Fortinet NSE6_FWB-6.4 (Fortinet NSE 6 - FortiWeb 6.4)
Fortinet NSE6_FWB-6.4 Exam Overview and Certification Value
I've been working with web application firewalls for years, and the Fortinet NSE6_FWB-6.4 exam is honestly one of those certifications that separates people who just know security buzzwords from folks who can actually lock down web apps in production. This isn't your typical multiple-choice security exam where you memorize definitions and call it a day.
What the Fortinet NSE 6 FortiWeb 6.4 certification actually validates
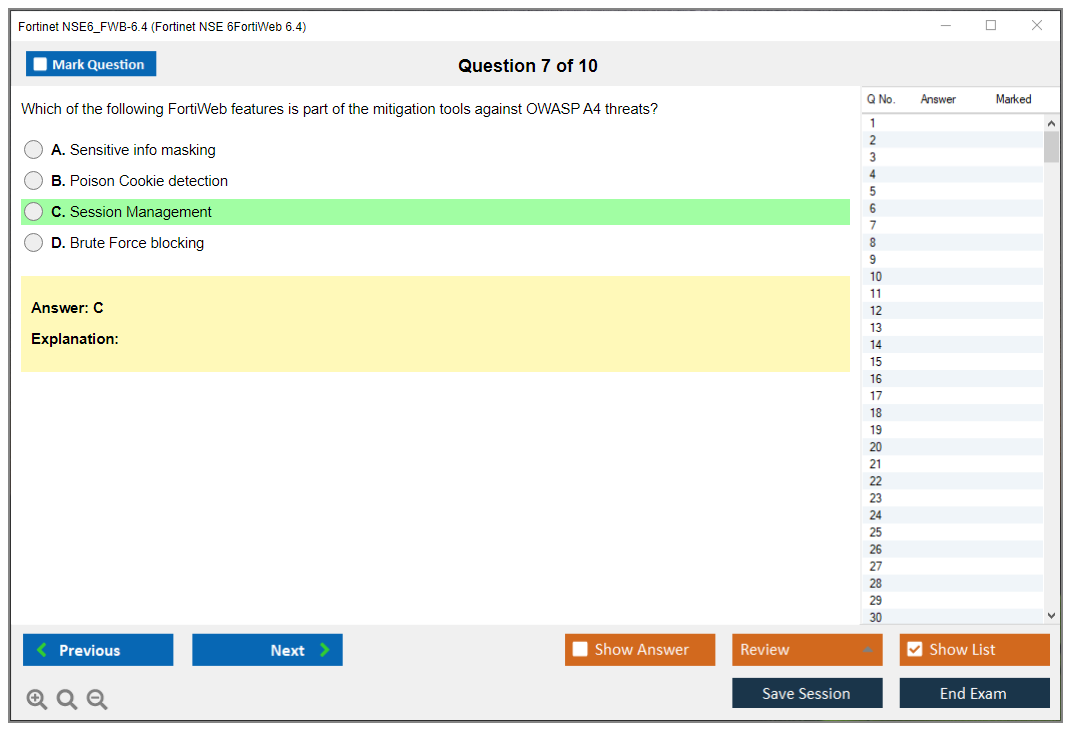
The NSE6_FWB-6.4 exam validates specialist-level skills in deploying, configuring, and managing FortiWeb 6.4 web application firewalls. We're talking advanced stuff here. Not just clicking through a GUI, but understanding how to protect web applications from the OWASP Top 10 threats, DDoS attacks, bot attacks, and those advanced web-layer exploits that keep security teams up at night. Anyone can install a WAF. Configuring it to stop attacks without breaking legitimate traffic? That's where this certification proves its worth.
The exam sits in the NSE 6 specialist track, which means it's above the NSE 4 FortiGate Infrastructure professional level but below the NSE 7 architect and NSE 8 expert tiers. It's that sweet spot where you're expected to have solid foundational knowledge but also demonstrate deep expertise in a specific product domain. You're not expected to architect entire Security Fabric deployments from scratch, but you absolutely need to know how FortiWeb integrates with FortiGate, FortiAnalyzer, and the broader Fortinet ecosystem. This can get complicated depending on your environment.
Who should actually take this exam
Security engineers who deal with web applications daily. WAF administrators. Application security specialists who need to prove they understand more than just scanning tools. Network security professionals expanding into application-layer protection. Security consultants who need vendor-specific credentials to back up their recommendations.
Honestly? If you're managing or planning to manage FortiWeb deployments, this certification makes sense. The job market values specialists, not generalists who know a little about everything. I've seen job postings specifically asking for NSE 6 FortiWeb experience because organizations using Fortinet solutions want people who can hit the ground running without months of on-the-job training.
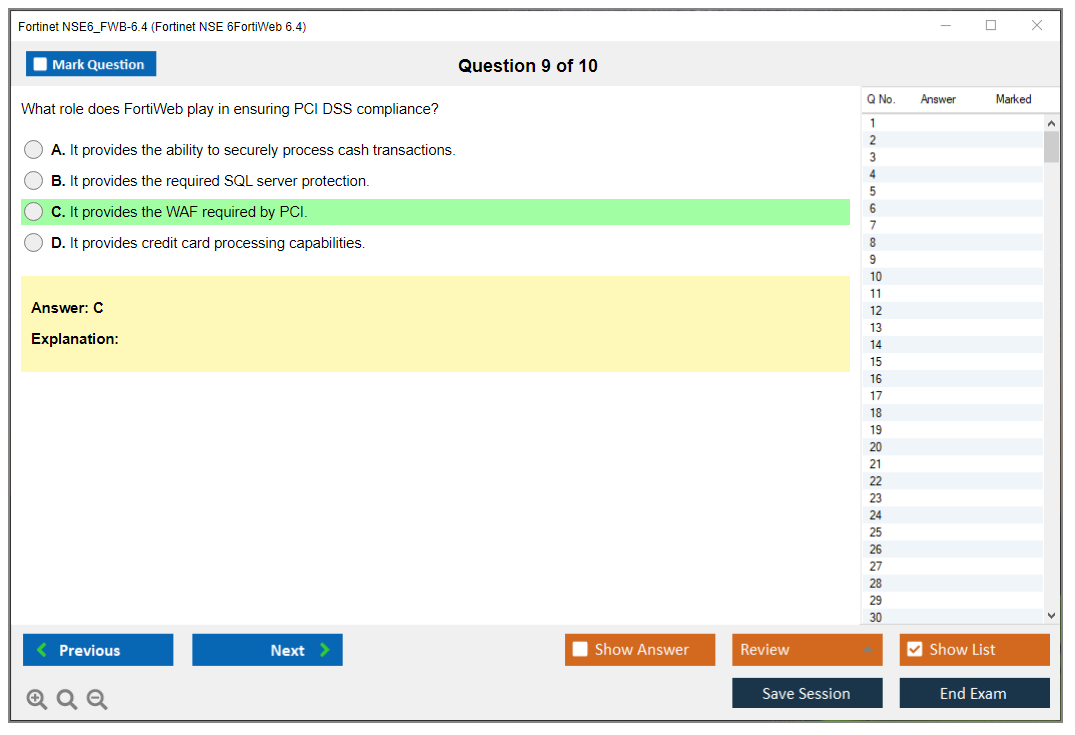
The real-world application scenarios this cert prepares you for are pretty extensive. Designing multi-layer web security architectures. Implementing zero-day protection using machine learning signatures. Optimizing WAF performance so you're not introducing latency that pisses off users and developers alike. You'll learn policy tuning and false positive reduction, which is honestly 80% of WAF administration work. And security event analysis that actually leads to actionable intelligence instead of just noise.
Why FortiWeb 6.4 specifically matters
FortiWeb 6.4 represents a mature WAF solution with machine learning capabilities that go beyond basic signature matching. It includes API security features, which is huge considering how many breaches happen through poorly secured APIs these days. The bot mitigation stuff is sophisticated. Not just blocking obvious bots but identifying and handling sophisticated automated threats that mimic legitimate user behavior.
Web application attacks remain the top attack vector. SQL injection, cross-site scripting, authentication bypasses. These aren't theoretical threats, they're happening constantly. I saw a retail client get hammered by a credential stuffing attack last month that their old WAF missed completely. Organizations need people who can configure WAFs to stop these attacks while maintaining application functionality. The NSE6_FWB-6.4 certification proves you understand this balance.
How this certification fits your career trajectory
The career impact is real. Not gonna lie, having specialist certifications differentiates you in a crowded cybersecurity job market where everyone claims to be a "security expert." When you can point to vendor-specific expertise that's highly valued by organizations already invested in FortiWeb solutions, you become significantly more marketable. Experience still matters more than paper credentials in most interviews though.
Business value proposition matters too. Certified professionals can reduce web application breach risk, ensure compliance with regulations that mandate WAF deployment (PCI DSS, for example), and optimize security operations so you're not drowning in false positive alerts. Organizations care about this because breaches are expensive. Not just in direct costs but reputation damage and regulatory penalties.
