Fortinet NSE4_FGT-7.2 (Fortinet NSE 4 - FortiOS 7.2)
Fortinet NSE4_FGT-7.2 Exam Certification Overview
Look, if you're working with FortiGate firewalls or thinking about getting into them, the Fortinet NSE4_FGT-7.2 exam isn't optional. This certification sits in the middle of Fortinet's Network Security Expert program. It proves you can actually deploy and manage FortiOS 7.2 devices instead of just clicking around interfaces and hoping things work out.
What is the Fortinet NSE4_FGT-7.2 certification and why it matters
The NSE 4 FortiGate tier represents professional-level competency within Fortinet's ecosystem. You're beyond basics here. This is actual implementation territory where companies need reliable expertise. Below it sit the foundational NSE 1-3 certifications, mostly awareness stuff and basic concepts. Then above you've got specialized NSE 5-8 tracks where things get seriously technical and demanding. NSE 4's where you demonstrate you can actually do the work instead of just sounding knowledgeable in meetings.
FortiOS 7.2 introduced substantial changes from earlier versions. Improved SD-WAN capabilities, enhanced security fabric integration, and interface adjustments that really matter when you're configuring devices every single day. That's why version-specific certification isn't just Fortinet being picky. Version 7.2 really differs from 7.0 and definitely represents a significant departure from 6.4 functionality and workflows. You wouldn't want someone certified on 6.4 making confident assumptions about features that work completely differently now.
Employers absolutely care.
When a company runs Fortinet infrastructure, they need people who can troubleshoot at 2 AM without immediately escalating every single issue to tier-three support or vendor TAC. The NSE4_FGT-7.2 certification signals to hiring managers you've demonstrated that capability through validated examination rather than just claiming experience on your resume. Not gonna lie, it's one of those certs that actually gets you past HR filters and into technical interviews where your knowledge can shine.
Industry recognition matters here too. Fortinet holds significant market share in the next-gen firewall space, so this isn't some niche vendor certification that only applies to twelve companies worldwide. You'll find FortiGate devices deployed in SMBs, enterprises, service providers, government agencies. Basically everywhere security matters and budgets exist.
Quick tangent: I've seen people spend months studying for vendor certs only to discover the vendor barely has market presence in their region. That's not the case here. Fortinet's everywhere, which means your studying actually translates to job opportunities.
What the NSE4_FGT-7.2 certification validates
This exam tests full FortiOS 7.2 knowledge across deployment, configuration, and management domains in ways that surface real understanding versus memorization. You need to understand security policy creation. Sounds simple until you're simultaneously juggling NAT configurations, security profiles, and traffic shaping while maintaining business requirements. The exam validates you can build policies that actually work in production environments without creating security gaps or breaking legitimate traffic flows that users depend on.
Traffic inspection and threat prevention get heavy coverage.
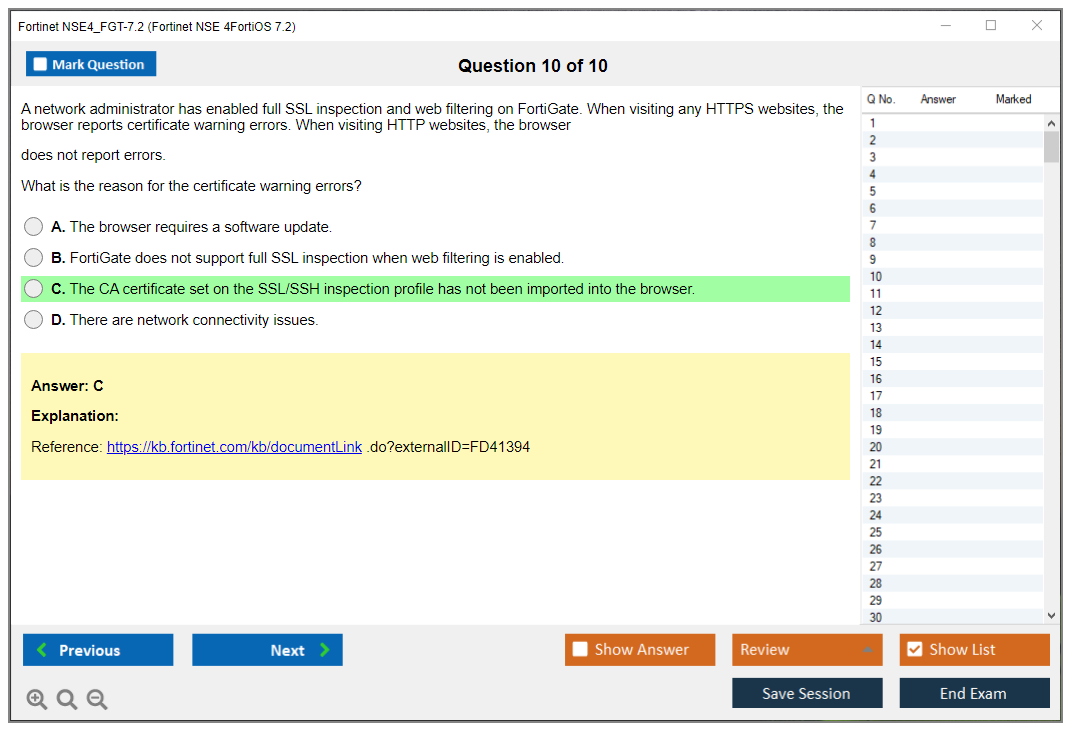
You'll need to know how SSL inspection works (and when it breaks things), when to apply which security profiles without creating bottlenecks, and how to configure IPS signatures without tanking performance on your hardware. This stuff trips up a lot of candidates who memorize commands but don't understand the underlying logic of how traffic flows through the inspection engine.
Network infrastructure integration is huge. Routing protocols, switching features, SD-WAN configurations that modern enterprises depend on. The thing is, FortiGate devices aren't just stateful firewalls anymore. They're core network infrastructure components handling routing, switching, and security simultaneously. You need to know BGP, OSPF, static routing, policy-based routing, and how SD-WAN performance SLAs affect traffic steering decisions in hybrid WAN environments. It's a lot.
VPN implementation covers both IPsec site-to-site and SSL VPN for remote access scenarios that became critical during remote work shifts. You'll configure tunnel parameters, authentication methods, routing over VPNs, and troubleshoot why that tunnel keeps dropping during important user presentations. High availability configurations matter too. Active-passive, active-active, clustering, session synchronization, all that fun stuff that keeps services running when hardware inevitably fails.
Monitoring and troubleshooting capabilities separate people who barely pass from people who excel in real environments. You need FortiAnalyzer integration knowledge, log interpretation skills that go beyond grepping for errors, packet capture analysis, and debug command familiarity that doesn't bring production systems to their knees. Authentication mechanisms span local databases, RADIUS, LDAP, SAML, FSSO. Basically every way users prove their identity in modern heterogeneous networks.
Who should pursue the Fortinet NSE 4 FortiOS 7.2 certification
Network security administrators managing FortiGate deployments? Obviously.
If you're already configuring these devices daily, certification formalizes your knowledge and probably fills gaps you didn't even know existed until someone asks you a specific question. System engineers designing security solutions need this foundation before proposing architectures to clients or management, because recommending solutions you don't deeply understand creates risk.
IT professionals transitioning into cybersecurity find NSE 4 valuable because it combines networking and security concepts rather than treating them as separate domains. You're not just learning firewall rules in isolation. You're understanding how traffic flows through network segments, how attacks actually work against infrastructure, and how to prevent them through layered defenses. That's marketable knowledge that transfers across environments.
Managed security service providers employ tons of NSE 4 certified engineers because they're supporting multiple client environments with different FortiGate models, firmware versions, and configurations simultaneously. You can't afford to fumble around when a client's firewall is blocking critical business traffic during peak hours.
Network engineers expanding into next-gen firewall technologies will find this certification bridges traditional routing and switching knowledge with modern security requirements in ways that make sense. Security analysts benefit from understanding FortiGate capabilities when they're investigating incidents or tuning detection rules to reduce false positives.
Technical consultants advising on Fortinet architecture need this credibility. Clients won't trust your recommendations if you're not certified on the platforms you're proposing. Career changers with networking backgrounds have a realistic path here since the exam builds on fundamental concepts rather than requiring years of security-specific experience in specialized domains.
Career benefits and opportunities after certification
Job prospects improve noticeably.
Roles like FortiGate Administrator, Security Engineer, and Network Security Specialist explicitly list this certification in requirements. Not just as "nice to have" but as actual prerequisites. Some organizations won't even interview candidates without it, particularly Fortinet partners who need certified staff for maintaining partnership tiers and accessing support resources.
Salary advantages exist compared to non-certified peers, though exact numbers vary significantly by market, cost of living, and experience level. What I've seen across multiple markets is that certification helps you negotiate better initial offers and strengthens your case during performance reviews when you're advocating for raises. It's tangible proof you've invested in professional development beyond just showing up and doing assigned tasks.
The certification creates a foundation for advanced NSE tracks that specialize your expertise. You can pursue NSE 5 FortiAnalyzer or NSE 5 FortiManager certifications to specialize in those centralized management platforms, or go deeper with NSE 6 and NSE 7 specializations in areas like SD-WAN architecture, cloud security, or email security. Some ambitious people aim for NSE 8 expert-level credentials, which represent serious mastery and typically require years of dedicated experience.
Credibility when recommending solutions matters more than people realize in client-facing or internal consulting roles. When you're proposing a Fortinet security architecture to stakeholders, being NSE 4 certified means you understand implementation realities, not just vendor marketing materials and feature checklists. You'll also get access to Fortinet partner programs and technical resources that aren't publicly available, which helps with troubleshooting and staying current.
Professional networking opportunities emerge through Fortinet community engagement, user groups, and partner events that happen regionally and virtually. You'll connect with other certified professionals, which leads to knowledge sharing, job opportunities, and career mentoring that wouldn't happen otherwise.
