're online. Do it again a day before. Different network. Different room. Less risk.
Retake policies and what to do if you fail
Waiting periods are typically 14 to 30 days between attempts, and there may be limits on how many retakes you can do in a year. Every retake generally needs a new paid voucher. Yeah, it adds up.
Use the domain score report like a map. If you bombed data protection, go back to encryption basics, key management, and secure communications choices that fit constrained devices. If architecture tripped you up, sketch secure IoT architecture patterns on paper and practice explaining why the gateway exists, where auth belongs, and how logging works when devices are offline half the time.
Remediation strategy matters. Read the CIoTSP exam objectives, match them to your notes, do a CIoTSP practice test, and then review wrong answers until you can explain them without guessing. That's the whole game.
Quick FAQs people always ask
What is the CertNexus ITS-110 CIoTSP certification and who should take it?
It's an IoT security certification for people building, deploying, or securing connected devices and their supporting systems. If IoT shows up in your tickets, you're a candidate.
How much does the CertNexus ITS-110 exam cost?
Typically $295 to $350 USD, plus regional fees, with possible bundle and voucher discounts.
What is the passing score for the CIoTSP exam?
Usually around 70 to 75% or a scaled equivalent, with immediate pass or fail and domain-level feedback.
How hard is the CIoTSP exam and how long should I study?
Intermediate if you know security basics, harder if IoT's new. Most people need a few weeks of focused study, especially on protocols, constrained device realities, and lifecycle controls.
What are the CIoTSP renewal requirements and how do you maintain the certification?
Follow the current CertNexus policy for renewal cycle, fees, and continuing education credits. Log your training, relevant work, and approved learning activities so renewal doesn't become a last-minute scramble.
CIoTSP Exam Objectives: Complete Domain Breakdown
Understanding the ITS-110 exam blueprint
The CertNexus ITS-110 exam isn't one of those certs where you can just skim a guide and wing it. The blueprint they publish? Actually detailed, which is good news. You know exactly what you're signing up for. Each domain's got a percentage weighting that tells you where to focus study time. Ignoring those percentages is a rookie mistake I've seen people make way too often, even folks who should know better by that point in their careers.
Official exam objectives map pretty directly to what you'll actually do in IoT security work. This is refreshing compared to some certs that feel ridiculously academic. When you're studying threat modeling for IoT, you're learning skills that translate to real deployments. The 2026 version added more emphasis on edge computing security and updated the cryptography section to reflect lightweight algorithms that actually work on constrained devices.
One thing. You can't just pick your favorite domains and ignore the rest. I mean, you could try, but the weighting's distributed enough that weak spots'll hurt you. Domain 2 might be 22% max, but Domain 8 still hits 8-12%, and those governance questions can be tricky if you've never thought about supply chain risk in IoT contexts before. Like, I once watched someone bomb an otherwise solid exam performance because they figured governance was just fluff. It wasn't.
IoT security foundations make up the base layer
Domain 1 covers roughly 15-20% of the exam. Foundational stuff you absolutely need. The IoT ecosystem's more than just smart lightbulbs. You've got perception layers with sensors, network layers handling communication, application layers processing data, and users interacting with it all. This expands your attack surface in ways that traditional networks just don't experience at the same scale or complexity.
Resource constraints? Huge deal. In IoT security, unlike traditional IT where you can throw more RAM at a problem, IoT devices often have kilobytes of memory and run on batteries. This creates unique security challenges that don't exist in server environments. Scale matters too because you might secure one device perfectly, but what happens when you're managing 50,000 of them across different firmware versions?
Threat actors targeting IoT range from script kiddies building botnets to nation-states conducting espionage through connected devices. The Mirai botnet showed everyone what happens when default credentials meet massive scale. Wasn't pretty. Physical attacks're also on the table since many IoT devices sit in accessible locations.
The exam covers threat modeling methodologies like STRIDE adapted for IoT contexts, and you need to know frameworks like the OWASP IoT Top 10 and IEC 62443. NIST's got IoT-specific guidance too. Security by design principles mean building security in from the start rather than bolting it on later, which should be obvious but clearly isn't based on the state of consumer IoT.
Architecture and design questions test your practical knowledge
Domain 2's weighted at 18-22%, making it one of the heaviest sections. The multi-layer architecture questions go deep into how perception layers, network layers, and application layers interact and where security controls fit. Some scenarios'll make you think twice about deployment decisions you might've considered straightforward before studying this material.
Edge computing versus cloud? Big decision point in IoT deployments. Edge processing reduces latency and keeps sensitive data local, but it also means you're securing compute resources in potentially hostile physical environments. Cloud processing centralizes security controls but creates bandwidth and privacy concerns.
IoT gateways act as aggregation points and protocol translators. Critical security chokepoints. Network segmentation strategies often isolate IoT devices on separate VLANs or even physically separate networks because compromised IoT devices shouldn't have access to your corporate network.