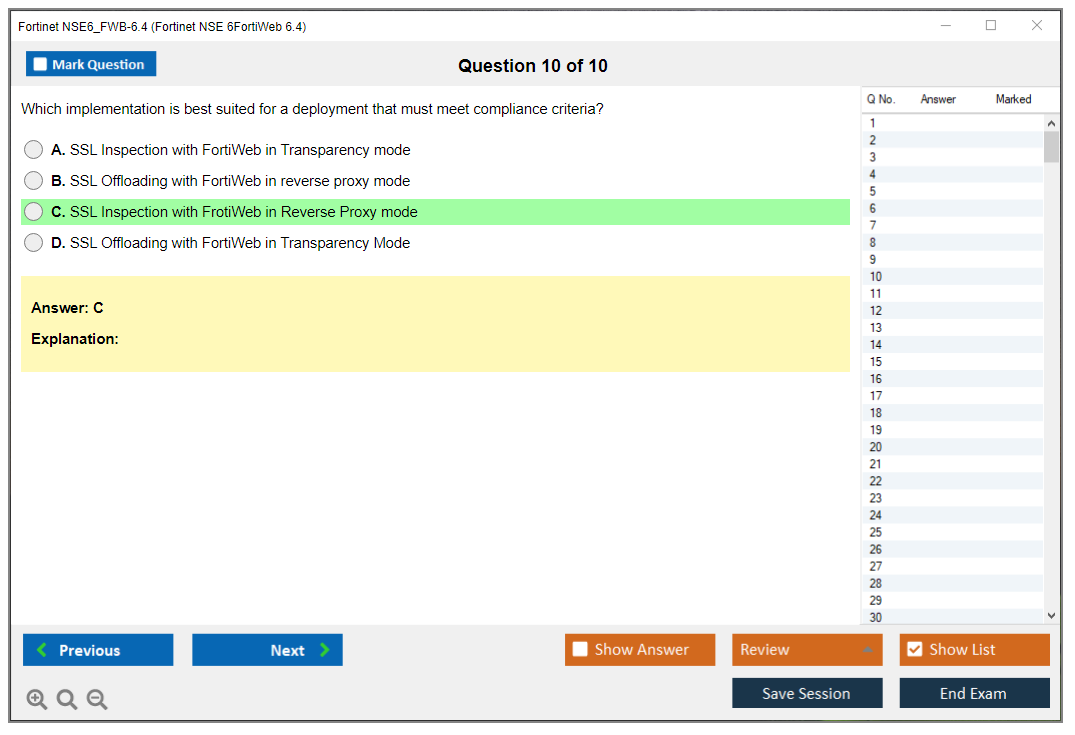
The exam aligns closely with actual job tasks. Questions mirror real deployment scenarios you'll face: configuring reverse proxy mode versus transparent mode, setting up server pools and load balancing, implementing SSL/TLS offloading and inspection, creating custom attack signatures when built-in ones don't cut it. Troubleshooting why legitimate traffic is getting blocked. Setting up high availability pairs so you don't have a single point of failure. It's practical.
Complementary certifications worth considering
The NSE 4 FortiOS certification is honestly a solid foundation before tackling NSE 6 FortiWeb. Understanding FortiGate firewall concepts helps because FortiWeb often sits behind or alongside FortiGates in production environments. Some people also pursue NSE 7 Enterprise Firewall certifications to round out their Fortinet knowledge, though that's more of a long-term career move.
Outside the Fortinet ecosystem? CISSP provides broader security context. CEH gives you the attacker perspective that helps when tuning WAF policies. Understanding how exploits work makes you better at stopping them. Vendor-neutral web security certifications exist but honestly lack the hands-on configuration depth that vendor-specific certs provide.
Version-specific considerations you need to know
Here's something important: the NSE6_FWB-6.4 exam covers features specific to the 6.4 release. Fortinet updates FortiWeb regularly, and newer versions introduce features, change configuration options, and modify best practices. You might need recertification or upgrade exams when newer versions become the standard. This is typical for vendor certifications. They want to ensure certified professionals stay current with product capabilities.
The certification validates both theoretical knowledge and hands-on configuration skills essential for production environments. You can't just read documentation and pass this exam. You need lab time. Experience breaking things and fixing them. Understanding why certain configuration choices matter in real deployments versus lab environments where security is the only consideration.
Fortinet ecosystem integration
FortiWeb doesn't exist in isolation. It integrates with FortiAnalyzer for centralized logging and reporting, FortiManager for policy management across multiple FortiWeb instances, and the broader Security Fabric for threat intelligence sharing. Understanding these integrations is part of the exam because real deployments use these capabilities. A FortiWeb that's not feeding security events to your SIEM or FortiAnalyzer is basically blind. You're stopping attacks but not learning from them or correlating them with other security data.
Look, web application security is complex. Applications change constantly. New vulnerabilities emerge weekly. Attack techniques evolve faster than signature updates can keep up. The NSE6_FWB-6.4 certification demonstrates you understand this complexity and can implement defenses that adapt to changing threats while maintaining application availability. That's the real value proposition. Not just passing an exam, but proving you can protect critical web applications in production environments where downtime and security breaches both carry significant consequences.
NSE6_FWB-6.4 Exam Cost, Registration, and Logistics
Fortinet NSE6_FWB-6.4 exam is the Fortinet NSE 6 specialist exam for FortiWeb 6.4, the FortiWeb web application firewall certification that proves you can deploy, tune, and troubleshoot a WAF in the real world. Not theory. Actual FortiWeb 6.4 configuration and deployment stuff like policies, server objects, certificates, and security profiles that map pretty cleanly to OWASP Top 10 protection with FortiWeb.
Fortinet NSE6_FWB-6.4 (NSE 6, FortiWeb 6.4) exam overview
What the certification validates
This one validates you can run FortiWeb like an adult. You're expected to understand how traffic gets processed, how to publish apps safely, how to do HTTPS offload or inspection without breaking everything. And you've gotta troubleshoot when the dev team says "your WAF blocked our login" but they won't send you logs.
Short version? WAF ops. Longer version, the part that matters for hiring: you can take FortiWeb security profiles and policies, apply them without torching production, and then explain what happened with decent logging and monitoring.
Who should take NSE6_FWB-6.4 (recommended roles)
This is a good fit for WAF admins, security engineers, and network/security folks who got handed "protect these web apps" as an extra duty. Sometimes feels like punishment, but here we are. Some appsec people take it too, especially if they're the ones pushing bot mitigation, signatures, constraints, and positive security models.
Not entry level. Not impossible either. But you should already be comfortable reading HTTP/S behavior and dealing with cert chains. I once watched someone freeze up on a TLS question because they'd never actually looked at a cert chain before, which made for a rough afternoon.
NSE6_FWB-6.4 exam cost and registration
Exam cost (what to expect)
The NSE6_FWB-6.4 exam cost typically lands in the $400 to $500 USD range. That's the number most people see. But it's not a global constant, because pricing can vary by region and testing provider, plus taxes in some places can make the final checkout total feel weirdly higher than what your coworker paid.
Regional pricing variations are real. EMEA, APAC, and the Americas can all differ. The only number that matters is what you see when you're booking in your region, so check your local Pearson VUE pricing for the exact amount tied to your account location and currency.
One more angle people forget. Training bundles. Some official Fortinet training courses include exam vouchers. If your employer's paying for training anyway, that can reduce the overall cost of the Fortinet NSE 6 FortiWeb 6.4 certification by a lot compared to buying the course and then buying the voucher separately.
If you're in a company training a group, ask about corporate or bulk purchasing. Organizations training multiple employees sometimes get volume discounts through Fortinet partners. Not always advertised, worth asking, quiet money.
How to register and schedule the exam
Registration is basically the Pearson VUE flow:
Create an account on Pearson VUE, then search for the NSE6_FWB-6.4 exam code, and pick a testing center or online proctoring option. That's the whole thing, but the details matter. Name mismatches and expired IDs are the dumbest way to lose a test day you were ready for. I mean it happens more than you'd think.
Scheduling flexibility? Decent. Exams are available at authorized testing centers worldwide, plus online proctored options for remote testing, so you're not stuck driving two hours unless your city has limited availability.
Book ahead. Seriously. Peak seasons are real. I recommend scheduling 2 to 4 weeks out, because last-minute slots can be limited in popular areas. You don't want your study plan to get wrecked because the only open appointment is 19 days later than you planned.
Online proctoring requirements
Online proctoring is convenient, but it's picky. You'll need stable internet, a webcam, a microphone, a private space, and you'll do a system compatibility check. If any of that's flaky you can lose time arguing with the proctor while your stress spikes through the roof. Terrible way to start an exam that already expects you to think clearly about reverse proxies and policy order.
Do the system test early. Clean your desk. Warn your roommates.
Testing center advantages
Testing centers are boring, and that's the point: controlled environment, fewer technical issues. If you're worried your home network will hiccup or your laptop fans will go full jet engine mid-exam, a center's the safer bet.
Retake policy and costs
If you fail an attempt, you'll need to purchase another exam voucher. No free redo. Understand retake waiting periods before rescheduling, because Pearson VUE and vendor policies can enforce cooldown windows that mess with your timeline if you were hoping to "try again next weekend."
Not gonna lie, budgeting for a retake's smart. Even if you don't need it. That mental safety net helps.
Voucher validity, payments, cancellations, check-in
Exam voucher validity is typically 12 months, but verify your expiration date when you buy it. People get burned when they purchase early, get busy at work, and then realize their voucher expires the week before they planned to sit. Annoying.
