CompTIA CS0-003 (CompTIA CyberSecurity Analyst CySA+ Certification Exam)
CompTIA CySA+ CS0-003 Exam Overview
What is the CompTIA CySA+ CS0-003 certification
CompTIA CySA+ CS0-003 is an intermediate-level cybersecurity analyst certification. It validates hands-on security operations skills. This isn't just theory. The focus is what you actually do when you're sitting in a SOC staring at logs and trying to figure out if that weird traffic pattern is an actual attack or just Bob from accounting breaking things again.
CS0-003 is the current exam version replacing CS0-002, which CompTIA launched in 2024. The update wasn't cosmetic. They overhauled content to reflect how cybersecurity has evolved, particularly around cloud security monitoring, automation, and the modern threat space that keeps getting more chaotic every year.
This cert focuses heavily on behavioral analytics, threat intelligence, and defensive security operations. You're learning to be the person who spots the bad stuff before it becomes a headline, which is getting harder with how sophisticated attacks have become. It's vendor-neutral, which is refreshing because you're not locked into one company's ecosystem. The certification is recognized globally across industries and government sectors, making it valuable whether you're eyeing private sector jobs or federal positions.
Real-time threat detection? That's the core. The CySA+ validates your ability to detect, analyze, and respond to security threats in real-time environments. That's the core value here. You're proving you can handle the pressure when something suspicious pops up at 2am and you need to decide whether to escalate or investigate further.
It bridges the gap between foundational Security+ and advanced CASP+ certifications. If you've got your SY0-701 or SY0-601, this is your logical next step. Security+ teaches you the concepts. CySA+ teaches you to actually use them when someone's trying to break into your network.
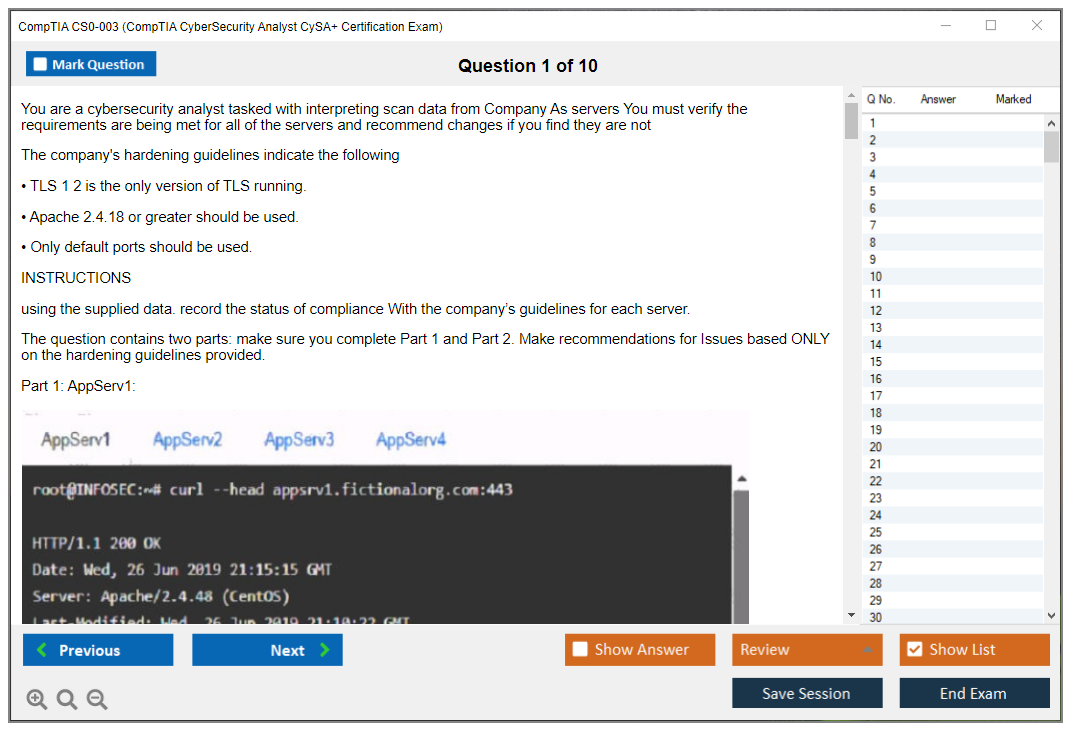
The exam emphasizes practical application through performance-based questions and scenario analysis. You can't just memorize definitions and pass. You'll face simulated environments where you need to configure tools, analyze logs, or triage incidents. These PBQs separate people who've actually touched security tools from those who just read about them, which makes total sense given what SOC analysts actually deal with daily.
CompTIA aligned CS0-003 with the NIST National Initiative for Cybersecurity Education (NICE) framework. The cert meets ISO 17024 standards. It's approved for DoD 8570.01-M baseline certification requirements, so if you're targeting government contracts or federal positions, this checks major boxes.
You get three-year certification validity requiring continuing education for renewal. Look, that's actually reasonable. Cybersecurity changes fast, and what worked three years ago might be laughably outdated today. I once saw a security policy document from 2019 that didn't mention zero trust or cloud workloads at all, which tells you how quickly this field moves compared to, say, accounting practices that can stay stable for decades.
What the CySA+ certification validates
Threat detection and response capabilities in Security Operations Center (SOC) environments sit at the heart of this certification. You're demonstrating you can work tier 1 or tier 2 analyst roles where you're the first line of defense against intrusions.
The exam tests proficiency with security information and event management (SIEM) platforms and log analysis. SIEM tools like Splunk, QRadar, or Elastic Security are everywhere in enterprise environments, and CySA+ proves you can actually use them to find needles in haystacks. That requires understanding correlation rules, how to write queries, and how to spot anomalies in massive volumes of event data that would overwhelm someone without proper training.
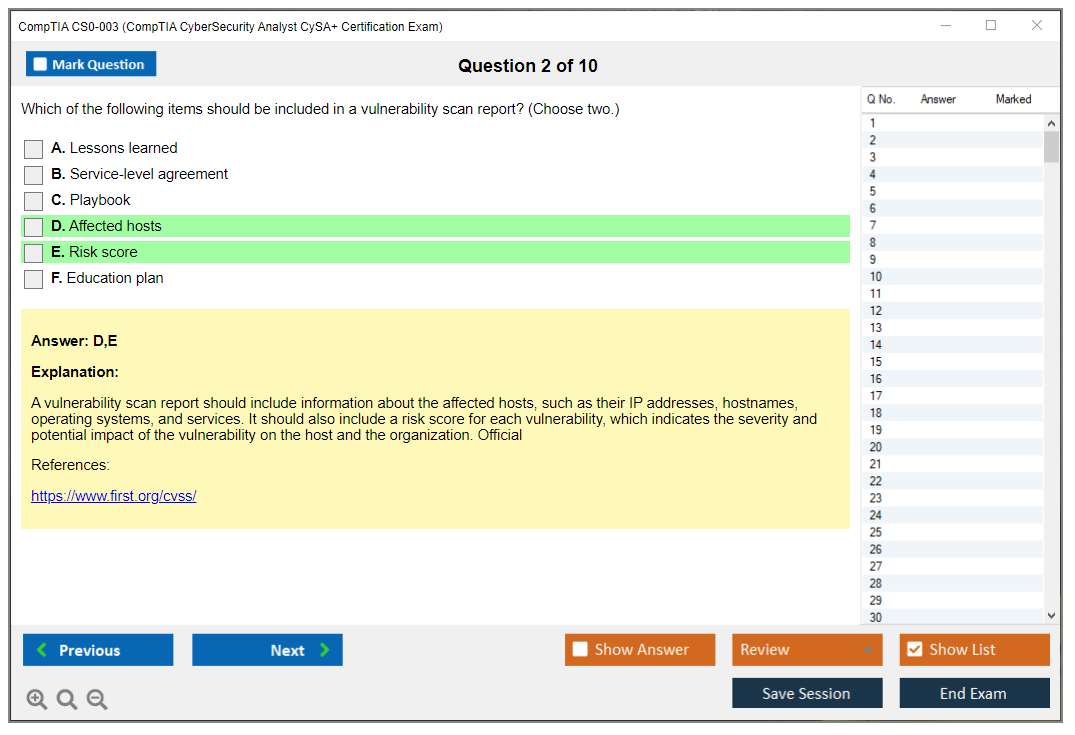
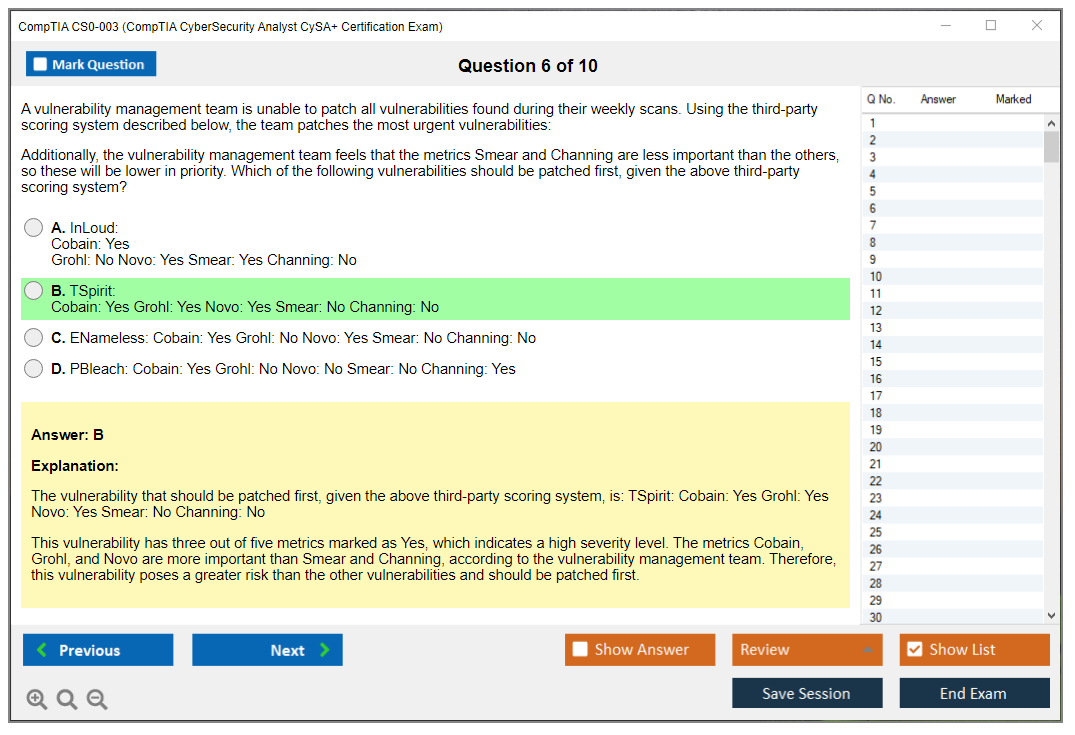
Vulnerability management lifecycle gets significant coverage. Scanning, assessment, and prioritization all get tested. It's not enough to run Nessus and export a report. You need to understand CVSS scoring, how to prioritize remediation based on business context, and how to communicate findings to teams who don't speak security.