Communication protocols like MQTT, CoAP, and AMQP each have different security characteristics. MQTT's popular but the basic version has no built-in security. Like, none. CoAP's designed for constrained devices and supports DTLS. You need to know when to use each and how to secure them properly.
Wireless security gets complicated fast. Wi-Fi security's relatively well understood, but Zigbee, LoRaWAN, and cellular IoT each have unique threat models that don't always map to what you'd expect from wired or traditional wireless experience. Bluetooth Low Energy's had multiple security vulnerabilities discovered over the years. The exam expects you to understand these differences, not just memorize protocol names.
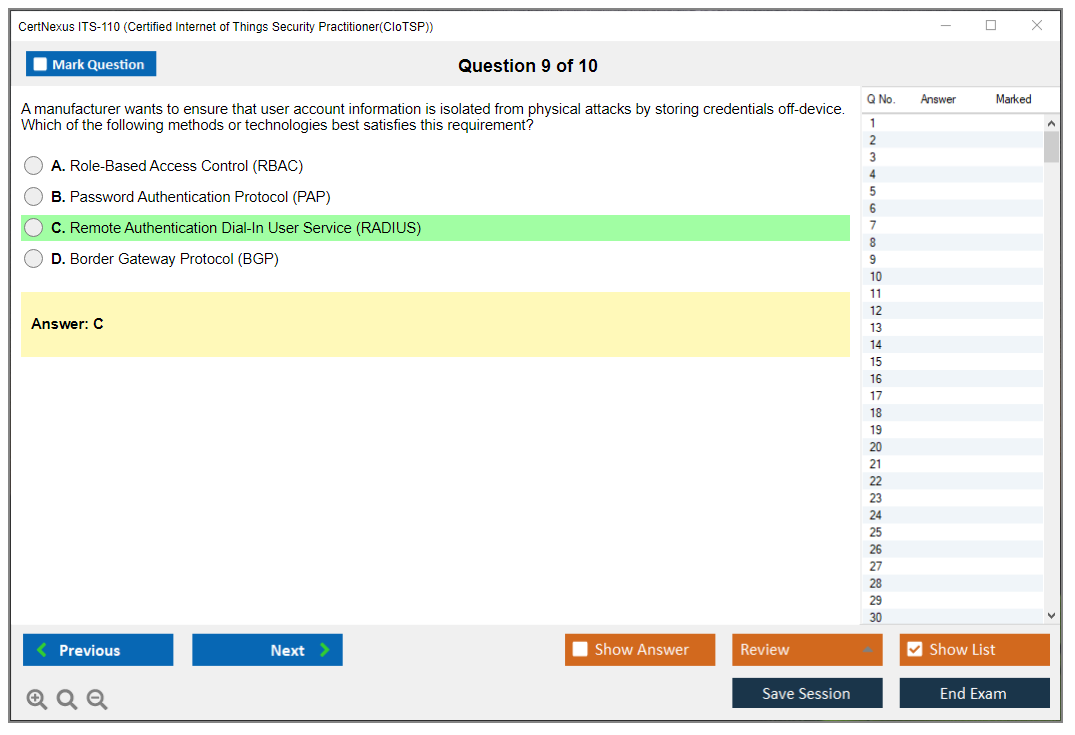
Identity and access control in resource-limited environments
Domain 3 covers 15-18%. Focuses on how you authenticate and authorize devices that might not have keyboards or displays. Device identity management starts at provisioning when you establish a unique identifier and credentials for each device.
Certificate-based authentication using PKI's common in enterprise IoT, but managing certificate lifecycles across thousands of devices creates operational challenges that'll keep you up at night if you're not careful. Some devices support hardware-backed certificates stored in secure elements, others rely on software storage that's more vulnerable.
Authorization models like RBAC work okay for user access, but ABAC (attribute-based access control) often makes more sense for IoT where you're making decisions based on device type, location, trust level, and other attributes. OAuth and OpenID Connect're showing up more in IoT platforms, especially for third-party integrations.
Device attestation proves a device's running legitimate firmware and hasn't been tampered with. Ties into secure boot concepts. Decommissioning's often overlooked but you need processes to revoke credentials when devices're retired or compromised.
Data protection across the IoT lifecycle
Domain 4 weighs in at 15-18%. Covers how you protect data from collection through storage and transmission. Data classification in IoT contexts means understanding that some sensor data's innocuous while other telemetry could reveal personal information or trade secrets.
Encryption at rest protects stored data, but many IoT devices have limited storage encryption capabilities. Encryption in transit using TLS is standard, but TLS overhead can be too much for constrained devices, leading to alternatives like DTLS or even custom lightweight protocols.
Lightweight cryptography's its own specialization. Algorithms like ECC provide strong security with smaller key sizes compared to RSA. AES-128's often preferred over AES-256 because the performance difference matters on low-power processors.
Key management's where many IoT deployments fail spectacularly. How d'you securely distribute keys to devices? Where're they stored? When d'you rotate them? Hardware security modules and secure elements provide tamper-resistant key storage, but they add cost. Budget conversations around HSMs can get contentious fast. The exam covers key lifecycle management from generation through rotation and revocation.