Payment methods usually include major credit cards and vouchers, and sometimes purchase orders depending on how you register and whether you're going through a company channel.
Cancellation and rescheduling policies are usually reasonable: Pearson VUE typically allows free reschedules up to 24 to 48 hours before the appointment. Don't assume, because regional rules and exam program rules can differ.
Check-in is its own mini process. If you're at a testing center, arrive 15 to 30 minutes early for ID verification and locker rules. If you're online, plan a 15-minute system check, room scan, and proctor instructions before the clock really gets going.
Identification requirements are strict: bring a government-issued photo ID with a signature. Make sure your name matches your registration details exactly. Middle initials, hyphens, spacing, the petty stuff. It matters.
Special accommodations exist. If you need them, request testing accommodations through Pearson VUE during registration, and don't wait until the week of the exam.
NSE6_FWB-6.4 passing score and exam format
Passing score (how scoring works)
People ask about the NSE6_FWB-6.4 passing score a lot. Fortinet doesn't always publish a simple "you need X%" number for every exam in a way that stays consistent over time, and scoring models can change. Treat any fixed number you see online as suspect unless it's current and from Fortinet.
You will get a preliminary pass/fail right after, which is nice. The official score report typically shows up in the Fortinet certification portal within a few days.
Question types, time limit, and exam delivery
Expect scenario-based questions that feel like "here's the config and symptoms, what do you change," mixed with conceptual stuff tied to FortiWeb 6.4 exam objectives. Delivery is Pearson VUE, either at a center or online proctored.
NSE6_FWB-6.4 difficulty level
Difficulty rating (beginner/intermediate/advanced)
I'd call it intermediate to advanced if you're new to WAFs. If you already live in WAF land, it's more like "detailed intermediate," because it's vendor-specific and rewards time spent in the GUI and CLI rather than just knowing OWASP headlines.
What makes the exam challenging
FortiWeb has lots of moving pieces: policy flow, server objects, certificates, logging. If you don't have hands-on time, questions about why traffic's blocked or why HTTPS offload fails will feel like guessing.
How long to study (typical timelines)
If you're already administering FortiWeb, 2 to 4 weeks of focused review can be enough. If you're coming from general firewall work, plan longer, because WAF logic is different and the "normal firewall instincts" don't always apply.
NSE6_FWB-6.4 exam objectives (official topics)
FortiWeb deployment modes and architecture show up a lot, plus traffic processing, policies, and server objects. Security profiles matter too: signatures, constraints, and bot mitigation. You should know where each control's applied and what it breaks when misconfigured.
Authentication, certificates, and HTTPS inspection/offload are frequent pain points in production, so expect them. Logging, monitoring, and troubleshooting are not optional, because the product lives or dies on whether you can prove what it blocked and why. Also, high availability, performance, and maintenance basics, because nobody wants a WAF that becomes the single point of failure.
Prerequisites and recommended experience
Formal prerequisites (if any)
There usually aren't strict NSE6_FWB-6.4 prerequisites like "must hold NSE 5," but Fortinet expects you to be ready at the NSE 6 level. That's implied.
Recommended hands-on skills (WAF, HTTP/S, OWASP, PKI)
You should be comfortable with HTTP methods, headers, cookies, TLS basics, cert chains, and how OWASP Top 10 maps to WAF controls. If PKI makes you sweat, fix that before exam week.
Best study materials for FortiWeb 6.4 (NSE6_FWB-6.4)
Official Fortinet training and courseware
Start with official training if you can. It fits with the Fortinet NSE 6 FortiWeb 6.4 certification objectives and tends to mirror the way Fortinet words questions.
FortiWeb documentation to prioritize
Admin guide and cookbooks are your friends. Release notes too, because behavior changes across versions can show up as "which feature works this way in 6.4."
Hands-on lab practice
Spin up a lab with a simple web app behind FortiWeb, then practice publishing, applying signatures and constraints, turning on bot mitigation, and reading logs when stuff breaks. That hands-on loop is what makes the exam feel fair.
NSE6_FWB-6.4 practice tests and exam prep strategy
Practice test options
For NSE 6 FortiWeb 6.4 practice tests, I'm picky. Avoid brain dumps, use questions that explain why an answer's right, because the exam's more about reasoning through FortiWeb behavior than memorizing menu paths.
Checklist: topics to master before test day
Know where to troubleshoot TLS failures. How policy order affects matching. What common false positives look like. How to confirm a block in logs.
Common mistakes? Two big ones. People skip certificates practice, then panic on HTTPS questions. Others ignore troubleshooting and focus only on "features," then get wrecked by scenario prompts.
NSE6_FWB-6.4 renewal and recertification
Certification validity and renewal cycle (how renewal typically works)
The NSE6_FWB-6.4 renewal policy can change as Fortinet updates its certification program, so check the current Fortinet Training/Certification portal for validity periods and renewal rules tied to your credential.
Keeping skills current (upgrade path and version changes)
FortiWeb versions move, and your job will too. Keep an eye on new features, updated signatures, and changes to defaults, because the real career value is staying employable when the platform updates, not just passing once.
FAQ (people also ask)
What is the NSE6_FWB-6.4 exam and who should take it?
It's a Fortinet NSE 6 specialist exam for FortiWeb 6.4, best for security/network engineers and WAF admins who deploy and manage FortiWeb in production.
How much does the NSE6_FWB-6.4 exam cost?
Usually $400 to $500 USD, with regional variation, so confirm the exact price in your Pearson VUE checkout.
What is the passing score for the NSE6_FWB-6.4 exam?
You'll see pass/fail immediately, but the exact scoring threshold can vary and isn't always published in a stable way. Check Fortinet's current exam page if you want the most accurate info.
How hard is the Fortinet NSE 6 FortiWeb 6.4 exam?
Intermediate to advanced, mostly because it's operational and vendor-specific. Hands-on time makes it way easier.
What are the best study materials and practice tests for NSE6_FWB-6.4?
Official Fortinet courseware plus FortiWeb docs first, then lab practice, then selective practice questions that explain the logic. FortiWeb 6.4 study materials that include troubleshooting examples are the ones that pay off.
NSE6_FWB-6.4 Exam Format, Passing Score, and Timing
Passing score (how scoring works)
The NSE6_FWB-6.4 exam typically needs 70% to pass. That's roughly 25-28 correct answers depending on total questions. The exact number shifts around because you'll face somewhere between 35 and 40 questions depending on your test version. Pretty standard for Fortinet NSE 6 level certifications, but what makes it really tricky is how they weight questions based on complexity and strategic importance.
Not all questions equal.
Here's where it gets interesting. Fortinet doesn't publicly disclose their exact scoring methodology, which I find frustrating. Questions are weighted based on difficulty and importance to real-world deployments. A complex scenario question analyzing multi-step troubleshooting might be worth significantly more than a straightforward recall question about default settings. You can't just count questions to know your exact standing.
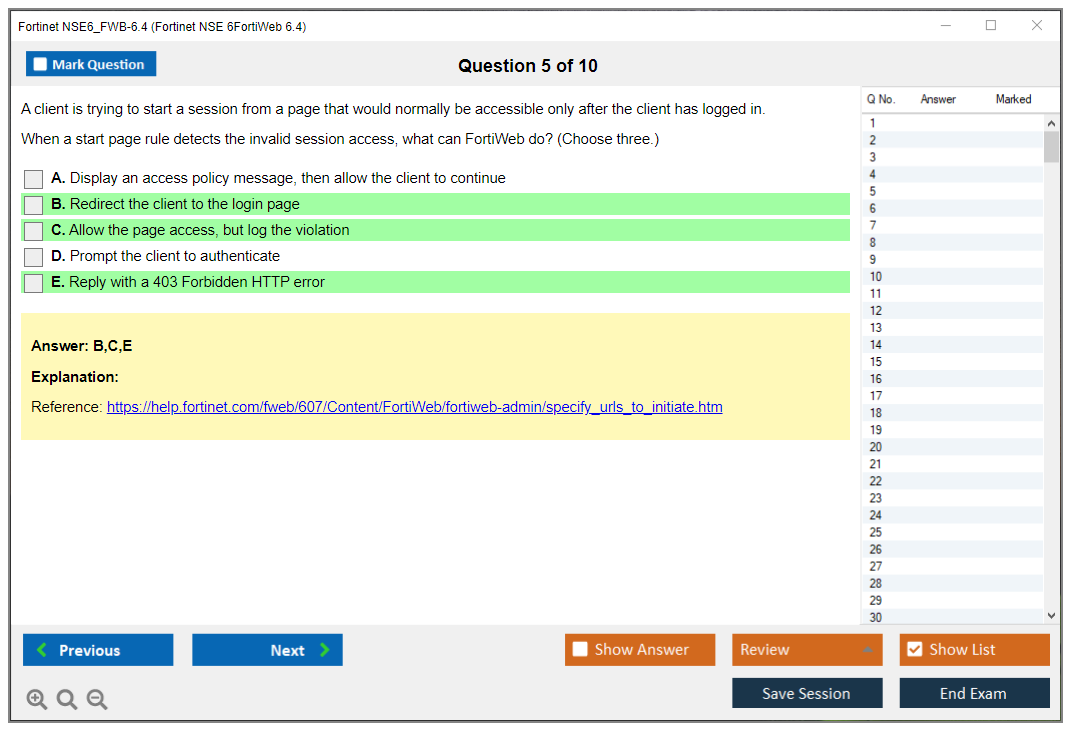
Zero partial credit on multiple-answer questions. If a question asks you to select three correct answers and you only pick two? You get nothing. It's all or nothing, which makes those multiple-select questions particularly dangerous if you're not absolutely certain. Harsh but it forces you to really know the material rather than gaming the system through educated guessing alone.