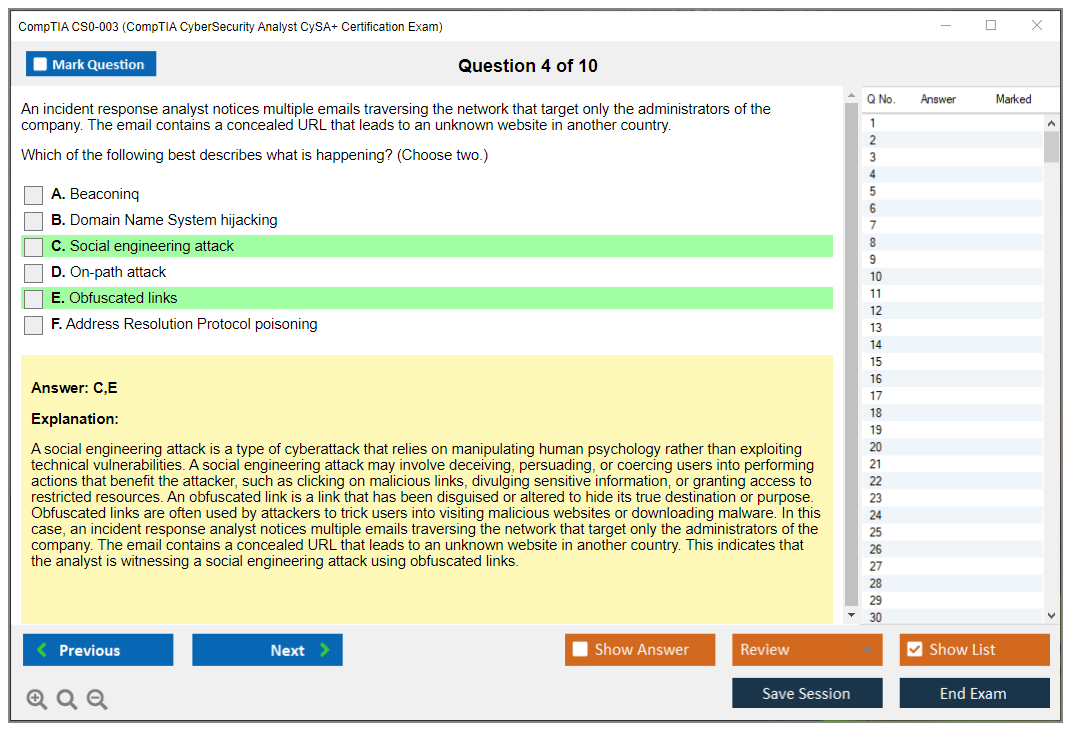
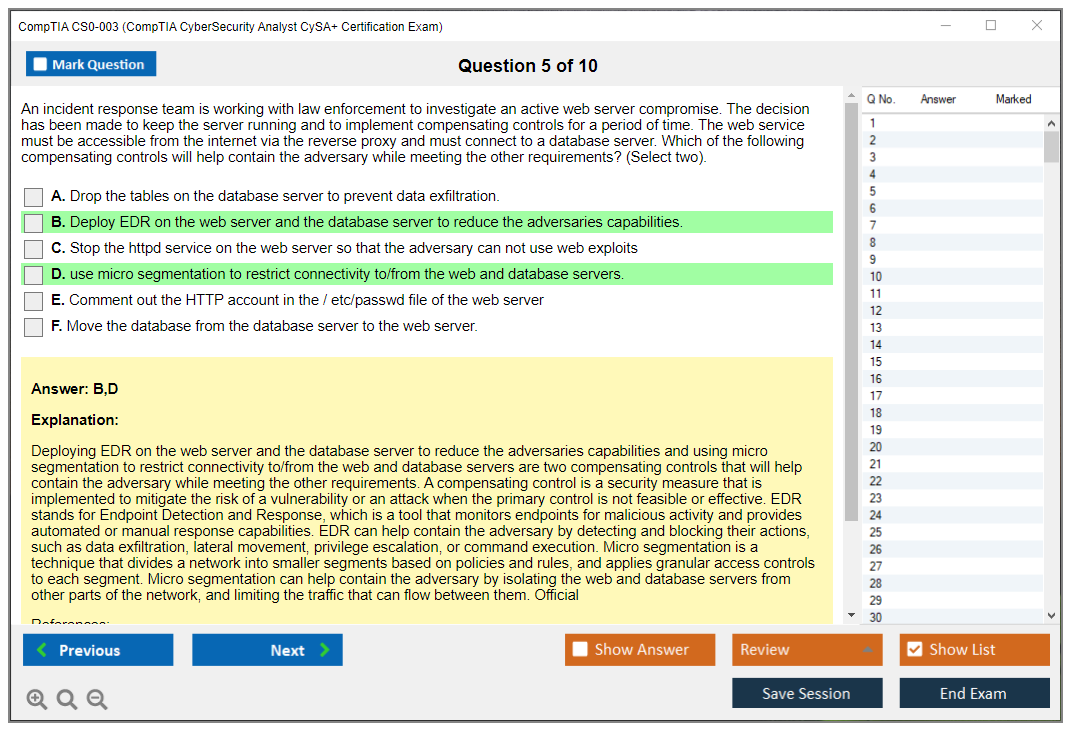
Incident response procedures following industry-standard frameworks like NIST and SANS are core competencies. When something goes wrong, you need a methodology. The certification validates you understand containment, eradication, recovery, and post-incident activities. You're expected to know when to pull a system offline versus monitor it to gather intelligence.
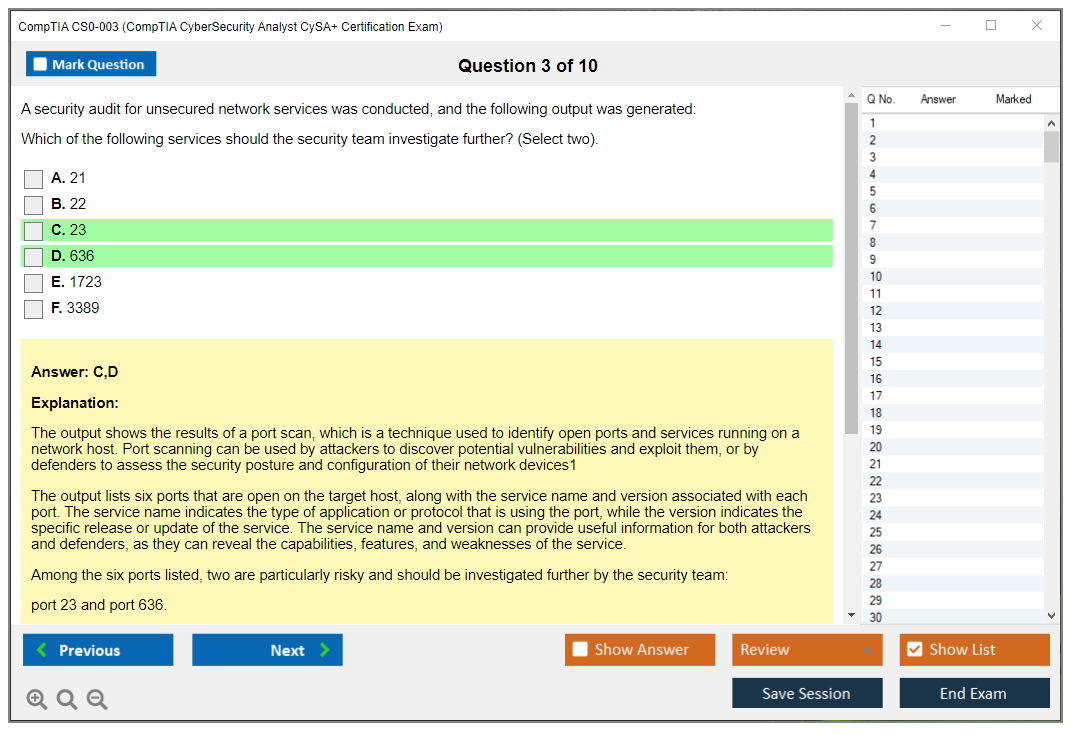
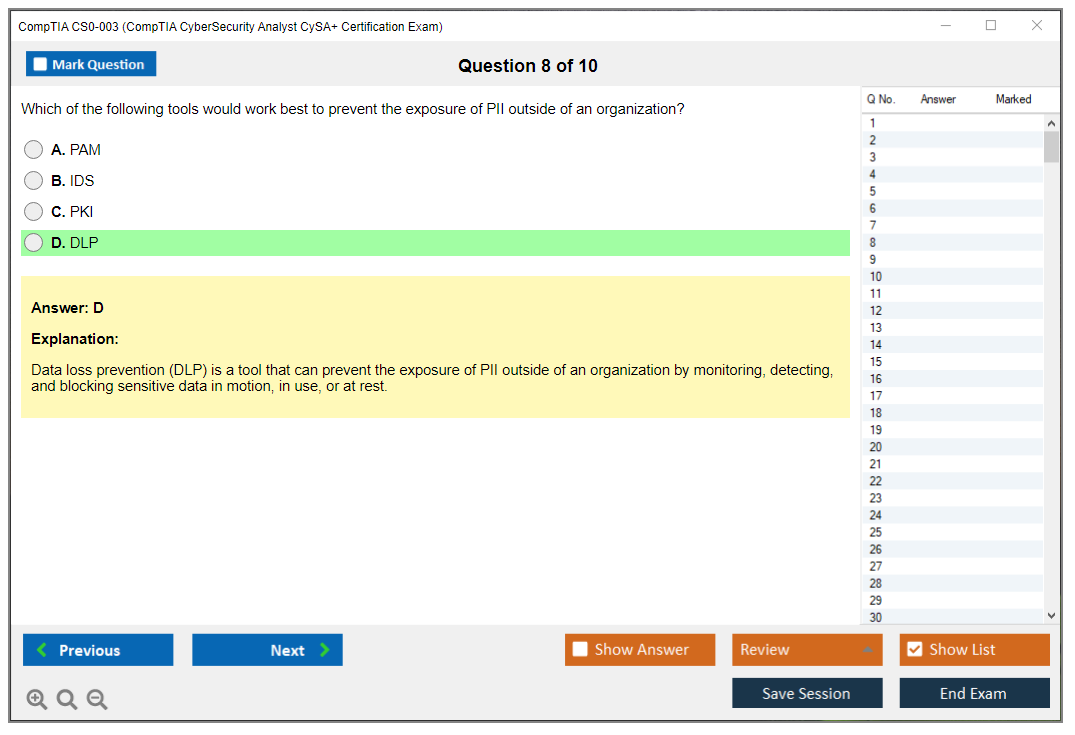
Security monitoring using various tools including IDS/IPS, EDR, and network traffic analysis demonstrates you can work across multiple detection layers. Modern security isn't about one magic tool. You're correlating data from Snort, CrowdStrike, network packet captures, and firewall logs to build a complete picture. That's what actual threat detection looks like in practice, not the sanitized scenarios you see in textbooks.