Privacy-enhancing technologies matter more as regulations like GDPR apply to IoT data. Anonymization and pseudonymization techniques can reduce privacy risks, but they need to be implemented correctly or they're useless.
Secure provisioning and firmware management
Domain 5 accounts for 12-15%. Covers how devices get configured initially and updated throughout their lifecycle. Zero-touch provisioning sounds great but introduces security risks if not implemented carefully. You need secure channels for initial credential exchange.
Firmware security starts with secure coding practices but extends to code signing so devices can verify updates're legitimate. Over-the-air updates're necessary for patching vulnerabilities, but the update mechanism itself can be an attack vector. Rollback protection prevents attackers from downgrading to vulnerable firmware versions.
Secure boot chains verify each component in the boot process, establishing a hardware root of trust that's non-negotiable for high-security deployments. Trusted execution environments isolate sensitive operations from the main OS. Managing patches across diverse IoT fleets with different firmware versions and capabilities's really hard, and the exam tests your understanding of these challenges.
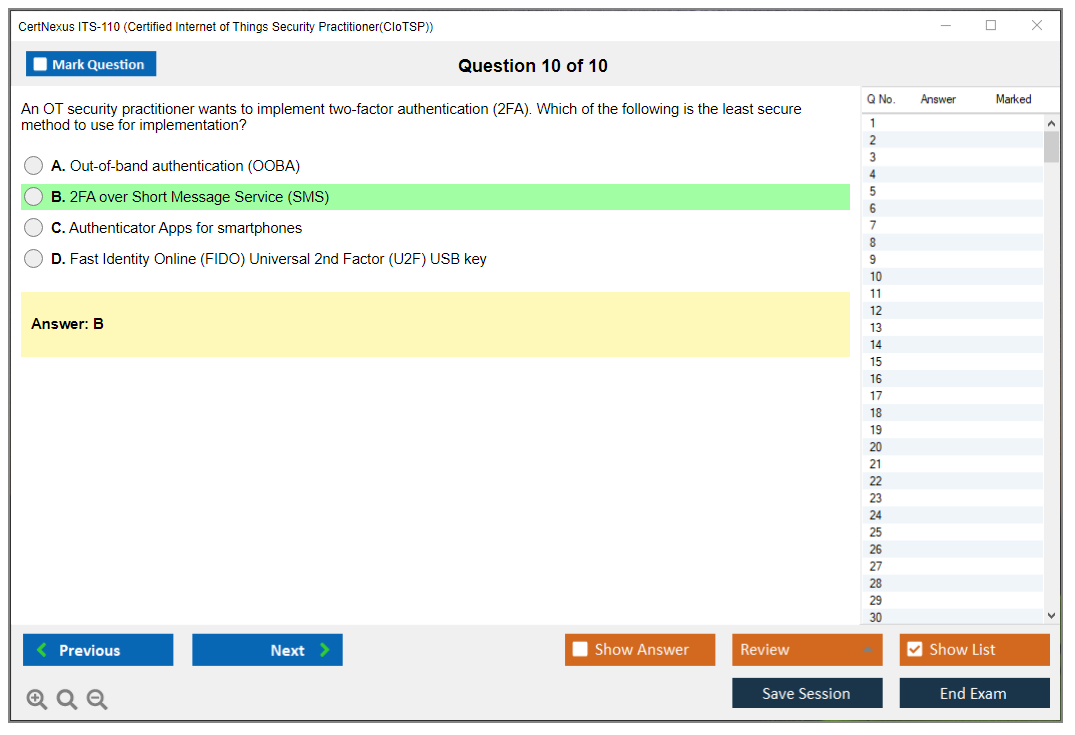
Monitoring and responding to IoT security incidents
Domain 6 covers 10-15%. Addresses how you detect and respond to security events. IoT monitoring's challenging because devices might have limited logging capabilities and generate massive volumes of telemetry that can hide malicious activity.
SIEM integration for IoT requires adapting traditional security monitoring to device constraints and scale. Anomaly detection and behavioral analytics can identify compromised devices based on unusual communication patterns or activity. Works pretty well when tuned right. Centralized logging architectures need to handle high-volume, low-value logs without choking.
Incident response for IoT has unique challenges like devices in remote locations or embedded in critical systems that can't be taken offline easily. Forensics on IoT devices might involve hardware analysis if firmware's been modified. Business continuity planning needs to account for scenarios where IoT systems're unavailable.
Testing and assurance validate your security controls
Domain 7's 10-12%. Covers how you verify IoT security. Penetration testing IoT systems requires different tools and techniques compared to traditional IT. You might need hardware hacking skills to access debug ports or extract firmware.
Fuzzing helps discover vulnerabilities in protocol implementations and input handlers. Static code analysis can identify security flaws in firmware before deployment, which saves a ton of headache later. Hardware security testing might involve JTAG debugging or side-channel analysis to extract cryptographic keys.