Good news? There's no penalty for guessing whatsoever. Unanswered questions count as wrong anyway, so you should always provide an answer even when you're completely unsure. I've seen people leave questions blank thinking it might help somehow. It doesn't work that way. Take your best educated guess based on eliminating obviously wrong answers.
You get immediate preliminary results when you submit. The screen shows your pass/fail status right there, which is both a relief and nerve-wracking depending on your confidence level going in. Within a few days, you'll receive a detailed score report that breaks down your performance by exam domain, showing which areas were strengths and which need improvement if you need to retake it.
Question types, time limit, and exam delivery
The Fortinet NSE6_FWB-6.4 exam gives you 105 minutes. That's 1 hour and 45 minutes total. With roughly 35-40 questions, you're looking at about 2.5 to 3 minutes per question on average, which sounds reasonable until you hit those scenario-based monsters that require analyzing configuration screenshots, log entries, and multi-paragraph descriptions that reference multiple interconnected systems and security policies simultaneously.
Question formats include primarily three types: multiple-choice single-answer (pick one correct option), multiple-choice multiple-answer (select all that apply), and scenario-based questions that present real-world configurations requiring analysis. The scenario questions are heavily emphasized here because Fortinet wants to verify you can actually deploy and troubleshoot FortiWeb in production environments, not just memorize definitions from study guides.
Time management becomes critical. I recommend flagging difficult questions for review if the testing platform allows it. Most do, thankfully. Don't burn 8 minutes on one tough scenario question when you could knock out three easier ones in that time. Answer what you know confidently first, mark the tricky ones, then circle back if time permits.
The exam isn't adaptive. Everyone gets the same number of questions regardless of performance. This is different from some other certification programs that adjust difficulty based on your answers. Questions appear in randomized order too, so don't expect them to start easy and progressively get harder. You might hit a brutal multi-part scenario as question three and a simple definition recall as question thirty.
Most testing centers provide erasable noteboards for scratch work, which is helpful for mapping out complex scenarios. You cannot bring any external materials. No notes, no calculators, no reference documentation whatsoever. If you're taking the exam via online proctoring, policies vary but typically allow one blank sheet of paper that you must show to the camera before starting. No bathroom breaks during the 105 minutes unless you want to risk forfeiting your exam depending on proctor rules, so plan accordingly and don't overhydrate beforehand.
Before starting, you'll need to accept a non-disclosure agreement. This NDA prevents you from sharing specific question content publicly, discussing exact scenarios you encountered, or reproducing test materials in any format. It's standard practice but worth mentioning because you can't expect detailed question breakdowns from others who've taken it.
The exam is available primarily in English. Potential other language options depending on your region exist. Verify language availability during registration because not all testing centers offer all languages. If you encounter technical issues during the exam (computer freezes, network problems, display issues), report them immediately to your proctor. Testing providers may grant additional time for verified technical problems, but you need to document it in real-time, not after completing the exam.
What makes this format challenging
The scenario-based emphasis is what separates casual FortiWeb users from people who actually know the product inside and out. Many questions present configuration screenshots where you need to identify misconfigurations, recommend best practices, or determine why protection isn't working as expected in specific deployment contexts. These aren't simple "what does this feature do" questions. They're "given this specific deployment with these settings, what's the best approach to solve this problem" questions that require integrated knowledge.
Questions range from straightforward configuration recall to complex multi-step troubleshooting scenarios that mirror real production issues. You might see a question showing FortiWeb logs with blocked traffic and need to determine which security profile rule triggered the block and whether it's a false positive requiring adjustment. Or a question might present a deployment architecture and ask which operation mode is most appropriate given specific requirements around network topology, traffic flow, and security objectives.
The exam emphasizes GUI-based configuration, which makes sense because most administrators work through the web interface daily. But it definitely includes CLI commands for advanced features and troubleshooting scenarios where the GUI doesn't provide sufficient visibility. You need comfort with both interfaces. If you've only ever clicked through the GUI without understanding what's happening under the hood, you'll struggle with deeper questions. Actually reminds me of a colleague who could work through the interface perfectly but completely froze when asked to verify a configuration via CLI during an outage. Not a fun situation to be in.
Wrong answers aren't obvious.
Distractor answers (the wrong options) are crafted carefully to represent common misconfigurations or misconceptions that practitioners actually make in the field. They're not obviously wrong gibberish. They're plausible-sounding options that might seem correct if you have incomplete knowledge or haven't encountered that specific scenario before. This is intentional because Fortinet wants to test depth of understanding, not surface-level familiarity with terminology.
All questions map directly to the published exam objectives, so there shouldn't be surprise topics outside the official domains listed in the exam blueprint. The question pool gets updated periodically to reflect software updates and emerging threats, but the format remains relatively consistent across versions. Official practice tests closely mirror actual exam question style and difficulty, which makes them valuable preparation tools worth investing in.
If you're serious about preparing efficiently, the NSE6_FWB-6.4 Practice Exam Questions Pack at $36.99 provides realistic question formats that match what you'll encounter. I've found that practicing with scenario-based questions is infinitely more valuable than just reading documentation because it forces you to apply knowledge rather than passively consume it without context.
One thing people underestimate? The mental fatigue factor is real. 105 minutes of intense concentration analyzing technical scenarios is exhausting in ways that surprise first-time takers. Your performance on question 35 might suffer compared to question 5 simply because your brain is tired and you're second-guessing decisions you'd normally make confidently. Practice full-length timed exams to build that stamina. It matters more than you'd think.
The non-adaptive nature means you can't relax after answering several questions correctly, assuming the exam is going easy on you or adjusting difficulty downward. Every question counts equally toward that 70% threshold, whether it's the first or last question in your sequence. Stay focused throughout the entire session without letting early successes breed overconfidence.
The format isn't designed to trick you through deceptive wording or gotcha questions. It's designed to verify you can actually configure, deploy, and troubleshoot FortiWeb 6.4 in production environments under realistic conditions. If you've got hands-on experience and have studied the exam objectives thoroughly while practicing with labs, the format shouldn't surprise you. But if you're trying to memorize your way through without understanding FortiWeb architecture, traffic processing flows, and security profiles at a functional level, the scenario questions will expose those gaps quickly.
NSE6_FWB-6.4 Difficulty Level and Study Time Requirements
Fortinet NSE6_FWB-6.4 (NSE 6, FortiWeb 6.4) exam overview
The Fortinet NSE6_FWB-6.4 exam is Fortinet's specialist-level test for FortiWeb 6.4, and honestly, it's checking whether you can actually run a WAF like an adult in production, not just clicking around the GUI or memorizing feature names like you're studying for vocab class. Real config choices, real troubleshooting, real "why is this app broken after we enabled security" moments that make your stomach drop.
What the certification validates is your ability to deploy and tune FortiWeb as a FortiWeb web application firewall certification, including FortiWeb 6.4 configuration and deployment, OWASP Top 10 protection with FortiWeb, and the day-two ops stuff that teams always forget about until something catches fire.
Who should take it? AppSec-ish security engineers. WAF admins. People doing reverse proxy, TLS offload/inspection, bot mitigation, and incident response around web apps. Basically anyone who's responsible when things go sideways. Also consultants who keep getting pulled into "we bought FortiWeb, now what" projects. If you're networking-only, you can still pass, but the web app security mindset is what makes this exam feel manageable instead of brutal.
NSE6_FWB-6.4 exam cost and registration
The NSE6_FWB-6.4 exam cost varies by region and testing provider, and Fortinet changes details over time, so you have to check the Fortinet Training/Certification portal and the registration page for your country. Annoying? Sure. Normal? Unfortunately.
Scheduling is straightforward once you have a Fortinet Training account. Pick your delivery method, pick a date, pay, and then you're committed. No magic here. Just don't wait until the last week because some regions have weird availability windows that'll mess up your timeline.
NSE6_FWB-6.4 passing score and exam format
The NSE6_FWB-6.4 passing score isn't something Fortinet always spells out in a nice permanent way publicly, and it can shift with exam revisions, which, I mean, it's frustrating, but you'll see scoring info in the official exam details when you register. Expect typical pro cert scoring behavior where you can feel good during the exam and still fail if your weak areas line up with weighted objectives.
Question types? That's where people get surprised. You get scenario-heavy items that feel like the Fortinet NSE 6 specialist exam FortiWeb version of "here's a log snippet, here's a config fragment, what's the best next step." Some questions are direct, sure, but a lot are about interactions between policies, server objects, and FortiWeb security profiles and policies.
NSE6_FWB-6.4 difficulty level
Intermediate to advanced.
That's the honest rating for the Fortinet NSE6_FWB-6.4 exam, and I'm not sugarcoating it. You need a solid base in web security and WAF concepts, and you need to be comfortable with HTTP/HTTPS behavior, cookies/sessions, redirects, caching weirdness, and what "normal traffic" looks like versus attack patterns that blend in.