Threat intelligence consumption, analysis, and application to defensive strategies shows you can take feeds of indicators of compromise and actually do something useful with them beyond just importing them into your security stack.
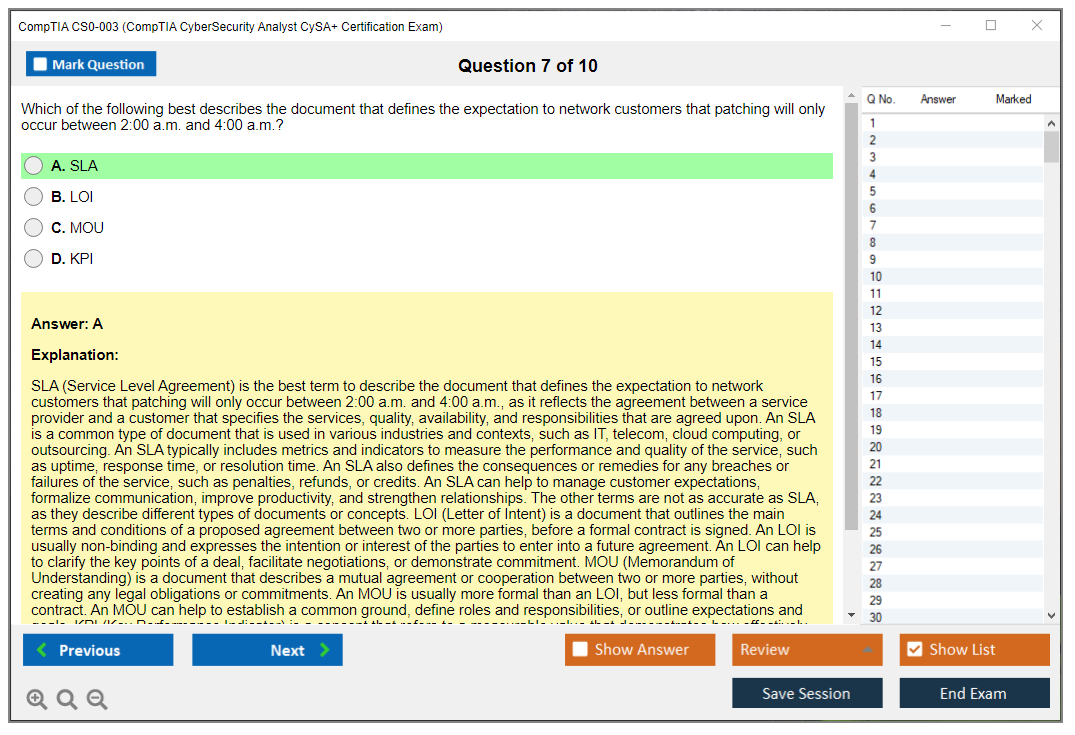
Compliance and assessment understanding for regulatory frameworks like PCI-DSS, HIPAA, and GDPR matters because security doesn't exist in a vacuum. You need to understand how your monitoring and response activities align with legal and regulatory requirements, which frankly adds complexity but also ensures you're not inadvertently violating regulations while hunting threats.
The certification validates security architecture concepts and defensive tool configuration. Reporting and communication skills for technical and non-technical stakeholders get tested. Forensic analysis basics with evidence preservation techniques round things out. That last part's key. You can't just start poking around a compromised system without thinking about chain of custody.
Who should take CS0-003 exam (job roles and use cases)
Security Operations Center (SOC) analysts at Level 1 and Level 2 positions are the primary audience. If you're working in a SOC or trying to break into one, this certification directly maps to your job responsibilities.
Cybersecurity analysts responsible for threat hunting and incident response will find CS0-003 validates the exact skills they use daily. Threat hunters need to understand attacker behaviors, tools, and techniques. This exam covers that territory comprehensively while also testing whether you can actually apply that knowledge under pressure when a real incident's unfolding and executives are breathing down your neck for answers.
Vulnerability analysts managing organizational security posture benefit from this cert. So do threat intelligence analysts working with IOCs and threat actor profiling. Security engineers implementing and maintaining defensive security tools will find the knowledge domains useful. The coverage varies depending on your specific role, but there's overlap across most defensive positions.
IT professionals transitioning into dedicated cybersecurity analyst roles should seriously consider this certification. I've seen plenty of network admins or sysadmins who want to move into security. CySA+ gives you the structured knowledge to make that transition credible.
Network administrators expanding into security monitoring responsibilities will find this helps formalize security knowledge they might be picking up organically. Compliance analysts requiring technical security assessment knowledge can use CySA+ to speak the same language as security teams.
Penetration testers seeking defensive security perspective and credentials might find this valuable too. Understanding how defenders think makes you a better pentester. It's like learning both offense and defense in sports, which only makes you more well-rounded overall. Career changers with Security+ looking for their next certification milestone have a clear path with CS0-003.
Career value and salary impact
Average salary for CySA+ certified professionals ranges $75,000 to $110,000 annually in the US market, though this varies significantly by location, experience, and organization size. Major metros obviously skew higher.
The certification demonstrates readiness for mid-level cybersecurity positions with hands-on responsibilities. It's not entry-level, but it's not senior architect either, so you're in that sweet spot where you're doing real work but not necessarily leading teams yet.
CySA+ meets baseline requirements for many federal government cybersecurity positions. If you're eyeing government contracts or federal civilian roles, this certification opens doors that stay closed without it.
It enhances resume credibility when combined with practical SOC experience. The cert plus experience is the combination employers actually want to see, which makes sense because they need people who can hit the ground running without months of hand-holding. It opens pathways to specialized roles in threat hunting, forensics, and incident response where the real interesting work happens.
Employers recognize CySA+ as proof of practical security operations knowledge, not just theory. It complements vendor-specific certifications like Splunk, Microsoft, or Cisco security tracks because it provides the foundational analytical thinking while vendor certs prove platform expertise.
The certification is a stepping stone toward CISSP, GIAC certifications, or other advanced credentials. Nobody starts at the top. CySA+ is a solid mid-career milestone.
Key differences between CS0-002 and CS0-003
Updated threat intelligence content reflecting the current threat space is probably the most noticeable change. Ransomware tactics, supply chain attacks, and nation-state TTPs that barely registered in CS0-002 are now prominently featured.
Enhanced focus on cloud security monitoring and hybrid environment analysis reflects how most organizations actually operate now. You can't just monitor on-prem anymore. You need to understand cloud-native logging, container security, and how to get visibility into AWS, Azure, or GCP environments. That's where most workloads are migrating anyway.
Expanded coverage of automation, orchestration, and SOAR platform concepts acknowledges that manual response doesn't scale. Security teams are adopting playbooks and automated response workflows, and CS0-003 tests whether you understand how to work with these systems.
Updated vulnerability management content including modern scanning methodologies addresses how vulnerability assessment has evolved. API security, container scanning, and infrastructure-as-code security scanning are all more prominent. That reflects where vulnerabilities are actually showing up these days rather than the traditional server-based weaknesses we've dealt with for decades.
Revised incident response procedures aligned with current frameworks mean you're learning what organizations actually do today, not what they did five years ago. Additional emphasis on supply chain security and third-party risk assessment reflects high-profile breaches that made everyone realize vendor security matters.
Enhanced performance-based questions testing practical tool usage means the exam got harder, frankly. But it also means passing proves more. Updated exam objectives reflecting evolving cybersecurity analyst responsibilities keep the certification relevant as job roles shift.