How NSE4_FGT-7.2 fits into overall professional development
Complementary certifications pair well.
A CCNA gives you solid networking fundamentals that make the FortiGate routing content significantly easier to absorb and apply. CompTIA Security+ provides vendor-neutral security concepts that contextualize Fortinet-specific implementations within broader industry frameworks. CISSP adds strategic security thinking if you're aiming for architecture or management roles that require understanding business risk and governance.
The pathway to advanced Fortinet certifications is pretty clear and logical. After NSE 4, you might pursue NSE 5 FortiAnalyzer 7.2 to master log analysis and reporting capabilities, especially if you work in a SOC environment where incident investigation depends on log correlation. NSE 6 FortiMail makes sense for email security specialization. NSE 7 Enterprise Firewall represents expert-level firewall architecture and troubleshooting that separates senior engineers from mid-level practitioners.
Building blocks for specialized domains include NSE 6 certifications in FortiWeb for web application security and bot protection, FortiNAC for network access control in zero-trust environments, or FortiAuthenticator for identity management and SSO implementations. Each addresses specific security challenges you'll encounter in complex environments that go beyond basic perimeter defense.
The ultimate progression for dedicated professionals leads toward NSE 7 and NSE 8 credentials that demand extensive experience and deep technical knowledge. These expert-level certifications aren't for everyone. They require serious commitment and real-world troubleshooting experience that you can't fake. But they represent the highest level of Fortinet expertise you can demonstrate through formal certification.
Vendor-neutral security knowledge transfers across platforms better than people expect when they're worried about vendor lock-in. Understanding firewall policy logic, VPN principles, or threat prevention concepts applies whether you're working with Fortinet, Palo Alto, Cisco, or Check Point equipment. The specific syntax changes, sure, but the foundational concepts remain consistent across implementations.
Practical skills matter more.
You'll apply troubleshooting methodologies, performance optimization techniques, and security best practices daily regardless of which vendor's equipment you're managing in production environments. NSE4_FGT-7.2 teaches you to think systematically about security problems and network traffic flows, not just memorize FortiGate commands or GUI navigation paths.
Certification is a starting point, not a finish line in your professional development. Technology evolves constantly. FortiOS 7.3, 7.4, and future releases will introduce new features and change existing functionality in ways that require adaptation. Continuous learning through hands-on experience, vendor documentation, community forums, and yes, newer certifications keeps your skills relevant and marketable. The NSE4_FGT-7.2 proves you've achieved a specific competency level at a specific point in time, which is valuable. Maintaining that edge requires ongoing effort, but that's true across IT careers generally, not just Fortinet specialization or security roles.
NSE4_FGT-7.2 Exam Details and Requirements
Fortinet NSE4_FGT-7.2 (Fortinet NSE 4 - FortiOS 7.2) overview
The Fortinet NSE4_FGT-7.2 exam proves you can actually run a FortiGate. Real-world stuff. It's about day-to-day FortiOS 7.2 administration, where one wrong policy order or one missed route turns into a weird outage ticket at 2 a.m.
This cert's for people who touch FortiGate configs, troubleshoot traffic, and need to explain why SSL inspection broke someone's banking site. Honestly, it happens more than you'd think, and sometimes it's not even your fault but you're still the one fielding calls. If you're aiming at network security admin, firewall engineer, SOC-ish roles that also manage edge devices, or you're the "network person" at an MSP, the Fortinet NSE 4 FortiOS 7.2 certification fits.
What the certification validates
You're being measured on practical competence. Stuff like FortiOS 7.2 firewall configuration, interfaces and zones, routing, FortiGate security policies and NAT, UTM/security profiles, VPNs, and visibility tooling. Basically everything that can wake you up at night when it breaks. Also the way Fortinet expects you to reason about traffic flow.
Traffic comes in.
Traffic goes out.
Why did it work?
Who should take NSE4_FGT-7.2
If you've deployed FortiGates, migrated policies, tuned web filtering, set up FortiGate VPN (IPsec/SSL) setup, or you've been the person staring at logs going "why is this session denied," you're in the target zone.
New to Fortinet? You can still pass, but you'll need lab time. I mean a lot of lab time, not just clicking around the GUI once or twice. Lots of people underestimate how opinionated FortiOS can be about where settings live and what features interact. CLI shows up.
NSE4_FGT-7.2 exam details
This is the part everyone wants before they open an NSE4_FGT-7.2 study guide and start highlighting things they'll never reread.
Exam format (question types, duration, delivery)
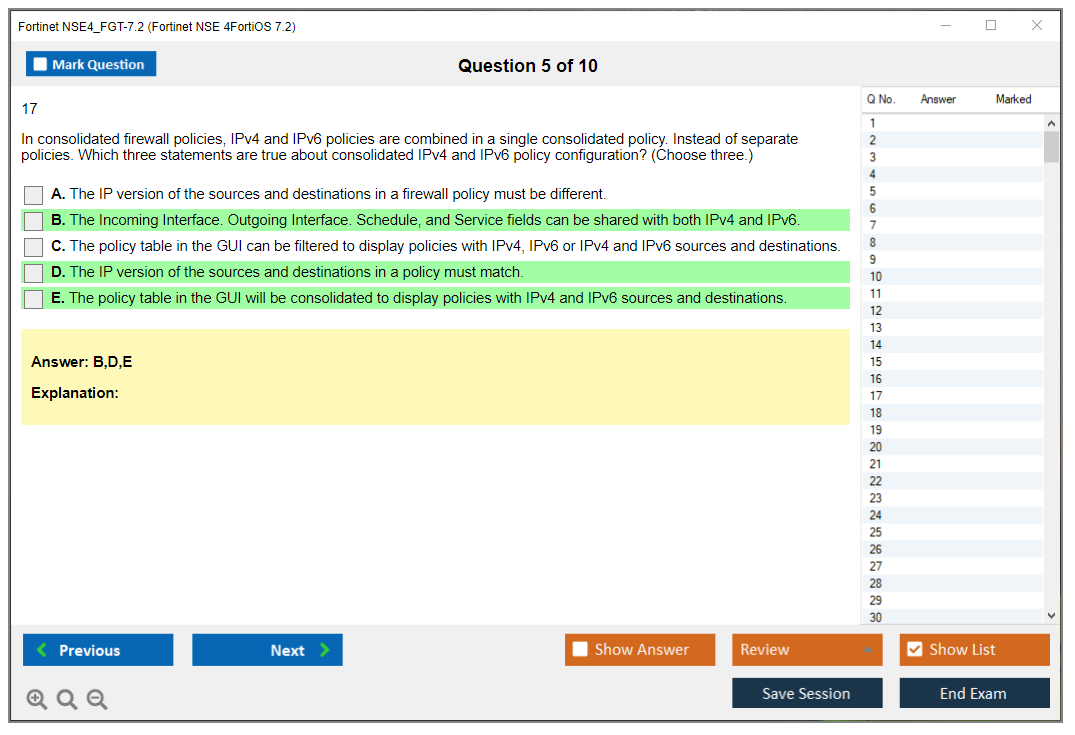
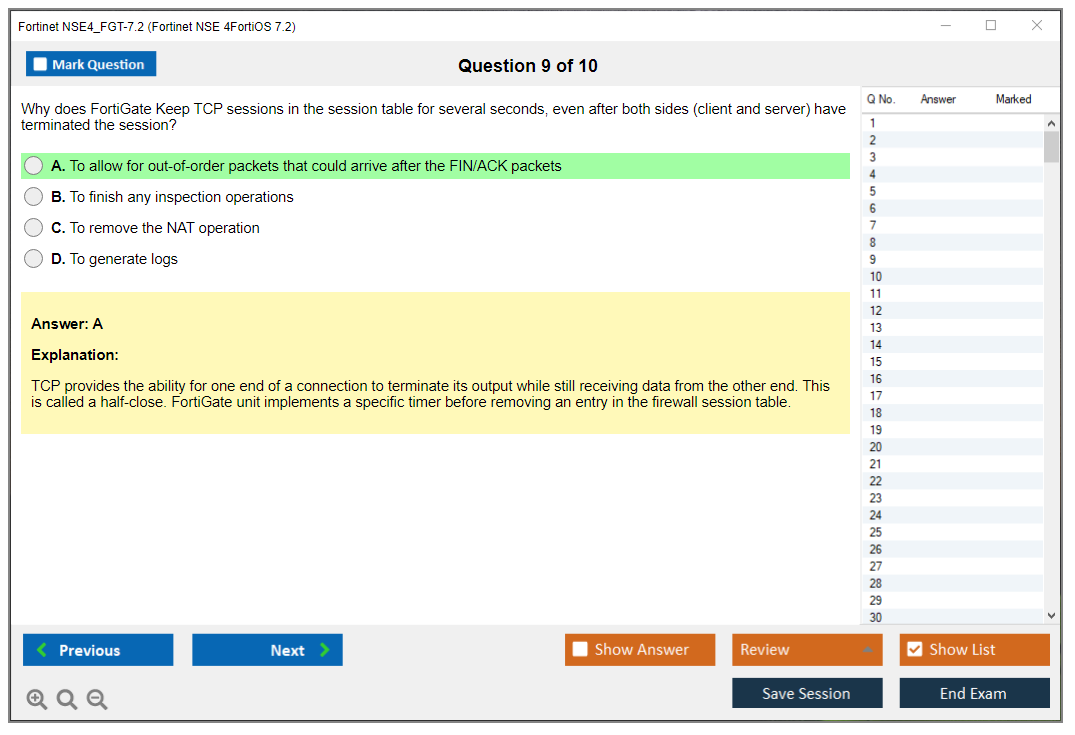
The Fortinet NSE4_FGT-7.2 exam is typically 60 multiple-choice questions. You'll see single-answer multiple choice and multiple-answer multiple choice, and not gonna lie, the multi-answer ones are where people bleed points because there's no partial credit. If it asks for two correct answers and you pick one right plus one wrong, that's a full miss. Feels brutal but that's how they keep the bar high.