Security validation confirms controls're working as designed. Device hardening involves disabling unnecessary services, changing default credentials, and minimizing attack surface. Third-party security assessments and certifications provide independent verification, which matters for compliance and customer confidence.
Governance and compliance tie it all together
Domain 8 rounds out the exam at 8-12% with policy, regulatory, and legal considerations. IoT security policies need to address the entire device lifecycle from procurement through disposal. Disposal's often forgotten until it becomes a problem. Regulatory compliance varies by industry and region, with healthcare, automotive, and critical infrastructure having specific requirements.
Supply chain security's critical because you're trusting vendors for device security. Vendor risk management processes should evaluate security practices before procurement. Privacy impact assessments identify risks from data collection and processing. Liability considerations matter because IoT security failures can have real-world consequences beyond data breaches.
Studying all eight domains thoroughly? Non-negotiable for passing ITS-110. The weighting tells you where to spend more time, but gaps in any domain'll cost you points. If you're serious about preparing, the ITS-110 Practice Exam Questions Pack gives you realistic questions across all domains so you can identify weak areas before test day. The exam maps well to real-world IoT security work, which makes the study time worthwhile beyond just passing the cert.
Prerequisites and Recommended Experience for CIoTSP
Quick overview of CertNexus ITS-110 (CIoTSP)
The CertNexus ITS-110 CIoTSP certification targets IoT security. It's for folks securing connected devices end to end, not just running a vulnerability scan and calling it done. You'll see different roles here. SOC analysts dealing with IoT alerts, network admins suddenly managing "smart" everything, appsec people reviewing device APIs, plus engineers designing secure IoT architecture spanning device, gateway, edge, and cloud layers.
Reality check time.
IoT's messy. Constraints hit hard. Attack surfaces? They sprawl everywhere, and honestly, that's where most teams start panicking because traditional security playbooks don't quite fit when you're dealing with a sensor running on a coin battery that needs to last five years. I once watched a team spend three weeks trying to figure out how to patch a device that was literally welded shut inside a street lamp. That kind of thing never comes up in the CISSP curriculum.
If you're wondering "What is the CertNexus ITS-110 CIoTSP certification and who should take it?", here's my take: go for it if you're already doing security work and keep running into devices you can't fully control, or if you're in IoT engineering and you're sick of security being that afterthought someone remembers right before launch with a hastily assembled checklist and terrible energy.
What CIoTSP validates day to day
CIoTSP proves you can handle IoT device risk management throughout a complete lifecycle. Provisioning, identity, firmware, wireless links, cloud backends, and yeah, the ugly parts. Logging gaps and patching realities that nobody wants to discuss in status meetings. It also digs into IoT threat modeling and IoT vulnerability assessment, which separates disciplined teams from ones that'll get absolutely wrecked.
Lots of certs talk security. This one's different.
It focuses on security where devices are fragile, protocols get weird, and you've gotta care about what happens after deployment, when that thing's sitting in a warehouse, mounted on a pole, or living in somebody's kitchen collecting dust and data.
Exam details that matter (ITS-110)
CertNexus exam delivery typically happens through online proctoring or test centers, depending on your region and what's available when you actually buy the voucher. The format's multiple choice style, leaning toward applied knowledge rather than math problems or code debugging. Time limits and question counts shift around, so I always tell people to double-check the official listing right before scheduling. Stale blog posts are literally everywhere and nobody updates them.
People also ask "How much does the CertNexus ITS-110 exam cost?". The CertNexus ITS-110 exam cost varies based on whether you're buying a standalone voucher, getting it bundled with Certified Internet of Things Security Practitioner training, or purchasing through a partner. Voucher pricing fluctuates more than you'd expect. Training bundles can be worthwhile if structure helps you learn, but if you're already doing security work you might be fine self-studying plus working through practice questions.
Another common one: "What is the passing score for the CIoTSP exam?" CertNexus publishes scoring policies per exam, and that's where you'll locate the current CIoTSP passing score. Don't obsess over it. Focus on mastering the CIoTSP exam objectives, because scoring changes won't save you if you can't reason about secure provisioning, device identity, or what "secure communications" actually means when you're working with constrained hardware that can barely run AES.
What to study (CIoTSP exam objectives)
The CIoTSP exam objectives read like stuff teams argue about in actual projects, which I mean as a genuine compliment.
IoT security foundations appear first: attack surface, threats, risks, and how devices differ from normal endpoints that you can just throw an agent on and forget. Then you get into architecture. Device, gateway, edge, cloud, and designing systems so you're not trusting the wrong layer or assuming a compromised device can't pivot to your entire network. Identity, authentication, and access control are massive, because "default password" is still ending careers in 2025.
Data protection's another core bucket. Encryption, key management, secure communications, and what breaks when devices have limited CPU, memory, or power budgets that make your favorite cryptographic library completely impractical. Secure provisioning, firmware integrity, signing, and OTA updates matter tremendously too.
An update pipeline's basically a supply chain pipeline with all the same nightmare scenarios.