Compared to NSE 4, it's significantly harder. NSE 4 tests broad Fortinet product knowledge and common firewall operations. Here, you're in the weeds with implementation decisions, troubleshooting, optimization techniques, and those painful tradeoffs between blocking attacks and not breaking the app that executives care about.
Look, the hardest part? The exam doesn't reward shallow awareness. You can know that machine learning exists in FortiWeb and still get wrecked because the question is really about when to use it, what profile mode makes sense, and how you'd interpret what it's flagging. Not just that it exists. Same with advanced bot mitigation. Same with HTTPS inspection configurations. Same with high availability scenarios where you have to think about session persistence, certs, and what happens during failover. Short questions. Big consequences.
Scenario-based complexity is real here. Multi-layered prompts show logs, config snippets, and then ask you to reason about security policy interactions, like an application delivery postmortem disguised as multiple choice. If you haven't done WAF troubleshooting, you'll spend half the time just translating what you're reading.
Hands-on experience matters more than people want to admit. Candidates with 6 to 12 months of FortiWeb in production usually do better than study-only candidates because they've already felt the pain of false positives, learned what to log, and know which "obvious" settings are actually dangerous in a live app. Lab practice is the next best thing. A virtual or physical lab environment dramatically improves your understanding of feature interactions and troubleshooting, especially when you intentionally break things like TLS versions, cipher mismatches, or a misordered policy.
Overconfidence is a trap. Network security folks sometimes assume WAF is just "firewall but for HTTP," and then they run into regex constraints, cookie security, PKI chains, and app behavior that doesn't act like clean RFC examples. Web stuff is messy. Always. You know what else catches people? The assumption that if they've used another vendor's WAF, FortiWeb will be intuitive. Maybe for the basics, but every product has quirks in how it handles edge cases, and FortiWeb's policy evaluation order can bite you if you're not careful.
How long to study (and what that actually means)
For beginners new to FortiWeb, 8 to 12 weeks is a sane timeline if you're doing 10 to 15 hours weekly. And that's not just reading slides, that includes building a lab, replaying traffic, and learning how FortiWeb thinks. If you're actively working with FortiWeb in production, 4 to 6 weeks can be enough, because your "study time" is partly your day job already.
Total study hours? Plan 80 to 120 hours if you want a real buffer. Video training, documentation review, and hands-on practice. And yes, documentation is a volume problem: FortiWeb 6.4 docs run hundreds of pages. Strategic reading is how you survive. Focus on the FortiWeb 6.4 exam objectives, admin guide sections tied to policies and profiles, logging and troubleshooting chapters, and the release notes for 6.4-specific changes and GUI differences versus earlier versions.
Daily pace works. I like 1 to 2 hours daily over 2 to 3 months because retention is better than cramming, and you have time to revisit stuff like PKI and HTTPS flows when it doesn't click the first time. A boot camp approach can work too: 5 days intensive training plus 2 to 3 weeks self-study, but only if your baseline is already strong. Otherwise you just get a week of information overload and then panic.
Learning curve factors that stretch prep time: weak HTTP/HTTPS protocol understanding, not being comfortable with regular expressions, and shaky PKI concepts like intermediates, SNI, and certificate chain validation. The thing is, those topics are quiet exam killers. Not glamorous. Still important.
NSE6_FWB-6.4 exam objectives (what gets tested)
FortiWeb deployment modes and architecture show up a lot, because your mode choice affects everything downstream, including troubleshooting. Traffic processing, policies, and server objects are core because FortiWeb is basically a decision engine built from these pieces.
Security profiles? That's the heart of it. You'll see signatures and constraints, bot mitigation, and machine learning security profiles, and the exam expects you to think about tuning and false positives, not just turning stuff on. Logging, monitoring, and troubleshooting is where the exam feels "real world," because questions often present symptoms and ask for diagnosis. Not config recall.
Authentication and certificates matter. HTTPS inspection/offload configurations matter. High availability, performance, and maintenance basics matter. Feature breadth beats ultra-deep specialization here, so you need broad coverage across the product, but you don't have to be a developer or cryptographer. You just can't hand-wave the web basics.
Best study materials and practice tests (and how to use them)
Start with official Fortinet training and courseware if you can. Then use the docs like a reference, not a novel. Build a lab with FortiWeb in front of a simple app, even a deliberately vulnerable one, and practice common workflows: create server objects, publish, apply profiles, generate logs, tune, and test HA behavior if your lab can simulate it.
For practice tests, pick ones that look like scenario questions, not trivia dumps. You want items that force you to interpret logs and configuration side effects. If you want a focused add-on for drilling exam-style questions, the NSE6_FWB-6.4 Practice Exam Questions Pack is here: NSE6_FWB-6.4 Practice Exam Questions Pack. I mean, use it like a mirror. If you miss a question, go recreate that scenario in your lab and prove you understand it.
Readiness indicator: consistently scoring 80%+ on practice exams and successfully completing lab scenarios without guessing your way through. That's when you're close. If you're still shaky on HTTPS inspection flows or why a policy match didn't happen, you're not ready yet. Simple.
Also, study groups help more than people expect. Talking through a messy scenario with someone else forces you to explain your reasoning, and that's basically what the exam is testing. If you can explain it, you can answer it.
Common failure reasons, retakes, and what to fix
Most failures? Insufficient hands-on practice, weak understanding of security profiles, and weak HTTP protocol knowledge. Not gonna lie, people also fail because they studied the wrong version. Version-specific details matter, and FortiWeb 6.4 has changes you need to recognize, and the exam will punish "I used 6.2 once" assumptions.
If you fail, the second attempt is usually a pass for people who actually use the score report correctly. Target the weak domains, do labs for those exact areas, and stop reading everything. Focus. Community feedback tends to put first-attempt pass rates around 60 to 70% for prepared candidates, which feels right for an intermediate-to-advanced specialist exam.
If you want more targeted question reps while you patch gaps, circle back to the NSE6_FWB-6.4 Practice Exam Questions Pack and treat misses as lab assignments, not as something you just "review."
Difficulty compared to other vendors? Similar to F5 ASM specialist or Imperva specialist certifications. Same vibe. WAF products are all about edge cases and tuning, and exams mirror that.
Renewal and recertification notes
The NSE6_FWB-6.4 renewal policy and validity timing can change as Fortinet updates the program, so verify current rules in the portal. Don't assume it matches older NSE tracks. Same for anything tied to upgrades across FortiWeb versions.
FAQ (people also ask)
What is the NSE6_FWB-6.4 exam and who should take it?
It's the Fortinet specialist exam for FortiWeb 6.4, aimed at engineers who deploy, manage, and troubleshoot WAF protections in real environments, especially around OWASP Top 10 and bot/automation abuse.
How much does the NSE6_FWB-6.4 exam cost?
The NSE6_FWB-6.4 exam cost depends on region and provider. Check the Fortinet certification portal for the current price where you live.
What is the passing score for the NSE6_FWB-6.4 exam?
Fortinet doesn't always publish a static number publicly. You'll see scoring details during registration and in the official exam page for your region.
How hard is the Fortinet NSE 6 FortiWeb 6.4 exam?
Intermediate to advanced. Much harder than NSE 4. Heavy on scenario troubleshooting, configuration choices, and tuning, not just feature definitions.
What are the best study materials and practice tests for NSE6_FWB-6.4?
Official training, FortiWeb 6.4 study materials like the admin guide and release notes, plus hands-on labs. For exam-style drills, add something like NSE6_FWB-6.4 Practice Exam Questions Pack alongside lab work so you're not only memorizing.
FortiWeb 6.4 Exam Objectives and Core Knowledge Domains
FortiWeb deployment architecture and operational modes
Okay, real talk here. When you're prepping for the Fortinet NSE6_FWB-6.4 exam, you've gotta understand that FortiWeb isn't some cookie-cutter appliance you just slap into your network and call it a day. It's got multiple operational modes, and honestly, picking the wrong one? That can turn your deployment into either a complete nightmare or just make it totally ineffective for what you're actually trying to accomplish here.