Time is 105 minutes (1 hour 45 minutes). Do the math and it's under two minutes a question, which sounds fine until you hit a scenario with a network diagram, a policy table, and a config snippet that looks like a real change request someone pasted into Slack at 4 p.m. on a Friday. Scenario-based questions are common. They require analysis of configurations, routing, NAT, VIPs, and sometimes how inspection profiles change behavior.
You may also see:
- Drag-and-drop questions for ordering steps or matching concepts (these can be fast points if you practiced)
- Simulated configuration questions (these vary by exam version, and you shouldn't bet your whole prep plan on sims existing, but you should prep like they can)
Before you start, you accept a non-disclosure agreement.
Standard NDA stuff.
Also: no breaks. None. Plan your water and caffeine like an adult.
It matters.
Questions are drawn from a validated item bank that maps to the published NSE4_FGT-7.2 exam objectives, so random trivia's less likely than "here's a config, what happens next."
Exam delivery methods and scheduling
Pearson VUE is the official testing partner. That means you can schedule at an authorized testing center worldwide, or do online proctoring from home or office.
Testing center's the old-school route. You show up, empty your pockets, lock your stuff, and they give you scratch materials in a controlled environment. No personal items. No phone. No "I'll just check my notes real quick." The upside is fewer technical surprises and you don't have to worry about your cat jumping on your keyboard mid-exam.
Online proctoring is convenient but pick it only if your setup's clean. You'll need a webcam, mic, stable internet, and a space that won't trigger proctor flags.
Your desk must be boring.
The check-in process includes identity verification with a government-issued photo ID, and they'll usually have you scan the room.
Scheduling's flexible, with appointments most days, but don't assume same-day availability during busy periods. December and January can be a nightmare because everyone's trying to hit year-end cert goals. Rescheduling and cancellation policies are typically 24 to 48 hours notice, depending on region and the exact Pearson VUE rules at the time, so always read the confirmation email like it's a change window notice.
Exam cost
The standard exam fee is typically $400 USD, though region and currency can shift the number. There's usually no extra registration fee beyond the voucher itself.
Where people get surprised is the prep spend. Like, they budget for the exam but forget everything else. Official instructor-led FortiGate 7.2 training can run $2,000 to $3,500 depending on whether it's live online, in-person, bundled, whatever. Self-study can be cheaper, but it's not free either. Budget $100 to $300 for a decent NSE4_FGT-7.2 practice test, a good study guide, and lab resources.
Retakes cost the full exam fee each time.
No discount by default.
No magic "second try coupon" unless your employer or a promo covers it. There's typically no limit on attempts, but waiting periods can apply, so don't plan on brute forcing it weekly.
Employer reimbursement's common for this cert, especially if your company's a Fortinet shop. I mean, if you're keeping the firewall estate healthy, it's a reasonable training budget line item.
ROI is real. For many people, the NSE 4 FortiGate certification cost pays for itself in 6 to 12 months via a title bump, better consulting rates, or simply being the person who gets picked for security projects instead of generic network chores.
Passing score
The NSE4_FGT-7.2 passing score is commonly described as 70%, so roughly 42 out of 60. Fortinet uses scaled scoring to keep different exam forms consistent, so don't get too hung up on exact raw math, but that 70% target's the number most candidates plan around.
You get a score report immediately for electronic exams. Pass/fail plus a percentage score, and typically domain-level feedback that shows where you were strong or weak. No question-by-question breakdown. No "review mode." There's also no official curve where they adjust because the exam was "hard that day." Minimum competency stays the same across administrations.
Difficulty level (what makes it challenging)
Intermediate-to-advanced. That's the honest label.
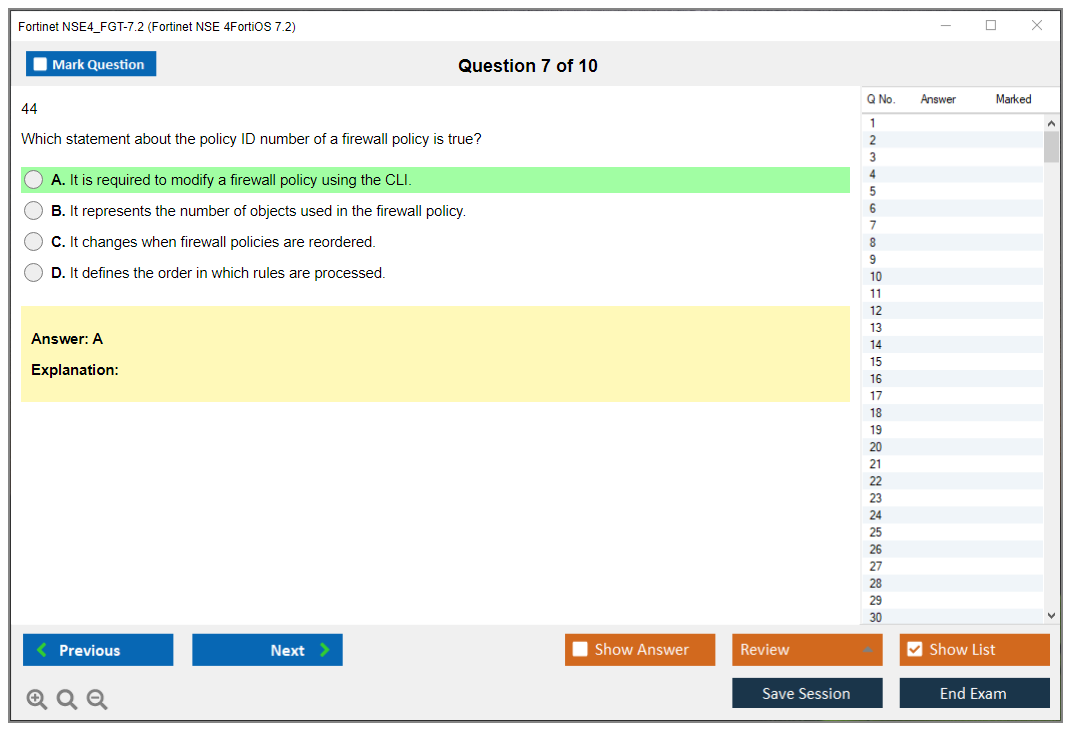
It's challenging because it's not only memorization. You need practical reasoning about traffic flow, routing decisions, policy match order, inspection behavior, and the way FortiOS features interact across GUI and CLI, which can feel like learning two languages that share vocabulary but not grammar. Scenario-based questions force troubleshooting thinking, not "what does this acronym mean."
FortiOS 7.2 differences vs older versions can trip you up too. People bring habits from 6.x or early 7.x, then get caught by changed defaults, renamed options, or different UI paths. I've seen folks with years of experience miss questions because they assumed behavior hadn't changed. Another pain point: integration topics like SD-WAN, SSL inspection, and Security Fabric concepts require you to connect dots across features, not treat them like separate chapters.
Common pitfalls:
- Missing "except" or "not" in the question (brutal, and it'll haunt you)
- Rushing scenario questions, then choosing an answer that would be true in a different topology
- Underestimating CLI syntax and output interpretation
Difficulty compared to other vendor certs? Similar ballpark to CCNP Security or PCNSE, especially if you're new to Fortinet's way of doing things. First-attempt pass rates get guessed around 60 to 70% for well-prepared candidates, and that feels believable.
NSE4_FGT-7.2 exam objectives (FortiOS 7.2)
Fortinet publishes objective domains and you should read them.
Not optional.
The exam sticks close to them, and a good NSE4_FGT-7.2 study guide should map directly to each domain.
System and network settings
Interfaces, VLANs, zones, addressing, DNS, admin access, and device basics. Expect questions about what happens when management access is missing, or what setting controls which service can hit an interface.
Firewall policies, NAT, and security profiles
This is the core. Policy match logic, order, implicit deny, central NAT vs policy NAT concepts, VIPs, and profile attachment. Most of the exam lives here. Web filter, AV, IPS, application control, SSL inspection mode choices.
Know the defaults.
Authentication and user access
Local users, groups, remote auth basics, and how policies reference identity. Also captive portal-ish behavior can appear.
Routing (static/dynamic) and SD-WAN
Static routes, policy routes, and dynamic routing basics depending on the objective list version. FortiGate routing and SD-WAN questions often look simple but hide a "which route wins" detail, or an SLA/health-check behavior detail that changes path selection.