Monitoring and incident response in IoT environments shows up, and honestly this is where organizations are weakest. Logs don't exist, telemetry's thin, and someone decided the device can't phone home "because bandwidth costs", so good luck investigating that breach. Testing and assurance covers IoT vulnerability assessment, validation, and hardening. Governance and compliance rounds it out, because regulated industries keep buying IoT anyway despite having no idea how to secure it properly.
Official prerequisites (what CertNexus requires)
Here's the deal with CIoTSP prerequisites: there usually aren't formal ones.
CertNexus typically states no mandatory prerequisites for ITS-110, and they run an open enrollment policy where basically anyone can attempt the exam without proving work history or showing other certifications first. That's not a loophole. That's intentional design. You don't need to show proof of work history, you don't need another cert, and there isn't a gatekeeping checklist blocking your path.
That said. No prerequisites isn't "no prep". Huge difference.
Formal prerequisites are about eligibility. Recommended preparation's about whether you'll pass without questioning your career choices halfway through question 30. CertNexus keeps barriers low because IoT security's still a massive skills gap problem, and blocking entry behind a stack of other certs would just slow down the people who actually need this knowledge, like engineers being thrown into securing connected systems with zero warning and a two-week deadline.
Recommended background knowledge and experience
Networking fundamentals matter way more than people expect. If TCP/IP, the OSI model, DNS, DHCP, NAT, TLS, and common ports are fuzzy concepts, you'll feel it immediately. IoT stacks are basically networking plus constraints plus weird protocols nobody teaches in boot camps, so your baseline has to be rock solid.
Foundational cybersecurity concepts are table stakes. CIA triad, authentication versus authorization, basic crypto concepts, hashing versus encryption, key handling, and why "we rolled our own crypto" is the opening line of every security postmortem. You should also understand operating system security on Linux and Windows, plus at least the general idea of embedded OS realities, like limited logging capabilities and minimal patch windows that make vulnerability management a creative exercise.
Cloud computing concepts help since most IoT platforms are cloud-backed nowadays. You don't need to be an AWS wizard, but you should understand IAM, device identity patterns, message brokers, and where telemetry actually lands when devices phone home. A general awareness of IoT ecosystems and use cases matters too, because threat models change dramatically depending on whether you're securing consumer cameras, industrial sensors, medical devices, or fleet trackers that need to work in places without reliable connectivity.
Programming or scripting exposure's helpful but not essential. Python helps you reason about automation and parsing weird data formats. C helps you understand why memory bugs still matter and why buffer overflows aren't just theoretical problems. JavaScript shows up if you touch dashboards and APIs.
You can pass without being a developer, but you can't pass if you refuse to think like one or understand how code decisions create security implications.
Security tools familiarity's also useful. Wireshark, basic vulnerability scanners, API testing tools, and some comfort reading logs without immediately panicking. You don't need to be a pentester with a black hoodie, but you should be able to recognize what "normal" traffic looks like and when a device's doing something sketchy at 3 AM.
Ideal work experience before pursuing CIoTSP
I usually recommend 1 to 2 years in IT, cybersecurity, or a related technology role before attempting CIoTSP. Not because the exam's elite or gatekept, but because context matters tremendously. If you've never troubleshot a network issue, never handled patching cycles, never seen an incident ticket escalate, a lot of the exam questions feel abstract rather than practical scenarios you can visualize.
Hands-on exposure to IoT devices is beneficial. Even home lab stuff counts.
A smart plug, a camera, a Zigbee hub, a local MQTT broker, and you poking at traffic with curiosity. That's valuable experience. Network administration experience helps tremendously because you already think in flows and segmentation rather than just "plug it in and hope." SOC or security operations experience helps because you've already built the mental habit of "what could go wrong, and how would we actually detect it happening."
Project involvement with IoT deployments is excellent, especially if you've dealt with onboarding, provisioning, and ongoing support headaches. Security assessment or testing experience transfers well too. No specific IoT security experience is required, but if you've done any secure IoT architecture reviews or device hardening work, you'll recognize patterns instead of just memorizing terms that all sound similar.
Certifications that pair well with CIoTSP prep
If you want a clean runway, CompTIA Network+ and Security+ are the obvious foundation. Security+ is a baseline for general security language and concepts that everyone assumes you know. Network+ helps you stop guessing about protocols and traffic patterns.
CertNexus CFR's a good match if you're coming from an operations angle and want more incident response muscle memory. SSCP's solid for practitioners who want broader security coverage beyond just IoT. CEH can help if you're weak on testing methodology, though honestly it's most useful when you already have lab time and want a structured view of attacker workflows rather than just theoretical knowledge.
How they build toward CIoTSP success is pretty straightforward. Network+ gives you the "how does it talk" layer. Security+ gives you the "how do we protect it" layer. CFR helps with "what do we do when it breaks and everyone's freaking out". Then CIoTSP ties all that to IoT constraints, lifecycle realities, and the device-to-cloud chain that's way more complex than most people expect.