CS0-003 Exam Objectives and Domains
CompTIA CySA+ CS0-003 exam overview
The CompTIA CS0-003 CySA+ exam is what I recommend when someone tells me "theory's not cutting it anymore, I need actual job skills." It's a cybersecurity analyst certification focused on what you're really doing in a SOC during a midnight shift, how you parse through chaotic logs that barely make sense, how you figure out which alerts actually matter when everything's screaming at once, and how you translate technical chaos into something a non-security person can grasp without their eyes glazing over.
Real workflows here. Detection and response. Actual tickets. Escalations that go nowhere. Reports that collect dust. And yeah, that's exactly why the CompTIA CySA+ CS0-003 certification hits different compared to Security+. Way more applied.
What the CySA+ certification validates
Look, the CySA+ badge means CompTIA trusts you won't freeze up during threat detection and response. You're competent. Not flawless. You're supposed to understand security monitoring and SIEM basics, vulnerability management and scanning, incident response procedures, and then here's the kicker: communicate findings like a professional with actual evidence and recommendations that align with business realities instead of just yelling "we're all gonna die."
Short version? SOC brain. Analyst instincts.
Who should take CS0-003 (job roles and use cases)
Security analyst. SOC analyst. Vulnerability management analyst. Junior incident responder. Also IT folks trying to escape pure sysadmin work and pivot into security.
If you've spent months living in tickets and tooling, it'll click. If you've just been memorizing port numbers, honestly, you're gonna have a rough time.
CS0-003 exam objectives (domains)
Official domains and weighting (summary)
The CS0-003 exam objectives break down like this:
Domain 1: security operations (33%). Domain 2: vulnerability management (30%). Domain 3: incident response and management (20%). Domain 4: reporting and communication (17%).
Not gonna sugarcoat it. The weighting reveals what CompTIA actually thinks matters in day-to-day work, and it's heavily detect it, categorize it, respond appropriately, then document everything.
Key skills covered (threat detection, vulnerability management, incident response, reporting)
You're drowning in logs and alerts, then suddenly you're interpreting vuln scanners and app testing concepts, then you're making containment decisions under pressure, and you finish by creating reports that somehow need to satisfy both engineers who want every technical detail and executives who want three bullet points. That's the entire vibe. I once watched a senior analyst spend forty minutes reformatting a report because someone complained about the font, which tells you everything about how much of this job involves actual security versus bureaucratic theater.
Domain 1: security operations (33% of exam)
Security operations turns process into actual defense. You need solid procedures because a SOC without them devolves into people just staring at dashboards while arguing in Slack, and the exam expects you to grasp continuous watching, baseline establishment, and how "normal" traffic patterns make oddities jump out when something sketchy happens.
SIEM dominates here. Log aggregation, correlation, and analysis using SIEM platforms is core, because the job often involves grabbing messy signals from endpoints, identity systems, DNS, proxy, cloud logs, and then connecting the dots fast enough to actually prevent damage. Alert triage and prioritization is the flip side. You've gotta know how to categorize alerts, assign severity ratings, and work efficiently instead of treating every single alert like the building's on fire.
Threat intel shows up too. Sources, formats, and integration, including STIX, TAXII, and OpenIOC. The exam isn't expecting you to become a threat intel researcher, but it does want you recognizing how intel feeds both detections and hunting, and how to track an Indicator of Compromise across the entire enterprise without losing it in some nightmare spreadsheet. Threat hunting approaches appear as hypothesis-driven versus intelligence-driven, and you should articulate what you're hunting, why it matters, and what data confirms you're right or proves you're chasing ghosts.
SOAR concepts matter way more than people anticipate. Security orchestration, automation, and response focuses on making repetitive tasks less soul-crushing, like enrichment, ticket creation, containment steps, and executing playbooks consistently. The exam loves testing workflow automation and playbook development at a conceptual level. Data enrichment deserves attention too, because layering in context like asset criticality, user identity, geo-IP data, known bad hashes, or recent vuln scan findings can transform a "meh" alert into a "drop everything right now" situation.
Communication protocols are baked into ops. Escalation procedures matter. Who gets contacted? When do you escalate to IR? And yeah, measurements and KPIs for SOC performance, like mean time to detect and mean time to respond, plus volume trends and false positive rates. Boring stuff. Still gets tested.
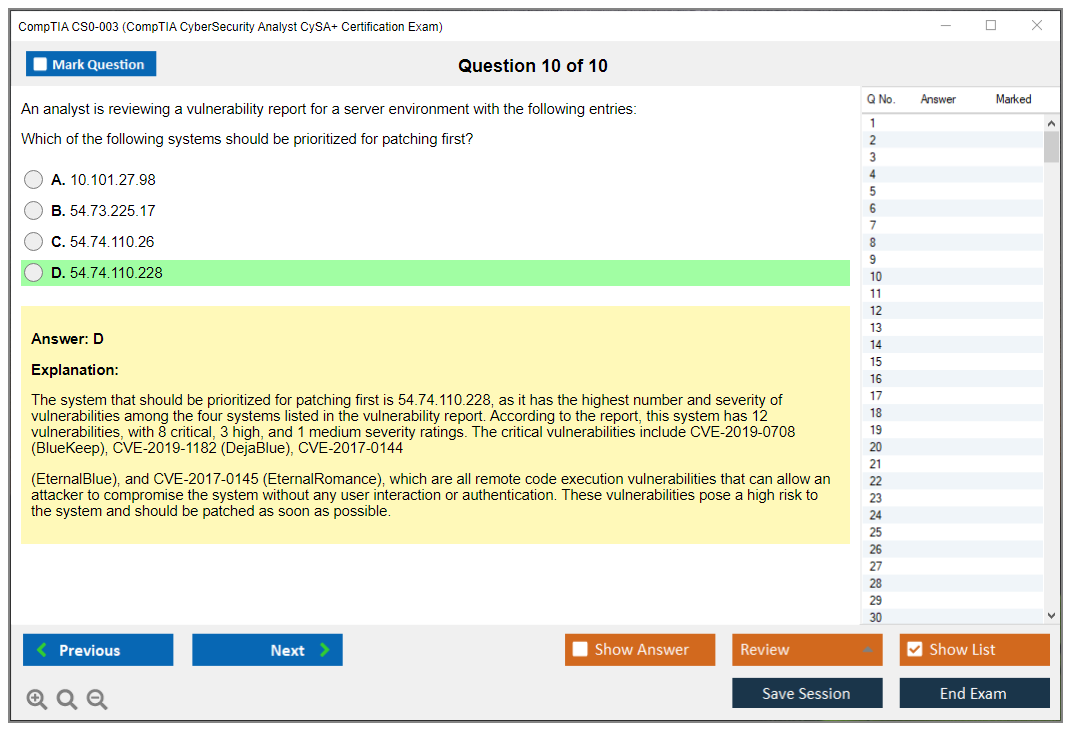
Domain 2: vulnerability management (30% of exam)
Vulnerability management represents a lifecycle, not just a scanner screenshot you email around. Identification, prioritization, fixing stuff, and then validation that your fix actually worked. The exam wants you understanding scanning tools and techniques, configuration best practices, and where credentialed versus non-credentialed scanning fits, because authenticated scanning changes what you can observe, which completely changes your confidence level in the results.
Network scanning splits between internal and external attack surfaces. Internal discovers what attackers exploit after gaining initial foothold. External reveals what the internet sees. Different risk stories. Application security testing concepts appear too: SAST, DAST, and IAST. You don't need becoming an AppSec engineer overnight, but you do need knowing what each method observes and when it's useful, plus accepting the reality that web app vuln checking mixes automated scanning with manual verification because scanners love false positives and bizarre edge cases.
Infrastructure vulnerability identification covers servers, workstations, and network devices. Cloud introduces its own mess, like shared responsibility models, identity misconfigurations, exposed storage buckets, and service-specific logging that impacts what you can actually validate. Container and orchestration scanning emerges as Docker and Kubernetes concerns. Think about images, base layers, vulnerable packages, and cluster misconfigurations that transform a minor issue into full lateral movement opportunities.
Prioritization is where candidates crash and burn. CVSS matters, exploitability matters, and business context matters more than both combined, because a medium CVSS score on a public-facing system with documented active exploitation might completely outrank a higher score on some isolated dev box that three people access. Risk-based vuln management and fix strategy development translates to "patch what'll actually hurt you first." Compensating controls become critical when patching isn't possible. WAF rules, network segmentation, disabling vulnerable features, tightening IAM policies, or adding detection rules. Then you document everything, you communicate it to both technical teams and executives, you patch with proper testing before touching production, and you validate success by rescanning.
Domain 3: incident response and management (20% of exam)
This domain covers the incident response lifecycle: preparation, detection, analysis, containment, eradication, recovery. You also need incident classification and categorization based on severity and actual impact, because saying "we detected malware" isn't a severity level by itself. Context matters enormously. The incident response plan and playbooks deserve attention, because during actual incidents you don't wanna be inventing your process mid-breach while everyone's panicking and Slack's melting down.
Evidence handling appears prominently. Chain of custody requirements. Proper preservation. Forensic analysis fundamentals. Memory forensics, disk forensics, network forensics, and timeline reconstruction across multiple disparate data sources. You're not expected becoming a full-time forensic examiner, but you are expected understanding what evidence proves useful, how to avoid contaminating it, and what specific questions each source can answer.
Containment strategies always involve tradeoffs. Block the user account? Isolate the compromised host? Disable credentials? Stop a service? You're constantly balancing business continuity against threat mitigation, which is corporate-speak for "don't take down payroll processing if you can contain the threat another way." Eradication focuses on removing persistence tricks and access paths, not just deleting one suspicious file. Recovery means getting back to normal operations and validating you're really clean. Post-incident lessons learned and root cause analysis get included, plus communication protocols during active situations, legal and regulatory breach notifications, and coordination with law enforcement or external IR teams when it escalates to that level.