VPNs (IPsec and SSL VPN)
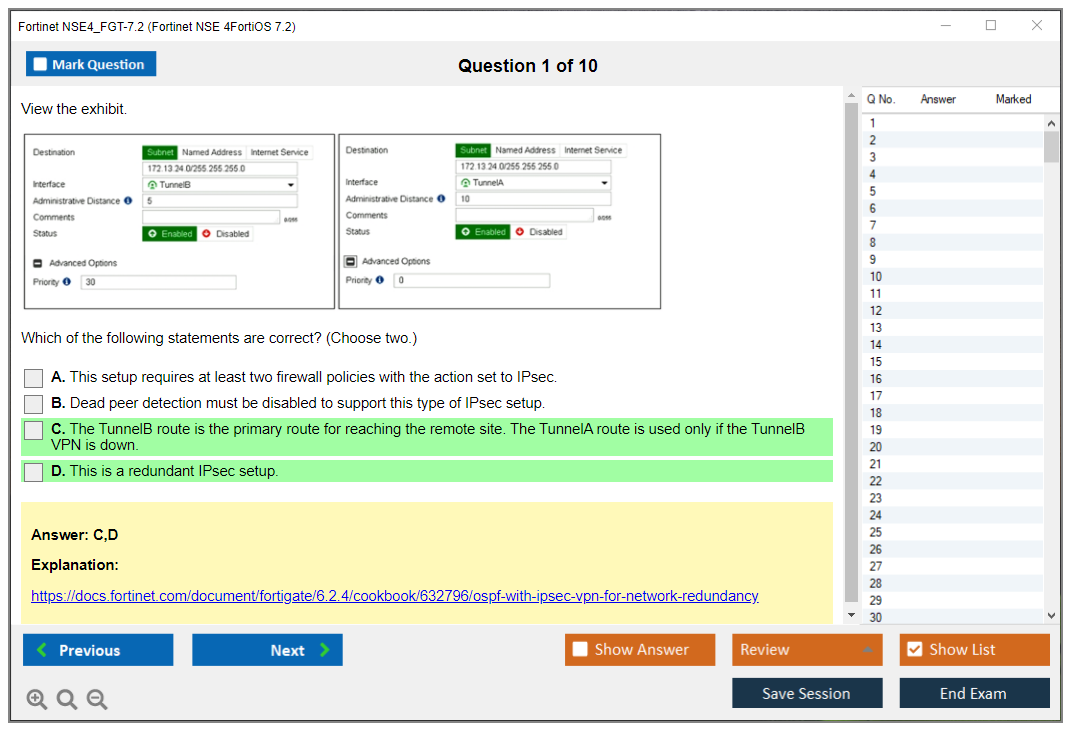
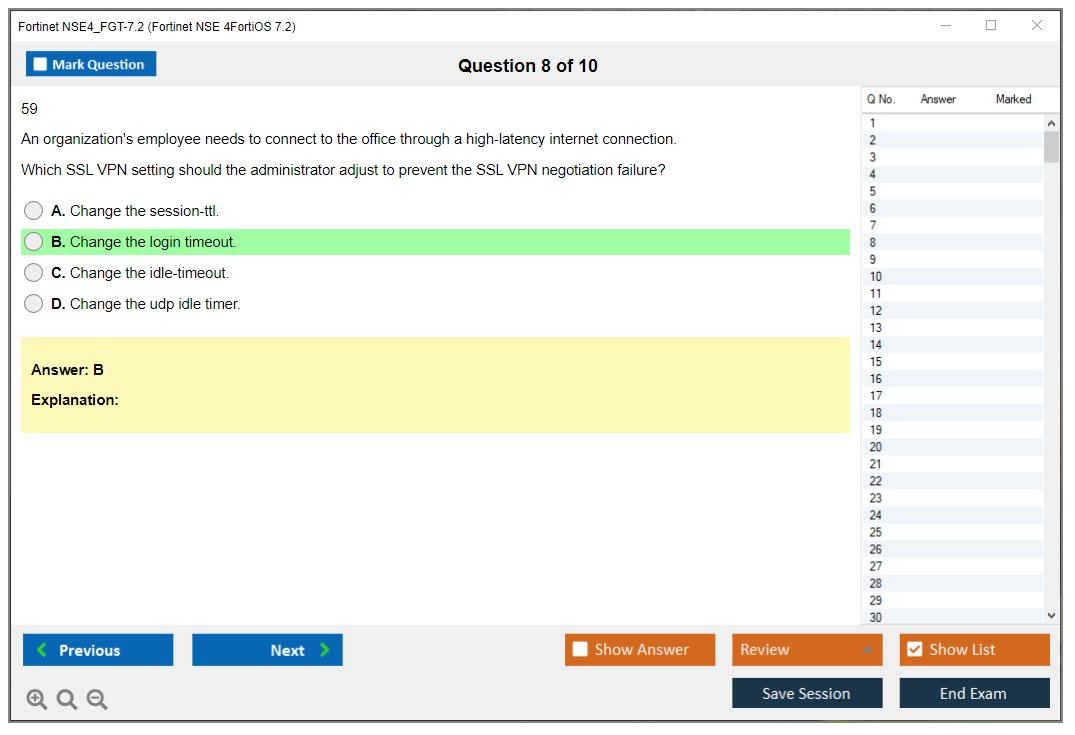
Site-to-site IPsec concepts, phase1/phase2 parameters at a high level, route-based VPN behavior, and SSL VPN portal vs tunnel mode basics. Expect troubleshooting style prompts like "users can connect but can't reach subnets," which is usually routes, policies, or split tunnel settings. The thing is, it could also be firewall zones or interface trust levels, so you've gotta think through the whole path.
High availability (HA) and redundancy
Cluster basics, failover behavior, and what syncs.
Also what breaks sync.
It happens.
Logging, monitoring, and troubleshooting (FortiAnalyzer/FortiGate tools)
Logs, session tables, flow traces, debug basics, and visibility. You may see references to FortiAnalyzer and logging monitoring and how to confirm a security profile action vs a routing issue.
Prerequisites and recommended experience
Prerequisites (official vs. recommended)
Officially, Fortinet exams often don't require a prerequisite cert to sit the test. Realistically, you want hands-on time. If you're reading only PDFs and never touched policy order, you're gambling.
Hands-on skills checklist (FortiGate/FortiOS 7.2)
You should be able to build and verify: interfaces/VLANs, basic policies, NAT/VIPs, attach profiles, basic SD-WAN rules, at least one working IPsec tunnel, and basic log-based troubleshooting. Also be comfortable reading CLI output without panicking.
Best study materials for NSE4_FGT-7.2
Official training (Fortinet Training Institute / courseware)
If you can get official courseware through the Fortinet training portal or employer access, do it. It fits with objectives and uses Fortinet's language, which matters on test day.
Documentation to prioritize (FortiOS 7.2 admin guides, cookbooks)
Docs beat random blog posts when you're trying to confirm behavior. Fortinet cookbooks are good for "here's how it's normally built," and admin guides help when you need the exact setting name and its effect.
Actually, I'd argue the cookbooks are more useful than the guides at first because they walk you through common deployments step by step, which helps when you're trying to understand why something's built a certain way versus just what each knob does. Once you're comfortable with the flow, then the admin guides become your reference for the edge cases and weird integrations.
Labs and home practice setup (VMs, hardware, cloud)
A home lab's where the cert stops being abstract and starts feeling real. FortiGate VM, a couple of VLANs, a fake WAN, a fake LAN, and you can rehearse policies, routing, and VPN. If you have spare hardware, great, but if not, VMs can still teach you 80% of what the exam asks, and that's usually enough.
NSE4_FGT-7.2 practice tests and exam prep strategy
Practice tests (how to choose quality sources)
Pick practice questions that explain why an answer's correct, not just "A is right." Avoid brain-dump vibes because they'll teach you patterns but not concepts. A decent NSE4_FGT-7.2 practice test should reference objectives and force you to think through scenarios, especially around NAT, routing decisions, and inspection behavior.
Topic-by-topic revision plan (2-6 week schedules)
If you have FortiGate experience, two to three weeks of focused review can work: read objectives, patch weak domains, do labs, then practice tests. If you're newer, take four to six weeks and build configs from scratch repeatedly, because muscle memory matters when a question shows a partial config and asks what's missing.
Common mistakes to avoid on exam day
Don't speed-read. Don't assume version behavior from older FortiOS. I mean, that's how you miss the easiest questions because you're confident about something that changed two releases ago. And don't second-guess every answer because you saw someone on a forum claim "the exam is tricky." It's tricky in predictable ways, mostly around qualifiers and traffic flow logic.
Exam results and certification issuance
You get immediate pass/fail after submitting.
If you pass, the official digital certificate typically shows up in the Fortinet training portal within about 5 business days. You also get a digital badge you can add to LinkedIn and email signatures, plus a verification number for employers.
No physical certificate's mailed unless you specifically request it, and transcript access is available through Pearson VUE and your Fortinet training account. Directory listing as a certified professional's usually optional.
Renewal / recertification for Fortinet NSE 4
Renewal requirements and validity period (what to verify)
Fortinet programs change names and rules over time, so verify the current validity period and the official NSE4_FGT-7.2 renewal requirement inside your Fortinet account and the certification policy page.
Don't trust old Reddit threads.
Policies drift.
Recertification options (retake vs. higher-level path)
Often the clean options are retaking the current exam version or earning a higher-level Fortinet cert that renews lower ones, depending on the program rules at the time. If your job's already pushing you into more design and multi-site work, the higher-level path can be smarter than repeating the same admin exam every cycle.
Keeping skills current with FortiOS releases
Stay current by reading release notes for the features you actually use: SD-WAN behavior, SSL inspection changes, logging defaults, and any policy/NAT UI shifts. A little monthly maintenance beats a panic cram later.
FAQs (quick answers)
Cost, passing score, and difficulty recap
How much does the NSE4_FGT-7.2 exam cost? Typically $400 USD, region-dependent.
What's the passing score for NSE4_FGT-7.2? Commonly 70% (about 42/60), with scaled scoring.
How hard's the Fortinet NSE 4 (FortiOS 7.2) exam? Intermediate-to-advanced, especially if you lack hands-on troubleshooting.
Best last-minute study materials and practice tests
Best study materials for NSE4_FGT-7.2? Official courseware plus Fortinet docs plus a lab you can break and fix. Add a reputable practice test that explains answers, not just scores.
Objectives and prerequisites summary
What are the NSE4_FGT-7.2 exam objectives? FortiGate system setup, policies/NAT/security profiles, auth, routing/SD-WAN, VPNs, HA, and logging/troubleshooting. Prereqs aren't usually enforced, but real FortiGate experience is what makes the exam feel fair instead of brutal.