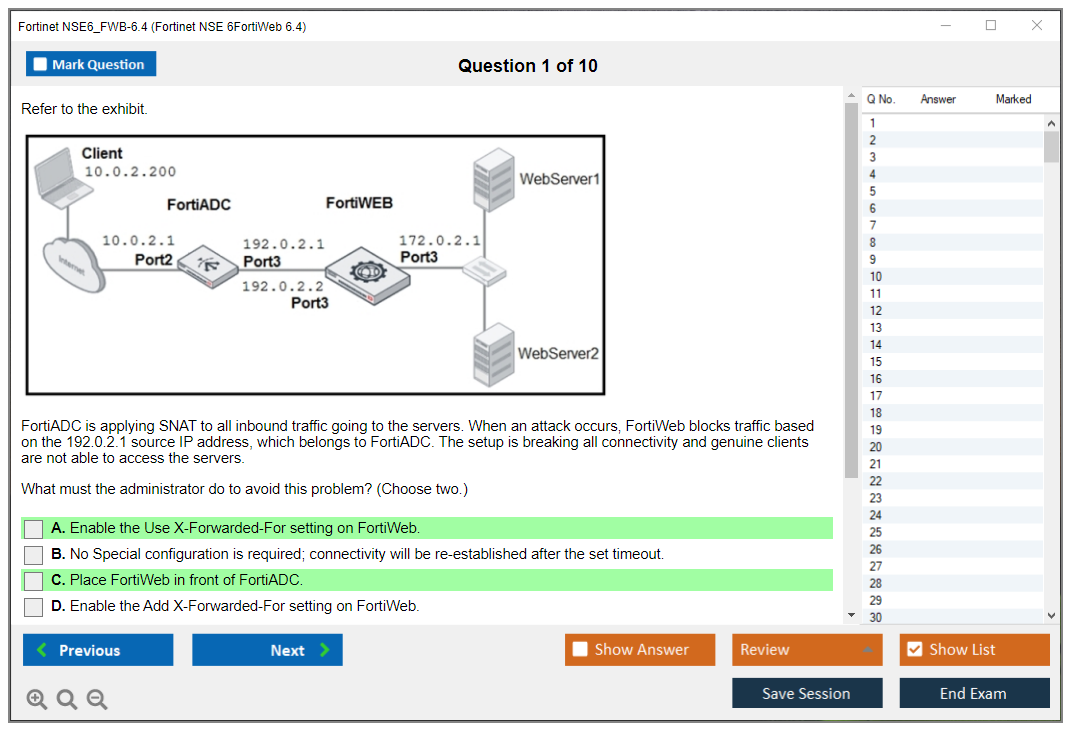
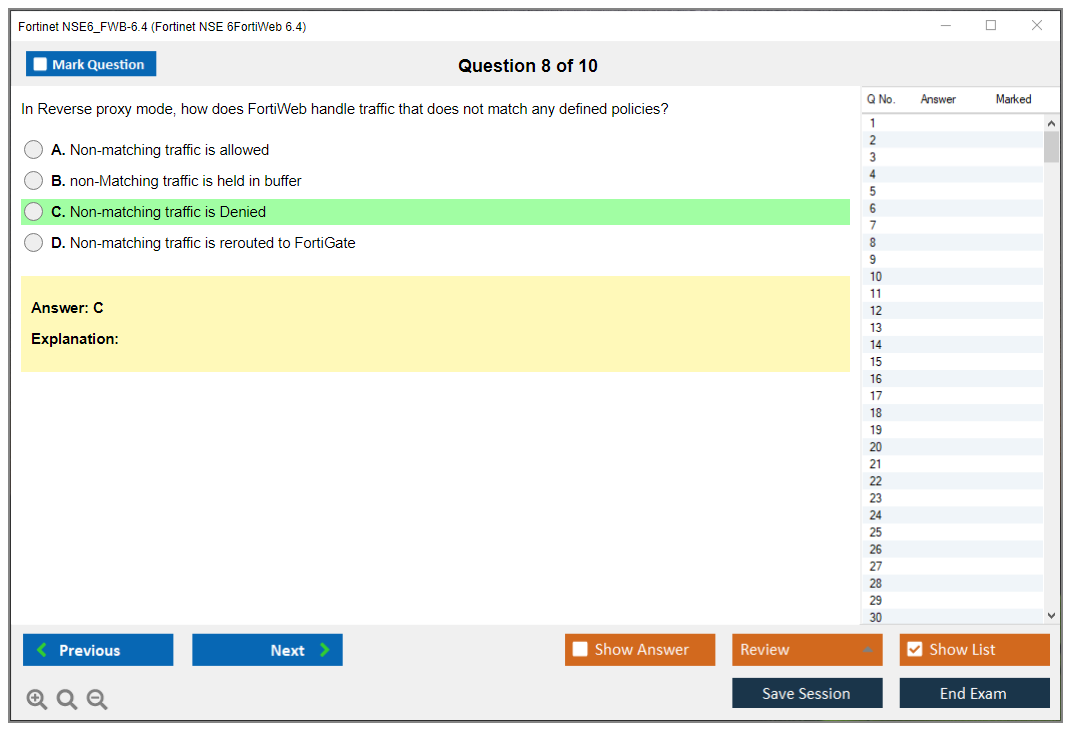
Reverse proxy mode? Yeah, that's probably what most folks think of first when they hear "web application firewall." FortiWeb sits right between your clients and those backend servers, terminating connections and inspecting absolutely everything flowing through. It's strong because you get full visibility and control, but here's the catch: FortiWeb becomes the endpoint for all SSL/TLS connections. True transparent proxy mode works differently. It's inline like reverse proxy, sure, but it preserves those original client IP addresses, which means you'll need to adjust network routing to make sure traffic actually flows through the device properly instead of bypassing it entirely.
Then there's transparent inspection mode, which is honestly more passive in nature. I use this during initial tuning phases because it monitors traffic without actually intervening in the flow. Perfect for developing policies without breaking production systems and making your users scream at you. Offline protection mode analyzes mirrored traffic copies, so you get threat detection without any inline latency concerns whatsoever.
WCCP deployment scenarios? Those integrate with routers using Web Cache Communication Protocol for transparent traffic redirection. Network topology considerations matter too. Single-arm versus dual-arm deployments have different routing implications. VLAN configurations change how you segment traffic, and you'll need to think through high availability pairs, load distribution strategies, and how FortiWeb integrates with existing infrastructure like load balancers or CDNs that're already sitting in your environment. Not gonna lie, this domain trips up tons of people because it's about knowing what each mode does. It's about knowing when and why you'd pick one over another based on your specific environment, business requirements, and the technical constraints you're working within.
Server objects, policies, and how traffic actually gets processed
Server pool configuration? That's where you define backend server groups. You're setting up health monitoring checks, choosing load balancing algorithms (round robin, least connections, whatever fits your application best), and configuring session persistence so users don't get bounced between servers mid-session, which would log them out or lose their shopping cart.
Virtual server creation maps external services to internal servers. You need to nail down protocol specifications and port configurations correctly or literally nothing works.
Server policy structure is hierarchical, following a specific order of operations. The policy matching logic has inheritance principles where settings cascade down unless you override them at lower levels. Protected hostname definitions tell FortiWeb which domains and URLs it's actually protecting. Wildcard usage is common here for handling subdomains. Multi-tenancy configurations let you protect multiple completely separate applications on one FortiWeb instance, which is great for service providers or large enterprises managing different business units.
HTTP and HTTPS service parameters include protocol-specific settings, connection limits, timeout values. All the performance tuning knobs you can turn when things aren't behaving right. Content routing rules let you do URL-based routing, host-based routing, or more advanced traffic steering scenarios based on pretty much any HTTP element you can think of. The thing is, SNI handling is critical for multi-domain HTTPS deployments using a single IP address, and X-Forwarded-For preservation maintains original client IP information as traffic passes through proxy layers so your backend logs don't just show FortiWeb's IP for every single request.
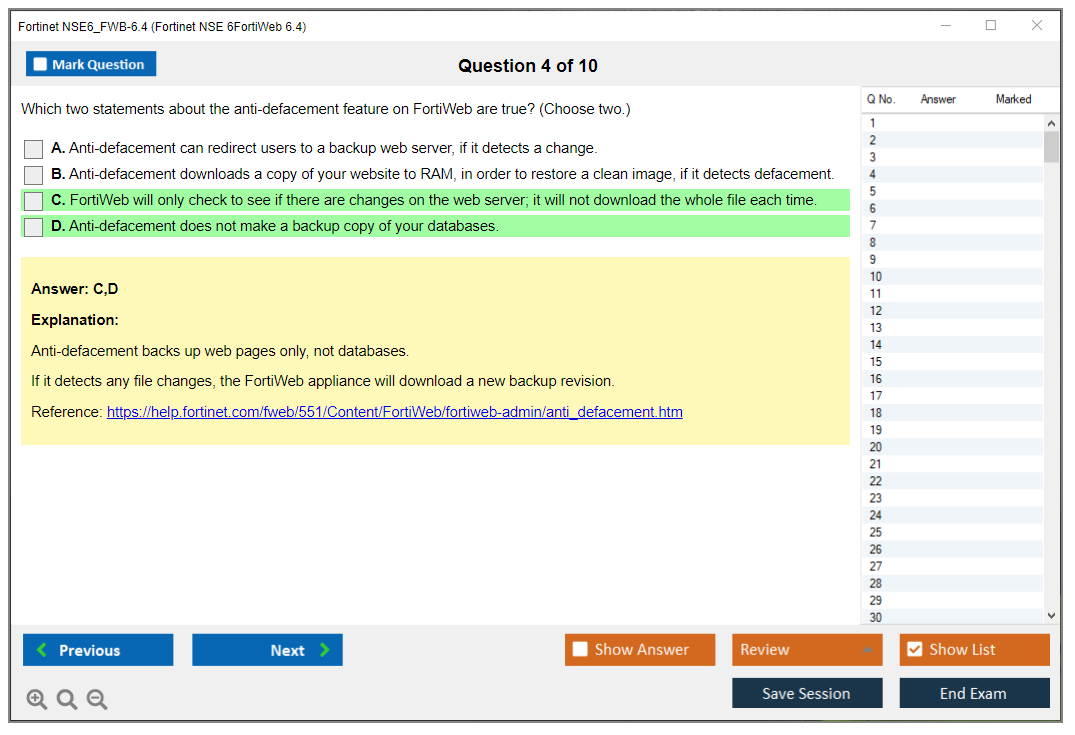
Security profiles and signature-based protection mechanisms
Signature database updates happen automatically, but you can also do manual updates. Understanding versioning and rollback procedures saves you when an update causes unexpected issues or breaks legitimate application functionality. Attack signature categories cover SQL injection, cross-site scripting, command injection, path traversal. Basically the entire OWASP Top 10 and then some additional attack vectors. Signature severity levels classify threats as high, medium, or low risk, and you configure appropriate response actions for each severity.