Domain 4: reporting and communication (17% of exam)
People dismiss this domain initially. Then they get promoted and suddenly realize it's half the job.
You need creating security assessment reports for both technical and executive audiences, vulnerability assessment report components (findings, risk ratings, actionable recommendations), and incident response documentation with accurate timelines. Compliance reporting also surfaces, like PCI-DSS, HIPAA, SOX, GDPR requirements. Numbers and measurements matter for communicating program success, and dashboards matter for real-time posture visualization and trend analysis across incidents, vulnerabilities, and emerging threats.
Executive summaries represent a genuine skill. Translate technical findings into business risk without resorting to fear-mongering. Recommendations must be sorted based on risk exposure, cost implications, and implementation complexity. Communication methods vary by stakeholder group. Also critical: secure handling and distribution of sensitive security information, because the worst move involves emailing detailed breach information to the wrong distribution list. Presentation skills matter too, since briefings and training sessions are increasingly part of the analyst career track.
Performance-based question (PBQ) topics across domains
PBQs are where CompTIA tests whether you can do the work.
Expect SIEM query creation and log analysis scenarios, vulnerability scan interpretation and prioritization exercises, incident response decision-making in simulated situations, packet capture analysis for network traffic, security tool configuration and rule creation, threat intel analysis with IOC extraction, and report generation from provided data. Some of these you can brute-force through practice. Others require being comfortable reading through noise quickly.
CS0-003 exam cost and registration
Exam voucher price (what to expect)
CS0-003 exam cost varies by region and available discounts, but in the US it typically lands around $400-ish for a new CompTIA pro-level exam voucher. Check CompTIA's official store for current pricing because it shifts.
Where to buy vouchers and schedule the exam (CompTIA/Pearson VUE)
Purchase through CompTIA directly (or approved partners if you're using training bundles), then schedule with Pearson VUE. You can test at a physical center or online, but online proctoring gets picky about your room setup, your desk cleanliness, and your internet connection stability.
Retake policy and budgeting tips
CompTIA retake rules are published and fairly straightforward. Budget for a potential retake if you're not consistently passing practice exams. Don't fool yourself into thinking you'll "wing it" if your SIEM and triage skills are shaky.
CS0-003 passing score and scoring format
Passing score (what it means)
The CS0-003 passing score uses a scaled score system, and CompTIA publishes the exact required number for the exam. Scaled scoring means you're not just counting correct answers in a straightforward way.
Question types (multiple-choice and performance-based questions)
You'll encounter multiple-choice plus PBQs. Performance-based questions usually appear early in the exam. Manage your time carefully.
How the exam is scored (scaled scoring overview)
Scaled scoring represents CompTIA's method for maintaining difficulty consistency across different exam versions. Treat every question like it counts. Because it does.
CySA+ CS0-003 difficulty: what to expect
Why candidates find CS0-003 challenging
It's broad. And it's applied knowledge. You're forced to switch modes rapidly between detection logic, vuln prioritization, and incident decisions, and that constant context-switching fries people who only studied one narrow area.
Common weak areas (log analysis, SIEM, triage, vuln prioritization)
Weak spots I consistently observe: SIEM queries, noisy alert triage, and risk-based fixing logic. Also cloud logging gaps. People claim they "know" cloud, but they can't explain what specific evidence they'd pull during an incident.
How long to study (time estimates by experience level)
If you've already worked in a SOC, 4 to 6 weeks seems realistic. If you're newer, 8 to 12 weeks is safer, especially if you need substantial hands-on time with security monitoring and SIEM plus scanning tools.
CS0-003 prerequisites and recommended experience
Official prerequisites (if any)
No hard prerequisites exist. CompTIA recommends prior knowledge though.
Recommended background (Security+, networking, SOC workflows)
Security+ level fundamentals help tremendously. Networking knowledge matters. Basic scripting helps. Prior familiarity with SOC workflows is a cheat code.
Skills checklist before you start
Know how to read logs. Know what CVSS represents. Know IR phases. Be comfortable writing a concise report.
Best CS0-003 study materials (official + third-party)
Official CompTIA resources (study guide, eLearning, CertMaster)
CompTIA's study guide and CertMaster products map closely to the CS0-003 exam objectives. They're not always engaging, but they're properly aligned.
Books and video courses (how to choose)
Pick one primary course and one solid book. Mixing five different sources sounds productive and typically turns into elaborate procrastination.
Hands-on labs (SIEM, scanning, IR simulations)
Labs matter most here. Spin up a small SIEM environment, ingest actual logs, write a couple queries, run a vuln scan in a safe lab environment, and practice interpreting results like you're gonna brief an ops team that's already overloaded.
Study plan (4 to 8 week outline)
Weeks 1 and 2: domain 1 plus substantial SIEM practice. Weeks 3 and 4: domain 2 with scanning and prioritization drills. Weeks 5 and 6: incident response scenarios and evidence handling basics. Weeks 7 and 8: reporting practice, dashboard creation, and full mixed review.
CS0-003 practice tests and exam prep strategy
How to use practice tests effectively (timed sets, review, error log)
Use CySA+ CS0-003 practice tests in strictly timed mode, then maintain an error log explaining why your wrong answer was incorrect. Not just identifying the right answer. Understanding the why.
Performance-based question (PBQ) prep tips
Practice writing SIEM queries. Practice reading packet captures. Practice prioritizing a vulnerability list with business context. One skill at a time. Then mixed scenarios.
Final-week revision checklist
Review IOCs and enrichment workflows. Review vuln lifecycle steps. Review containment versus eradication distinctions. Complete one full timed practice exam.
Renewal: how to renew CySA+ (CE program)
Renewal cycle length and CEUs
CySA+ renewal requirements fall under CompTIA's CE program, typically a three-year cycle requiring continuing education units (CEUs).
Ways to renew (CE activities, CertMaster CE, higher certs)
You can renew via CE activities, CertMaster CE, or earning a higher CompTIA certification that automatically renews it. Read the current policy, because CompTIA periodically updates available options.
Fees, deadlines, and avoiding expiration
Pay attention to CE fees and submit CEUs well before the deadline. Don't wait until the last month. People always do. It's unnecessarily stressful.
CS0-003 FAQ (quick answers)
Cost, passing score, difficulty (at-a-glance)
Cost: check current voucher pricing, expect around $400 US. Passing score: CompTIA publishes it specifically for CS0-003. Difficulty level: medium-to-hard if you lack hands-on experience.
Best study materials and practice tests
Start with official objectives, add one solid course, then extensive labs, then practice tests. CySA+ CS0-003 study materials that include realistic PBQs are worth paying for if they're really high-quality.
Objectives and prerequisites
The CS0-003 exam objectives serve as your blueprint. No formal prerequisites exist, but Security+ level knowledge plus actual SOC exposure helps enormously.
Renewal requirements and timeline
Three-year CE cycle, submit required CEUs, pay associated fees, don't miss deadlines. That's the whole deal.
CS0-003 Exam Cost and Registration
What you're actually paying for the CS0-003 exam
Look, the standard CompTIA CS0-003 CySA+ exam voucher costs $392 USD. That's what you'll pay when purchasing directly from CompTIA's website, and it's not cheap compared to entry-level certs like the CompTIA A+ exams. This is an intermediate certification validating threat detection and incident response skills, so the pricing reflects that positioning. You're proving you can actually handle real security analyst work here.
Regional variations exist. If you're outside the US, currency exchange rates and local market factors can push that number higher or lower depending on where you live. I've seen people in Europe pay the equivalent of $420-$450 after conversion. Others in certain regions get slightly better deals through local CompTIA partners.
Your $392 gets you one exam attempt. Just one. That includes scheduling flexibility at any Pearson VUE testing center or through their online proctoring system, but there's no built-in retake safety net at this price point. No sneaky additional fees for scheduling or rescheduling, as long as you follow the policy windows (more on that later). The good news? CompTIA keeps it straightforward on the fee structure.
Finding discounts and alternative purchasing options
Not everyone pays full price. Students can access academic pricing through the CompTIA Academic Partner program, which typically knocks off a decent chunk if your school's enrolled. Military members and veterans should absolutely check CompTIA's partnership programs for discounts. I've seen these range from 10-15% off, sometimes more depending on current promotions.
Bundle options are where things get interesting. CompTIA offers packages combining the exam voucher with study materials like CertMaster Learn or CertMaster Practice. The total cost ends up lower than buying everything separately. A common bundle might run $600-$700 but include the exam plus structured learning content that would otherwise cost $300+ on its own. Seems steep until you break down what you're actually getting.
Corporate buyers training multiple employees can negotiate bulk purchase discounts. If your employer's paying for certification, ask if they've got existing volume agreements with CompTIA or authorized training partners. These deals can reduce per-voucher costs significantly when buying 10, 20, or more at once.
Your exam voucher typically stays valid for 12 months from purchase. That's your window to schedule and take the test. These vouchers are non-refundable, which sucks if you change your mind, but they can be transferable within the same organization in some cases. Check the specific terms when purchasing.
Where to actually buy vouchers and schedule
The official CompTIA store at comptia.org is the most straightforward option. You buy the voucher, receive a code via email, then use that code when scheduling through Pearson VUE. Simple, direct, no middleman confusion.
CompTIA Academic Partners handle institutional purchases and student discounts. If you're enrolled in a training program, your school might purchase vouchers in bulk and resell them to students at the discounted rate. I'd verify this before assuming it's available.
Authorized CompTIA training partners often bundle exam vouchers with their courses. This can be cost-effective if you were planning to take instructor-led training anyway, but verify they're actually authorized before handing over money. Third-party resellers exist, and while some are legitimate, I've heard nightmare stories about invalid voucher codes from sketchy vendors.