Technical skills to build before you grind study mode
Packet analysis in Wireshark's huge. If you can filter traffic, follow streams, and spot TLS handshakes without constantly Googling syntax, you're way ahead. Basic Linux command line proficiency matters because tools, scripts, and embedded environments tend to look Linux-ish even when they're running some proprietary embedded OS.
Wireless knowledge helps a lot. Wi-Fi basics, Bluetooth/BLE concepts, Zigbee/Thread awareness, and understanding what changes when you're not on nice reliable Ethernet with predictable behavior.
Encryption concepts matter too, especially key management and how certs and trust chains behave in the real world when someone misconfigures something.
Cloud platform basics help, specifically AWS IoT, Azure IoT, and Google Cloud IoT patterns, even if Google's product names keep changing every six months. API testing tools are also worth learning because IoT backends are just API backends with extra steps and usually worse documentation. Configuration management and hardening techniques show up across devices, gateways, and cloud services, and you should be comfortable with the idea of secure defaults and least privilege, even when developers fight you on it because "it's easier this way."
Knowledge gaps for career changers (and how to patch them)
IT folks new to security should focus on threat modeling and risk assessment. Not fancy templates that nobody uses. Just learn to identify assets, entry points, trust boundaries, and realistic attacker goals, then map controls that actually fit the budget and constraints.
Security folks new to IoT need to learn device constraints and protocols fast. Battery life, compute limitations, intermittent connectivity, limited patch ability, and long lifecycles change absolutely everything about how you approach security. Developers moving into security need a defensive mindset and more testing practice, because "it works on my machine" isn't a security argument and never will be.
For self-study, mix a CIoTSP study guide style resource with vendor documentation and hands-on labs. Online courses and bootcamps can speed things up if you need structure fast, but you still need lab time, even if it's just capturing traffic from a cheap device and writing down what you see happening.
If you want a focused way to pressure-test your readiness, a practice pack helps tremendously. I've seen people get real value out of the ITS-110 Practice Exam Questions Pack when they treat it like diagnostics, not like a magic shortcut that'll somehow teach them everything. Use it, mark weak domains, go back to the objectives, then retest. Repeat until patterns emerge. Same advice applies if you use any CIoTSP practice test, whether official or third-party.
Also, budget time for review. Honestly. Rushing through material is how you miss easy points on questions you actually knew but misread because you were panicking about time.
Academic background considerations
Computer science or engineering degrees help because you've probably seen networking fundamentals, OS concepts, and basic programming logic. Cybersecurity programs align well too, especially if they covered threat modeling or secure systems design rather than just compliance checklists.
Self-taught people can absolutely pass. I mean, a lot of the best security folks I've worked with learned by building labs, breaking stuff intentionally, fixing it, then writing down what they wish they'd known earlier and sharing it with others.
Certs can substitute for formal education in many hiring pipelines, especially when you combine them with actual projects. A home IoT lab write-up, a small assessment report, or a GitHub repo with scripts and detailed notes can do more for credibility than a transcript nobody bothers reading anyway.
Difficulty, practice strategy, and renewal notes
People ask "How hard is the CIoTSP exam and how long should I study?" I'd call it beginner-to-intermediate, but spiky in specific areas. The spikes are protocols, lifecycle security, and reasoning about constraints when perfect security isn't possible. If you already know networking and security basics, 3 to 6 weeks of consistent study plus lab work is realistic. If you're new to both domains, plan longer and be patient with yourself.
For prep strategy, don't just read passively. Do stuff.
Use the ITS-110 Practice Exam Questions Pack once early to find your gaps and weak domains, then again near the end to check timing and mental endurance, and keep your notes mapped directly to the CIoTSP exam objectives so you're studying what's actually tested rather than interesting tangents.
Renewal comes up too. "What are the CIoTSP renewal requirements and how do you maintain the certification?" CertNexus has specific CIoTSP renewal requirements around renewal cycles, fees, and continuing education policies, and those can shift over time, so confirm on their official site rather than trusting old forum posts. In general, expect to track continuing education credits through training courses, relevant work projects, and ongoing learning activities that prove you're staying current.
One last thing. If you're stressing about eligibility, stop. Open enrollment means you can take the shot whenever you're ready. The real prerequisite is being willing to learn the parts of IoT security that are really annoying and frustrating, because those are usually the parts that matter most when something goes wrong in production.
Difficulty Level and Pass-Rate Expectations
Is this exam actually hard or just hyped up?
Okay, so here's the deal. The CIoTSP occupies this strange in-between space that really surprises people. It's not entry-level material you'll master during a casual weekend study marathon, but it won't make you spiral into existential dread about your professional path either. Most folks I've chatted with who've actually sat for it? They call it moderately challenging, which, I mean, honestly feels pretty accurate.
Here's the thing though. Intermediate isn't the same as simple. You need legitimate security fundamentals already ingrained in your skillset, and memorizing textbook definitions won't cut it for passing. The ITS-110 (Certified Internet of Things Security Practitioner (CIoTSP)) exam demands you apply conceptual knowledge to authentic scenarios, which is where tons of candidates faceplant even after they've supposedly studied everything.