NSE4_FGT-7.2 Exam Objectives and Domains
NSE4_FGT-7.2 exam objectives and domains
The Fortinet NSE4_FGT-7.2 exam is basically the gold standard when you're trying to prove you've got real chops deploying and managing FortiGate firewalls that run FortiOS 7.2. Here's the thing: it's regurgitating features from memory or whatever. The exam actually tests whether you can configure interfaces, write firewall policies that work, troubleshoot VPNs when they're acting up, and keep networks humming along without constant fires to put out. Every domain builds on what came before, so understanding how everything connects matters way more than just cramming CLI commands the night before.
Before we dig into the seven domains, let's be real. What does the Fortinet NSE 4 FortiOS 7.2 certification actually validate? You've gotta demonstrate hands-on skills with FortiOS 7.2's new features. Stuff like improved SD-WAN algorithms, updated security profiles, better HA synchronization, and refined VPN options that actually make sense now. The exam isn't theoretical. Most questions drop you into scenarios where you troubleshoot a misconfigured policy or figure out why an IPsec tunnel won't come up.
Real talk here.
If you've worked with FortiGate boxes before, you already know that FortiOS 7.2 refined a ton of the UI and CLI workflows compared to 6.x releases. The NSE4_FGT-7.2 exam objectives reflect those changes, especially around SD-WAN health checks and security profile groups. I mean, if you're still on 6.4 or earlier firmware, spend time in the 7.2 admin guide before you take this test. My buddy spent three weeks reviewing documentation he thought was "close enough" and bombed the first attempt because the interface behavior changed between minor versions.
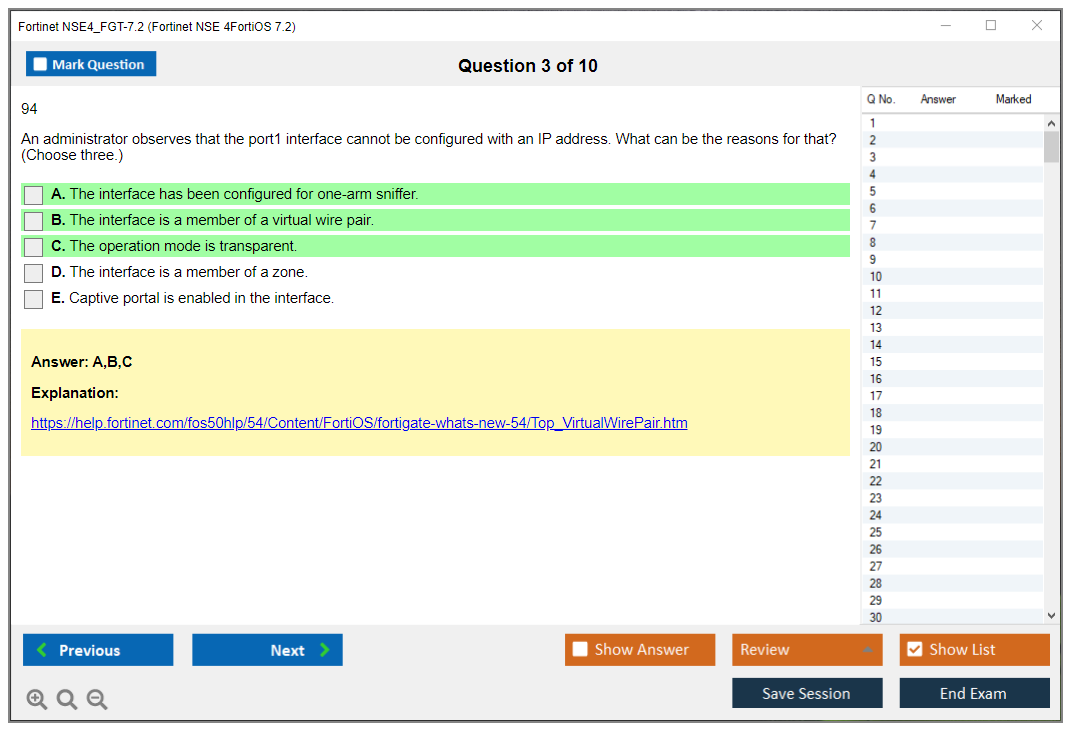
System and network settings configuration
This domain covers the basics. But it's not trivial. Initial FortiGate setup means understanding the factory default IP, how to connect via console, and setting up your management interfaces so you don't lock yourself out. Been there, not fun. You'll configure physical interfaces, VLANs, aggregate (LACP) interfaces, loopback interfaces for routing protocols, and various tunnel interfaces for VPNs or GRE. Each interface type has quirks. VLAN tagging on trunks, aggregate interface distribution algorithms, tunnel MTU considerations.
System settings are straightforward but critical: hostname, time zone, NTP servers (so your logs don't lie about timestamps), DNS servers for FQDN resolution. Administrative access configuration is where people trip up. Restricting HTTPS/SSH/PING per interface, setting up trusted hosts, and making sure you don't expose management to the internet by accident.
Administrator accounts? They've got privilege levels. Super_admin can do anything, prof_admin handles most configs but can't touch some global settings, and read-only accounts are for monitoring. You also need to know FortiOS firmware upgrade procedures. Uploading images via GUI or CLI, checking compatibility, and rolling back if something breaks. Configuration backup and restore operations cover local storage, USB drives, TFTP, FTP. Basically every way you might save or load a config in a disaster recovery scenario.
HA heartbeat interface configuration is part of this domain too, even though HA gets its own section later. You'll monitor system resources like CPU, memory, disk usage, and session table utilization to spot performance bottlenecks before they become problems that wake you up at 3 AM. Device registration and licensing (FortiCare support contracts, FortiGuard security subscriptions) are tested because without valid licenses, your AV and IPS signatures go stale fast.
Understanding what's new in FortiOS 7.2 compared to previous versions is essential. Fortinet loves asking "which feature was introduced in 7.2?" questions. Spend time in the release notes.
Firewall policies, NAT, and security profiles
This is the heart of the NSE4_FGT-7.2 exam. Firewall policy creation, ordering, and packet flow logic determine whether traffic gets permitted or denied. FortiOS processes policies top-down. First match wins. You need to understand policy-based routing, multiple routing tables, and how route lookups interact with policy decisions.
Source NAT (SNAT)? For outbound internet access, it's usually straightforward. Either central SNAT on the outbound interface or IP pools. Destination NAT (DNAT) for inbound service publishing uses Virtual IP (VIP) objects. You map a public IP to an internal server, then reference that VIP in a policy. Central SNAT versus policy-based NAT is a common exam scenario. When do you use which?
Security profiles are where FortiGate shines: antivirus, web filtering, application control, IPS, DNS filtering. Antivirus has proxy-based and flow-based scanning modes with different performance and detection trade-offs. Proxy-based inspects the full file but adds latency. Flow-based is faster but less thorough. Web filtering uses categories, quotas, and custom URL lists. Application control relies on signatures to identify apps regardless of port. You can block Facebook even if users tunnel it over HTTPS.
IPS signatures have severity levels and actions (block, monitor, quarantine). SSL/TLS inspection is a huge topic. Certificate inspection for server cert validation, deep inspection for full decryption (requires installing a CA cert on clients), or no inspection when privacy matters. Security profile groups bundle multiple profiles so you don't attach them individually to every policy.