You can also purchase directly through Pearson VUE when scheduling. You'll pay full price without access to discounts or bundles available through CompTIA directly.
Scheduling happens through the Pearson VUE website after you've got your voucher code. Search for testing centers by zip code or city. Urban areas typically have multiple locations with lots of available time slots. Rural areas might require driving an hour or scheduling weeks out. The online proctoring option gives you flexibility to test from home if you've got a quiet space, reliable internet, and a webcam that meets their requirements.
I'd recommend scheduling 2-4 weeks in advance for your preferred date and time. Weekend slots fill up fast. They disappear quick, honestly. You'll get a confirmation email with all the details, location instructions or online setup requirements, and the list of what you can and can't bring.
Rescheduling or canceling's possible up to 24-48 hours before your appointment. The exact window depends on whether you're testing in-center or online, so check the specific policy. Miss that window and you forfeit the voucher. No refund. No rescheduling. Just $392 gone.
The retake situation and realistic budgeting
Failed the exam? You're buying another voucher. There's no discounted retake pricing. It's the full $392 again, which is frustrating but that's how CompTIA operates. They don't impose a mandatory waiting period, so you could theoretically reschedule for the next day if slots are available. But I wouldn't recommend that approach unless you barely missed the passing score and identified very specific knowledge gaps.
Take time to review weak areas before dropping another $392. The exam report shows which domains you struggled with. Rushing into a retake without addressing those gaps just burns money. I've seen people fail three or four times because they kept retaking too quickly instead of actually studying the material they didn't know. Seems obvious in hindsight but happens all the time.
Some bundle packages include a retake voucher at a discounted combined price. These "exam + retake" bundles might cost $550-$650 total, which is cheaper than buying two separate vouchers if you do end up needing that second attempt. Given that first-attempt pass rates hover around 60-70% (meaning 30-40% of people fail initially), budgeting for a potential retake makes sense. It's just realistic planning.
Beyond the exam voucher, factor in study materials. Budget $50-$300 depending on what resources you choose. Official CompTIA materials run expensive, but third-party books, video courses, and resources like our CS0-003 Practice Exam Questions Pack at $36.99 offer more affordable alternatives that still cover the objectives thoroughly.
Instructor-led training? That's $500-$2,500 depending on format and provider. Virtual bootcamps tend cheaper than in-person multi-day courses, which makes sense given overhead costs. Practice test subscriptions run $30-$100 for decent quality platforms that simulate the actual exam environment. Lab environments for hands-on SIEM, vulnerability scanning, and incident response practice might cost money unless you're using free trials or community editions of security tools.
Total realistic budget for full preparation and exam? I'd say $500-$1,000. That covers the exam voucher, quality study materials, practice tests, and potentially a retake if needed.
My cousin spent three months prepping for this thing and still had to take it twice. First time he got cocky after passing Security+ and figured he could skim the objectives. Burned through $392 in 165 minutes. Second time he actually sat down with the material, practiced on real tools, and passed with room to spare. The difference wasn't his intelligence. It was his respect for what the exam actually tests.
If your employer offers certification reimbursement, verify the process before purchasing. Some companies require pre-approval, while others reimburse only after you pass. That can affect your planning pretty significantly.
Don't forget the three-year renewal cycle. CySA+ requires continuing education units (CEUs) to maintain certification. While there are free ways to earn those, some people budget for renewal fees or additional training to keep current.
Exam format and what you're sitting down to face
The CS0-003 exam contains a maximum of 85 questions. You're looking at a mix of multiple-choice and performance-based questions (PBQs), with those PBQs typically appearing first in the exam sequence. You get 165 minutes. That's 2 hours and 45 minutes to complete everything. Sounds like a lot until you're actually in there.
This is a linear format exam. You can't skip questions and return to them later like you could with some older certification exams. Once you move forward, that's it. This format forces you to manage time carefully and make decisions without the luxury of flagging tough questions for review. Can mess with people who rely on that strategy.
The performance-based questions simulate real security analyst tasks. You might analyze logs in a SIEM interface, configure vulnerability scan settings, triage alerts, or document incident response steps. These take longer than multiple-choice questions and carry significant weight in your final score.
Testing center delivery involves physical check-in with ID verification, secure testing environment with cameras, and proctors monitoring the room. Online proctoring puts a live proctor on your webcam throughout the entire exam, watching for any suspicious behavior. Both options work fine, but online proctoring requires environmental prep. Quiet room, clean desk, stable internet, specific browser and system requirements.
The exam's primarily available in English, though some regional translations exist. Check Pearson VUE for language availability in your area if English isn't your first language.
If you're working toward CySA+ and already have foundational knowledge from something like Security+ SY0-701, the $392 investment makes sense as a career progression step. But go in prepared. The exam isn't easy, and treating it casually wastes money you could spend on better preparation resources upfront. Why throw away nearly $400 when spending $100 more on quality study materials might actually get you past it first try?
CS0-003 Passing Score and Scoring Format
CompTIA CySA+ CS0-003 exam overview
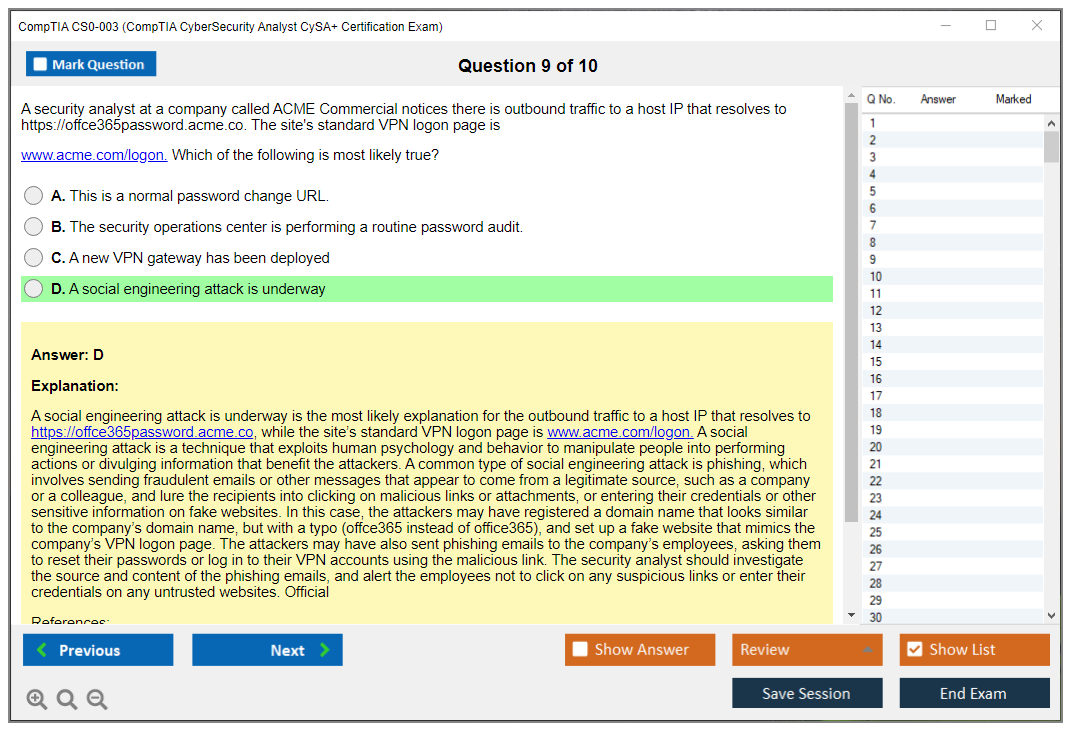
The CompTIA CS0-003 CySA+ exam tests whether you can actually think like an analyst who's buried in Tuesday morning alerts, not just regurgitate definitions from a study guide. You've gotta read messy clues, spot what's weird, and make the "least bad" call under pressure. Short questions? Yeah. Long scenarios that make you second-guess everything? Absolutely. Context everywhere.
What the CySA+ certification validates is honestly pretty specific: threat detection and response, security monitoring and SIEM work, vulnerability management and scanning, plus incident response procedures that actually match how organizations operate in the real world, not some textbook fantasy. Look, it's not a red team flex cert. It's blue team stuff. "Can you handle Tuesday morning alerts without losing your mind" territory.
Who should take CS0-003. SOC analysts. Junior incident responders. Anyone stuck in help desk who keeps getting pulled into security tickets and secretly wants that to become their full-time gig.
CS0-003 exam objectives (domains)
CompTIA publishes the CS0-003 exam objectives, and you should treat them like your contract, not optional reading. If a topic's listed, it can show up, even if your favorite course barely mentions it. Frustrating but that's how it works.
Official domains and weighting change over time as CompTIA refreshes versions, so don't trust random screenshots you find on Reddit. Pull the current CS0-003 exam objectives PDF from CompTIA and mark it up like you're studying for finals. Annotate everything.
Key skills covered are what you'd expect from a cybersecurity analyst certification: triage alerts, interpret logs, write or understand SIEM queries, evaluate scan results, rank remediation work, and communicate what happened to someone who doesn't care about packet headers or technical gibberish. The thing is, reporting matters too. Fragments. Short updates. Because executives don't read paragraphs. I once watched a manager glaze over during a five-minute briefing that could've been three bullet points, and that taught me more about communication than any course module ever did.
CS0-003 exam cost and registration
CS0-003 exam cost is the part nobody wants to talk about until the week they're ready, honestly. The voucher price usually lands in the "this better help my career" range, and it's normal to budget for a retake just in case. Nobody plans to fail, but life happens.
Where to buy vouchers and schedule the exam. You can buy through CompTIA's store or authorized partners, then schedule through Pearson VUE for a test center or online proctoring. Read the online testing rules if you go that route. They're strict as hell. People fail check-in for dumb stuff like a messy desk.