Custom signature creation? That's huge for real-world deployments. You're writing regular expressions for organization-specific attack patterns that the built-in signatures don't catch because they're unique to your application or environment. Vulnerability scan protection detects and blocks automated scanning tools doing reconnaissance against your applications. Attackers probing for weaknesses before launching targeted attacks. Known attack sources get handled through IP reputation integration and blacklist/whitelist management for blocking or allowing specific source addresses.
Signature exceptions and tuning is where you spend a ton of time in real deployments, no joke. Creating exceptions for legitimate traffic that triggers false positives is an ongoing process that never really ends, and attack log analysis helps you interpret signature match logs for security incident investigation. I mean, you're gonna be looking at these logs constantly when you're first deploying FortiWeb. Figuring out what's real threats versus what's just noisy false positives from how your application actually works in practice.
I remember this one deployment where the application used a weird custom CMS that passed SQL-looking strings in URL parameters for legitimate queries. Took us three days to tune the signatures properly because every page view looked like an injection attempt. Coffee was consumed in dangerous quantities.
Protocol constraints and input validation rules
Protocol constraint profiles define allowed HTTP methods, versions, headers, and protocol elements. You're basically saying "my application only needs GET and POST, so block everything else like DELETE or TRACE." URL parameter restrictions include length limits, character restrictions, and parameter count enforcement to prevent buffer overflows or injection attacks. File upload controls let you restrict file types by extension or MIME type, set size limits to prevent storage exhaustion, and detect malicious files before they hit backend servers.
Cookie security enforcement? It adds HttpOnly and Secure flags automatically, SameSite attributes for CSRF protection, and protects against cookie tampering through integrity checks. HTTP header validation checks for required headers your application needs, forbidden headers that shouldn't be there, and header value constraints. Request body inspection validates POST data formats, enforces JSON or XML schemas against expected structures, and verifies content types match what they claim to be rather than sneaking malicious content through content-type spoofing.
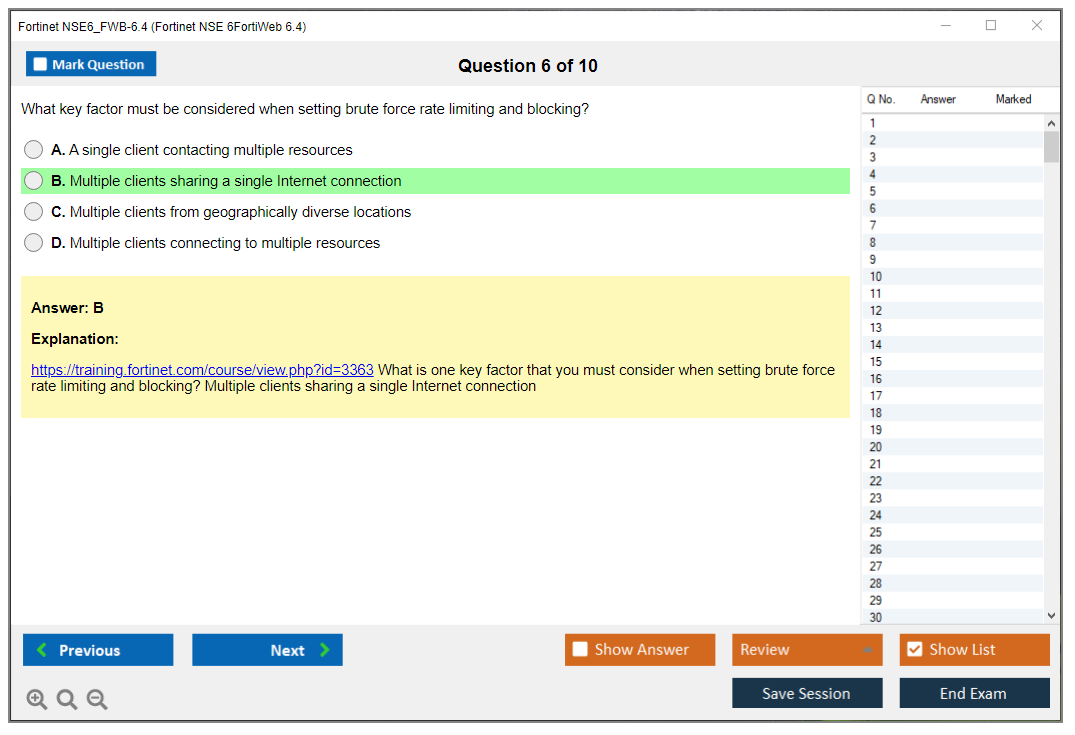
Geo-IP filtering provides country-based access control, which is surprisingly useful when you know your application should only be accessed from specific regions. Like blocking all traffic from countries where you don't do business. Rate limiting and DoS prevention set request rate thresholds per source IP, connection limits to prevent resource exhaustion, and mitigate slow attack scenarios where attackers try to exhaust resources without triggering traditional rate limits by keeping connections open just barely long enough to avoid timeouts.
Machine learning and advanced bot mitigation strategies
The machine learning security service does anomaly detection for zero-day attacks without needing signature updates first, which is critical for protection against novel threats. ML model training establishes baselines during learning periods. You adjust sensitivity based on how your application behaves normally so the model knows what "normal" looks like. Bot detection mechanisms include JavaScript challenges that bots often fail, CAPTCHA integration when you need human verification for sensitive operations, browser fingerprinting techniques, and behavioral analysis that looks at how the client actually behaves over time.
Credential stuffing protection? That detects automated login attempts using stolen username/password pairs and prevents account takeover attacks at scale. API abuse prevention protects RESTful APIs from automated abuse and excessive requests that could overwhelm your services. Biometric behavioral analysis examines mouse movement patterns, typing rhythms, and human interaction verification. Stuff bots typically can't replicate well because they're automated scripts rather than actual humans sitting at keyboards.
Bot signature versus behavioral detection combines signature-based identification of known bot frameworks with heuristic methods for detecting unknown bots. Threshold and action configuration defines bot scores based on multiple factors, confidence levels for classification accuracy, and automated response actions like presenting challenges or outright blocking depending on the threat level.
Authentication, single sign-on, and access control implementation
Authentication methods supported? They include LDAP for Active Directory integration, RADIUS for network-based auth, SAML for enterprise SSO, local database for standalone deployments, and client certificate authentication for high-security scenarios. SAML SSO integration requires identity provider configuration on the IdP side, service provider setup on FortiWeb, and attribute mapping between the IdP and FortiWeb so user attributes flow correctly. Two-factor authentication integrates FortiToken hardware tokens, SMS messages, email codes, and third-party 2FA solutions like Duo or Google Authenticator.
Authentication policies define URL-based authentication requirements. Some URLs might be public facing, others require authentication before access, and exemption rules handle edge cases like health check endpoints. Session security controls manage session timeout for security, idle timeout to free up resources, and forced re-authentication scenarios for sensitive operations. Authorization rules implement role-based access control based on user roles and user group-based policy application, so different users see different levels of access depending on their permissions. Credential security covers password policies like complexity requirements, account lockout mechanisms after failed attempts, and credential transmission protection ensuring passwords aren't sent in cleartext. Federated identity management handles multi-domain SSO scenarios and cross-organization authentication for partner access or merged company environments.