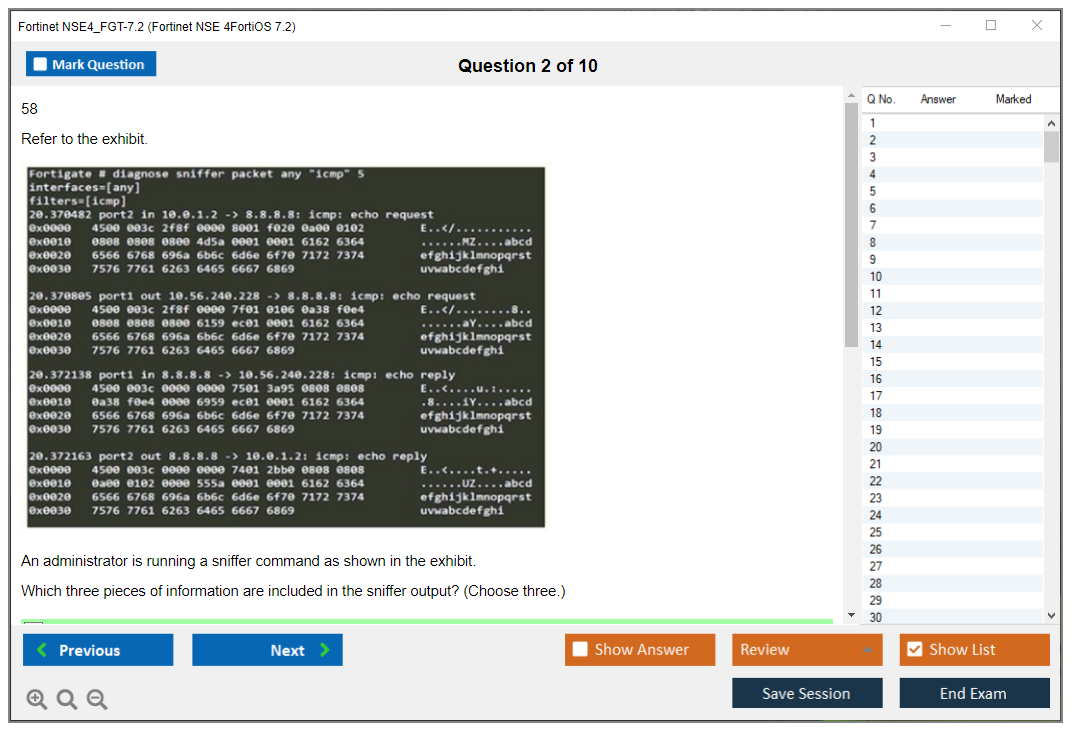
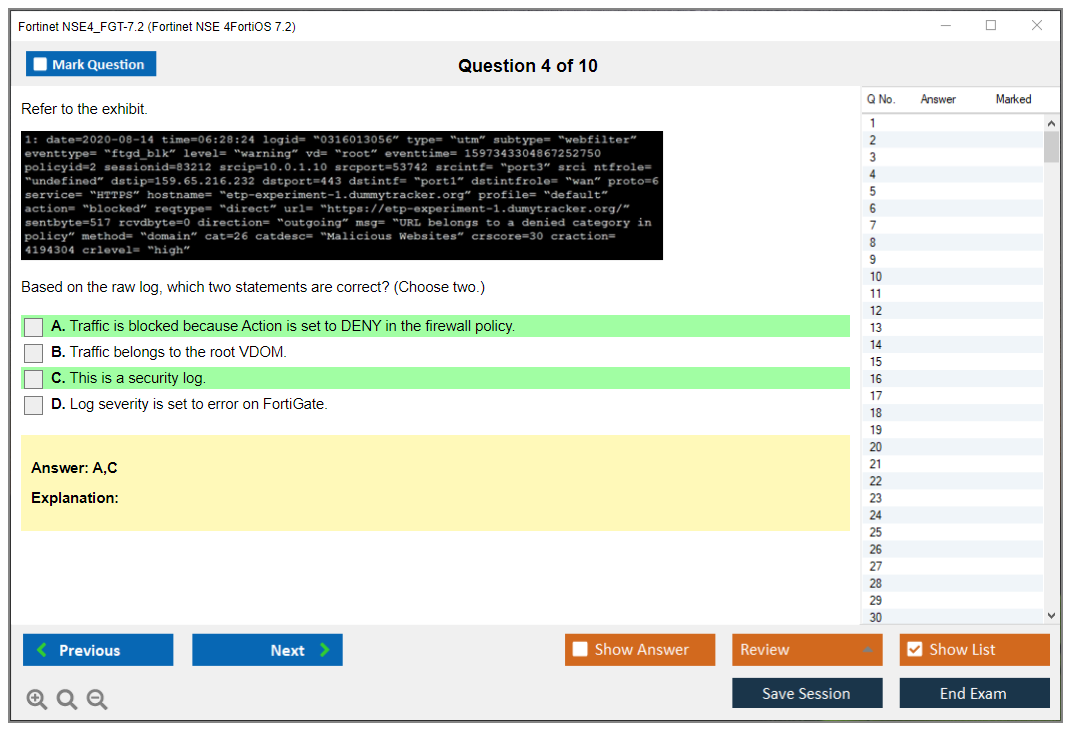
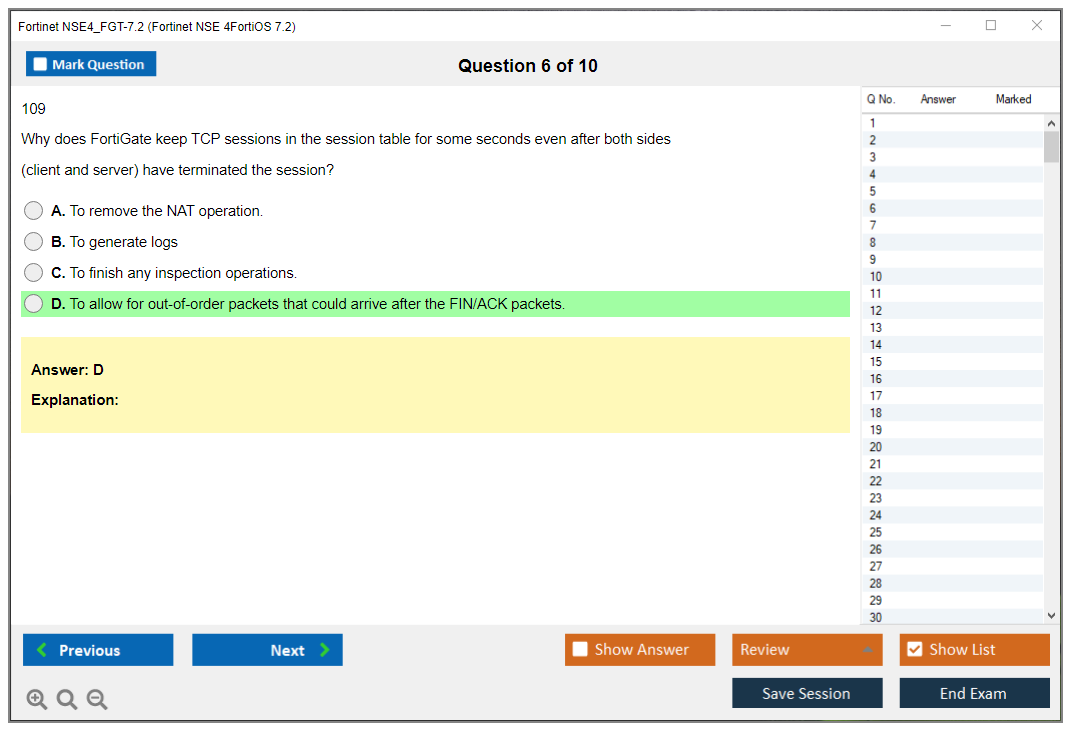
DoS policies catch floods. Anomaly protection catches weird traffic patterns. Policy consolidation helps when you've got 500 rules and performance tanks. Session helpers and ALG functionality handle protocols like FTP, SIP, H.323 that use dynamic ports. Troubleshooting with packet capture and 'diagnose debug flow' is key. Exam scenarios often give you broken policies and ask what's wrong.
If you want realistic practice, the NSE4_FGT-7.2 Practice Exam Questions Pack at $36.99 covers these policy scenarios in depth, including NAT edge cases and security profile misconfigurations.
Authentication and user identity management
Local user database? It's the simplest option. Users stored directly on FortiGate. But most enterprises use LDAP, RADIUS, or Active Directory. LDAP server integration pulls user info from AD or other directories. RADIUS handles network access control, often for wireless or VPN. TACACS+ is for administrative access with command authorization.
FSSO (Fortinet Single Sign-On) integrates with Active Directory so firewall policies can reference user groups instead of IPs, which makes way more sense for managing access in a dynamic environment where users move around and work remotely all the time. FSSO agent deployment models include DC agent (installed on domain controller), polling mode (agent queries DC logs), and advanced mode with collector agent. SAML authentication works for web-based services. Users authenticate via an IdP, then access resources through FortiGate.
Two-factor authentication with FortiToken adds a second factor (something you have) to passwords. User groups simplify policy management. Firewall user authentication in policies means users must authenticate before traffic is allowed. Guest user management and captive portal deployment are common for WiFi hotspots or contractor access.
Identity-based policies are more flexible than IP-based policies but require authentication infrastructure. Authentication timeouts and session management prevent stale sessions. Troubleshooting authentication failures involves checking LDAP bind credentials, FSSO connectivity, and debug auth logs. Certificate-based authentication for VPN and admin access uses client certs instead of passwords.
Routing fundamentals and SD-WAN implementation
Static routing is basic. But you need to understand administrative distance, which route wins when multiple paths exist. Policy-based routing steers traffic based on source, destination, or service instead of just destination. Dynamic routing protocols (RIP, OSPF, BGP) are all tested. RIP is old, rarely used.
OSPF area types (backbone, stub, NSSA), neighbor relationships (adjacency states), and route redistribution between protocols are core knowledge. BGP attributes like AS path, local preference, and MED influence path selection. BGP peering (eBGP versus iBGP) and route maps for filtering are common scenarios.
SD-WAN is huge in FortiOS 7.2. SD-WAN members are your WAN links: MPLS, internet, LTE. Health checks measure latency, jitter, and packet loss. Performance SLA configuration defines acceptable thresholds. SD-WAN rules steer traffic based on application, destination, and link quality. Load balancing algorithms include spillover (use primary until full), session-based (distribute per session), volume-based (balance by bandwidth), and source-IP hashing.
Link quality measurement triggers failover when SLA thresholds are breached. Integration with FortiManager centralizes SD-WAN orchestration across multiple sites. Troubleshooting routing issues means analyzing the routing table, running traceroute, and checking interface status. Multicast routing and IGMP snooping come up occasionally.
For those moving from earlier versions, the NSE4_FGT-7.0 or NSE4_FGT-6.4 exams covered similar concepts, but 7.2's SD-WAN enhancements are more advanced.
VPN technologies: IPsec and SSL VPN
IPsec VPN fundamentals. IKE phase 1 (establish secure channel) and phase 2 (negotiate encryption for user traffic). You need to know encryption algorithms (AES, 3DES) and authentication methods (PSK, certificates). Site-to-site IPsec VPN comes in route-based (uses tunnel interface) and policy-based (no interface, policy defines traffic) flavors. Route-based is more flexible for dynamic routing.
Dialup/remote access IPsec VPN serves mobile users. IPsec with dynamic IP addresses uses DynDNS or aggressive mode. VPN tunnel monitoring and dead peer detection (DPD) detect dead tunnels and trigger reconnection. IPsec VPN redundancy uses multiple tunnels with failover.
SSL VPN? It's easier for end users. No IPsec client required. Web mode provides clientless access to web apps via a portal. Tunnel mode with FortiClient gives full network access. SSL VPN user portals can be customized per group. Bookmarks are shortcuts to internal web apps. Split tunneling sends only corporate traffic through the VPN. Full tunneling routes everything.
SSL VPN authentication supports local users, RADIUS, LDAP, and certificates. VPN traffic inspection means security profiles scan VPN traffic just like regular traffic. Certificate management (importing CAs, creating CSRs, managing certificate chains) is necessary. Troubleshooting VPN connectivity involves separating phase 1 failures (authentication, proposals) from phase 2 failures (selectors, routing). Log analysis with 'diag vpn ike log' and 'diag vpn tunnel list' is key. Hardware acceleration offloads crypto to dedicated chips for better performance.