Retake policy and budgeting tips. CompTIA's retake rules are posted publicly, and they can change, so verify before you plan anything. My take: if money's tight, don't gamble on "one shot." Build a real prep plan, and if you want extra reps, grab something like a CS0-003 Practice Exam Questions Pack to pressure-test weak areas before you burn a voucher.
CS0-003 passing score and scoring format
What is the passing score for CS0-003. It's 750 on a scaled range of 100 to 900. That number's the same no matter which exam form you get, which matters because you and the person sitting next to you might not see the exact same question set. Different versions exist.
Scaled scoring isn't a percentage-based calculation. You don't finish and go "I got 78%, I'm safe." You get a scaled score, and CompTIA keeps the exact scaling algorithm proprietary. Not gonna lie, that annoys spreadsheet-brained people, but it's normal in certification testing across the industry.
People ask what the "real" percent is. The common estimate's around 75% to 80% correct to pass, but that's an equivalent guess, not a promise, because the exact percentage varies due to difficulty weighting that happens behind the scenes. More difficult questions may contribute more to the scaled score, easier ones may contribute less, and psychometric analysis sets those weights using statistical models. All questions still contribute to your final score regardless of difficulty. So yes, even "easy" items matter. Don't throw away points.
No partial credit for multiple-choice questions. If it's single-answer, you're either right or wrong. If it's select-all-that-apply, same deal, and those can be brutal because one missed option tanks the whole thing. Feels unfair but that's the format.
Performance-based questions are weighted more heavily than multiple-choice. That's the part a lot of candidates underestimate, because they spend weeks on flashcards and then get hit with an interactive task that feels like a mini lab practical. Partial credit's possible on some PBQ formats, and that's a big deal because it means you can still pick up points even if you don't finish perfectly. Progress counts.
Passing score is established through psychometric analysis to keep scoring fair across versions. That's also why a 750's supposed to represent the same competency level across all exam administrations. Your score reflects competency, not how you compared to other candidates. No curve against the room. Just you versus the standard they've set.
Understanding scaled scoring methodology
Scaled scoring exists because different candidates receive different question sets. If one version's slightly harder, you shouldn't get punished for it. That'd be ridiculous. So CompTIA takes your raw score (how many you got correct) and converts it to the scaled 100 to 900 number.
Here's the catch. You can't calculate the exact percentage needed, because the scaling model and question weights aren't published anywhere. And honestly, chasing the minimum's a trap anyway, because the exam's designed to test across domains, so if you try to "game it" you usually just end up with weird gaps that show up in PBQs or scenario items that require broader knowledge.
Focus on thorough domain knowledge. If you want a practical way to measure readiness, timed practice plus review beats guessing a magic percent every time. That's where a second pass through something like the CS0-003 Practice Exam Questions Pack can help, because it forces you to explain why an answer's right, not just recognize it from memory.
Question types on CS0-003 exam
Multiple-choice single answer is the classic format. One right option. Three wrong ones that feel suspiciously close, designed to trip you up if you're not paying attention.
Multiple-choice multiple answers is select-all-that-apply. Read the prompt twice. Then read it again. Tiny words matter. "Always," "never," "best" change everything.
Performance-based questions (PBQs) simulate real tasks. Drag-and-drop shows up for categorization and sequencing work. Matching questions connect tools to outcomes or steps to phases. Scenario-based questions are everywhere and they're honestly the vibe of CySA+. It's all about context.
No essay questions. No typed short answers. Which sounds easier, until you realize the exam still wants you to think critically, it just does it through scenarios and tasks that require decision-making.
Performance-based questions (PBQ) details
Typically you'll see 3 to 5 PBQs at the beginning. They can be time sinks, like 5 to 15 minutes each, depending on how comfortable you are with the workflow. Wait, I should mention you can skip them and come back later, and I mean, that's often the smart move if you need to rack up quicker points first and settle your nerves.
PBQs can include SIEM query building and log analysis, vulnerability scan interpretation and remediation prioritization, network diagram analysis and control placement, incident response decision trees and sequencing, plus security tool configuration or rule creation that feels like actual job tasks. The first two are the ones I see people struggle with most, because they require you to read output, infer what matters, and ignore the noise, all while the clock's running and your brain's yelling.
Hands-on labs matter for PBQs. Watching videos helps, sure, but clicking around in a lab's different. Muscle memory kicks in. If you're light on practice, add a lab week, and pair it with targeted questions from the CS0-003 Practice Exam Questions Pack so you can link the "doing" with the "why."
How exam results are delivered
You get an immediate preliminary pass/fail at the test center or right after an online exam ends. Your scaled score shows on screen after completion. That moment's either relief or frustration.
The official score report usually shows up in your CompTIA certification account within about 24 hours. It includes your overall scaled score and a domain-level performance breakdown, but not specific per-domain scores and definitely not question-by-question feedback. You won't see the questions you missed, you won't get correct answers, which is annoying for review purposes.
Passing candidates get access to the digital badge and certificate stuff. Failed candidates get diagnostic guidance so they can focus study on weak domains, which's actually useful if you're willing to be honest about what you avoided.
CySA+ CS0-003 difficulty: what to expect
CS0-003 is challenging because it's not trivia-first. You're interpreting evidence. Logs. Alerts. Scan summaries. A lot of "what should you do next" thinking, where two options might both be valid in the real world but only one matches CompTIA's expected priority. Can feel arbitrary.
Common weak areas: log analysis, SIEM filtering, triage decisions, vuln prioritization. Also reporting. People sleep on reporting because it feels soft, then get hammered by questions that ask for the best wording, the best metric, or the best next communication step for non-technical stakeholders.
How long to study. If you already work in a SOC, 3 to 6 weeks of focused prep can be enough. If you're coming from IT support, plan 6 to 10 weeks and do labs. No shortcuts.
CS0-003 prerequisites and recommended experience
Official prerequisites. CompTIA typically lists recommendations rather than hard requirements, so nobody checks your résumé at the door. You can register regardless.
Recommended background: Security+ level basics, comfort with networking concepts, familiarity with SOC workflows, and a working understanding of how incidents move from detection to containment to lessons learned in a real environment. Skills checklist before you start: reading logs without fear, basic vuln scanning concepts, and being able to explain what a SIEM's doing when it correlates events from multiple sources.
Best CS0-003 study materials (official + third-party)
Official CompTIA resources include study guides and eLearning options. Third-party books and video courses are fine, but pick one primary source and one backup, otherwise you'll drown in content and never finish anything. Decision paralysis is real.
Hands-on labs. Do at least a little SIEM practice, even if it's simulated, and run through a couple vuln scan reports so "severity" stops being just a word on a screen.
Study plan. 4 to 8 weeks works for most people if you keep a steady rhythm: learn objectives, do questions, review misses, then do PBQ-style practice until it clicks.
CS0-003 practice tests and exam prep strategy
Practice tests work when you review them like a detective, not when you speed-run them for a score you screenshot and forget. Timed sets. Then an error log. Then re-test the weak domains until you're consistently stronger.
PBQ prep tips: practice reading messy outputs, limit your perfectionism, and get comfortable making a call with incomplete info. That's the job. That's what they're testing.
Final-week revision checklist. Tighten up the domains you keep missing, re-skim the CS0-003 exam objectives, and stop cramming brand-new topics 24 hours before the exam. That just creates anxiety.
Renewal: how to renew CySA+ (CE program)
CySA+ renewal requirements are handled through CompTIA's CE program. Renewal cycle length's typically three years, and you'll need a certain number of CEUs or an accepted alternative like higher-level certs or CompTIA's renewal products.
Fees and deadlines are real. Put reminders on your calendar. Expiration's annoying and avoidable if you just plan ahead.
CS0-003 FAQ (quick answers)
What is the passing score for CS0-003? 750 on a 100 to 900 scaled score.
How much does the CompTIA CySA+ CS0-003 exam cost? Voucher pricing varies, check current CompTIA pricing and partner discounts before you buy.
How hard is the CySA+ CS0-003 exam? Harder than memorization certs, because it pushes analysis and workflow thinking instead of recall.
What are the CS0-003 exam objectives and domains? Download the official objectives PDF from CompTIA and map your study plan to it. Seriously, do this first.
How do I renew my CySA+ certification? Use CompTIA CEUs, CertMaster CE, or qualifying higher certs before the renewal deadline hits.
CySA+ CS0-003 Difficulty: What to Expect
Why candidates find CS0-003 challenging
Look, CS0-003 isn't your typical memorization test. This is an intermediate-level certification demanding both theoretical knowledge and practical application, and that combination trips up loads of people. You can't just read a book and expect to pass.
The heavy emphasis on hands-on skills makes this exam different from something like SY0-701 where you can get pretty far with solid theory. CS0-003 wants proof you've actually used the tools, not just read about them. Performance-based questions will drop you in front of a simulated SIEM interface or log analyzer and expect you to actually do something with it. No multiple choice safety net on those.
The thing is, the exam covers four massive domains. You need security operations skills, vulnerability management expertise, incident response knowledge, and reporting capabilities all at once. That's a diverse skill set that doesn't develop overnight. Most people come into this strong in one or two areas and weak in others, which creates gaps you absolutely have to fill before test day.
The scenario-based questions require critical thinking beyond memorization, honestly. You'll get a situation with multiple technically correct answers, but only one best answer given the specific context. That business context piece kills people who are purely technical. You might know how to use Wireshark perfectly, but if you can't prioritize which traffic to investigate first based on business impact, you're gonna struggle hard.
Time pressure? Real.
165 minutes for up to 85 questions. Sounds generous until you hit those performance-based questions that can eat 10-15 minutes each. Get stuck on a PBQ early, and you're suddenly racing through multiple-choice questions you should be reading carefully. Not gonna lie, I've seen people run out of time with 20 questions left unanswered.