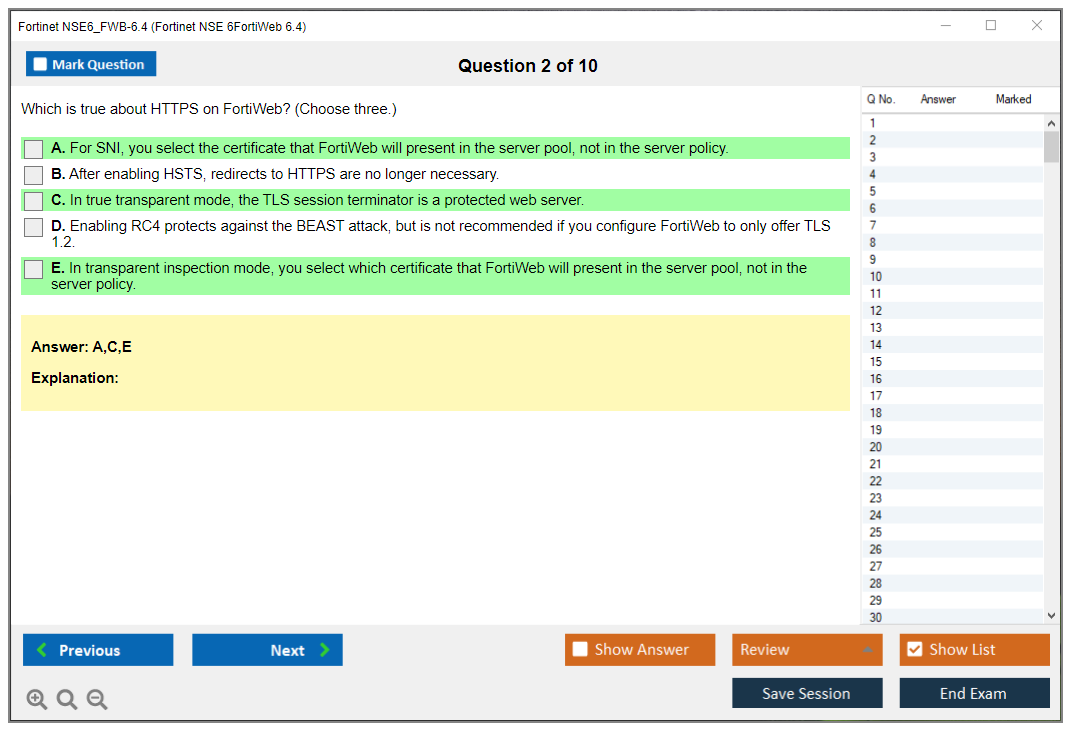
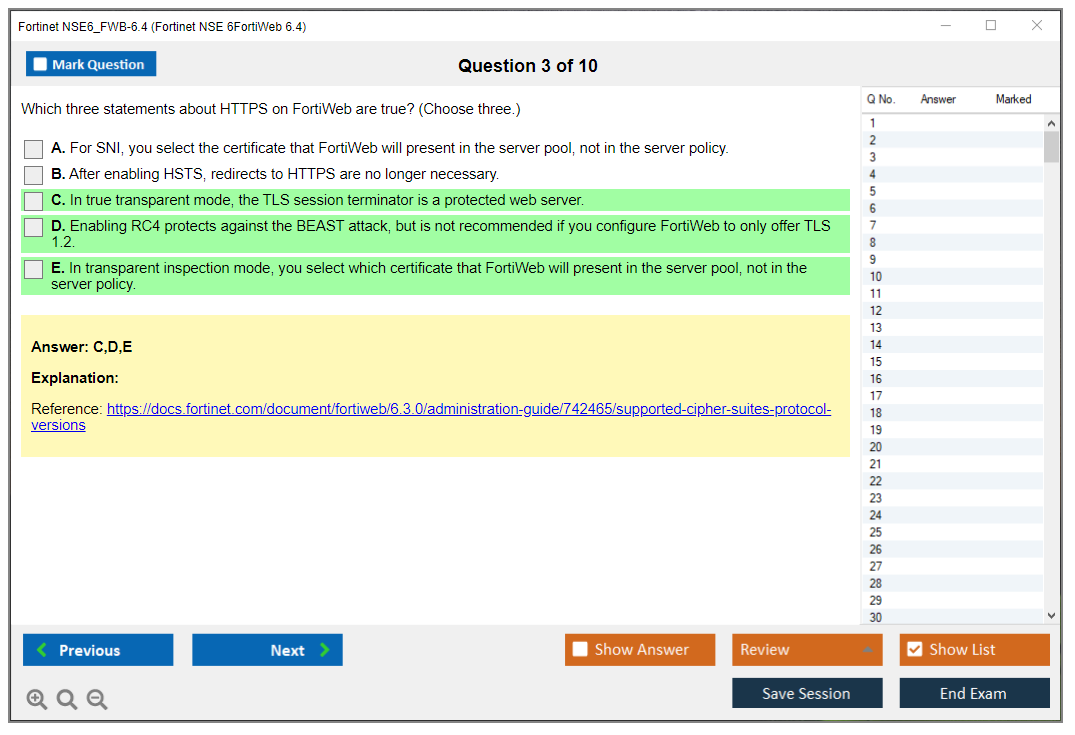
HTTPS inspection, certificate management, and SSL/TLS offloading
Certificate types? You've got server certificates for HTTPS services, intermediate CA certificates for the trust chain, and client certificate validation certificates for mutual authentication. Certificate installation procedures cover importing certificates in various formats, private keys with proper permissions, and managing the certificate chain properly so browsers don't throw warnings. SSL/TLS offloading decrypts traffic at FortiWeb for inspection while reducing backend server load. Those servers don't have to handle the crypto overhead, which can be significant under high traffic loads.
SSL/TLS bridging versus offloading is an important distinction that trips people up. Bridging re-encrypts traffic to backend servers for end-to-end encryption, while offloading sends plaintext internally, which is fine if your internal network is trusted. Certificate-based authentication uses client certificate validation for mutual TLS authentication scenarios where both sides verify each other. Let's Encrypt integration? That provides automated certificate provisioning and renewal, which is fantastic for reducing administrative overhead and preventing those embarrassing certificate expiration incidents.
Perfect Forward Secrecy configuration uses ephemeral key exchange methods like ECDHE for better security. Even if the private key is compromised later, past sessions can't be decrypted. TLS protocol versions should enforce TLS 1.2 or 1.3 minimum nowadays, disabling weak protocols like SSLv3 and TLS 1.0 that have known vulnerabilities, along with weak cipher suites. Certificate revocation checking through OCSP and CRL validation ensures certificates haven't been revoked by the CA after issuance. Honestly, this catches compromised certificates before they cause damage. SNI and multi-domain certificates support multiple domains with appropriate certificate selection based on the requested hostname in the TLS handshake.
Logging, monitoring, and troubleshooting capabilities
Log types? They include attack logs showing security events, traffic logs for all requests, event logs for administrative actions, and system logs for device health. Syslog integration forwards logs to external SIEM systems like Splunk, dedicated log servers, and FortiAnalyzer for centralized management and correlation across your entire Fortinet infrastructure. Attack visualization through dashboard widgets provides real-time attack monitoring and trend analysis. Seeing attacks spike helps you respond faster. Report generation includes scheduled reports for weekly reviews, custom report templates adjusted to your needs, and compliance reporting for audits like PCI-DSS or HIPAA.
Alert configuration? That sets up email alerts for security teams, SNMP traps for network monitoring systems, and webhook notifications for security events that integrate with incident response platforms. Packet capture provides diagnostic capabilities for troubleshooting false positives and connectivity issues when logs alone aren't enough. Debug logging enables detailed debugging output when you're deep into troubleshooting mode, though you typically don't leave this on in production because of the performance impact it has and the massive log volume it generates, filling up storage quickly.
For anyone preparing for the NSE6_FWB-6.4 exam, these core knowledge domains represent what you'll actually be tested on come exam day. It's different from something like NSE4_FGT-7.2 where you're focused on FortiGate firewalls and general network security. FortiWeb is specialized for web application protection, so you need deep knowledge of HTTP/HTTPS protocols, web-based attacks, and application-layer security that goes way beyond traditional firewalling. The exam tests practical knowledge, not just theory you memorized, so hands-on experience with FortiWeb deployments makes a massive difference in your ability to answer scenario-based questions correctly rather than just guessing.
Conclusion
Wrapping up your NSE6_FWB-6.4 path
Look, the Fortinet NSE6_FWB-6.4 exam isn't something you can cram for over a weekend and hope for the best. Honestly? If you've been working with web application firewalls for a while and you understand HTTP traffic inspection at a deep level, you've got a solid foundation. But this certification really wants to see that you can deploy, configure, and troubleshoot FortiWeb in production scenarios that mirror what enterprises actually deal with, including all those edge cases nobody talks about until something breaks at 2 AM.
Deployment modes matter. Traffic processing policies too. The exam objectives cover a lot of ground, but honestly the security profiles section trips people up more than it should because you need to understand not just what bot mitigation or signature-based protection does, but when to apply each method and how they interact with server objects and authentication flows. HTTPS inspection and certificate management is another area where theory meets painful reality. If you haven't actually configured SSL offloading or troubleshot certificate chain issues in a lab, you're gonna struggle with scenario-based questions. I mean, reading about certificate validation is way different from watching it fail in real-time and figuring out why.
What really helped me (and what I tell everyone prepping for the Fortinet NSE 6 FortiWeb 6.4 certification) is building out a home lab. Not gonna lie, even a virtual setup where you can test different deployment modes and break things intentionally teaches you more than reading the admin guide five times. Combine that hands-on time with official Fortinet training materials and you're in good shape. But here's the thing: you also need to validate your knowledge against real exam-style questions before test day, though I'll admit I procrastinated on this part way longer than I should've. Reminds me of when I kept putting off studying for my driver's test in high school, convinced I already knew everything from playing racing games. Spoiler: parallel parking in Gran Turismo doesn't translate.
Practice tests matter.
A lot, actually. They expose gaps in your understanding of FortiWeb 6.4 exam objectives and help you get comfortable with how Fortinet phrases questions, which can be tricky if you're used to other vendor exams (Cisco people, I'm looking at you.. totally different question style). The NSE6_FWB-6.4 passing score demands you know your stuff across all domains, so targeted practice on weak areas makes a huge difference in your confidence and performance. Mixed feelings here. Some folks say practice exams make you memorize answers instead of learning concepts, but that's only true if you're just speed-running them without understanding why each answer's correct.
If you're serious about passing on your first attempt, I'd recommend checking out the NSE6_FWB-6.4 Practice Exam Questions Pack. It's built specifically for this exam version and covers the full scope of what you'll face. Pair that with your lab work and study materials, and you'll walk into the testing center (or boot up your online proctored session) actually ready, not just hoping you studied the right things.