High availability and redundancy
FortiGate HA ensures uptime. HA modes are Active-Passive (one device forwards traffic, other is standby) and Active-Active (both forward traffic, often with virtual clustering). HA cluster configuration requires matching firmware, similar hardware, and proper cabling. HA heartbeat interfaces carry cluster communication. Dedicated HA links are best practice.
HA synchronization covers configuration (so both units match), session (so failover doesn't break connections), and file (AV signatures, certificates). Device priority and override settings determine which unit becomes master. HA monitoring detects failures. Interface monitoring fails over if a critical link goes down. Link monitoring can track physical ports or IP targets.
Failover testing validates the cluster works. Virtual clustering in Active-Active mode distributes load by VLAN or policy. FGCP (FortiGate Clustering Protocol) is standard. FGSP (FortiGate Session Life Support Protocol) syncs sessions without full HA. HA with VRRP integration allows FortiGate clusters to work with third-party routers. Chassis clustering on high-end models combines multiple chassis.
Troubleshooting HA issues? Split-brain scenarios (both units think they're master), synchronization problems (config out of sync), and heartbeat failures. Configuration backup before HA changes is critical. Recovery from a failed HA setup is painful.
Logging, monitoring, and troubleshooting
FortiGate logging architecture includes traffic logs (allowed/denied sessions), event logs (admin actions, HA events), security logs (AV/IPS/web filter hits), and system logs (hardware, routing). Local logging stores logs on the FortiGate disk with configurable quotas. Remote logging to FortiAnalyzer centralizes logs from multiple devices. Syslog server integration sends logs to third-party SIEM systems. Log filtering reduces noise. Log only what you need.
FortiView dashboards provide real-time visibility into traffic by source, destination, application, and threat. Security rating and posture monitoring show your security effectiveness. FortiAnalyzer integration requires configuring log forwarding and ensuring network connectivity. Report generation for compliance (PCI, HIPAA) and security analysis is common.
Packet capture ('diagnose sniffer packet') captures raw packets for deep troubleshooting. Debug commands like 'diagnose debug flow' trace packet processing through policies, NAT, and routing. Session table analysis shows active connections, useful for spotting connection leaks or session exhaustion. Performance monitoring via dashboard widgets tracks CPU, memory, disk, and session counts.
Important CLI commands include 'get system status', 'get system performance status', 'diagnose sys top', 'get router info routing-table', and 'execute ping'. Firmware upgrade troubleshooting covers boot loops, corrupted images, and rollback procedures. Support bundles ('execute backup full-config') collect logs and config for Fortinet TAC cases.
Common troubleshooting scenarios: connectivity issues (check routing, policies, NAT), policy misconfigurations (wrong order, missing NAT), VPN failures (phase 1 versus phase 2, routing), and performance problems (CPU, session table full).
Exam format and cost
The Fortinet NSE4_FGT-7.2 exam typically has 60 multiple-choice questions. You get 105 minutes. Exam cost is around $400 USD, though Pearson VUE pricing varies by region. Passing score is 70% (42 correct answers), but that's tight. You can't afford many mistakes. The exam is proctored at Pearson VUE centers or via online proctoring.
Difficulty level? It's tougher than the old NSE 4 exams. Fortinet added more scenario-based questions where you analyze logs, configs, or debug output. Rote memorization won't cut it. You need to understand why a policy works, not just how to create one.
Prerequisites and recommended experience
Official prerequisites? None. But realistically, you should have six months of FortiGate experience and solid networking fundamentals: subnetting, routing, NAT, VPNs. Hands-on skills checklist includes configuring interfaces, writing policies, setting up VPNs, troubleshooting with CLI. If you've never touched a FortiGate, start with the NSE 4 FortiGate certification track from earlier versions to build foundational skills.
Best study materials for NSE4_FGT-7.2
Official training from Fortinet Training Institute is pricey but thorough. Instructor-led or self-paced. The FortiOS 7.2 Administration Guide is your bible, over 1000 pages of config examples. Cookbooks and technical notes cover specific scenarios like OSPF over IPsec or SD-WAN with dual ISPs. Labs are necessary. GNS3 or EVE-NG with FortiGate VM images let you practice at home. Hardware labs are better but expensive.
For broader Fortinet skills, check out the FortiAnalyzer 5.4 Specialist or FortiManager 5.4 Specialist exams. They complement FortiGate knowledge.
Practice tests and exam prep strategy
Quality NSE4_FGT-7.2 practice tests simulate exam questions and identify weak areas. Avoid brain dumps. They're outdated and don't teach you troubleshooting. Topic-by-topic revision: spend week one on system config and policies, week two on routing and SD-WAN, week three on VPNs and HA, week four on logging and troubleshooting. Common mistakes? Rushing through questions, not reading logs carefully, and forgetting that first match wins for policies.
Renewal and recertification for Fortinet NSE 4
The Fortinet NSE 4 FortiOS 7.2 certification is valid for two years. Renewal requires retaking the current exam. There's no "lite" recertification option. Alternatively, pass a higher-level exam like NSE 7 Enterprise Firewall 7.0 to keep your NSE 4 active. Keeping skills current means staying on top of FortiOS releases. Version 7.4
Prerequisites and Recommended Experience for NSE4_FGT-7.2
Fortinet NSE4_FGT-7.2 (Fortinet NSE 4, FortiOS 7.2) overview
The Fortinet NSE4_FGT-7.2 exam is Fortinet's core FortiGate admin certification for FortiOS 7.2, and honestly, it's their way of verifying "yep, this person won't freak out when asked to configure and troubleshoot a FortiGate in production." This isn't some "security awareness" participation trophy. It's actual admin-level thinking, loaded with "what'd you do in this situation" scenarios.
Here's the thing. If you've been living exclusively in switch land, this exam feels like you're jumping into deep water. If you've already been managing firewalls, VPNs, and routing changes during those fun 3 AM maintenance windows, it's totally doable.
What the certification validates
You're proving you can handle legitimate FortiOS 7.2 work: FortiOS 7.2 firewall configuration, FortiGate security policies and NAT, identity management, VPNs, logging, and the classic "why is this traffic just.. dying" troubleshooting. You're also demonstrating you understand how FortiGate fits into an organization's infrastructure, not just how to work through the GUI.
Short version? Configure. Validate. Fix.
Who should take NSE4_FGT-7.2
Network and security admins. MSP engineers. People who've become the designated "firewall person" on-call. Also anyone who keeps getting dragged into FortiGate tickets and wants that to translate into a raise instead of just.. more tickets.
I mean, if you've never touched FortiGate, you can still pass, but you'll spend significantly longer building context because FortiOS has its own logic and UI patterns, and the exam expects you're already thinking like a FortiGate admin.
NSE4_FGT-7.2 exam details
Exam format (question types, duration, delivery)
Fortinet exams get delivered through Pearson VUE typically, and you're looking at a timed, proctored multiple-choice format. Often with scenario-based questions thrown in. Exact numbers shift, so verify the exam page before you schedule. Fortinet updates exam metadata more frequently than most people realize.
Timed. Quiet room. No second monitor allowed.
Exam cost
People always ask: How much does the NSE4_FGT-7.2 exam cost? Fortinet's exam pricing bounces around by region and currency, and sometimes your employer has vouchers through a partner program, so don't treat a random blog number as gospel. Check the Pearson VUE listing for the current NSE 4 FortiGate certification cost the week you're planning to book.
Also? Budget for a retake. Just, mentally prepare for that.
Passing score
Another common question: What is the passing score for NSE4_FGT-7.2? Fortinet typically doesn't publish a fixed "700/1000" type number for every version in a way you can rely on, and scoring can be scaled. If you see a specific NSE4_FGT-7.2 passing score quoted somewhere, treat it as "maybe outdated" unless it's straight from Fortinet's current exam page.
So what do you actually do with that? Aim for mastery, not threshold hunting. That mindset saves you, honestly.
Difficulty level (what makes it challenging)
How hard is the Fortinet NSE 4 (FortiOS 7.2) exam? It's medium-to-hard if you're brand new to FortiOS, and medium if you've actually configured production FortiGates. The challenge is the mixture: routing, security profiles, VPN behavior, authentication, and troubleshooting. You can't just memorize screenshots. You need cause-and-effect thinking. Like what changes when you enable central NAT, or how policy order and objects interact, or which logs you check first when a user screams "VPN is down."
One more thing? Fortinet loves "best answer" questions. Two options look right. One is more right.
NSE4_FGT-7.2 exam objectives (FortiOS 7.2)
If you're using an NSE4_FGT-7.2 study guide, keep it mapped to the official NSE4_FGT-7.2 exam objectives, because random third-party outlines often miss logging, authentication edge cases, or SD-WAN behavior.
System and network settings
Interfaces, addressing, admin access, and the foundational stuff that makes the box reachable and functional. DNS, DHCP, NTP, and management settings appear here. Yes, you should understand why time drift destroys certificates and VPNs.
Firewall policies, NAT, and security profiles
This is the heart. FortiGate security policies and NAT includes policy matching logic, objects, services, schedules, and NAT modes. Security profiles bring in AV, web filtering, IPS, SSL inspection basics, and profile attachment to policies.
Policy order matters. A lot.
Authentication and user access
Local users, groups, and integration with directory services. Expect concepts around who's allowed, how they're identified, and what happens when auth fails. You should be comfortable with LDAP, RADIUS, and typical Active Directory environments.
Routing (static/dynamic) and SD-WAN
Static routing is the minimum. Dynamic routing is a nice-to-have, and it appears because real networks aren't one flat subnet. FortiGate routing and SD-WAN also means you understand how SD-WAN rules influence path choice and how that interacts with policies and health checks.
Routes first. Then policies. Then NAT. That mental order helps when troubleshooting.