How CIoTSP stacks up against other certs you might know
Knocked out Security+ or Network+ already? CIoTSP's definitely more complex. Those foundational certifications provide breadth across topics, but CIoTSP expects you to dive considerably deeper into IoT-specific domains while maintaining that full security perspective. I'd compare it to CySA+ or SSCP difficulty-wise, maybe slightly less brutal than CEH depending on what background you're bringing.
It's nowhere near CISSP or OSCP territory. Those are different beasts. CISSP has that managerial orientation and ridiculous breadth spanning all domains, while OSCP'll have you yanking your hair out during lab exercises at ungodly hours. CIoTSP doesn't require that intensity of commitment or accumulated experience. The specialized GIAC certifications typically penetrate way deeper into particular niches than CIoTSP attempts.
The IoT specialization's what distinguishes it, though. You can't just coast on generalized security knowledge. You've gotta understand how resource-constrained devices fundamentally alter the security equation, why protocols like MQTT and CoAP actually matter in practice, and how edge computing architectures differ from traditional cloud security models. Wait, did I mention the protocol diversity? Because honestly, that alone could fill a separate exam. Anyway, that specialization elevates it beyond entry-level classification.
What actually trips people up on this exam
Understanding IoT protocols plus their security implications? Probably the biggest stumbling block I've witnessed. MQTT, CoAP, Zigbee, LoRaWAN..these aren't technologies most security professionals encounter daily. You need to know not just their definitions, but where vulnerabilities hide and how to secure them across different deployment contexts. The exam throws scenarios requiring you to select the appropriate protocol for specific use cases while juggling security constraints at the same time.
Resource limitations really mess with people's intuitions. In traditional IT security, you throw computational power at problems without thinking twice. Need stronger encryption? Sure, provision more processing capacity. But IoT devices might operate on batteries for years with minimal CPU power, so suddenly you're making tradeoffs you've literally never considered before. The exam tests whether you really understand these constraints or if you're just slapping desktop security logic onto embedded devices.
Cryptography selection gets complicated fast. You can't just declare "use AES-256 for everything" and consider it solved. The exam wants you knowing when symmetric versus asymmetric makes sense, how key management functions when you've deployed thousands of field devices, and why lightweight cryptography even exists as a category. I've watched people who understand crypto theoretically completely bomb questions about applying it to IoT scenarios.
Secure firmware updates and OTA processes represent another pain point candidates struggle with consistently. How do you ensure integrity? What happens if an update fails midway through? How do you prevent rollback attacks? The exam digs into these lifecycle management issues that plenty of security professionals never contemplate until they're suddenly responsible for managing a fleet of deployed devices.
The distinction between edge, fog, and cloud security approaches trips people up because it's not always clear-cut where processing should occur or how to secure data moving between these architectural layers. Scenario questions describe a deployment and ask you identifying security gaps or recommending controls, which requires synthesizing knowledge across multiple domains at once.
What you can realistically expect for pass rates
CertNexus doesn't publish official pass rate statistics, which honestly is pretty standard in the certification industry. Based on conversations with training providers and actual candidates, I'd estimate well-prepared folks pass at around 60-70% on their first attempt. That's not terrible, but it's also not guaranteed.
First-time pass rates are probably lower than overall rates since people who fail tend to return better prepared. I mean, failing once provides you a much clearer picture of what the exam actually tests versus what you assumed it would test. The candidates who invest in proper training materials, allocate enough study time, and have some hands-on IoT experience tend to perform better than those attempting to wing it based solely on general security knowledge.
Some candidates fail despite what appears like solid preparation because they underestimate the scenario-based question format. You can know all the facts but still select wrong answers if you can't apply that knowledge to realistic situations presented. Others fail because they focus too heavily on one or two domains and get blindsided by questions from areas they glossed over during studying. The exam pulls from all eight domains, so knowledge gaps will hurt you.
How much time should you actually budget for studying?
Already working in security with some IoT exposure? Figure 40-60 hours spread over 4-6 weeks is reasonable. That gives you enough time to fill knowledge gaps, work through practice questions, and get comfortable with IoT-specific concepts without burning out completely. You're not starting from zero, so you can focus on the specialized material.
IT professionals new to security should plan for 80-100 hours over 8-12 weeks. You need learning both security fundamentals and the IoT-specific applications, which just takes time to absorb properly. Rushing through it in a month might work if you're a fast learner with exceptional retention, but most people need that longer timeline letting concepts sink in.
Career changers or people without much IT background? Budget 120-150 hours over 12-16 weeks minimum. I know that sounds like a ton. You're learning security from scratch plus a specialized subdomain layered on top. The CFR-410 (CyberSec First Responder (CFR) Exam) might actually be a better starting point if you're completely new to security, then circle back to CIoTSP once you've established fundamentals.