The exam requires understanding multiple security tools and platforms at once, not just one at a time, which is where it gets messy. You need to know how SIEM correlates with vulnerability scanners, how threat intelligence feeds into incident response, how forensic tools preserve evidence that gets reported to stakeholders. It's all interconnected. The exam tests those connections constantly in ways that feel unfair if you haven't connected the dots yourself. (And honestly, even experienced folks sometimes miss these relationships until they're forced to think about them under pressure.)
Log analysis questions demand pattern recognition and anomaly detection skills that are really hard to develop without real SOC experience. You're looking at firewall logs, IDS alerts, authentication failures, and network traffic all mixed together. Finding the actual threat signal in that noise requires practice most study guides can't really give you.
Vulnerability prioritization requires business context and risk assessment judgment beyond just reading CVSS scores. I mean, two vulnerabilities might both be critical severity, but one affects the public web server and one affects an isolated development box. Which do you patch first? The exam wants you to think like an analyst, not a robot following a checklist.
Incident response scenarios test procedural knowledge and proper sequencing in ways that feel unfair if you haven't done it before. Containment before eradication, documentation throughout, chain of custody for evidence. Miss one step or do them out of order, and you've compromised the entire response in the exam's eyes.
The exam assumes baseline networking and security knowledge not explicitly taught in the exam objectives, which honestly catches people off guard. They expect you already understand TCP/IP, subnetting, common protocols, basic security concepts. Weak on networking fundamentals? You'll struggle with packet analysis questions even if you studied the CySA+ material thoroughly. That's why SY0-601 or similar is basically required preparation even though it's not an official prerequisite.
Questions often have multiple partially correct answers requiring best-choice selection. Three options might be technically valid responses to an incident, but only one follows proper procedure or considers the specific constraints mentioned in the scenario. You can't just pick "an answer that works." You need "the best answer for this situation."
Real-world complexity gets reflected.
Questions don't oversimplify. The exam doesn't give you clean, textbook scenarios. You'll get incomplete information, conflicting indicators, time constraints, and resource limitations just like actual SOC work. Some candidates find this frustrating because they want clear-cut answers, but that's not how security analysis works in the real world.
Common weak areas reported by candidates
SIEM query syntax and log correlation across multiple sources rank as top struggle points. People understand what SIEMs do but can't actually write queries or correlate events from firewalls, endpoints, and network devices into a timeline that makes sense. The exam will absolutely test this with hands-on PBQs where you're expected to craft functioning queries.
Performance-based questions requiring hands-on tool familiarity cause panic for candidates who only studied theory. You might see a Wireshark capture, a Nessus scan output, or a Splunk dashboard and need to actually interact with it under timed conditions. Reading about these tools doesn't prepare you to use them under time pressure when your brain's already stressed.
Vulnerability scanning tool output interpretation and false positive identification trip up people constantly. You'll get a scan report with 50 findings and need to identify which are actual risks versus misconfigurations or false alarms. Understanding scanner limitations and validation techniques matters more than knowing the tools themselves.
CVSS scoring calculation and vulnerability prioritization methodology get tested in detail. You need to understand the difference between base, temporal, and environmental scores. You need to know when a high CVSS score doesn't actually mean high priority for your specific environment. The exam loves questions where the scariest-sounding vulnerability isn't actually the one you should fix first.
Incident response procedure sequencing and decision-making under constraints show up everywhere. Preparation, identification, containment, eradication, recovery, lessons learned. You need to know what happens when and why. The exam will give you scenarios where you have limited time or resources and ask what you do first.
Threat intelligence format differences between STIX, TAXII, and OpenIOC confuse people because they sound similar but serve different purposes. STIX structures the data, TAXII transports it, OpenIOC describes indicators. The exam wants you to know when to use each and how they work together in real threat intelligence workflows.
Network traffic analysis and packet capture interpretation require practice most people don't get. You need to spot normal versus suspicious patterns in TCP handshakes, identify data exfiltration attempts, recognize command-and-control traffic. This stuff is hard to learn from books alone.
Compliance framework requirements and mapping to security controls bore people during study but show up on the exam. PCI-DSS, HIPAA, GDPR, SOX. You need to understand what each requires and how technical controls satisfy those requirements. The reporting domain especially hits this area hard.
Forensic analysis procedures and evidence handling protocols require procedural knowledge beyond technical skills. Order of volatility, chain of custody, write blockers, hashing for integrity. You need to know the why behind each step, not just the what you're supposed to do.
Security automation and SOAR platform concepts are newer additions that catch people off guard. Understanding how playbooks work, when to automate versus when to use human judgment, and how SOAR integrates with other tools matters for the security operations domain more than candidates expect.
Cloud security monitoring differs from on-prem in ways many study materials skip, which is frustrating. Shared responsibility models, cloud-native logging, API monitoring, container security. The exam recognizes that modern analysts work in hybrid environments, not purely on-prem.
Reporting and communication appropriate for different stakeholder audiences is a soft skill that technical people often neglect. You need to explain the same incident differently to the SOC manager, the CISO, and the affected business unit. The exam tests whether you understand what each audience needs to know and how much detail to provide.
Tool-specific knowledge for Splunk, Wireshark, Nessus, and Nmap appears frequently even though the exam is supposedly vendor-neutral. You don't need to be an expert in each, but you need working familiarity with how they function and what their output looks like.
How long to study for CS0-003 (time estimates by experience level)
Complete beginners with no IT security experience shouldn't jump straight into CySA+, honestly. Get Security+ first or you'll waste time and money. The exam assumes too much foundational knowledge to start here.
Security+ certified candidates with no SOC experience need 8-12 weeks with 10-15 hours weekly study to have a realistic shot. You've got the theory foundation but lack the practical application skills. That gap requires serious lab time, not just reading textbooks or watching videos passively.
Security+ certified with 1-2 years SOC experience can probably manage 6-8 weeks with 8-10 hours weekly study. You've seen real incidents and used actual tools, so you're connecting concepts to experience rather than learning from scratch. Your weak spots are probably the formal methodologies and compliance stuff that don't come up daily.
Experienced security analysts with 3+ years in the role might only need 4-6 weeks with 5-8 hours weekly study. You're doing this work daily. You mainly need to formalize your knowledge and fill gaps in areas you don't encounter regularly. Focus on your weak domains and practice test performance.
Career changers with strong IT backgrounds need 10-14 weeks with a thorough study plan. You understand technology and can learn quickly, but security analysis is different from systems administration or networking. You need time to develop the security mindset and learn tools you've never touched before.
Study time should include reading, hands-on labs, and practice testing in roughly equal measure. Don't spend 90% of your time reading and 10% practicing. The exam tests application, so your study should too.
Add 2-4 weeks if you're lacking hands-on experience with security tools regardless of how much theory you know. You cannot substitute reading for actual practice with SIEMs, vulnerability scanners, and packet analyzers. Set up home labs or use cloud-based practice environments to get your hands dirty.
Intensive boot camp format works.
5-7 days full-time study with 40+ hours weekly. This requires complete focus and works best for experienced analysts who need structured review, not beginners who need time for concepts to sink in and marinate.
Part-time study beats cramming for better retention in my experience. Spreading 60 hours over 8 weeks gives you time to practice, forget, remember, and reinforce. Cramming 60 hours into one week might get you through the exam but won't make you a better analyst in the long run.
Adjust your timeline based on individual learning pace and prior knowledge gaps, obviously. Some people pick up log analysis instantly while others struggle. Some understand compliance frameworks easily while others find them confusing. Be honest about where you're starting from. Lying to yourself about your skill level just wastes study time.
Conclusion
Wrapping up your CS0-003 path
Okay, look. The CompTIA CS0-003 CySA+ exam? You can't just wing it on a random Tuesday afternoon. It tests actual skills like threat detection and response, vulnerability management and scanning, security monitoring and SIEM operations. Basically all the stuff you'd really be doing in a SOC role day-to-day. The CS0-003 exam objectives cover ground that matters in the field, and that's exactly why the cybersecurity analyst certification carries real weight with hiring managers who've seen every cert under the sun.
Runs about $392. That's the exam cost if you're buying direct from CompTIA, which yeah, isn't pocket change when you're budgeting month-to-month. But here's my take: when you actually consider what the credential does for your resume and salary potential down the line, it's worth budgeting for, even if it stings initially. Just remember the CS0-003 passing score sits at 750 on a 100-900 scale, so you need solid prep going in. Not gonna sugarcoat it. Some candidates seriously underestimate how granular the questions get around log analysis and incident response procedures, then they're blindsided.
I mean, you've probably figured out by now that CompTIA CySA+ CS0-003 certification prep needs way more than just skimming a book the week before. You want CySA+ CS0-003 study materials that include genuine hands-on work. Actual SIEM platforms, vulnerability scanners, the tools you'll physically touch in the real job environment. Mix official resources with third-party courses if that's your style, but make practice tests your anchor. That's where you discover the gaps in your knowledge before exam day discovers them for you, which is.. not fun. I actually watched a buddy reschedule twice because he kept avoiding the performance-based sections in his prep, figured he'd "figure it out" during the test. Spoiler: he didn't.
Technically none. The CS0-003 prerequisites are "officially" nonexistent, but realistically you should have Security+ or equivalent experience under your belt first, or you'll struggle with foundational concepts. And once you pass? CySA+ renewal requirements kick in every three years. You'll need 60 CEUs through the continuing education program, which you can earn through training, higher certs, or other activities CompTIA accepts as valid.
Before you schedule that exam, make sure you're drilling with quality CySA+ CS0-003 practice tests that mirror the real format closely. Performance-based questions can throw you if you've only done multiple-choice. Wait, I should mention the Practice Exam Questions Pack at /comptia-dumps/cs0-003/ gives you realistic scenarios that expose weak spots you didn't even know existed, which beats finding out during the actual exam when it's way too late to do anything about it.
You've got this. But preparation's what separates people who pass confidently from people who reschedule awkwardly. Put in focused study time, use the right resources that work, and you'll walk out with a certification that opens doors in security operations instead of just collecting digital dust.