VPNs (IPsec and SSL VPN)
You'll encounter FortiGate VPN (IPsec/SSL) setup concepts: phase1/phase2 ideas, proposals, authentication methods, split tunneling, portal basics, and "why can I connect but can't reach anything." IPsec is standard for site-to-site. SSL VPN appears constantly for remote access, even if some organizations are shifting away from it.
I actually spent about two weeks once chasing a VPN issue that turned out to be an expired intermediate cert on a third-party CA. Nobody noticed for months because the main cert was fine. That's the kind of tedious stuff you learn to check automatically after enough late nights.
High availability (HA) and redundancy
Basic HA concepts: what fails over, what syncs, and what breaks when you configure it wrong. Know the intent and the operational impact, not just "active-passive is a thing."
Logging, monitoring, and troubleshooting (FortiAnalyzer/FortiGate tools)
Logs. Forward traffic logs, event logs, and basic debug flow thinking. Also, FortiAnalyzer and logging monitoring concepts matter because in real life you're not scrolling one box forever. You need to know where visibility comes from and how to confirm a hypothesis quickly.
Ping. Traceroute. Packet capture. Repeat.
Prerequisites and recommended experience
Prerequisites (official vs. recommended)
Here's the part people overcomplicate. Official prerequisites from Fortinet for this exam are basically: there are no mandatory prerequisite certifications required to attempt the exam. That's it. No gatekeeping like "must already have NSE 3" before scheduling.
Fortinet does recommend a learning path though. They recommend completing NSE 1, NSE 2, and NSE 3 first for foundational knowledge, and those NSE 1-3 are free online courses that cover security awareness and the Fortinet product ecosystem. They won't teach you to build a full IPsec mesh from scratch, but they do help you speak Fortinet and understand what all the products are for.
Completion of the official NSE 4 FortiOS 7.2 training course is really suggested but not required. This is the significant one, because the course fits with the exam style and covers the "Fortinet way" of features, and it reduces the amount of guessing you do when two answers both sound plausible.
Alternative pathway? Equivalent work experience with FortiGate devices can substitute formal training. If you've spent months doing real changes, fixing real outages, and reading real logs, you already have the core muscle memory the course tries to simulate.
Also worth saying plainly: no specific education degree requirements. No minimum years of IT experience formally required. Nobody asks for your diploma at the exam check-in. They care if you can answer the questions.
Hands-on skills checklist (FortiGate/FortiOS 7.2)
Recommended technical background and skills, if you want this to feel fair:
You want 2 to 3 years of hands-on experience with network security technologies. Solid TCP/IP fundamentals. OSI model, subnetting, routing, and what happens when MTU or asymmetric routing ruins your day. Familiarity with firewall concepts like stateful inspection, NAT types, and access control list logic. Experience with VPN technologies in production (both IPsec and SSL if possible) because the exam loves VPN detail and the "connected but no traffic" situation.
A few more that matter more than people admit? Comfort with CLI and text-based config, because you'll troubleshoot faster if you can read config snippets and know what they imply. Understanding authentication protocols: LDAP, RADIUS, Active Directory, and how group membership maps to policy. Exposure to troubleshooting tools like ping, traceroute, packet capture, and reading logs without getting lost. General infrastructure knowledge (DNS, DHCP, NTP). Security concepts: encryption, certificates, PKI, and basic threat awareness so security profiles aren't just magic checkboxes.
FortiGate-specific time? Minimum 6 to 12 months working with FortiGate in production or at least a serious lab. You should have deployed a FortiGate in different positions: edge internet firewall, internal segmentation, and a DMZ scenario, because policy design looks different in each. You need to be able to configure basic firewall policies and NAT rules quickly. Implement at least one VPN solution (site-to-site IPsec is the classic starting point, and remote access comes next).
And yes, you should be comfortable validating behavior: policy lookup, session table thinking, and reading forward traffic logs to confirm the firewall did what you told it to do, not what you meant.
Best study materials for NSE4_FGT-7.2
Official training (Fortinet Training Institute / courseware)
If you can get access, take the official FortiGate 7.2 training aligned to NSE 4. It's the closest thing to "study what the exam writers expect," and it fills gaps like feature interactions and common defaults that bite people.
Documentation to prioritize (FortiOS 7.2 admin guides, cookbooks)
Docs are massive, so don't read everything. Prioritize the FortiOS 7.2 Administration Guide sections for firewall policy flow, NAT modes, VPN configuration, routing, SD-WAN, and logging. Cookbooks are excellent when you want a working baseline config you can reproduce in a lab and then break on purpose.
Labs and home practice setup (VMs, hardware, cloud)
Lab time is the cheat code. FortiGate VM in a hypervisor, a couple of test subnets, and a client VM gets you most of the way. Hardware is nicer if you have it. Cloud images can work too, but watch cost creep.
Build. Break it. Fix it.
NSE4_FGT-7.2 practice tests and exam prep strategy
Practice tests (how to choose quality sources)
NSE4_FGT-7.2 practice test content is a minefield. Some are legitimate and teach you where you're weak. Some are brain dumps with wrong answers and weird phrasing that trains bad habits. If the questions look like they were machine-translated three times, run.
Pick sources that explain why an answer is correct, and cross-check anything questionable against Fortinet docs or your lab.
Topic-by-topic revision plan (2 to 6 week schedules)
If you've got 2 weeks, focus on your weakest objectives first, then do mixed review. If you've got 6 weeks, do one objective area per week with labs, then a final week of mixed scenarios and troubleshooting drills. Keep a running notebook of "things I got wrong and why." That list is gold.
Common mistakes to avoid on exam day
Rushing, misreading "most likely" vs "best," and ignoring one word like "incoming interface" that changes the whole policy match. Another classic? Overthinking a question when the exam is really testing a default behavior you should know from lab time.
Slow down. Read twice.
Renewal / recertification for Fortinet NSE 4
Renewal requirements and validity period (what to verify)
For NSE4_FGT-7.2 renewal, verify the current validity period and policy on Fortinet's certification site, because programs evolve. Don't rely on old forum posts. This is admin work, but it matters, especially if your employer tracks cert expiration dates.
Recertification options (retake vs. higher-level path)
Usually your options are retaking the current exam version or moving up to a higher-level Fortinet certification that renews lower ones, depending on Fortinet's current rules. If you're already doing FortiManager or FortiAnalyzer work daily, a higher-level path can make more sense than retaking.
Keeping skills current with FortiOS releases
FortiOS changes. Features move. Defaults shift. Keep reading release notes for things you actually use: VPN behavior, SSL inspection changes, and logging/reporting updates. Your future self will thank you during the next upgrade window.
FAQs (quick answers)
Cost, passing score, and difficulty recap
Cost varies by region and Pearson VUE listing. Passing score isn't something I'd bank on as a fixed public number. Difficulty is fair if you have real FortiGate time, rough if you're trying to brute-force memorize.
Best last-minute study materials and practice tests
Official courseware notes, FortiOS 7.2 docs for your weak spots, and a reputable practice test that explains answers. Last minute is for tightening, not learning brand new VPN concepts.
Objectives and prerequisites summary
No mandatory prerequisite certifications. Fortinet recommends NSE 1-3 first (free). Official NSE 4 FortiOS 7.2 training is recommended, not required, and real FortiGate work can substitute. If your background includes TCP/IP, firewalling, VPNs, routing, auth, and troubleshooting, the Fortinet NSE 4 FortiOS 7.2 certification is a realistic next step.
Conclusion
Wrapping up your NSE4_FGT-7.2 path
Look, you won't just pass this thing overnight. The Fortinet NSE4_FGT-7.2 exam demands a real strategy and actual hands-on experience with FortiGate 7.2. There's no shortcut here. Way too many candidates assume they can brute-force memorize their way through the NSE4_FGT-7.2 exam objectives without ever launching a firewall console. That's exactly why first-attempt failures happen so frequently.
The FortiOS 7.2 firewall configuration components, the routing complexities and SD-WAN peculiarities, the VPN tunnel troubleshooting challenges.. all this stuff makes sense when you've personally debugged it yourself during late-night lab sessions. There's something about troubleshooting at 2am that makes concepts stick, you know? I remember spending an entire weekend trying to figure out why an IPsec tunnel kept dropping, only to realize I'd fat-fingered a subnet mask. Frustrating? Sure. But I'll never make that mistake again.
After you've completed your FortiGate 7.2 training and successfully built several security policies, NAT rules, and maybe an IPsec tunnel or two, that's your signal to start working through NSE4_FGT-7.2 practice test materials. Not earlier. Practice tests reveal exactly where knowledge gaps exist, which exam objectives you're shaky on, and what the actual question format feels like.
The Fortinet NSE 4 FortiOS 7.2 certification cost isn't small. We're looking at several hundred dollars depending on where you're located. Retaking because you skipped preparation? That stings.
The NSE4_FGT-7.2 passing score sits around 70% (Fortinet doesn't officially confirm this), which seems reasonable until you're faced with a simulation question about FortiAnalyzer logging or some twisted SD-WAN scenario. Those questions eat your time. A full NSE4_FGT-7.2 study guide helps, but nothing replaces drilling scenarios over and over until FortiGate security policies and NAT logic becomes instinctive. Almost automatic.
Oh, and the NSE4_FGT-7.2 renewal requirement? Don't overlook that. This cert expires. You'll need to either retake it or pursue a higher-level NSE track to maintain active status. Fortinet updates FortiOS constantly, so staying current isn't optional if you want this credential carrying actual weight with employers.
If you're committed to passing on your first attempt and you want exam-realistic questions that reflect what Fortinet actually tests, grab the NSE4_FGT-7.2 Practice Exam Questions Pack at /fortinet-dumps/nse4_fgt-7-2/. It's among the stronger resources I've encountered for targeting weak areas without burning time on outdated material. Combine that with your lab work and official documentation, and you're positioned well. Get after it.