Intensive study works for some people, like if you've got a week off and can dedicate 8-10 hours daily to studying. I've known folks who've passed after cramming for two weeks straight, but that approach is risky and the knowledge doesn't stick as well long-term. Distributed learning over several weeks gives your brain time processing and connecting concepts, which helps not just for passing but for actually using this knowledge on the job.
Why CIoTSP is more manageable than it seems at first
The exam objectives are well-defined. Gives you a clear roadmap for what to study. You're not guessing at what might appear on the exam. CertNexus lays out the eight domains and what falls under each, so you can methodically work through the material without wondering if you're missing something critical.
There's a ton of IoT security resources available now compared to even a few years ago. It's kinda crazy actually. NIST has published IoT security frameworks, OWASP has IoT-specific guidance, and vendors have released whitepapers on securing various protocols and implementations. You're not hunting for scarce information anymore.
The vendor-neutral approach helps too, which I appreciate. You don't need learning proprietary platforms or specific product implementations. The exam tests concepts and best practices that apply across different IoT ecosystems, which reduces the complexity compared to vendor-specific certifications where you're memorizing menu structures and command syntax.
No hands-on lab component means you're not being evaluated on your ability performing under time pressure in a practical environment. Multiple choice format lets you use elimination strategies and educated guessing when you're not 100% certain. The exam duration gives you enough time per question, so you're not frantically rushing through.
Why it's trickier than the marketing materials suggest
The breadth of coverage across eight domains means you can't just master two or three areas and hope for the best. Questions come from everywhere, and you need at least working knowledge of all domains to hit the passing score. Some candidates underestimate this and focus too narrowly on favorite topics.
The depth required in specialized areas like cryptography and protocol security goes beyond surface-level understanding completely. You can't just know that MQTT uses publish-subscribe messaging. You need understanding QoS levels, authentication mechanisms, and how TLS fits into the picture architecturally. The exam'll test whether you actually get it or just memorized a definition from study materials.
Distractors in questions are designed catching superficial understanding. Wrong answers often sound plausible if you're not thinking carefully about the scenario presented. I've seen practice questions where three of four answers are technically correct in some context, but only one fits the specific scenario described. That requires careful reading and solid comprehension, not just pattern matching to keywords you studied.
The rapidly evolving nature of IoT security means the exam has to balance established best practices with emerging threats and solutions constantly. You need staying current with industry trends while also understanding foundational concepts that don't change. The AIP-110 (Certified Artificial Intelligence Practitioner) faces similar challenges with fast-moving technology, but IoT has the added complexity of diverse hardware, protocols, and deployment environments that all need securing differently.
Conclusion
Wrapping things up
Look, here's the deal. The CertNexus ITS-110 CIoTSP certification isn't just another cert to toss on your resume. It fills this weird gap that tons of security professionals don't even realize exists until they're knee-deep in an IoT deployment that's completely fallen apart. The exam objectives cover everything from secure IoT architecture to device risk management and threat modeling, which honestly makes sense given how absolutely chaotic IoT environments become when security's treated like an afterthought instead of a foundation.
The CIoTSP passing score? Sits at 70%. Sounds reasonable, right? Until you're actually there trying to remember the difference between secure provisioning methods across different device types while the clock's ticking and your brain's foggy. Not gonna lie, the CertNexus ITS-110 exam cost is pretty competitive compared to vendor-specific IoT security certification options. Especially when you factor in that you're learning vendor-neutral concepts that apply whether you're working with industrial sensors or smart building systems or whatever IoT mess your organization's deployed.
Here's what matters most, I think. The CIoTSP prerequisites are minimal. Like, really minimal. But your actual success depends entirely on how well you understand networking fundamentals and basic security principles before diving into IoT-specific challenges like constrained device security and OTA firmware updates. You can memorize facts about IoT vulnerability assessment techniques all day long, but if you don't actually grasp why edge computing changes your security model, you're gonna struggle hard with scenario-based questions that require applying concepts rather than regurgitating definitions.
The Certified Internet of Things Security Practitioner training options? They vary widely in quality and depth, honestly. Some people crush this exam with just the official study materials. Others need hands-on labs with actual IoT devices to make concepts stick in their heads. Whatever your learning style happens to be, don't skip the practice tests. They expose gaps in your knowledge about governance frameworks and compliance considerations that you probably glossed over (or let's be real, completely skipped) during initial study sessions.
One thing about CIoTSP renewal requirements: they're pretty straightforward compared to some other certs I've dealt with, but you need to plan ahead because those continuing education credits don't accumulate by themselves. Set calendar reminders. Like, now. I once let a different cert lapse because I kept thinking I had more time than I actually did, and having to retake an exam you already passed once is the kind of special frustration that stays with you.
If you're serious about checking your IoT security skills and want a reality check before exam day, the ITS-110 Practice Exam Questions Pack gives you scenario-based questions that mirror the actual test format. It's honestly one of the better ways to identify weak spots in areas like secure communications protocols or incident response procedures specific to IoT environments before you drop money on the real exam. The thing is, most people don't realize where their knowledge gaps are until they're staring at a question that seems like it's written in another language.